When it comes to testing web applications, having a reliable framework is essential. This module will introduce you to two of the most popular tools in the field: Burp Suite and OWASP ZAP, both of which provide comprehensive functionality for finding and exploiting vulnerabilities in web applications.
Intercepting Web Requests
With our proxy now up and running, we can start intercepting and manipulating the HTTP requests sent by the web application under test. This allows us to examine the data being sent, make modifications, and then forward the requests to their intended destination. Mastering this technique is key to understanding how web applications communicate and uncovering potential vulnerabilities.
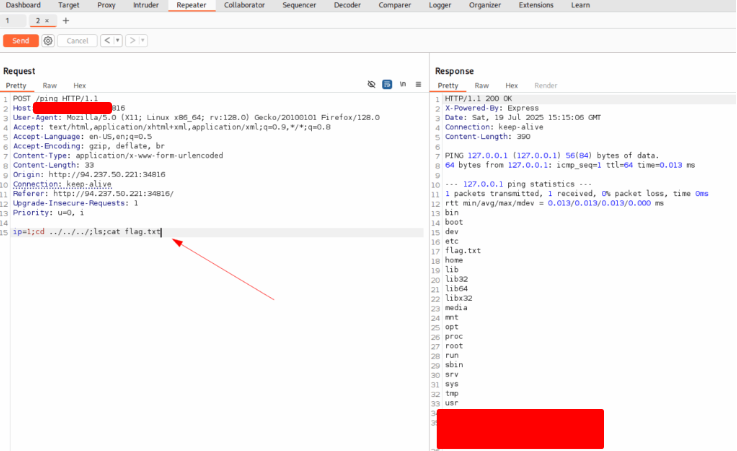
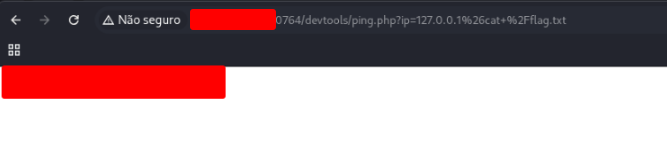
Try intercepting the ping request on the server shown above, and change the post data similarly to what we did in this section. Change the command to read ‘flag.txt’
Open the site and the burp suite. And intercept the request. Send it to the Repeater tab.
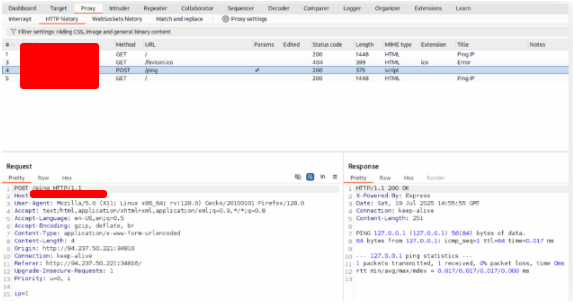
Change the ip parameter and send the request. You’ll find the content of the file.
ls; cat flag.txt;

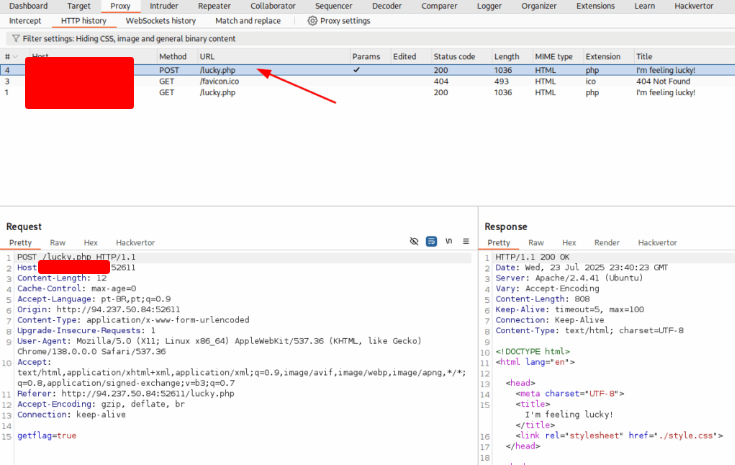
Repeating Requests
Previously, we bypassed input validation to execute a command injection on the remote server. To run a different command, we’d have to intercept the request again, supply a new payload, forward it, and then check the browser for the result.
As you can imagine, repeating this process for every command would be tedious—each action could take 5–6 steps to execute. That’s where request repeating comes in.
Request repeating lets us resend any web request that has already passed through the proxy. This way, we can quickly tweak a request, forward it, and receive the response directly in our tools—without intercepting and modifying every single request manually. It’s a huge time-saver for repetitive testing tasks.
Try using request repeating to be able to quickly test commands. With that, try looking for the other flag.
Change the parameter again to get the flag file.
Encoding/Decoding
When we modify and send custom HTTP requests, it’s often necessary to encode or decode data so that the web server interprets it correctly. Both Burp Suite and OWASP ZAP come with built-in encoders and decoders, allowing us to quickly transform text into the proper format—or reverse it—without leaving the tool.
This feature is especially useful when dealing with URL encoding, Base64, HTML entities, or other formats commonly used in web applications. Using these built-in tools ensures our requests are correctly interpreted and reduces the chance of errors during testing.
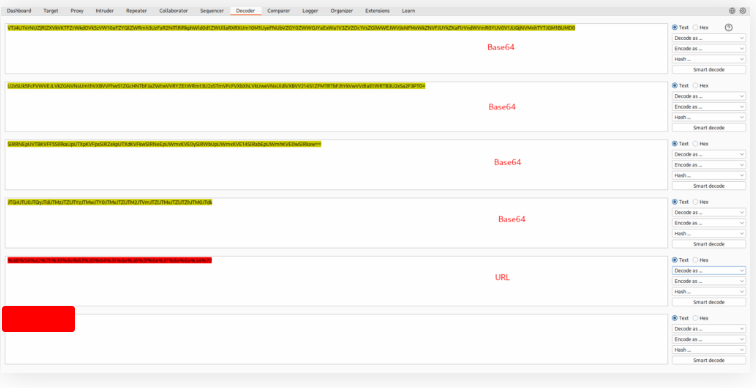
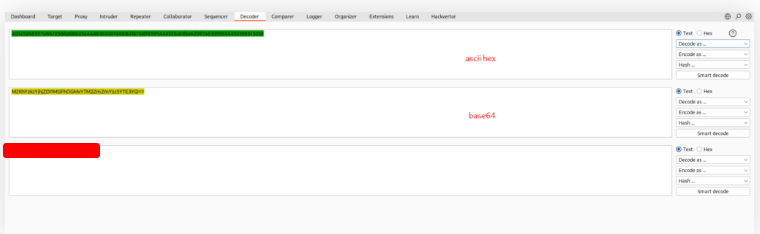
The string found in the attached file has been encoded several times with various encoders. Try to use the decoding tools we discussed to decode it and get the flag.
Download the file and use the Burp Decoder
Proxying Tools
One of the most powerful features of web proxies is the ability to intercept web requests made not just by browsers, but also by command-line tools and thick client applications. This allows us to see exactly what these applications are sending over the network and lets us leverage all the proxy features we’ve used with web applications.
To route traffic through a web proxy, we configure the tool to use it as its proxy server—for example, http://127.0.0.1:8080, just like we did with our browsers. Each application may have a slightly different method for setting its proxy, so a little investigation is usually required.
In this section, we’ll go through some examples showing how to use Burp Suite or OWASP ZAP to intercept requests from these tools. The setup process is the same for both proxies, giving us flexibility no matter which one we choose.
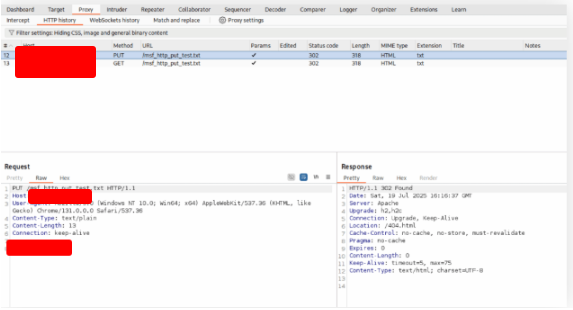
Try running ‘auxiliary/scanner/http/http_put’ in Metasploit on any website, while routing the traffic through Burp. Once you view the requests sent, what is the last line in the request?
Edit the file on /etc/proxychains.conf
#socks4 127.0.0.1 9050
http 127.0.0.1 8080
Execute msfconsole and use auxiliary/scanner/http/http_put.
$ msfconsole
Metasploit tip: Save the current environment with the save command,
future console restarts will use this environment again
https://metasploit.com
=[ metasploit v6.4.69-dev ]
+ -- --=[ 2529 exploits - 1302 auxiliary - 432 post ]
+ -- --=[ 1672 payloads - 49 encoders - 13 nops ]
+ -- --=[ 9 evasion ]
Metasploit Documentation: https://docs.metasploit.com/
msf6 > set PROXIES HTTP:127.0.0.1:8080
PROXIES => HTTP:127.0.0.1:8080
msf6 > use auxiliary/scanner/http/http_put
[*] Using action PUT - view all 2 actions with the show actions command
msf6 auxiliary(scanner/http/http_put) > show options
Module options (auxiliary/scanner/http/http_put):
Name Current Setting Required Description
---- --------------- -------- -----------
ACTION PUT yes PUT or DELETE
FILEDATA msf_test_file no The data to upload into the file
FILENAME msf_http_put_test.txt yes The file to attempt to write or delete
PATH / yes The path to attempt to write or delete
Proxies HTTP:127.0.0.1:8080 no A proxy chain of format type:host:port[,type:host:port][,…]. Supported proxies: sanni, socks4, socks4s, socks5, socks5h, http
RHOSTS 162.241.203.150 yes The target host(s), see https://docs.metasploit.com/docs/using-metasploit/basics/using-metasploit.html
RPORT 80 yes The target port (TCP)
SSL false no Negotiate SSL/TLS for outgoing connections
THREADS 1 yes The number of concurrent threads (max one per host)
VHOST no no HTTP server virtual host
Auxiliary action:
Name Description
---- -----------
PUT Upload local file
View the full module info with the info, or info -d command.
msf6 auxiliary(scanner/http/http_put) > set RHOSTS 162.241.203.150
RHOSTS => 162.241.203.150
msf6 auxiliary(scanner/http/http_put) > run
[-] 162.241.203.150: File doesn't seem to exist. The upload probably failed
[] Scanned 1 of 1 hosts (100% complete) [] Auxiliary module execution completed
msf6 auxiliary(scanner/http/http_put) >
After that, go back to your Burp Suite.
Burp Intruder
While Burp Suite and OWASP ZAP are best known as web proxies, they offer a lot more than just intercepting traffic. Two of their most valuable features for penetration testers are web fuzzers and web scanners.
The built-in web fuzzers act as comprehensive tools for fuzzing, enumeration, and brute-forcing, and can even replace many command-line tools like ffuf, dirbuster, gobuster, or wfuzz.
In Burp Suite, the web fuzzer is called Burp Intruder. It can fuzz pages, directories, subdomains, parameters, and parameter values, giving testers fine-grained control over their attacks. While incredibly powerful, the free Community version limits speed to 1 request per second—much slower than CLI-based fuzzers, which can send thousands of requests per second. This makes the free version suitable only for short or targeted queries.
The Pro version, on the other hand, removes these speed limits and adds advanced features, making Burp Intruder one of the most effective web fuzzing and brute-forcing tools available.
In this section, we’ll explore practical examples of how to use Burp Intruder for web fuzzing and enumeration.
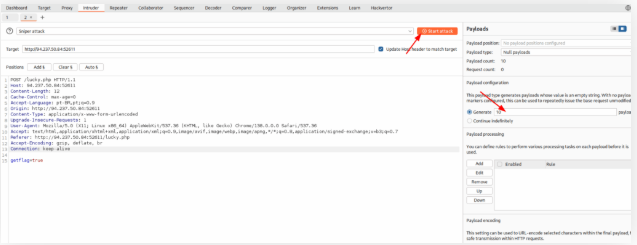
Use Burp Intruder to fuzz for ‘.html’ files under the /admin directory, to find a file containing the flag.
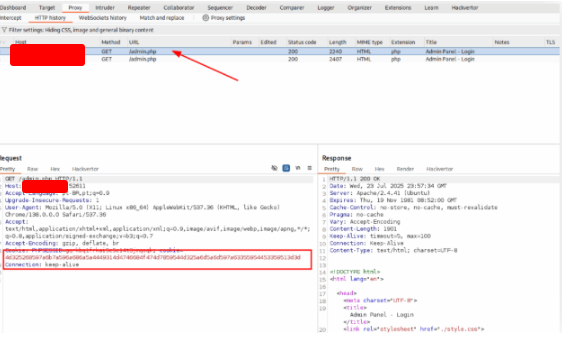
Open the browser and intercept the request with burp
Right click and send it to Intruder. Replace the get command and insert a position. Select the list Filenames – long and Start the Attack.
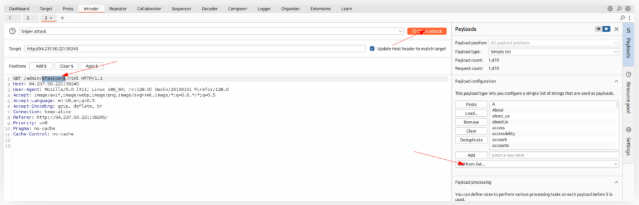
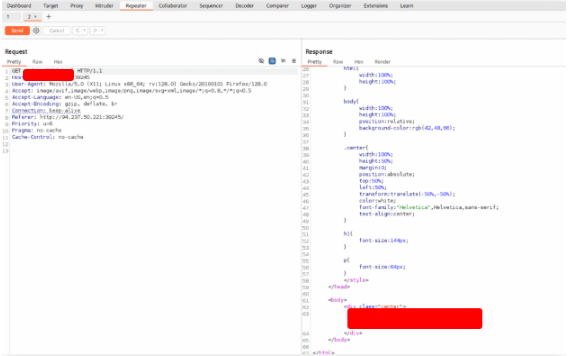
Find the status 200. Right click on it and send it to Repeater
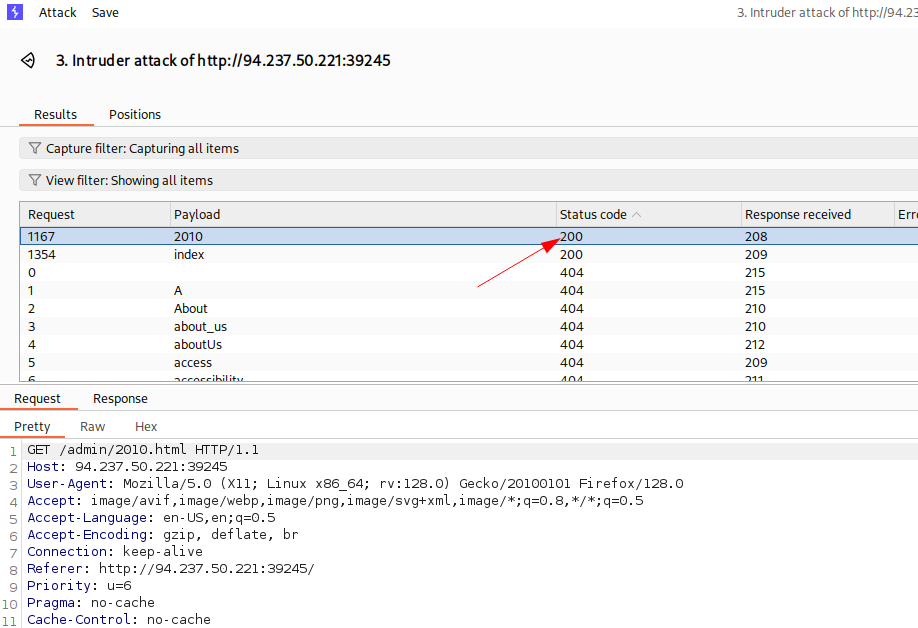
Send the request and get the flag.
ZAP Fuzzer
OWASP ZAP also comes equipped with its own web fuzzing tool, aptly named ZAP Fuzzer. While it may not offer all the advanced features of Burp Intruder, it makes up for it in speed: unlike the free version of Burp, ZAP Fuzzer does not throttle requests, making it an excellent choice for high-speed fuzzing tasks.
In this section, we’ll replicate the web fuzzing exercises we performed with Burp Intruder using ZAP Fuzzer. This “apples-to-apples” comparison will help you evaluate which tool fits your workflow best, balancing features, speed, and ease of use.
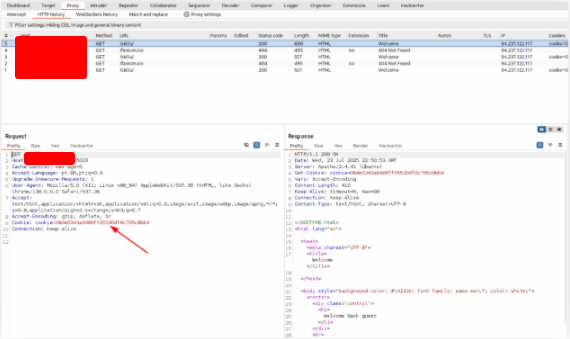
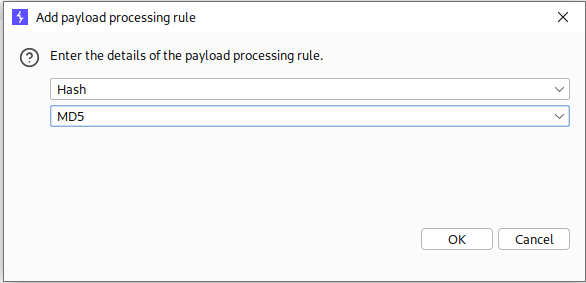
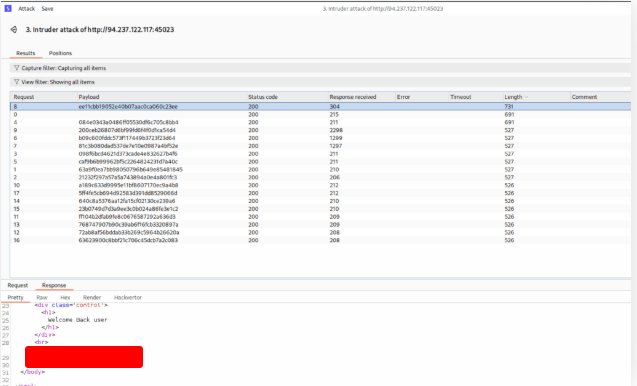
The directory we found above sets the cookie to the md5 hash of the username, as we can see the md5 cookie in the request for the (guest) user. Visit ‘/skills/’ to get a request with a cookie, then try to use ZAP Fuzzer to fuzz the cookie for different md5 hashed usernames to get the flag. Use the “top-usernames-shortlist.txt” wordlist from Seclists.
Start the lab and access the page 2x. After see the message “Welcome Back guest”, go to the burp suite.
Now we need to discover, what type of hash is this.
$ hash-identifier 084e0343a0486ff05530df6c705c8bb4
###############################################################
# #
# _ _ _ _ ____ ____ ____ ____ _ _ #
# | | | | _ _ | | | | | _ \ / ___| / ___| / ___|| || | #
# | |_| | | || | | |_| | | | | || | _ \___ \| | _ | || |_#
# | _ | | __ | | _ | | |_| || |_| | ___) | |_| ||__ _|
# |_| |_| |_| |_| |_| |_| |____/ \____| |____/ \____| |_| #
# #
# Hash ID v1.2 #
# By Zion3R #
# www.Blackploit.com #
# Root@Blackploit.com #
# #
###############################################################
Possible Hashes:
[+] MD5
[+] Domain Cached Credentials - MD4(MD4(($pass)).(strtolower($username)))
Least Possible Hashes:
[+] RAdmin v2.x
[+] NTLM
[+] MD4
[+] MD2
[+] MD5(HMAC)
[+] MD4(HMAC)
[+] MD2(HMAC)
[+] MD5(HMAC(WordPress))
[+] Haval-128
[+] Haval-128(HMAC)
[+] RipeMD-128
[+] md5(md5($salt).$pass)
[+] md5(md5($salt).md5($pass))
[+] md5(md5($username.$pass).$salt)
[+] md5(md5($pass))
[+] md5(md5(md5($pass)))
[+] md5(md5(md5(md5($pass))))
[+] md5(sha1($pass))
[+] md5(sha1(md5($pass)))
[+] md5(sha1(md5(sha1($pass))))
[+] md5(strtoupper(md5($pass)))
HASH: 084e0343a0486ff05530df6c705c8bb4
Possible Hashes:
[+] MD5
[+] Domain Cached Credentials - MD4(MD4(($pass)).(strtolower($username)))
We discovered that it’s a MD5. Right click on it and choose Send to Intruder. Configure the Intruder choosing the list:
/usr/share/seclists/Usernames/top-usernames-shortlist.txt
And add a payload to convert the user in md5
Start the attack and you will find the answer.
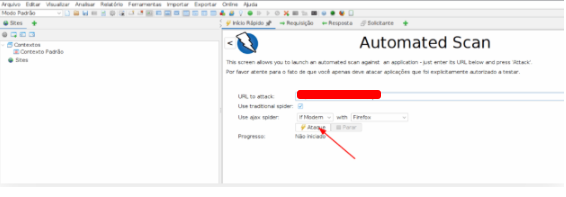
ZAP Scanner
OWASP ZAP also includes a Web Scanner that functions similarly to Burp Scanner. It can automatically build a site map using the ZAP Spider, and perform both passive and active scans to detect a wide range of vulnerabilities. This makes ZAP a powerful all-in-one tool for web application security testing.
Run ZAP Scanner on the target above to identify directories and potential vulnerabilities. Once you find the high-level vulnerability, try to use it to read the flag at ‘/flag.txt’
Start the attack on the Zap
When finish, you will find the vulnerability
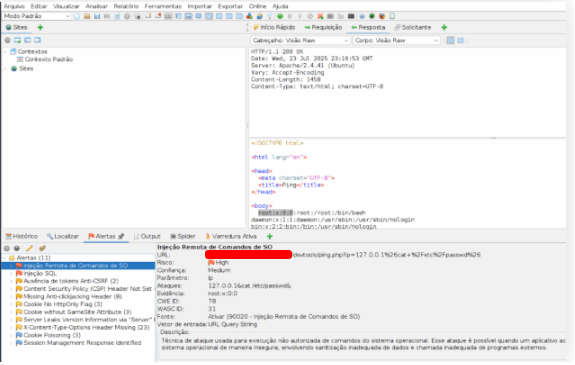
Now it’s easy, just explore on the browser
Skills Assessment – Using Web Proxies
During an internal penetration test for a local company, you’ll often encounter web applications with varying behaviors and protections. In these situations, tools like Burp Suite and OWASP ZAP can become indispensable.
For each scenario, evaluate the specific features of your chosen proxy tool—such as intercepting requests, fuzzing parameters, scanning for vulnerabilities, or replaying requests—and determine which feature is most effective for achieving the objective.
To get started, connect to Pwnbox, a web-based Parrot Linux instance provided for our labs. Pwnbox allows you to safely test and interact with the internal applications in a controlled environment.
Open the page on the browser. Right click on the page and choose inspector. Click on the button and erase the disabled property.
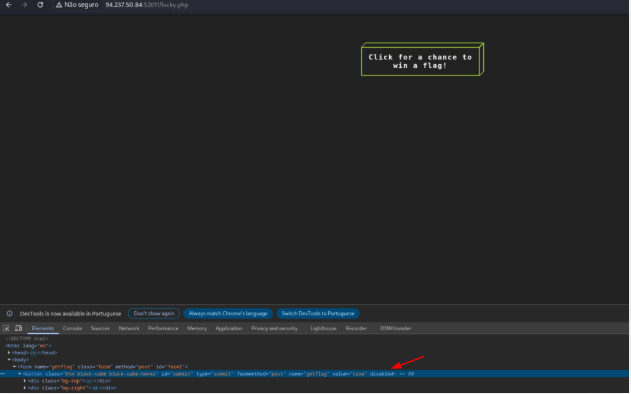
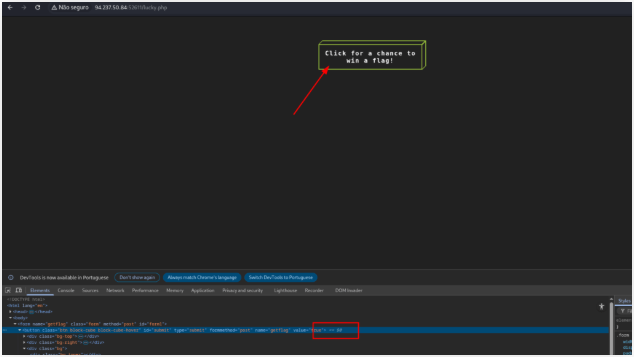
Click on the button and intercept the request on burp suite.
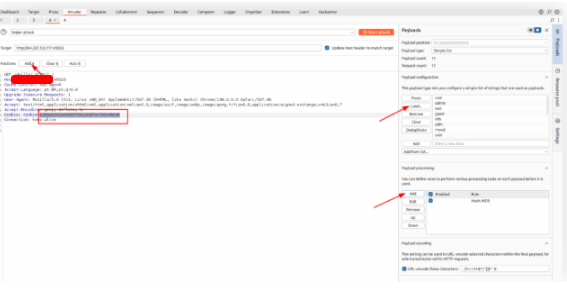
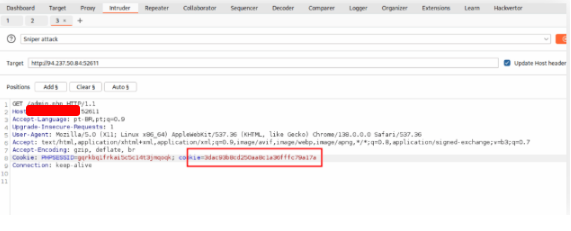
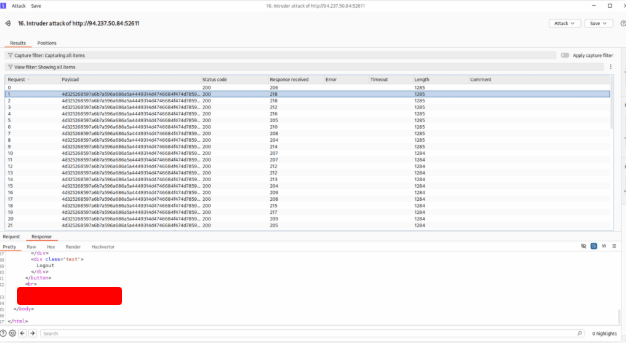
Right click on it and choose Send to Intruder.
Select the option Null Payloads and send 10 or more payloads. And you get the answer.
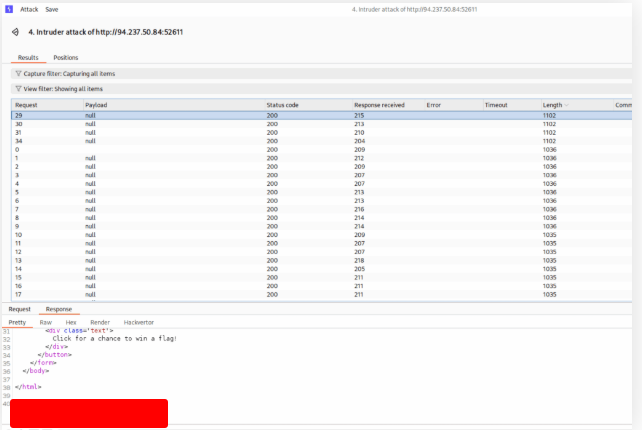
The /admin.php page uses a cookie that has been encoded multiple times. Try to decode the cookie until you get a value with 31-characters. Submit the value as the answer.
Open the page and intercept the request with burp.
Copy this value and decode in the Decode tab
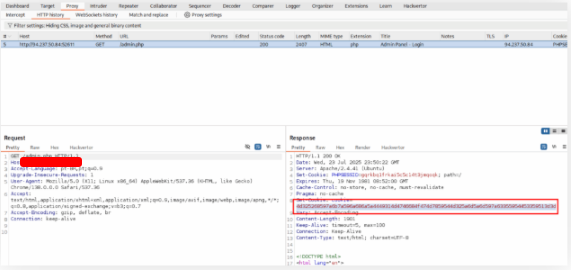
Once you decode the cookie, you will notice that it is only 31 characters long, which appears to be an md5 hash missing its last character. So, try to fuzz the last character of the decoded md5 cookie with all alpha-numeric characters, while encoding each request with the encoding methods you identified above. (You may use the “alphanum-case.txt” wordlist from Seclist for the payload)
Access the page 2x and intercept the second request using burp. Right click and click on Send to intruder.
Replace the cookie for the cookie that we discovered in the last exercise.
Read the list above, and inset the payload Base64 decode and Enconde as ASCII64 hex
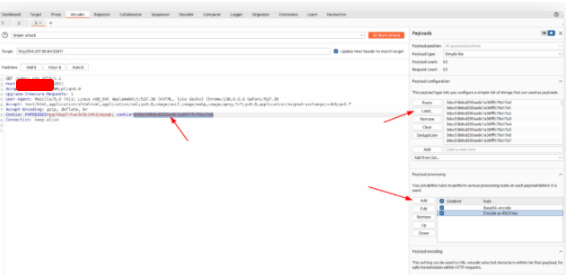
The list that I used
3dac93b8cd250aa8c1a36fffc79a17a0
3dac93b8cd250aa8c1a36fffc79a17a1
3dac93b8cd250aa8c1a36fffc79a17a2
3dac93b8cd250aa8c1a36fffc79a17a3
3dac93b8cd250aa8c1a36fffc79a17a4
3dac93b8cd250aa8c1a36fffc79a17a5
3dac93b8cd250aa8c1a36fffc79a17a6
3dac93b8cd250aa8c1a36fffc79a17a7
3dac93b8cd250aa8c1a36fffc79a17a8
3dac93b8cd250aa8c1a36fffc79a17a9
3dac93b8cd250aa8c1a36fffc79a17aa
3dac93b8cd250aa8c1a36fffc79a17ab
3dac93b8cd250aa8c1a36fffc79a17ac
3dac93b8cd250aa8c1a36fffc79a17ad
3dac93b8cd250aa8c1a36fffc79a17ae
3dac93b8cd250aa8c1a36fffc79a17af
3dac93b8cd250aa8c1a36fffc79a17ag
3dac93b8cd250aa8c1a36fffc79a17ah
3dac93b8cd250aa8c1a36fffc79a17ai
3dac93b8cd250aa8c1a36fffc79a17aj
3dac93b8cd250aa8c1a36fffc79a17ak
3dac93b8cd250aa8c1a36fffc79a17al
3dac93b8cd250aa8c1a36fffc79a17am
3dac93b8cd250aa8c1a36fffc79a17an
3dac93b8cd250aa8c1a36fffc79a17ao
3dac93b8cd250aa8c1a36fffc79a17ap
3dac93b8cd250aa8c1a36fffc79a17aq
3dac93b8cd250aa8c1a36fffc79a17ar
3dac93b8cd250aa8c1a36fffc79a17as
3dac93b8cd250aa8c1a36fffc79a17at
3dac93b8cd250aa8c1a36fffc79a17au
3dac93b8cd250aa8c1a36fffc79a17av
3dac93b8cd250aa8c1a36fffc79a17aw
3dac93b8cd250aa8c1a36fffc79a17ax
3dac93b8cd250aa8c1a36fffc79a17ay
3dac93b8cd250aa8c1a36fffc79a17az
3dac93b8cd250aa8c1a36fffc79a17aA
3dac93b8cd250aa8c1a36fffc79a17aB
3dac93b8cd250aa8c1a36fffc79a17aC
3dac93b8cd250aa8c1a36fffc79a17aD
3dac93b8cd250aa8c1a36fffc79a17aE
3dac93b8cd250aa8c1a36fffc79a17aF
3dac93b8cd250aa8c1a36fffc79a17aG
3dac93b8cd250aa8c1a36fffc79a17aH
3dac93b8cd250aa8c1a36fffc79a17aI
3dac93b8cd250aa8c1a36fffc79a17aJ
3dac93b8cd250aa8c1a36fffc79a17aK
3dac93b8cd250aa8c1a36fffc79a17aL
3dac93b8cd250aa8c1a36fffc79a17aM
3dac93b8cd250aa8c1a36fffc79a17aN
3dac93b8cd250aa8c1a36fffc79a17aO
3dac93b8cd250aa8c1a36fffc79a17aP
3dac93b8cd250aa8c1a36fffc79a17aQ
3dac93b8cd250aa8c1a36fffc79a17aR
3dac93b8cd250aa8c1a36fffc79a17aS
3dac93b8cd250aa8c1a36fffc79a17aT
3dac93b8cd250aa8c1a36fffc79a17aU
3dac93b8cd250aa8c1a36fffc79a17aV
3dac93b8cd250aa8c1a36fffc79a17aW
3dac93b8cd250aa8c1a36fffc79a17aX
3dac93b8cd250aa8c1a36fffc79a17aY
3dac93b8cd250aa8c1a36fffc79a17aZStart the attack and get the flag
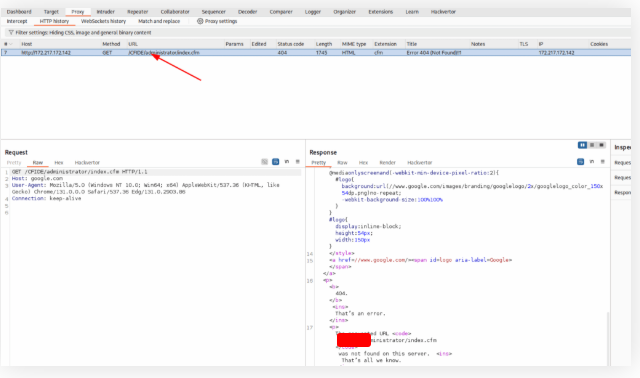
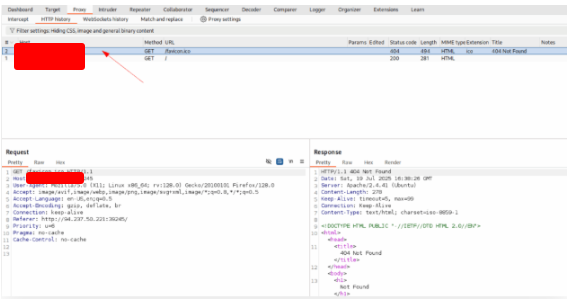
You are using the ‘auxiliary/scanner/http/coldfusion_locale_traversal’ tool within Metasploit, but it is not working properly for you. You decide to capture the request sent by Metasploit so you can manually verify it and repeat it. Once you capture the request, what is the ‘XXXXX’ directory being called in ‘/XXXXX/administrator/..’?
Open msfconsole.
$ msfconsole
Metasploit tip: Search can apply complex filters such as search cve:2009 type:exploit, see all the filters with help search
*Neutrino_Cannon*PrettyBeefy*PostalTime*binbash*deadastronauts*EvilBunnyWrote*L1T*Mail.ru*() { :;}; echo vulnerab
*Team sorceror*ADACTF*BisonSquad*socialdistancing*LeukeTeamNamaq*OWASP Moncton*Alegori*exit*Vampire Bunnies*APT59
*QuePasaZombiesAndFriends*NetSecBG*coincoin*ShroomZ*Slow Coders*Scavenger Security*Bruh*NoTeamName*Terminal_Cuti
*redspiner*BFG*MagentaHats*0x01DA*Kaczuszki*AlphaPwners*FILAAH*aRaffaela*HackSurVyette*outout*HackSouth*Corakay*yeeb
**SKUACy0ber_COBRA*flaghuntersx*0xCDAI_Generated*CSec*p3nnm3d*ITFs*CTF_Circle*InnotecLabs*baadf00d*BIkSwitchers*0x
*ItPwns - Intergalactic Team of PWNers*PCCsquared*fr334laks*runrCMD+0x194*Kapital Krakens*ReadyPlayer1337*Team 443
*H4CKSN0W*Inf0s3c*CTF_Community*DC2ia*NiceWay*0xBlueSky*Me3k*Pipi*Hack*Porg_Pwn_Platoon*Hackertyx*hackersteeboys*
*ideaginen0007*eggcellent*H4xCw167*localhorts*Original Cyan Lonkero*Sad_Pandas*FalseFlag*OurHeartBleedsOrange*
*Cult of the Dead Turkey*doesthismatter*crayontheft*Cyber Mausoleum*scripterz*VetSec*norbot*Delta Squad Zero*Mukee
*x00-x00*BlackCat*AREsx*cpx*vaporsec*purplehax*RedTeam@MTU*UsalamaTeam*vitamin*K*RISC*forkbomb44x*hownbrowncown
*etherknot*cheseebaguette*todowngrade*FRI3ND5*badfirmware*Cut3Dr4wg0n*dcc615*nora*Polaris One*team+hail_hack*Takoyal
*$udo_Society*incognito-flash*TheScientists*Tea Party*Reapers of Pwnage*OldBoys*MoUl3Fr1t1B13r3*bearsiwithsaws*DCT
*iMosuke*Infosec_zitr0*CrackTheFlag*TheConquerors*Asur*4xFang*Rogue-CTF*CyberxTMHC*The_Pirhacks*btwIsueArch*MadDawgs*
*HInc*The Pighty Mangolins*CCSF_RamSec*x4n0n*x0rc3r3rs*emehacr*Ph4n70m_R34p3r*humziq*Preeminence*UMGC*ByteBrigade*
*TeamFastmark*Towson-Cyberkata*new0x*rzhev*PA Hackers*Kuleolma*Nakateam*L0g!c_B0mb*NOVA-Infosec*teamstyle*Panic*
*B0NG0R3*
*Les Tontons FL4guerS*
*' UNION SELECT 'password'*
*burner_herz0g*
*here_there_be_trolls*
*rt4s_6rung4nd4*NYUSEC*
*Ikasten10*TWc*balkansec*
*TofuElRoll*Trash_Pandas*
*Astra*Got Schwartz?*tmux*
*\nIs*Juicy white peach*
*HackerKnights*
*Pentest Rangers*
*placeholder name*bitup*
*UQASers*onotch*
*NeNiNuMmOk*
*Maux de tête*LalaNG*
*crr0t2z3r0p0r*clueless*
*HackWara*
*Kugelschreibertester*
*icemasters*
____ ____ _ _ ____ _ __ __ ___
/ ___|| _ \| | | |/ ___| / \ | \/ |/ _ \
\___ \| |_) | | | | | / _ \ | |\/| | | | |
___) | _ <| |_| | |___ / ___ \| | | | |_| |
|____/|_| \_\\___/ \____/_/ \_\_| |_|\___/
Capture
The
Flag
*404 : Flag Not Found*
*OCD247*Sparkle Pony*
*KillShot*ConEmu*
*echo"hacked"*
*karamel4e*
*cybersecurity.li*
*OneManArmy*cyb3r_w0lf*
*AreYouStuck*Mr.Robot*
*EPITA Rennes*
*guildOfGengar*Trite*
*The Libbyrators*
*JeffTadashi*Mikelar*
*ky_dong_day_song*
*JustForFun!*
*g3tsh3LLs0on*
*Phở Đặc Biệt*Paradox*
*KaRIPux*infoSec*
*bluehens*Antoine77*
*genxy*TRADE_NAMES*
Configure the exploit.
=[ metasploit v6.4.64-dev ]
+ -- --=[ 2519 exploits - 1296 auxiliary - 431 post ]
+ -- --=[ 1610 payloads - 49 encoders - 13 nops ]
+ -- --=[ 9 evasion ]
Metasploit Documentation: https://docs.metasploit.com/
msf6 > use auxiliary/scanner/http/coldfusion_locale_traversal
msf6 auxiliary(scanner/http/coldfusion_locale_traversal) > set RHOST google.com
RHOSTS => google.com
msf6 auxiliary(scanner/http/coldfusion_locale_traversal) > set RPORT 80
RPORT => 80
msf6 auxiliary(scanner/http/coldfusion_locale_traversal) > set PROXIES HTTP:127.0.0.1:8080
PROXIES => HTTP:127.0.0.1:8080
msf6 auxiliary(scanner/http/coldfusion_locale_traversal) > run
[*] Scanned 1 of 2 hosts (50% complete)
[*] Scanned 2 of 2 hosts (100% complete)
[*] Auxiliary module execution completed
msf6 auxiliary(scanner/http/coldfusion_locale_traversal) >
set RHOST google.com
set RPORT 80
set PROXIES HTTP:127.0.0.1:8080
Intercept the request on Burp and get the flag.