This module breaks down the penetration testing process into its individual stages, explaining each step in detail. We’ll explore the many responsibilities of a penetration tester during an engagement, with clear examples to illustrate real-world scenarios.
Additionally, the module covers pre-engagement steps, such as the criteria and considerations for establishing a contract with a client before starting a penetration test. This ensures both legal and professional standards are met before diving into the technical work.
Pre-Engagement
The pre-engagement stage is all about preparing for the actual penetration test. During this phase, critical questions are asked, and contractual agreements are put in place. The client shares what they want tested, while we provide guidance on how to maximize the efficiency and effectiveness of the test.
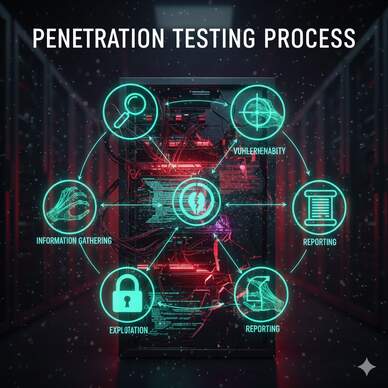
The penetration testing process generally follows these stages:
Pre-Engagement → Information Gathering → Vulnerability Assessment → Exploitation → Post-Exploitation → Lateral Movement → Proof-of-Concept → Post-Engagement
The pre-engagement process itself has three essential components:
- Scoping Questionnaire – Helps define the boundaries, goals, and priorities of the engagement.
- Pre-Engagement Meeting – A discussion to clarify expectations, rules of engagement, and technical details.
- Kick-Off Meeting – The official start, confirming all parties understand the plan and objectives.
Before diving into these steps, a Non-Disclosure Agreement (NDA) must be signed by all parties to protect sensitive information and ensure confidentiality.
How many documents must be prepared in total for a penetration test?
Here are the 7 documents that must be prepared during the pre-engagement phase of a penetration test:
Reports (produced during and after the test)
Non-Disclosure Agreement (NDA)
Scoping Questionnaire
Scoping Document
Penetration Testing Proposal (Contract / Scope of Work – SoW)
Rules of Engagement (RoE)
Contractors Agreement (required only if physical testing is included)
[REDACTED]
Vulnerability Assessment
During the vulnerability assessment phase, we take all the data collected in the information gathering stage and carefully analyze it. This phase is all about turning raw information into actionable insights.
The penetration testing process generally follows these stages:
Pre-Engagement → Information Gathering → Vulnerability Assessment → Exploitation → Post-Exploitation → Lateral Movement → Proof-of-Concept → Post-Engagement
At its core, analysis is a detailed examination of events or processes, identifying their origins and potential impact. With the right precautions and strategies, this knowledge can help prevent risks or even trigger defensive measures proactively.
Vulnerability assessment can be complex, because it involves considering many interdependent factors. In every analysis, we’re constantly balancing three perspectives: past (what has happened), present (what is happening), and future (what could happen). Understanding both the origin of a vulnerability and its potential consequences is critical for building a secure environment.
What type of analysis can be used to predict future probabilities?
Predictive analysis uses past and current data to forecast future outcomes.
It takes the results of descriptive (what happened) and diagnostic (why it happened) analysis and applies statistical or modeling techniques to estimate what is likely to happen next.
In penetration testing, predictive analysis helps us identify trends or potential security weaknesses before they are exploited, by recognizing patterns in system behavior, vulnerabilities, or configurations.
[Redacted]
Post-Exploitation
Once we’ve successfully exploited a target system during the Exploitation stage, the focus shifts to Post-Exploitation. Even here, we must consider whether to use Evasive Testing, just as we did earlier. However, being inside the system makes it much harder to avoid triggering alerts.
The goal of post-exploitation is to gather sensitive, security-relevant information from the target from a local perspective. It’s also the stage where we collect business-critical data, which often requires higher privileges than a standard user account.
Key components of Post-Exploitation include:
- Evasive Testing: Acting stealthily to avoid detection.
- Information Gathering: Deep diving into system data, configurations, and files.
- Pillaging: Collecting useful credentials, tokens, or other secrets.
- Vulnerability Assessment: Identifying weaknesses that can be leveraged further.
- Privilege Escalation: Gaining higher access levels on the target system.
- Persistence: Ensuring long-term access to the system if needed.
In essence, Post-Exploitation transforms access into actionable intelligence, helping us understand both the technical weaknesses and the business risks of a compromised system.
How many types of evasive testing are mentioned in this section?
Evasive, Hybrid Evasive, Non-Evasive
[Redacted]
What is the name of the security standard for credit card payments that a company must adhere to? (Answer Format: acronym)
- PCI stands for Payment Card Industry.
- DSS stands for Data Security Standard.
So, PCI-DSS = Payment Card Industry Data Security Standard.
This is the official security standard that companies must follow if they store, process, or transmit credit card information.
Its purpose is to protect cardholder data and reduce fraud by enforcing strong security controls.
[Redacted]
Post-Engagement
Just as there’s significant preparation before a penetration test officially begins, there’s also important work to do after all scans, exploitation, lateral movement, and post-exploitation activities are complete.
These post-engagement activities are often contractually required and help ensure that the test is properly closed out. While no two engagements are exactly alike, certain steps are generally followed to finalize the assessment, document findings, and provide actionable recommendations to the client.
In short, the post-engagement phase ensures that all loose ends are tied up, risks are communicated clearly, and the client receives the full value of the penetration test.
What designation do we typically give a report when it is first delivered to a client for a chance to review and comment? (One word)
- A Draft report is not final — it means the results are complete but open to feedback and clarification.
- The client may need to:
- verify technical details,
- ask questions,
- correct internal terminology,
- or provide additional context.
After this review and discussion, the pentester updates the document and then issues the FINAL version.
So:
| Stage | Report Designation | Purpose |
|---|---|---|
| First delivery | DRAFT | Allows client review, corrections, and comments |
| After review | FINAL | Official deliverable that may be used for audit or compliance |
[Redacted]