Step 1 -> Asset Discovery (Domains & Subdomains)
Tools: Subfinder + DNSx
# Find subdomains and resolve them
subfinder -d target.com -o subdomains.txt
dnsx -l subdomains.txt -a -resp-only -o resolved.txt
Use shosubgo to extract subdomains from Shodan.
Step 2 -> Probing & Port Scanning
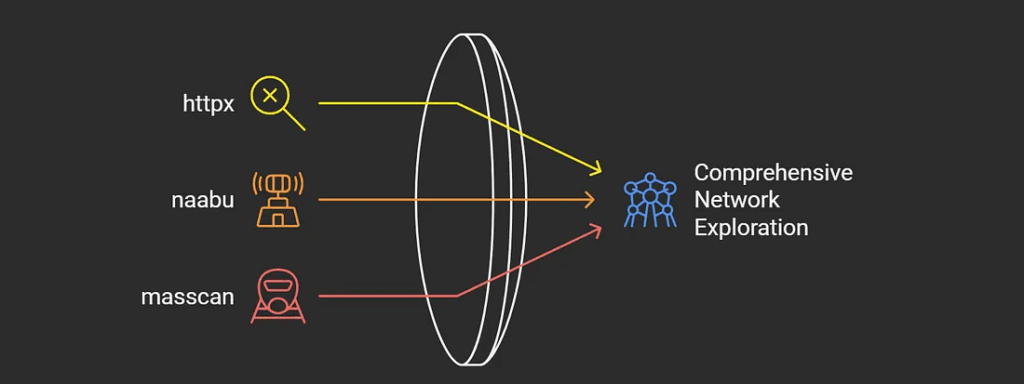
Tools: Naabu + Httpx
naabu -l resolved.txt -p -top-1000 -o ports.txt
httpx -l resolved.txt -title -tech-detect -status-code -o livehosts.txt
Add -web-server in httpx to fingerprint web servers.
Step 3 -> Tech Stack & Framework Detection
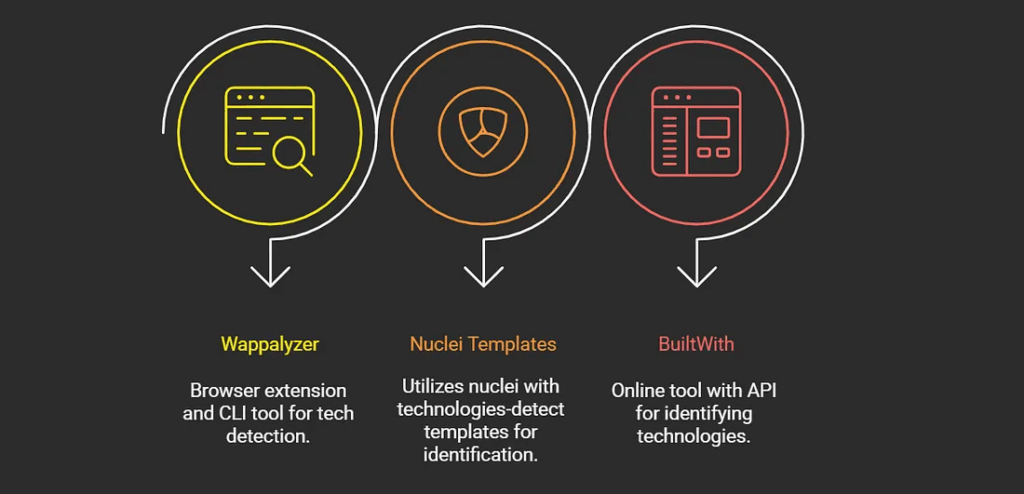
Why? Knowing whether the app runs WordPress, Laravel, NGINX, Apache, etc. helps you focus on relevant attack vectors.
Step 4 -> Crawl & Endpoint Discovery
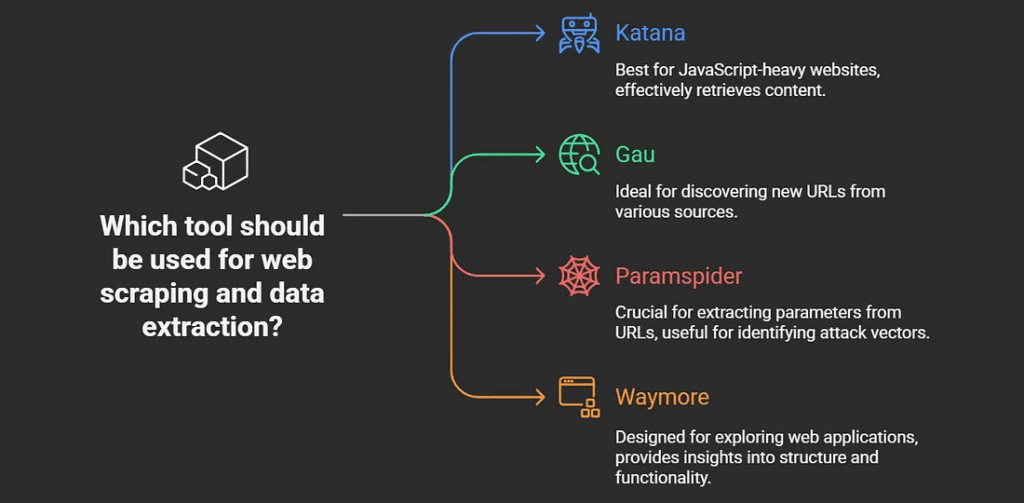
Tools: Katana + Gau
katana -u https://target.com -js-crawl -o endpoints.txt
gau target.com | tee gau.txt
Combine outputs and filter for unique parameters.
Step 5 -> Parameter & Secret Hunting
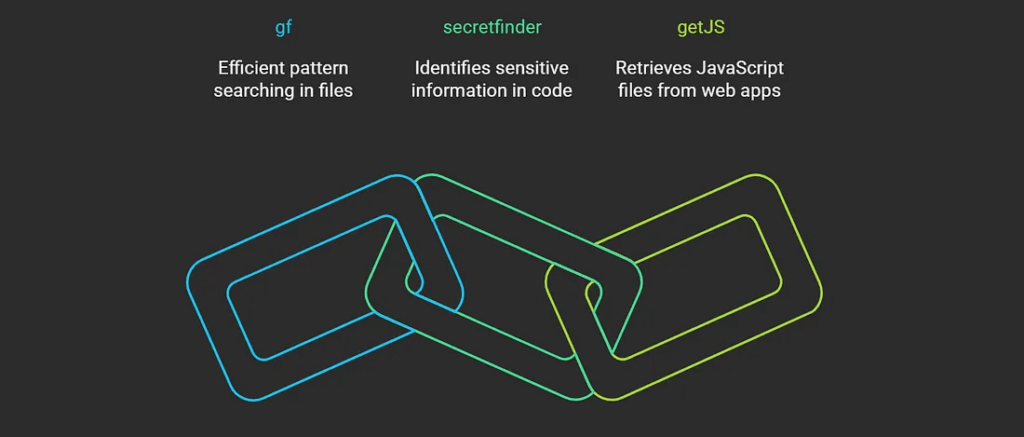
Tools: GF Patterns
# Extract juicy parameters
gf xss gau.txt > xss-params.txt
👉 Look for parameters like: redirect=, url=, file=, callback= – these are often goldmines.
Step 6 -> JavaScript Recon
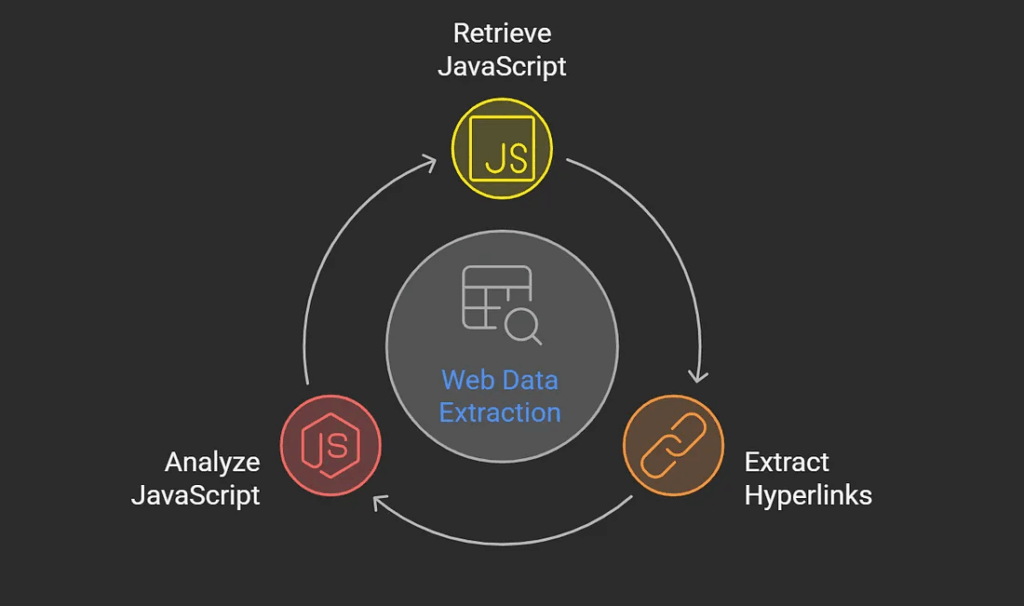
Tool: GetJS
getJS --url https://target.com --output jsurls.txt
Inside JavaScript you might find:
- API endpoints
- Secrets/tokens
- Internal links
- Hidden paths
Step 7 -> CDN, WAF, and DNS Intel
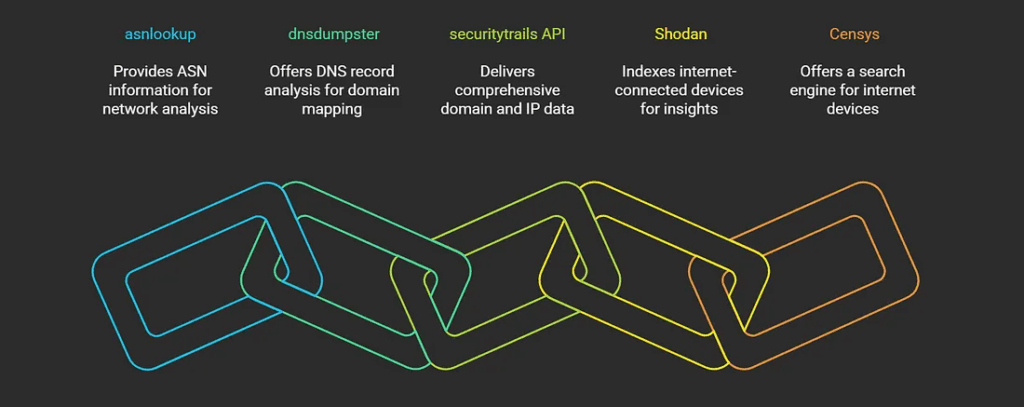
Understanding CDN/WAF configurations helps you:
- Confirm if requests reach the origin server.
- Plan rate-limit bypasses.
- Detect misconfigured edge services.
Advanced Recon & Automation
Once you master the basics, you can scale your recon with automation + AI-powered fingerprinting.
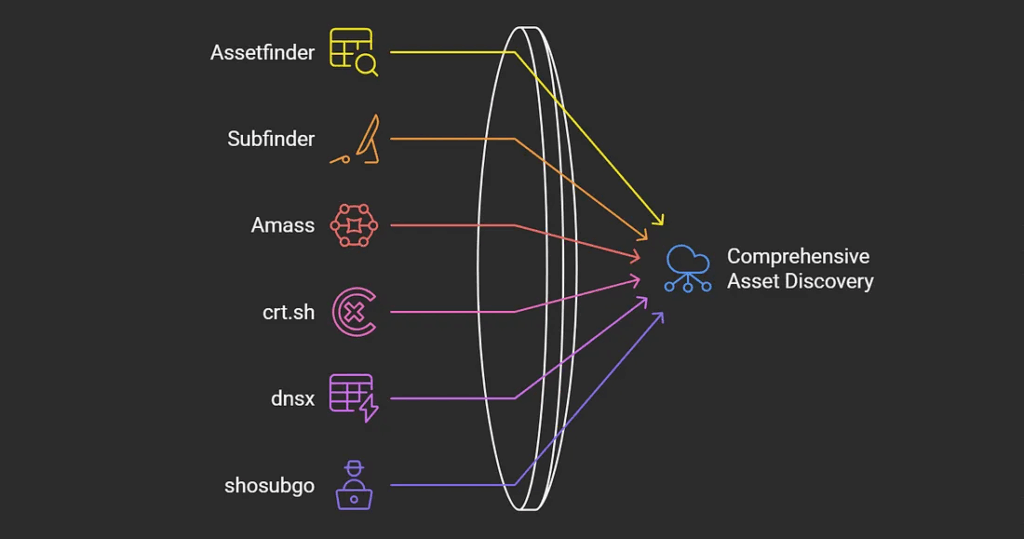
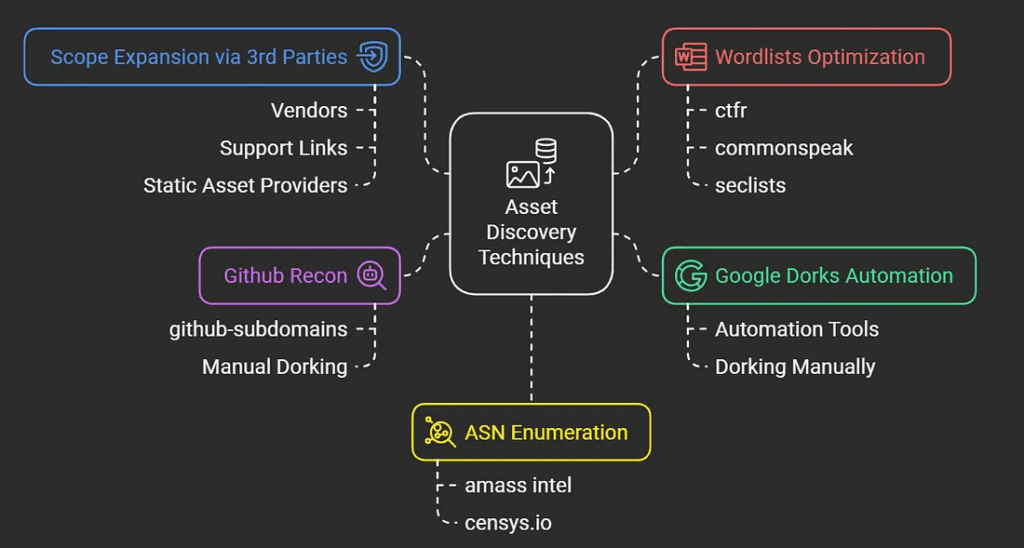
Advanced Asset Discovery
# Parallel subdomain enumeration
subfinder -d target.com -silent | anew subs.txt
assetfinder -subs-only target.com | anew subs.txt
amass enum -passive -d target.com | anew subs.txt
curl -s "https://crt.sh/?q=%25.target.com&output=json" | jq -r '.[].name_value' | anew subs.txt
# Filter CDNs/WAFs
dnsx -l subs.txt -resp -silent | grep -ivf cdn_providers.txt | anew resolved.txt
Pro Tools: Chaos, Shodan, Commonspeak2
ReconX: Automation Script Example
Here’s a simple automation script that combines multiple steps into one flow:
#!/bin/bash
# ReconX: Autonomous Recon Engine
target=$1
mkdir -p $target/{recon,js,cloud,exploits}
# Phase 1: Asset Mapping
subfinder -d $target -silent | anew $target/recon/subs.txt
amass enum -passive -d $target | httpx -jarm -asn | tee $target/recon/live_jarm.txt
nuclei -l $target/recon/live_jarm.txt -t ~/nuclei-templates/ -es info -o $target/recon/nuclei_tech.txt
# Phase 2: JS Intel
getJS --url-file $target/recon/live_jarm.txt --output $target/js/js_urls.txt
python3 SecretFinder.py -i $target/js/js_urls.txt -o $target/js/secrets.json
# Phase 3: Attack Surface Expansion
waymore -i $target -o $target/recon/waymore
gf xss $target/recon/waymore/waymore.txt | qsreplace -a | dalfox pipe --silence
This script helps you automate common recon steps and keeps your findings well-organized.
Final Thoughts
Reconnaissance isn’t about running a single command – it’s a process. The more disciplined and creative you are in mapping your target, the better your chances of finding high-value bugs.
Always remember: Tools don’t find bugs. Hackers do.