Introduction
Password cracking — the offline brute-force attacks you hear about — remains one of the most practical ways attackers gain unauthorized access. Many apps and systems hash or encrypt sensitive data so that plaintext passwords aren’t stored and intercepted credentials aren’t easily exposed during a man-in-the-middle. Password cracking tries to reverse that protection by repeatedly guessing inputs until the original password (cleartext) is recovered.
Why password cracking works
There are two big reasons these attacks often succeed:
- Weak or reused passwords. People pick easy or recycled passwords across sites, which makes hashes trivial to recover with modest effort.
- Targeted wordlists and mutation rules. Attackers tailor wordlists and apply rules (e.g., leetspeak, appended numbers, common suffixes) to mimic how real users create passwords, dramatically improving crack rates.
The toolbox: Hashcat and friends
A number of open-source utilities simplify offline cracking; Hashcat is one of the most widely used. It supports many hashing algorithms, is highly configurable (modes, dictionaries, rules, masks), and can leverage GPUs for massive parallelism. Because of its flexibility and performance, Hashcat is a staple for offensive and defensive practitioners alike.
Why every security pro should learn it
Understanding password cracking is invaluable whether you’re attacking (red team, pentester) or defending (blue team, incident responder):
- During assessments you’ll frequently obtain password hashes that block further progress unless cracked.
- Knowing effective cracking strategies lets you prioritize which accounts are most at risk and helps you show clients concrete remediation steps (stronger policies, salted hashes, MFA).
- Defenders benefit from knowing what attackers can realistically achieve so they can harden systems accordingly.
Mastering the techniques and tools — especially Hashcat — gives you a transferable skill set that applies across many areas of information security.
Hashing vs. Encryption
Hashing is the process of transforming data into a unique, fixed-length string. No matter the input size — a short phrase or a long file — the resulting hash is always the same length for a given algorithm. Importantly, hashing is a one-way function, meaning you cannot reverse a hash to recover the original plaintext.
Hashing has many uses:
- Integrity checks: Algorithms like MD5 and SHA-256 are commonly used to verify files haven’t been altered.
- Password storage: Functions like PBKDF2 ensure passwords aren’t stored in plaintext.
- Message verification: Keyed hashes such as HMAC add an extra layer of security, acting like a tamper-proof checksum during data transmission.
How attackers approach hashing
Since you can’t reverse a hash, the only option for attackers is to guess possible inputs. They generate hashes from wordlists or brute-force guesses and compare them with the original hash until they find a match.
Common password hashing algorithms on Unix
Unix-based systems (Linux, BSD, Solaris) use several algorithms to secure stored passwords:
- SHA-512 – A fast, efficient algorithm, but vulnerable to rainbow table attacks because of its speed.
- Blowfish – A symmetric cipher adapted for password protection. More secure than SHA-512 but slower.
- BCrypt – Intentionally slow, making brute force and rainbow table attacks much harder.
- Argon2 – The modern standard for password hashing. It consumes both time and memory, which drastically increases the cost for attackers. It’s widely regarded as one of the most secure options available today.
Strengthening hashes with salting
To resist brute-force attacks, systems add a salt — a random piece of data mixed with the plaintext before hashing. This ensures that even identical passwords produce different hashes, slowing down precomputed attacks like rainbow tables. While salting increases difficulty for attackers, it doesn’t eliminate brute-force attempts entirely.
Generate an MD5 hash of the password ‘HackTheDome123!’.
Open your terminal and use the command bellow:
$ echo -n 'HackTheDome123!' | md5sum
[REDACTED]
Create the XOR ciphertext of the password ‘opens3same’ using the key ‘academy’. (Answer format: \x00\x00\x00\….)
Use the commands bellow:
python3
>> from pwn import xor
>> xor("opens3same", "academy")
And get the flag.
$ python3
Python 3.13.7 (main, Aug 20 2025, 22:17:40) [GCC 14.3.0] on linux
Type "help", "copyright", "credits" or "license" for more information.
>>> from pwn import xor
>>> xor('opens3same', 'academy')
/home/usuario/.local/lib/python3.13/site-packages/pwnlib/util/fiddling.py:340: BytesWarning: Text is not bytes; assuming ASCII, no guarantees. See https://docs.pwntools.com/#bytes
>>> b'[REDACTED]'
Identifying Hashes
One of the easiest ways to identify a hashing algorithm is by looking at the length of the hash it produces. Most algorithms generate outputs of a fixed size. For example:
- A 32-character hash could point to algorithms like MD5 or NTLM.
- A 40-character hash is commonly associated with SHA-1.
- Longer outputs (like 64 or 128 characters) often indicate stronger algorithms such as SHA-256 or SHA-512.
Hash formats and storage conventions
Hashes aren’t always stored as raw strings — they may appear in specific formats that include salts or identifiers:
- hash:salt → A simple way to combine the hash with its salt value.
- Example:
2fc5a684737ce1bf7b3b239df432416e0dd07357:2014Here, the hash is a SHA-1 digest, and the salt is2014.
- Example:
- $id$salt$hash → A structured format used by many Unix/Linux systems.
- Example:
$6$vb1tLY1qiY$M.1ZCqKtJBxBtZm1gRi8Bbkn39KU0YJW1cuMFzTRANcNKFKR4RmAQVk4rqQQCkaJT6wXqjUkFcA/qNxLyqW.U/This string has three sections separated by$:- 6 → The id, which indicates the algorithm. In this case,
6stands for SHA-512. - vb1tLY1qiY → The salt.
- The long string that follows → The actual hashed value.
- 6 → The id, which indicates the algorithm. In this case,
- Example:
Common ID values in hash formats
Here are some frequently seen identifiers and the algorithms they represent:
- 1 → MD5
- 2a / 2y → BCrypt (Blowfish-based)
- 5 → SHA-256
- 6 → SHA-512
Identify the following hash: $S$D34783772bRXEx1aCsvY.bqgaaSu75XmVlKrW9Du8IQlvxHlmzLc
Go to your terminal and use the command bellow:
hashid '$S$D34783772bRXEx1aCsvY.bqgaaSu75XmVlKrW9Du8IQlvxHlmzLc'
$ hashid '$$$D34783772bRXE1aCsvY.bqgaaSu75XmVlKrW9Du8IQLvxHlmzLc'
Analyzing '$$$D34783772bRXE1aCsvY.bqgaaSu75XmVlKrW9Du8IQLvxHlmzLc'
[+] [REDACTED]
Hashcat Overview
Hashcat is one of the most widely used open-source tools for cracking passwords. You can fetch it directly from the project site (for example with wget) and unpack it on the command line with a tool like 7z. If you want to see everything it can do, run hashcat -h to display the full help.
Major releases have added significant features and hundreds of supported hash types. For example, the 6.x series introduced many performance boosts and dozens of new hash modes; at the time this was written there were over 320 supported algorithms. You’ll find prebuilt binaries for Windows and Unix/Linux on the Hashcat GitHub, or you can build it yourself from source if you prefer.
A quick note about package managers: Hashcat’s core team keeps the official repository up to date, but distribution packaging (like an apt package) is usually maintained by third parties. That means the safest way to get the newest release is directly from Hashcat’s GitHub. For this guide we’ll demonstrate using the version bundled with Pwnbox, which—at the time of writing—includes the latest stable release (6.1.1).
What is the hash mode of the hash type Cisco-ASA MD5?
Use the command bellow to get the flag:
$ hashcat -h | grep -i Cisco-ASA
[REDACTED] | Cisco-ASA MD5
Dictionary Attack
Hashcat supports five primary attack modes, each suited to different hash types and password complexities. The simplest — and surprisingly effective — is the dictionary attack. Many organizations still suffer from weak password policies, and users commonly choose simple, guessable words or phrases. A dictionary attack leverages curated lists of likely passwords to try to match a hash quickly and efficiently.
Because real-world passwords often follow predictable patterns, dictionary attacks frequently succeed. Industry analyses of millions of leaked credentials consistently show that people reuse short, easy-to-remember passwords. For example, SplashData’s annual lists of the most common passwords illustrate how predictable user choices remain, with the top entries typically being extremely common and insecure.
Crack the following hash using the rockyou.txt wordlist: 0c352d5b2f45217c57bef9f8452ce376
Use the command above to crack the hash and get the flag.
$ hashcat -a 0 -m 0 hash /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
hashcat (v6.2.6) starting
* Device #1: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
* Device #2: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
CUDA API (CUDA 12.4)
* Device #1: NVIDIA GeForce RTX 2060 SUPER, 7607/7967 MB, 34MCU
OpenCL API (OpenCL 3.0 CUDA 12.4.131) - Platform #1 [NVIDIA Corporation]
_________________________________________________________________
* Device #2: NVIDIA GeForce RTX 2060 SUPER,
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #2 [The pocl project]
_________________________________________________________________
* Device #3: cpu-haswell-AMD Ryzen 5 3400G with Radeon Vega Graphics, skipped
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x000000ffff mask, 262144 bytes, 5/13 rotates
Rules: 1
Optimizers applied:
* Zero-Byte
* Early-Skip
* Not-Iterated
* Raw-Loop
* Single-Hal
* Slow-Hash
* Raw-Hash
ATTENTION! Pure (unoptimized) backend kernels selected.
Pure kernels can crack longer passwords, but drastically reduce performance.
If you want to switch to optimized kernels, append -O to your commandline.
See the above message to find out about the exact limits.
Watchdog: Temperature abort trigger set to 90C
Host memory required for this attack: 597 MB
Dictionary cache hit:
* Filename..: /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
* Passwords.: 14344385
* Bytes.....: 139921510
* Keyspace..: 14344385
0c352d5b2f45217c57bef9f8452ce3f0:[REDACTED]
Using the Hashcat combination attack find the cleartext password of the following md5 hash: 19672a3f042ae1b592289f8333bf76c5. Use the supplementary wordlists shown at the end of this section.
Combination attack modes take two wordlists and concatenate entries from each to generate candidate passwords. This mirrors how many people create passwords by joining familiar words—examples like welcomehome or hotelcalifornia are common in the real world.
Why it works: users often believe that merging words makes a password stronger, but these patterns are predictable and easy to model. Combination mode targets that exact behavior, producing human-like guesses that simple dictionary attacks might miss.
When to use it
- After a basic dictionary run, to catch merged-word variants.
- In targeted tests where you have contextual wordlists (brand names, project terms, common phrases).
- As part of a layered cracking strategy combined with mangling rules (capitalization, number/symbol suffixes).
Pro tip: Pair combination mode with lightweight mangling (e.g., add 1, !, or capitalize the first letter) to cover realistic variations like WelcomeHome1 or hotelCalifornia!.
Using the Hashcat combination attack find the cleartext password of the following md5 hash: 19672a3f042ae1b592289f8333bf76c5. Use the supplementary wordlists shown at the end of this section.
Create the first wordlist named wordlist1
sunshine<br>happy<br>frozen<br>golden
Create the second wordlist named wordlist2
hello<br>joy<br>secret<br>apple
Insert the md5 hash into a file named hash
echo '19672a3f042ae1b592289f8333bf76c5' > hash
Use both lists to crack the md5 hash and get the flag.
$ hashcat -a 1 -m 0 hash wordlist1 wordlist2
hashcat (v6.2.6) starting
* Device #1: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
* Device #2: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
CUDA API (CUDA 12.4)
* Device #1: NVIDIA GeForce RTX 2060 SUPER, 7579/7967 MB, 34MCU
OpenCL API (OpenCL 3.0 CUDA 12.4.131) - Platform #1 [NVIDIA Corporation]
_________________________________________________________________
* Device #2: NVIDIA GeForce RTX 2060 SUPER, skipped
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #2 [The pocl project]
_________________________________________________________________
* Device #3: cpu-haswell-AMD Ryzen 5 3400G with Radeon Vega Graphics, skipped
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Dictionary cache built:
* Filename..: wordlist1
* Passwords.: 4
* Bytes.....: 29
* Keyspace..: 4
* Runtime...: 0 secs
Dictionary cache built:
* Filename..: wordlist2
* Passwords.: 4
* Bytes.....: 23
* Keyspace..: 4
* Runtime...: 0 secs
Hashes: 1 digests; 1 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Optimizers applied:
* Zero-Byte
* Early-Skip
* Not-Salted
* Not-Iterated
* Single-Hash
* Single-Salt
* Raw-Hash
ATTENTION! Pure (unoptimized) backend kernels selected.
Pure kernels can crack longer passwords, but drastically reduce performance.
If you want to switch to optimized kernels, append -O to your commandline.
See the above message to find out about the exact limits.
Watchdog: Temperature abort trigger set to 90c
Host memory required for this attack: 1474 MB
Dictionary cache hit:
* Filename..: wordlist1
* Passwords.: 4
* Bytes.....: 29
* Keyspace..: 16
The wordlist or mask that you are using is too small.
This means that hashcat cannot use the full parallel power of your device(s).
Unless you supply more work, your cracking speed will drop.
For tips on supplying more work, see: https://hashcat.net/faq/morework
Approaching final keyspace - workload adjusted.
19672a3f042ae1b592289f8333bf76c5:[REDACTED]
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 0 (MD5)
Hash.Target......: 19672a3f042ae1b592289f8333bf76c5
Time.Started.....: Sat Sep 20 15:10:23 2025 (0 secs)
Time.Estimated...: Sat Sep 20 15:10:23 2025 (0 secs)
Kernel.Feature...: Pure Kernel
Guess.Base.......: File (wordlist1), Left Side
Guess.Mod........: File (wordlist2), Right Side
Speed.#1.........: 70657 H/s (0.01ms) @ Accel:512 Loops:4 Thr:128 Vec:1
Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)
Progress.........: 16/16 (100.00%)
Rejected.........: 0/16 (0.00%)
Restore.Point....: 0/4 (0.00%)
Restore.Sub.#1...: Salt:0 Amplifier:0-4 Iteration:0-4
Candidate.Engine.: Device Generator
Candidates.#1....: sunshinehello -> goldenapple
Hardware.Mon.#1..: Temp: 46c Fan: 0% Util: 6% Core:1830MHz Mem:6801MHz Bus:8
Started: Sat Sep 20 15:10:18 2025
Stopped: Sat Sep 20 15:10:24 2025
Mask Attack
Mask attacks let you craft candidate passwords that follow a known pattern — ideal when you already have a solid guess about a password’s length, structure, or parts. Instead of blindly cycling through every possible string, a mask describes exactly which positions are fixed characters, which positions should be drawn from specific character sets (for example [a-z] or [A-Z0-9]), and which are filled by special placeholders. That focused approach drastically reduces the search space, speeds up cracking, and makes your attacks far more efficient and targeted.
You can build masks from literal characters, ranges (like ?l for lowercase or [0-9] for digits), or flexible placeholders that represent whole character classes or custom sets. Below are the most common and useful placeholders you’ll encounter — keep these in mind when designing masks for real-world password patterns:
• ?l — one lowercase letter (a–z)
• ?u — one uppercase letter (A–Z)
• ?d — one digit (0–9)
• ?s — one special symbol (e.g., !@#$%)
• ?a — any printable ASCII character (lowercase, uppercase, digits, symbols)
• ?b — custom byte, used for arbitrary byte values
Use these placeholders (alone or combined with literal characters and ranges) to precisely model likely passwords — for example, a corporate pattern like Admin2025! could be encoded and efficiently targeted with a mask rather than brute force.
Crack the following MD5 hash using a mask attack: 50a742905949102c961929823a2e8ca0. Use the following mask: -1 02 ‘HASHCAT?l?l?l?l?l20?1?d’
Copy the hash into a file named hash and use the command bellow to get the flag.
$ hashcat -a 3 -m 0 md5_mask_example_hash -1 2 'HASHCAT?l?l?l?l?l?l?20?1?d'
hashcat (v6.2.6) starting
* Device #1: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
* Device #2: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
CUDA API (CUDA 12.4)
* Device #1: NVIDIA GeForce RTX 2060 SUPER, 7579/7967 MB, 34MCU
OpenCL API (OpenCL 3.0 CUDA 12.4.131) - Platform #1 [NVIDIA Corporation]
_________________________________________________________________
* Device #2: NVIDIA GeForce RTX 2060 SUPER, skipped
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #2 [The pocl project]
_________________________________________________________________
* Device #3: cpu-haswell-AMD Ryzen 5 3400G with Radeon Vega Graphics, skipped
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Hash 'md5_mask_example_hash' : Token length exception
* Token length exception: 1/1 hashes
This error happens if the wrong hash type is specified, if the hashes are
malformed, or if input is otherwise not as expected (for example, if the
--username option is used but no username is present)
No hashes loaded.
Started: Sat Sep 20 15:19:33 2025
Stopped: Sat Sep 20 15:19:33 2025
(venv)─(suricato@kali)─[~/Documentos/LOCAL/Exercicios]
$ hashcat -a 3 -m 0 hash -1 02 'HASHCAT?l?l?l?l?l?l?20?1?d'
hashcat (v6.2.6) starting
* Device #1: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
* Device #2: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
CUDA API (CUDA 12.4)
* Device #1: NVIDIA GeForce RTX 2060 SUPER, 7604/7967 MB, 34MCU
OpenCL API (OpenCL 3.0 CUDA 12.4.131) - Platform #1 [NVIDIA Corporation]
_________________________________________________________________
* Device #2: NVIDIA GeForce RTX 2060 SUPER, skipped
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #2 [The pocl project]
_________________________________________________________________
* Device #3: cpu-haswell-AMD Ryzen 5 3400G with Radeon Vega Graphics, skipped
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Optimizers applied:
* Zero-Byte
* Early-Skip
* Not-Salted
* Not-Iterated
* Single-Hash
* Single-Salt
* Brute-Force
* Raw-Hash
ATTENTION! Pure (unoptimized) backend kernels selected.
Pure kernels can crack longer passwords, but drastically reduce performance.
If you want to switch to optimized kernels, append -O to your commandline.
See the above message to find out about the exact limits.
Watchdog: Temperature abort trigger set to 90c
Host memory required for this attack: 1474 MB
50a742905949102c961929823a2e8ca0:[REDACTED]
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 0 (MD5)
Hash.Target......: 50a742905949102c961929823a2e8ca0
Time.Started.....: Sat Sep 20 15:21:04 2025 (1 sec)
Time.Estimated...: Sat Sep 20 15:21:05 2025 (0 secs)
Kernel.Feature...: Pure Kernel
Guess.Mask.......: HASHCAT?l?l?l?l?l?l?20?1?d [16]
Guess.Charset....: -1 02, -2 Undefined, -3 Undefined, -4 Undefined
Guess.Queue......: 1/1 (100.00%)
Speed.#1.........: 51182.7 kH/s (5.95ms) @ Accel:4096 Loops:1 Thr:32 Vec:1
Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)
Progress.........: 44564480/237672520 (18.75%)
Rejected.........: 0/44564480 (0.00%)
Restore.Point....: 0/16 (0.00%)
Restore.Sub.#1...: Salt:0 Amplifier:0-1 Iteration:0-1
Candidate.Engine.: Device Generator
Candidates.#1....: HASHCATtmqfy2020 -> HASHCATvjslg2020
Hardware.Mon.#1..: Temp: 48c Fan: 0% Util: 31% Core:1875MHz Mem:6801MHz Bus:8
Started: Sat Sep 20 15:21:03 2025
Stopped: Sat Sep 20 15:21:06 2025
Hybrid Mode
Hybrid mode is a twist on the combinator attack that lets you mix and match different generation strategies to produce highly tailored wordlists. Think of it as building a custom toolbox: you can combine whole wordlists with masks or other rules to zero in on likely password formats. That makes it especially powerful when you already have an idea of an organization’s password rules or recurring patterns — you can craft wordlists that reflect those habits instead of wasting effort on random guesses.
In tooling terms, hybrid attacks run under attack mode 6. As an illustration, take a password like football1$ — a common word plus a digit and a symbol. In hybrid mode you might pair a base wordlist (containing terms like “football”) with a mask that appends the numeric-and-symbol tail, producing a compact, focused list of candidates that mirror realistic human choices.
Crack the following hash: 978078e7845f2fb2e20399d9e80475bc1c275e06 using the mask ?d?s.
First, we need to identify what type of hash this string is:
$ hashid 978078e7845f2fb2e20399d9e80475bc1c275e06
Analyzing '978078e7845f2fb2e20399d9e80475bc1c275e06'
[+] SHA-1
[+] Double SHA-1
[+] RIPEMD-160
[+] Haval-160
[+] Tiger-160
[+] HAS-160
[+] LinkedIn
[+] Skein-256(160)
[+] Skein-512(160)
Now we can execute Hashcat with the exercise parameters
$ hashcat -a 6 -m 100 target_hash.txt /usr/share/wordlists/rockyou.txt '?d?s'
hashcat (v6.2.6) starting
/usr/share/wordlists/rockyou.txt: No such file or directory
Started: Sat Sep 20 16:30:48 2025
Stopped: Sat Sep 20 16:30:48 2025
$ hashcat -a 6 -m 100 hash /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt '?d?s'
hashcat (v6.2.6) starting
* Device #1: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
* Device #2: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
CUDA API (CUDA 12.4)
* Device #1: NVIDIA GeForce RTX 2060 SUPER, 7585/7967 MB, 34MCU
OpenCL API (OpenCL 3.0 CUDA 12.4.131) - Platform #1 [NVIDIA Corporation]
_________________________________________________________________
* Device #2: NVIDIA GeForce RTX 2060 SUPER, skipped
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #2 [The pocl project]
_________________________________________________________________
* Device #3: cpu-haswell-AMD Ryzen 5 3400G with Radeon Vega Graphics, skipped
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Optimizers applied:
* Zero-Byte
* Early-Skip
* Not-Salted
* Not-Iterated
* Single-Hash
* Single-Salt
* Raw-Hash
ATTENTION! Pure (unoptimized) backend kernels selected.
Pure kernels can crack longer passwords, but drastically reduce performance.
If you want to switch to optimized kernels, append -O to your commandline.
See the above message to find out about the exact limits.
Watchdog: Temperature abort trigger set to 90c
Watchdog: Temperature abort trigger set to 90c
Host memory required for this attack: 1474 MB
Dictionary cache hit:
* Filename..: /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
* Passwords.: 14344385
* Bytes.....: 139921510
* Keyspace..: 4733647050
978078e7845f2fb2e20399d9e80475bc1c275e06:[REDACTED]
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 100 (SHA1)
Hash.Target......: 978078e7845f2fb2e20399d9e80475bc1c275e06
Time.Started.....: Sat Sep 20 16:31:46 2025 (2 secs)
Time.Estimated...: Sat Sep 20 16:31:48 2025 (0 secs)
Kernel.Feature...: Pure Kernel
Guess.Base.......: File (/usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt), Left Side
Guess.Mod........: Mask (?d?s) [2], Right Side
Guess.Queue.Base.: 1/1 (100.00%)
Guess.Queue.Mod..: 1/1 (100.00%)
Speed.#1.........: 1710.1 kH/s (8.74ms) @ Accel:256 Loops:165 Thr:32 Vec:1
Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)
Progress.........: 2435727360/4733647050 (51.46%)
Rejected.........: 0/2435727360 (0.00%)
Restore.Point....: 7241728/14344385 (50.48%)
Restore.Sub.#1...: Salt:0 Amplifier:0-165 Iteration:0-165
Candidate.Engine.: Device Generator
Candidates.#1....: j0685141.. -> hsm425969(
Hardware.Mon.#1..: Temp: 46c Fan: 0% Util: 29% Core:1635MHz Mem:6801MHz Bus:8
Started: Sat Sep 20 16:31:37 2025
Stopped: Sat Sep 20 16:31:49 2025
Working with Rules
Rule-based attacks are the heavy artillery of password cracking — the most powerful and flexible mode you can run. Instead of relying solely on static wordlists or simple masks, rules let you transform every word in a list programmatically: add prefixes or suffixes, flip letter case, trim characters, reverse the string, substitute characters, and much more. That transforms modest wordlists into vast, realistic candidate sets without forcing you to store gigantic files on disk.
Because rules operate on-the-fly, they boost your cracking rates while saving both disk space and preprocessing time compared with generating and storing huge expanded lists. In practice you write rules as small functions: each one takes a candidate word as input and returns a modified version. Chain enough of those functions together and you can model common human behaviors (like “Password → password1!” or “john → John#2023”) with surgical precision.
Both John the Ripper and Hashcat support extensive rule sets, so you can reuse and combine proven transformations across tools. Below are examples of the kinds of rule functions you’ll frequently use (described conceptually rather than in specific syntax):
• Prefix — add one or more characters to the beginning of the word (e.g., add “!” or “2024”)
• Suffix — append characters to the end (very common: digits or symbols)
• Toggle / Change case — convert the whole word to lowercase/uppercase, or toggle the case of individual letters
• Delete / Cut — remove characters from specific positions or trim the start/end
• Reverse — flip the string (e.g., “drow” from “word”)
• Substitute — replace one character with another (e.g., “a” → “@”, “s” → “$”)
• Duplicate / Repeat — repeat the word or parts of it (useful for patterns like “passpass”)
• Truncate / Take — keep only the first or last N characters
• Leetspeak transformations — systematic character swaps to mirror human substitutions (o→0, i→1, e→3, etc.)
Using these building blocks you can craft compact rule files that emulate company password policies, cultural naming patterns, or specific leaks you’ve observed — resulting in smarter, faster cracking with much lower operational overhead.
Crack the following SHA1 hash using the techniques taught for generating a custom rule: 46244749d1e8fb99c37ad4f14fccb601ed4ae283. Modify the example rule in the beginning of the section to append 2020 to the end of each password attempt.
Create the file with the rule.
echo 'so0 si1 se3 ss5 sa@ c $2 $0 $2 $0' > rule.txt
Write the hash into a file.
echo '46244749d1e8fb99c37ad4f14fccb601ed4ae283' > hash
Execute hashcat with this rule to get the flag.
$ hashcat -a 0 -m 100 hash /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt -r rule.txt
hashcat (v6.2.6) starting
* Device #1: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
* Device #2: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
CUDA API (CUDA 12.4)
* Device #1: NVIDIA GeForce RTX 2060 SUPER, 7591/7967 MB, 34MCU
OpenCL API (OpenCL 3.0 CUDA 12.4.131) - Platform #1 [NVIDIA Corporation]
_________________________________________________________________
* Device #2: NVIDIA GeForce RTX 2060 SUPER, skipped
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #2 [The pocl project]
_________________________________________________________________
* Device #3: cpu-haswell-AMD Ryzen 5 3400G with Radeon Vega Graphics, skipped
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Rules: 1
Optimizers applied:
* Zero-Byte
* Early-Skip
* Not-Salted
* Not-Iterated
* Single-Hash
* Single-Salt
* Raw-Hash
ATTENTION! Pure (unoptimized) backend kernels selected.
Pure kernels can crack longer passwords, but drastically reduce performance.
If you want to switch to optimized kernels, append -O to your commandline.
See the above message to find out about the exact limits.
Watchdog: Temperature abort trigger set to 90c
Host memory required for this attack: 597 MB
Dictionary cache hit:
* Filename..: /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
* Passwords.: 14344385
* Bytes.....: 139921510
* Keyspace..: 14344385
46244749d1e8bf99c37ad4f14fccb601edae283:[REDACTED]
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 100 (SHA1)
Hash.Target......: 46244749d1e8bf99c37ad4f14fccb601edae283
Time.Started.....: Sat Sep 20 16:34:28 2025
Time.Estimated...: Sat Sep 20 16:34:28 2025
Kernel.Feature...: Pure Kernel
Cracking Common Hashes
During penetration tests we run into many different hash formats — some show up on almost every engagement, others are rare curiosities. Hashcat maintains a comprehensive catalog of supported hash modes, including each mode’s numeric ID, a short name, and an example hash. That reference is invaluable when you need to identify what you’re cracking and choose the right Hashcat mode.
Below are several of the hash types you’re most likely to encounter in the field, shown with their Hashcat mode number, common name, and an example hash:
| Hashmode | Hash name | Example |
|---|---|---|
| 0 | MD5 | 8743b52063cd84097a65d1633f5c74f5 |
| 100 | SHA1 | b89eaac7e61417341b710b727768294d0e6a277b |
| 1000 | NTLM | b4b9b02e6f09a9bd760f388b67351e2b |
| 1800 | sha512crypt $6$, SHA512 (Unix) | $6$52450745$k5ka2p8bFuSmoVT1tzOyyuaREkkKBcCNqoDKzYiJL9RaE8yMnPgh2XzzF0NDrUhgrcLwg78xs1w5pJiypEdFX/ |
| 3200 | bcrypt $2*$, Blowfish (Unix) | $2a$05$LhayLxezLhK1LhWvKxCyLOj0j1u.Kj0jZ0pEmm134uzrQlFvQJLF6 |
| 5500 | NetNTLMv1 / NetNTLMv1+ESS | u4-netntlm::kNS:338d08f8e26de93300000000000000000000000000000000:9526fb8c23a90751cdd619b6cea564742e1e4bf33006ba41:cb8086049ec4736c |
| 5600 | NetNTLMv2 | admin::N46iSNekpT:08ca45b7d7ea58ee:88dcbe4446168966a153a0064958dac6:5c7830315c7830310000000000000b45c67103d07d7b95acd12ffa11230e0000000052920b85f78d013c31cdb3b92f5d765c783030 |
| 13100 | Kerberos 5 TGS-REP etype 23 | $krb5tgs$23$user$realm$test/spn$63386d22d359fe42230300d56852c9eb$ < SNIP > |
Keep this kind of index handy during engagements — identifying the correct hash mode quickly saves time and avoids wasted cracking attempts. If you want, I can reformat this into a printable cheat sheet or expand the list with additional hash modes and notes on cracking strategies for each.
Crack the following hash: 7106812752615cdfe427e01b98cd4083
Let’s use hash-identifier to discover what type this hash is:
$ hash-identifier 7106812752615cdfe427e01b98cd4083
############################################################
# #
# _ _ _ _ ___ ___ ___ ___ #
# | | | |__ _ __ (_) ___ | |_|_ _| / __| / __| / __| #
# | |_| / _ \| '_ \| |/ _ \| __|| | \__ \ \__ \ \__ \ #
# | _ | (_) | | | | | (_) | |_ | | |___/ |___/ |___/ #
# |_| |_|\___/|_| |_|_|\___/ \__|___| v1.2 #
# By Zion3R #
# www.Blackploit.com #
# Root@Blackploit.com #
# #
############################################################
Possible Hashes:
[+] MD5
[+] Domain Cached Credentials - MD4(MD4(($pass)).(strtolower($username)))
Least Possible Hashes:
[+] RAdmin v2.x
[+] NTLM
[+] MD4
[+] MD2
[+] MD5(HMAC)
[+] MD4(HMAC)
[+] MD2(HMAC)
[+] MD5(HMAC(WordPress))
[+] Haval-128
[+] Haval-128(HMAC)
[+] RipeMD-128
[+] RipeMD-128(HMAC)
[+] SNEFRU-128
[+] SNEFRU-128(HMAC)
[+] Tiger-128
[+] Tiger-128(HMAC)
[+] md5($pass.$salt)
[+] md5($salt.$pass)
Copy the into a file named hash
echo '7106812752615cdfe427e01b98cd4083' > hash
And use hashcat to crack this hash
$ hashcat -a 0 -m 1000 -g 1000 hash /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
hashcat (v6.2.6) starting
* Device #1: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
* Device #2: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
CUDA API (CUDA 12.4)
* Device #1: NVIDIA GeForce RTX 2060 SUPER, 7581/7967 MB, 34MCU
OpenCL API (OpenCL 3.0 CUDA 12.4.131) - Platform #1 [NVIDIA Corporation]
_________________________________________________________________
* Device #2: NVIDIA GeForce RTX 2060 SUPER, skipped
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #2 [The pocl project]
_________________________________________________________________
* Device #3: cpu-haswell-AMD Ryzen 5 3400G with Radeon Vega Graphics, skipped
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Rules: 1000
Optimizers applied:
* Zero-Byte
* Early-Skip
* Not-Salted
* Not-Iterated
* Single-Hash
* Single-Salt
* Raw-Hash
ATTENTION! Pure (unoptimized) backend kernels selected.
Pure kernels can crack longer passwords, but drastically reduce performance.
If you want to switch to optimized kernels, append -O to your commandline.
See the above message to find out about the exact limits.
Watchdog: Temperature abort trigger set to 90c
Host memory required for this attack: 597 MB
Dictionary cache hit:
* Filename..: /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
* Passwords.: 14344385
* Bytes.....: 139921510
* Keyspace..: 14344385000
Cracking performance lower than expected?
* Append -O to the commandline.
This lowers the maximum supported password/salt length (usually down to 32).
* Append -w 3 to the commandline.
This can cause your screen to lag.
* Append -S to the commandline.
This has a drastic speed impact but can be better for specific attacks.
Typical scenarios are a small wordlist but a large ruleset.
* Update your backend API runtime / driver the right way:
https://hashcat.net/faq/wrongdriver
* Create more work items to make use of your parallelization power:
https://hashcat.net/faq/morework
7106812752615cdfe427e01b98cd4083:[REDACTED]
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 1000 (NTLM)
Hash.Target......: 7106812752615cdfe427e01b98cd4083
Time.Started.....: Sat Sep 20 18:08:26 2025 (11 secs)
Time.Estimated...: Sat Sep 20 18:08:37 2025 (0 secs)
Kernel.Feature...: Pure Kernel
Guess.Base.......: File (/usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt)
Guess.Mod........: Rules (Generated)
Guess.Queue......: 1/1 (100.00%)
Speed.#1.........: 990.3 MH/s (7.83ms) @ Accel:128 Loops:32 Thr:64 Vec:1
Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)
Progress.........: 10851450880/14344385000 (75.65%)
Rejected.........: 0/10851450880 (0.00%)
Restore.Point....: 10584064/14344385 (73.79%)
Restore.Sub.#1...: Salt:0 Amplifier:928-960 Iteration:0-32
Candidate.Engine.: Device Generator
Candidates.#1....: SSSSSun0000 -> MIYAYK-H
Hardware.Mon.#1..: Temp: 58c Fan: 45% Util: 84% Core:1845MHz Mem:6801MHz Bus:8
Started: Sat Sep 20 18:08:25 2025
Stopped: Sat Sep 20 18:08:39 2025
Cracking Miscellaneous Files & Hashes
Password-protected files are a staple find during penetration tests and security assessments — you’ll regularly encounter Microsoft Word and Excel documents, OneNote notebooks, KeePass database files, SSH private-key passphrases, PDFs, and a variety of archive formats like ZIP and 7z. The good news is that most of these formats aren’t black boxes: once you extract the underlying password hash or verifier, Hashcat can often be used to attempt a recovery.
To get those hashes into a Hashcat-friendly form you’ll usually rely on specialized extractors. John the Ripper ships a number of small C utilities (and the community maintains others) specifically for this purpose — tools such as office2john, pdf2john, zip2john, and extractors for KeePass and various archive types convert protected files into the canonical hash strings Hashcat understands. Many of these helpers come inside the John distribution or its source tree; in some cases you’ll need to compile them from source before using them. The basic workflow is simple: run the appropriate extractor against the protected file, capture the output (the example/hash string), then feed that into Hashcat with the correct mode.
A few practical tips: keep the original file metadata and a copy of the extracted hash for reporting and verification; test your extractor output on a tiny wordlist first to ensure the chosen Hashcat mode and format are correct; and remember that some formats (bcrypt, modern Office with strong KDFs, high-iteration PBKDF2) are deliberately slow to resist cracking, so plan your strategy around realistic expectations. Finally, treat all password-cracking activity as sensitive — document authorization, maintain an audit trail, and operate only within the scope of your engagement.
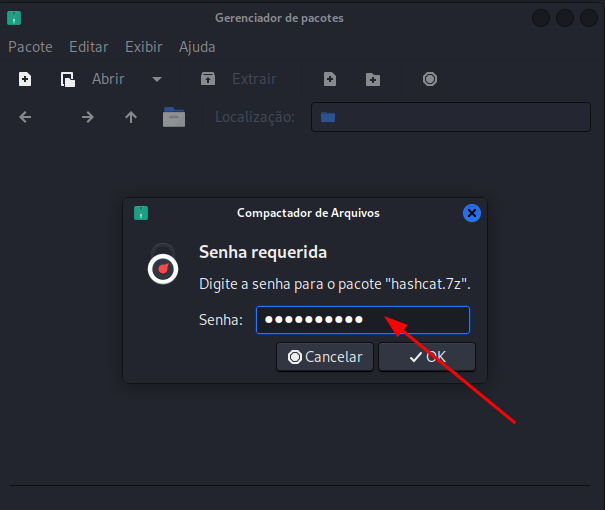
Extract the hash from the attached 7-Zip file, crack the hash, and submit the value of the flag.txt file contained inside the archive.
Download and unzip the file. Now we need to find the place that you have installed 7z2john.pl
$ locate 7z2john.pl
/usr/share/john/7z2john.pl
Use this script to get the hash and copy it into a text file. Edit and remove the first 10 characters of the created file.
$ /usr/share/john/7z2john.pl hashcat.7z > hash
WARNING: the hashes might contain sensitive encrypted data. Be careful when sharing or posting these hashes
hashcat.7z:$7z$0$19$0$5$9c7684c204c437fa000000000000000000$1098215690$112$106$7395978cad9ad8b18aef51ba2f9dcf909a1bff70d240b1c8e98dffabd352d69a1f37978e5df017
$7z$0$19$0$$859c7684c204c437fa000000000000000000$1098215690$112$106$7395978cad9ad8b18aef51ba2f9dcf909a1bff70d240b1c8e98dffabd352d69a1f37978e5df017
Now execute hashcat to find the password.
$ hashcat -m 11600 hash /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
hashcat (v6.2.6) starting
* Device #1: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
* Device #2: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
CUDA API (CUDA 12.4)
* Device #1: NVIDIA GeForce RTX 2060 SUPER, 7582/7967 MB, 34MCU
OpenCL API (OpenCL 3.0 CUDA 12.4.131) - Platform #1 [NVIDIA Corporation]
_________________________________________________________________
* Device #2: NVIDIA GeForce RTX 2060 SUPER, skipped
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #2 [The pocl project]
_________________________________________________________________
* Device #3: cpu-haswell-AMD Ryzen 5 3400G with Radeon Vega Graphics, skipped
This hash-mode is known to emit multiple valid candidates for the same hash.
==> Keep guessing to continue attack after finding the first crack.
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Hashfile 'hash' on line 1 (hashc...c3063744d0b81d1492ea1dcfe7ab9983): Signature unmatched
No hashes loaded.
Started: Sun Sep 21 16:07:46 2025
Stopped: Sun Sep 21 16:07:49 2025
$ nano hash
$ hashcat -m 11600 hash /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
hashcat (v6.2.6) starting
* Device #1: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
* Device #2: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
CUDA API (CUDA 12.4)
* Device #1: NVIDIA GeForce RTX 2060 SUPER, 7627/7967 MB, 34MCU
OpenCL API (OpenCL 3.0 CUDA 12.4.131) - Platform #1 [NVIDIA Corporation]
_________________________________________________________________
* Device #2: NVIDIA GeForce RTX 2060 SUPER, skipped
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, REL0C, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #2 [The pocl project]
_________________________________________________________________
* Device #3: cpu-haswell-AMD Ryzen 5 3400G with Radeon Vega Graphics, skipped
This hash-mode is known to emit multiple valid candidates for the same hash.
ATTENTION! Pure (unoptimized) backend kernels selected.
Pure kernels can crack longer passwords, but drastically reduce performance.
If you want to switch to optimized kernels, append -O to your commandline.
See the above message to find out about the exact limits.
Watchdog: Temperature abort trigger set to 90c
Host memory required for this attack: 1642 MB
Dictionary cache hit:
* Filename..: /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
* Passwords.: 14344385
* Bytes.....: 139921510
* Keyspace..: 14344385
Cracking performance lower than expected?
* Append -O to the commandline.
This lowers the maximum supported password/salt length (usually down to 32).
* Append -w 3 to the commandline.
This can cause your screen to lag.
* Append -S to the commandline.
This has a drastic speed impact but can be better for specific attacks.
Typical scenarios are a small wordlist but a large ruleset.
* Update your backend API runtime / driver the right way:
https://hashcat.net/faq/wrongdriver
* Create more work items to make use of your parallelization power:
https://hashcat.net/faq/morework
[s]tatus [p]ause [b]ypass [c]heckpoint [f]inish [q]uit => ^C
$7z$0$19$0$5$9c7684c204c437fa000000000000000000$1098215690$112$106$7395978cad9ad8b18aef51ba2f9dcf909a1bff70d240b1c8e98dffabd352d69a1f37978e5df017:123456789a
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 11600 (7-zip)
Hash.Target......: $7z$0$19$0$5$9c7684c204c437fa000000000000000000$1098215690$112$106$7395978cad9ad8b18aef51ba2f9dcf909a1bff70d240b1c8e98dffabd352d69a1f37978e5df017
Time.Started.....: Sun Sep 21 16:06:55 2025 (63 secs)
Time.Estimated...: Sun Sep 21 16:08:58 2025 (53 secs)
Kernel.Feature...: Pure Kernel
Guess.Base.......: File (/usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt)
Guess.Queue......: 1/1 (100.00%)
Speed.#1.........: 24.13 kH/s (41.45ms) @ Accel:32 Loops:128 Thr:128 Vec:1
Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)
Progress.........: 1234567/14344385 (8.60%)
Rejected.........: 0/1234567 (0.00%)
Restore.Point....: 0/14344385 (0.00%)
Restore.Sub.#1...: Salt:0 Amplifier:0-524288 Iteration:0-524288
Candidate.Engine.: Device Generator
Candidates.#1....: 123456 -> katong
Started: Sun Sep 21 16:05:52 2025
Stopped: Sun Sep 21 16:07:58 2025
The password is 123456789a
Unzip the file and edit the text file to get the flag.
Cracking Wireless (WPA/WPA2) Handshakes with Hashcat
Wireless security assessments are a common — and often critical — component of internal penetration testing. At first glance, Wi-Fi may seem like “just” a convenience for employees, but from a security standpoint it frequently represents a direct entry point into a company’s internal resources. In this article, we’ll explore why wireless testing is important, what a WPA/WPA2 handshake is, how it can be captured and cracked, which tools are typically used (such as Hashcat), and what countermeasures organizations should apply.
Why Include Wireless Testing in an Internal Pentest?
- Underestimated entry points: Wi-Fi networks are often poorly segmented from corporate infrastructure. An employee who connects through Wi-Fi might gain access to sensitive internal resources.
- Large attack surface: Access points, client devices (laptops, smartphones), outdated routers, and IoT devices frequently expose weak configurations or unpatched firmware.
- Accessible credentials: In many environments, obtaining valid Wi-Fi credentials (whether a pre-shared key or enterprise credentials) can be easier than exploiting internal services directly.
- High impact: A successful Wi-Fi authentication can lead to lateral movement, data exposure, and pivoting into critical systems.
WPA/WPA2 Handshake — What It Is and Why It Matters
When a client authenticates to a WPA/WPA2-protected network, a cryptographic exchange called the handshake occurs. Penetration testers often target this exchange because it can be captured and analyzed offline. There are two main types of captures used for attacks:
- 4-Way Handshake (MIC): This is the full exchange between a client and the access point. Capturing it allows brute-force or dictionary attacks against the pre-shared key (PSK).
- PMKID (Pairwise Master Key Identifier): Some implementations and access points expose a PMKID value, which contains enough information to attempt an offline attack. Unlike the 4-way handshake, you don’t need to capture a complete client–AP negotiation — the first packet is enough.
Cracking Captured Handshakes with Hashcat
Once a handshake (MIC or PMKID) has been captured, tools like Hashcat can be used to attempt password recovery. Hashcat supports both formats and can leverage powerful attack modes such as:
- Dictionary attacks: Testing common passwords or custom wordlists.
- Rule-based attacks: Extending wordlists by applying transformations (e.g., adding numbers, symbols, or variations).
- Mask attacks: Testing passwords with specific patterns (e.g.,
Company2025!).
By combining GPU acceleration with optimized algorithms, Hashcat significantly reduces the time required to test large numbers of potential passwords.
Mitigation Strategies
To protect corporate wireless networks against these types of attacks, organizations should implement strong security practices:
- Use WPA3 whenever possible, as it introduces stronger protections against offline dictionary attacks.
- Enforce complex and unique passphrases for WPA2-PSK networks, avoiding dictionary words or predictable patterns.
- Implement proper network segmentation, ensuring the wireless network is isolated from critical corporate infrastructure.
- Adopt enterprise authentication (802.1X with RADIUS) for stronger user-based access control.
- Regularly monitor and audit Wi-Fi infrastructure for rogue access points and misconfigurations.
Key Takeaways
- Wireless security assessments are essential because Wi-Fi often acts as a gateway to internal networks.
- WPA/WPA2 handshakes (4-way or PMKID) can be captured and used for offline password-cracking attempts.
- Tools like Hashcat make these attacks efficient, especially with GPU acceleration and advanced attack modes.
- Organizations can mitigate risks by adopting WPA3, enforcing strong credentials, segmenting networks, and using enterprise-grade authentication mechanisms.
A wireless assessment may not always be the most “exciting” part of a pentest, but it can quickly escalate into a high-impact finding if weak protections are uncovered.
Execute o cracking do MIC usando o arquivo .cap anexado.
The explanation provided in the exercise is outdated. First, convert the file into the 2200 format.
$ hcxdumptool 6.3.5 reading from corp_question1-01.cap ...
failed to read pcap packet header for packet 95415
summary capture file
file name.....................: corp_question1-01.cap
version (pcap/cap)............: 2.4 (very basic format without any additional information)
timestamp minimum (timestamp).: 16.07.2020 22:07:54 (1594937274)
timestamp maximum (timestamp).: 16.07.2020 22:12:43 (1594937563)
duration of the dump tool (minutes): 4
used capture interface........: 1
link layer header type........: DLT_IEEE802_11 (105) very basic format without any additional information about the quality
endianess (capture system)....: little endian
packets inside...............: 95415
ESSID (total unique).........: 1
BEACON (total)...............: 11
BEACON ON 2.4 ghz channel (from IE_TAG)..: 1
ACTION (total)...............: 11
PROBERESPONSE (total)........: 432
DEAUTHENTICATION (total).....: 48668
AUTHENTICATION (total).......: 327
AUTHENTICATION (OPEN SYSTEM)..: 327
ASSOCIATIONREQUEST (total)...: 80
ASSOCIATIONREQUEST (PSK).....: 80
REASSOCIATIONREQUEST (total).: 50
REASSOCIATIONREQUEST (PSK)....: 50
WPA encrypted................: 1145
EAPOL messages (total).......: 22
EAPOL RNS messages...........: 22
EAPOLTIME gap (measured maximum msec).: 110274
EAPOL ANONCE error corrections (NC)....: not detected
REPLAYCOUNT gap (measured maximum): 2
EAPOL M1 messages (total).....: 8
EAPOL M2 messages (total).....: 5
EAPOL M3 messages (total).....: 3
EAPOL M4 messages (total).....: 6
EAPOL pairs (total)..........: 11
EAPOL pairs written to 22000 hash file ...: 2 (RC checked)
EAPOL M12E2 (challenge)......: 1
EAPOL M32E2 (authorized).....: 1
packet read error.............: 1
Warning: out of sequence timestamps!
This dump file contains frames with out of sequence timestamps.
That is a bug of the capturing/cleaning tool.
Information: limited dump file format detected!
This file format is a very basic format to save captured network data.
It is recommended to use PCAP Next Generation dump file format instead. The PCAP Next Generation dump file format is an attempt to overcome the limitations of the classic pcap format.
https://www.wireshark.org/docs/wsug_html_chunked/AppFiles.html#ChAppFilesCaptureFilesSection
https://github.com/pcapng/pcapng
Information: radiotap header is missing!
Now use Hashcat to crack it.
$ hashcat -m 22000 corp_question1-01.22000 /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
hashcat (v6.2.6) starting
* Device #1: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
* Device #2: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
CUDA API (CUDA 12.4)
* Device #1: NVIDIA GeForce RTX 2060 SUPER, 7649/7967 MB, 34MCU
OpenCL API (OpenCL 3.0 CUDA 12.4.131) - Platform #1 [NVIDIA Corporation]
_________________________________________________________________
* Device #2: NVIDIA GeForce RTX 2060 SUPER, skipped
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #2 [The pocl project]
_________________________________________________________________
* Device #3: cpu-haswell-AMD Ryzen 5 3400G with Radeon Vega Graphics, skipped
Minimum password length supported by kernel: 8
Maximum password length supported by kernel: 63
Hashes: 2 digests; 2 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Rules: 1
Optimizers applied:
* Zero-Byte
* Single-Salt
* Slow-Hash-SIMD-LOOP
Watchdog: Temperature abort trigger set to 90c
Host memory required for this attack: 1474 MB
Dictionary cache hit:
* Filename..: /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
* Passwords.: 14344385
* Bytes.....: 139921510
* Keyspace..: 14344385
92a9fe85d6566281511762c33c0f62b6:cc40d04a0d96:48e244a7c4fb:CORP-WIFI:[REDACTED]
b7703fd2171bec27933ffc900faa6eb5b:cc40d04a0d96:80822381a9c8:CORP-WIFI:rockyou1
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 22000 (WPA-PBKDF2-PMKID+EAPOL)
Hash.Target......: corp_question1-01.22000
Time.Started.....: Sun Sep 21 17:29:43 2025 (0 secs)
Time.Estimated...: Sun Sep 21 17:29:43 2025 (0 secs)
Kernel.Feature...: Pure Kernel
Guess.Base.......: File (/usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt)
Guess.Queue......: 1/1 (100.00%)
Speed.#1.........: 420.9 kH/s (9.74ms) @ Accel:8 Loops:128 Thr:512 Vec:1
Extract the PMKID hash from the attached .cap file and crack it.
Just convert the file.
$ hcxcapngtool -o cracking_pmkid_question2.hc22000 cracking_pmkid_question2.cap
hcxdumptool 6.3.5 reading from cracking_pmkid_question2.cap ...
summary capture file
file name.....................: cracking_pmkid_question2.cap
version (pcapng)..............: 1.0
operating system.............: Linux 5.7.0-kali1-amd64
application...................: hcxdumptool 6.0.7-22-g2f82e84
interface name...............: wlan0
interface vendor.............: 00c0ca
openSSL version..............: 1.1
weak candidate...............: 12345678
MAC ACCESS POINT.............: 50e14a6afda7 (incremented on every new client)
MAC CLIENT...................: a4a6a9967f1e
REPLAYCOUNT..................: 65332
ANONCE.......................: 07f1dbf861f4ecce4652957f52d98663c5c6403a2e6d2ef2a4fee1c8760ed48
SNONCE.......................: 9834fe74077c307ef3189a49e07b24a7650e9b6a227135b7d453a665c92047a9
timestamp minimum (timestamp): 17.07.2020 16:28:48 (1595003328)
timestamp maximum (timestamp): 17.07.2020 16:34:59 (1595003699)
duration of the dump tool (minutes): 6
used capture interfaces......: 1
link layer header type.......: DLT_IEEE802_11_RADIO (127)
endianness (capture system)..: little endian
packets inside..............: 75
frames with FCS (radiotap)...: 75
frames with correct FCS (crc): 75
packets received on 2.4 GHz..: 75
ESSID (total unique).........: 4
BEACON (total)...............: 1
BEACON ON 2.4 GHZ channel (from IE_TAG)..: 1
PROBEREQUEST (undirected)....: 4
PROBERESPONSE (total)........: 1
EAPOL messages (total).......: 68
EAPOL RSN messages...........: 68
EAPOLTIME gap (measured maximum msec).: 125881
EAPOL ANONCE error corrections (NC)....: working
REPLAYCOUNT gap (suggested NC)........: 15
EAPOL M1 messages (total).....: 54
EAPOL M2 messages (total).....: 13
EAPOL M3 messages (total).....: 1
EAPOL M4 messages (total).....: 0
EAPOL pairs (total)...........: 16
EAPOL pairs (best)............: 1
EAPOL pairs written to 22000 hash file ...: 1 (RC checked)
EAPOL M12E2 (challenge)......: 1
RSN PMKID (total)............: 45
RSN PMKID (best).............: 2
RSN PMKID written to 22000 hash file...: 2
frequency statistics from radiotap header (frequency: received packets)
2437: 75
And use hashcat to crack it.
$ hashcat -m 22000 cracking_pmkid_question2.hc22000 /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
hashcat (v6.2.6) starting
* Device #1: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
* Device #2: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
CUDA API (CUDA 12.4)
* Device #1: NVIDIA GeForce RTX 2060 SUPER, 7566/7967 MB, 34MCU
OpenCL API (OpenCL 3.0 CUDA 12.4.131) - Platform #1 [NVIDIA Corporation]
_________________________________________________________________
* Device #2: NVIDIA GeForce RTX 2060 SUPER, skipped
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #2 [The pocl project]
_________________________________________________________________
* Device #3: cpu-haswell-AMD Ryzen 5 3400G with Radeon Vega Graphics, skipped
Minimum password length supported by kernel: 8
Maximum password length supported by kernel: 63
Hashes: 3 digests; 3 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Rules: 1
Optimizers applied:
* Zero-Byte
* Single-Salt
* Slow-Hash-SIMD-LOOP
Watchdog: Temperature abort trigger set to 90c
INFO: Removed hash found as potfile entry.
Host memory required for this attack: 1474 MB
Dictionary cache hit:
* Filename..: /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
* Passwords.: 14344385
* Bytes.....: 139921510
* Keyspace..: 14344385
b5849dab3bd0553413ed964530196e0a:10da43bef746:80822381a9c8:CORP-WIFI:[REDACTED]
609b77a10d933419201f49f25bfe222e:10da43bef746:e4e0a66592a7:CORP-WIFI:[REDACTED]
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 22000 (WPA-PBKDF2-PMKID+EAPOL)
Hash.Target......: cracking_pmkid_question2.hc22000
Time.Started.....: Sun Sep 21 17:29:43 2025 (0 secs)
Time.Estimated...: Sun Sep 21 17:29:43 2025 (0 secs)
Kernel.Feature...: Pure Kernel
Guess.Base.......: File (/usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt)
Guess.Queue......: 1/1 (100.00%)
Speed.#1.........: 420.9 kH/s (9.74ms) @ Accel:8 Loops:128 Thr:512 Vec:1
Skills Assessment
You’ve reached the end of the module — nice work. This final skills check is a practical, scenario-driven assessment of your knowledge of password hashing, hash identification, and Hashcat usage. Below I’ve expanded the original prompt into a clear, structured guide you can use as a study sheet or to run the assessment in a methodical way.
Assessment overview (what you must do)
You’ll receive several hashes collected during a penetration test. For each one you must:
- Identify the hash type (e.g., SHA-1, NetNTLMv2, Kerberos TGS-REP/TGS, DCC2).
- Select an appropriate cracking strategy and Hashcat mode.
- Attempt to recover the cleartext password using suitable wordlists, rules, masks, or hybrid attacks.
- Report the cleartext if cracked (for the exercise, submit the requested password value — e.g., “the password that appears 5 times”).
This simulates real-world red-team tasks where partial success on some hashes yields lateral movement and further compromise.
The scenarios (broken down and explained)
Below are the hashes you’ll see in the exercise with commentary on what they represent and how to approach them.
1) SQL-injection–extracted hash
0c67ac18f50c5e6b9398bfe1dc3e156163ba10ef
- Likely type: This is a 40-hex character string typical of SHA-1 (or salted variations). It could also be a truncated value — always verify.
- Approach: Use a hash identifier (e.g.,
hashid,hash-identifier) to confirm the hash family. Try dictionary + rule attacks (common passwords), then move to masks if you have a pattern. If salts are involved you need to know them and adapt the attack.
2) NetNTLMv2 (captured via Responder)
bjones::INLANEFREIGHT:699f1e768bd69c00:5304B6DB9769D974A8F24C4F4309B6BC:...[long blob]...
- Type: NetNTLMv2/NetNTLMv2 challenge-response capture (commonly from LLMNR/mDNS/NBT-NS poisoning tools like Responder).
- Why it matters: If cracked, the cleartext password allows direct authentication to Windows hosts or can be used to pivot.
- Approach: Use Hashcat mode for NetNTLMv2 (e.g., mode 5600 or the current recommended mode) with targeted wordlists and rules. Use GPU acceleration for speed. Consider targeted wordlists based on company naming, common suffixes, and leaked-password lists.
3) Kerberoast TGS ticket (Kerberos TGS-REP / krb5tgs)
$krb5tgs$23$*sql_svc$INLANEFREIGHT.LOCAL$mssql/inlanefreight.local~1443*$80be357f5e68b4f64a185397bf72cf1c$...
- Type: Kerberos TGS-REP hash for service accounts (Kerberoasting)—typical format for Hashcat’s krb5tgs mode.
- Why it matters: Cracking a service account password can allow lateral movement or escalation if that account has privileges (SQL service, DB access, local admin privileges on a host, etc.).
- Approach: Use Hashcat’s krb5tgs mode (e.g., mode 13100 / 17200 depending on Hashcat version — always confirm current mode). Kerberoast cracks can be slow if the password is complex; use focused wordlists, corporate-specific words, and rulesets. Try wordlist + rules before resorting to brute force masks.
4) Domain Cached Credentials 2 (DCC2 / Cached Domain Credential)
$DCC2$10240#backup_admin#62dabbde52af53c75f37df260af1008e
- Type: DCC2 (aka MSCACHE2) — Windows cached-domain-credential format. Harder to crack because it’s derived with multiple iterations.
- Why it matters: If you can crack a Domain Admin’s cached hash, you get full domain compromise.
- Approach: Use Hashcat’s mode for DCC2 (e.g., mode 2100/2301 family — check current mapping). Requires GPU and possibly long runtimes. Try focused dictionaries with corporate patterns, password reuse lists, and common admin patterns.
5) NTDS dump (final task)
- Task: From the NTDS dump you can often extract many user hashes. The final grading instruction in the exercise asks you to find the password that appears 5 times and submit its cleartext.
- Approach: This part is about completeness and perseverance — combine dictionaries, rules, masks and possibly targeted wordlists (company-related). You may be able to crack a large portion of NT hashes with adequate resources and datasets.
Practical methodology checklist (step-by-step, high level)
When you see a new hash in this lab, follow a reproducible process:
- Identify the hash family
- Tools:
hashid,hash-identifier,hashcat --example-hashessample matching - Why: determines Hashcat mode and attack choices
- Tools:
- Prepare the environment
- Ensure your GPU is available (
nvidia-smi), drivers OK, Hashcat up-to-date. - Create a working directory and session names.
- Ensure your GPU is available (
- Select initial attack strategy
- Start with wordlist + rules (high ROI).
- Wordlists: rockyou, seclists, company-specific lists, leaked corp lists.
- Rules:
best64.rule,dive.rule, or custom company-oriented rules.
- If dictionary fails, escalate
- Combinator attacks (combine two lists).
- Mask attacks for structured passwords: e.g.,
?u?l?l?l?d?d!etc. - Hybrid attacks (dictionary + mask) for suffixes or number patterns.
- Specialized attacks for special formats
- NetNTLMv2: use specific Hashcat mode (e.g., 5600/ or current mode) + wordlists/rules.
- Kerberoast (krb5tgs): use krb5tgs mode; try relevant dictionaries.
- DCC2 / MSCACHE2: expect slower cracking due to iterations; focused lists are crucial.
- Logging and checkpointing
- Use Hashcat’s
--sessionand--restorefeatures to resume. - Save cracked results and progress.
- Use Hashcat’s
- Post-crack use
- If a password is found, use it in the lab for privilege escalation or lateral movement steps as described by the scenario (e.g., authenticate to hosts, use credentials for pass-the-hash if permitted, etc.).
Practical tips & best practices
- Start small and focused. For each hash type, try targeted lists before wasting GPU cycles on full brute force.
- Leverage rules — they multiply the effectiveness of wordlists.
- Use mask attacks for structured passwords (people often append years, digits, or special characters).
- Maintain GPU health: watch temps when running long attacks.
- Record everything — cracked hashes, timestamps, attack vectors — for reporting in a pentest deliverable.
- Respect legal scope — only attempt cracking when you have written authorization (your scenario indicates authorized red-team activities).
Tools & wordlists (recommended)
- Hashcat — the engine.
- hashid / hash-identifier — quick hash family detection.
- JohnTheRipper — alternative for some formats.
- Responder / Responder outputs — NetNTLMv2 captures.
- Impacket / Rubeus / Kerberos tools — for ticket harvest/usage.
- Wordlists:
rockyou.txt,SecLists(Passwords),john’s wordlists, corp-specific lists you generate from OSINT. - Rulesets:
best64.rule,d3ad0ne.rule,rockyou-30000.rule, or custom.
What type of hash did your colleague obtain from the SQL injection attack?
$ hashid 0c67ac18f50c5e6b99398bfe1dc3e156163ba10ef
Analyzing '0c67ac18f50c5e6b99398bfe1dc3e156163ba10ef'
[+] [REDACTED]
[+] Double SHA-1
[+] RIPEMD-160
[+] Haval-160
[+] Tiger-160
[+] HAS-160
[+] LinkedIn
[+] Skein-256(160)
[+] Skein-512(160)
What is the cleartext password for the hash obtained from SQL injection in example 1?
Copy the hash text into a file.
echo "0c67ac18f50c5e6b9398bfe1dc3e156163ba10ef" > hash
Use Hashcat to crack it.
$ hashcat -m 100 -a 0 hash /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
hashcat (v6.2.6) starting
* Device #1: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
* Device #2: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
CUDA API (CUDA 12.4)
* Device #1: NVIDIA GeForce RTX 2060 SUPER, 7627/7967 MB, 34MCU
OpenCL API (OpenCL 3.0 CUDA 12.4.131) - Platform #1 [NVIDIA Corporation]
_________________________________________________________________
* Device #2: NVIDIA GeForce RTX 2060 SUPER, skipped
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #2 [The pocl project]
_________________________________________________________________
* Device #3: cpu-haswell-AMD Ryzen 5 3400G with Radeon Vega Graphics, skipped
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Rules: 1
Optimizers applied:
* Zero-Byte
* Early-Skip
* Not-Salted
* Not-Iterated
* Single-Hash
* Single-Salt
* Raw-Hash
ATTENTION! Pure (unoptimized) backend kernels selected.
Pure kernels can crack longer passwords, but drastically reduce performance.
If you want to switch to optimized kernels, append -O to your commandline.
See the above message to find out about the exact limits.
Watchdog: Temperature abort trigger set to 90c
Host memory required for this attack: 597 MB
Dictionary cache hit:
* Filename..: /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
* Passwords.: 14344385
* Bytes.....: 139921510
* Keyspace..: 14344385
0c67ac18f50c5e6b99398bfe1dc3e156163ba10ef:[REDACTED]
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 100 (SHA1)
Hash.Target......: 0c67ac18f50c5e6b99398bfe1dc3e156163ba10ef
Time.Started.....: Sun Sep 21 17:48:46 2025 (0 secs)
Time.Estimated...: Sun Sep 21 17:48:46 2025 (0 secs)
What is the cleartext password value for the NetNTLMv2 hash?
Copy the hash bellow into a file named hashNTLMv2
bjones::INLANEFREIGHT:699f1e768bd69c00:5304B6DB9769D974A8F24C4F4309B6BC:0101000000000000C0653150DE09D2010409DF59F277926E000000000200080053004D004200330001001E00570049004E002D00500052004800340039003200520051004100460056000400140053004D00420033002E006C006F00630061006C0003003400570049004E002D00500052004800340039003200520051004100460056002E0053004D00420033002E006C006F00630061006C000500140053004D00420033002E006C006F00630061006C0007000800C0653150DE09D20106000400020000000800300030000000000000000000000000300000B14866125D55255DD82C994C0D8AC3D9FF1A3EFDAECBE908F1F91C7BD4B05CF50A001000000000000000000000000000000000000900280063006900660073002F003100390032002E003100360038002E003100390035002E00310032003900000000000000000000000000
And execute Hashcat to crack it.
$ hashcat -a 0 -m 5600 hashNTLMv2 /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
hashcat (v6.2.6) starting
* Device #1: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
* Device #2: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
CUDA API (CUDA 12.4)
* Device #1: NVIDIA GeForce RTX 2060 SUPER, 7623/7967 MB, 34MCU
OpenCL API (OpenCL 3.0 CUDA 12.4.131) - Platform #1 [NVIDIA Corporation]
_________________________________________________________________
* Device #2: NVIDIA GeForce RTX 2060 SUPER, skipped
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #2 [The pocl project]
_________________________________________________________________
* Device #3: cpu-haswell-AMD Ryzen 5 3400G with Radeon Vega Graphics, skipped
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Rules: 1
Optimizers applied:
* Zero-Byte
* Not-Iterated
* Single-Hash
* Single-Salt
ATTENTION! Pure (unoptimized) backend kernels selected.
Pure kernels can crack longer passwords, but drastically reduce performance.
If you want to switch to optimized kernels, append -O to your commandline.
See the above message to find out about the exact limits.
Watchdog: Temperature abort trigger set to 90c
Host memory required for this attack: 597 MB
Dictionary cache hit:
* Filename..: /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
* Passwords.: 14344385
* Bytes.....: 139921510
* Keyspace..: 14344385
b1003e2c0e00600f06300016000030003003000570000000000e0000000000000000000000000000000000000000000000000000000000000000:0101000000000000000065315e0e9d2d01049d6f5d1277296e00000000000000000000000000000000000000000000000000000000000000000000000000000000003b000000000000003b000000000000000000000000000000000000000000000000000057000000004a0000b10bd1d60c0a000000000000000000000000000000000004000000: [REDACTED]
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 5600 (NetNTLMv2)
Hash.Target......: hashNTLMv2
Time.Started.....: Sun Sep 21 18:11:02 2025
Time.Estimated...: Sun Sep 21 18:11:02 2025
Kernel.Feature...: Pure Kernel
Crack the TGS ticket obtained from the Kerberoasting attack.
Insert the text above into a file named kebhash.
$krb5tgs$23$*sql_svc$INLANEFREIGHT.LOCAL$mssql/inlanefreight.local~1443*$80be357f5e68b4f64a185397bf72cf1c$579d028f0f91f5791683844c3a03f48972cb9013eddf11728fc19500679882106538379cbe1cb503677b757bcb56f9e708cd173a5b04ad8fc462fa380ffcb4e1b4feed820fa183109e2653b46faee565af76d5b0ee8460a3e0ad48ea098656584de67974372f4a762daa625fb292556b407c0c97fd629506bd558dede0c950a039e2e3433ee956fc218a54b148d3e5d1f99781ad4e419bc76632e30ea2c1660663ba9866230c790ba166b865d5153c6b85a184fbafd5a4af6d3200d67857da48e20039bbf31853da46215cbbc5ebae6a3b0225b6651ec8cc792c8c3d5893a8d014f9d297ac297288e76d27a1ed2942d6997f6b24198e64fea9ff5a94badd53cc12a73e9505e4dab36e4bd1ef7fe5a08e527d9046b49e730d83d8af395f06fe35d360c59ab8ebe2c3b7553acf8d40c296b86c1fb26fdf43fa8be2ac4a92152181b81afb1f4773936b0ccc696f21e8e0fe7372252b3c24d82038c62027abc34a4204fb6e52bf71290fdf0db60b1888f8369a7917821f6869b6e51bda15f1fd7284ca1c37fb2dc46c367046a15d093cc501f3155f1e63040313cc8db2a8437ee6dc8ceb04bf924427019b396667f0532d995e3d655b9fb0ef8e61b31e523d81914d9eb177529783c29788d486139e1f3d29cbe4d2f881c61f74ff32a9233134ec69f26082e8aaa0c0e99006a5666c24fccfd195796a0be97cecb257259a640641f8c2d58d2d94452ec00ad84078afc1f7f72f3b9e8210b5db73bf70cd13ef172ef3b233c987d5ec7ea12a4d4921a43fb670c9f48aaae9e1d48ec7be58638a8b2f89a62b56775deddbbc971803316470ee416d8a6c0c8d17982396f6c0c0eeec425d5c599fb60b5c39f8e9ceff4ee25c5bc953178972de616edae61586bb868e463f420e9e09c083662bcf6f0f522f78630792e02e6986f5dd042dfb70100ab59d8a01093b3d89949ea19fe9c596a8681e2a71abe75debd62b985d03d488442aa41cc8993eff0224de62221d39be8bf1d8b26f8f8768e90e5b4b886adaf02a19f55e6d1fd11b004d4e7b170c4f7feaa04b8dad207d6f863d50a251d9a9ce66951de41a3690fec6144e73428d4718cc7ec5eeeff841b4329a7ba51624f678557b6eafc55af026314cbf9dd9ca232977da3cce204899f3048101e0010f42d0076cd494526beea862c72ee48749ba071bcdd1a96c64a0d8f48c6acad7730121021be6323f69505aad8fb6281b7ac4a607d1d241f1fbffc70c4a74c997bb2fb77c452c0077efdea2a6c00704a8bee28326b5e554e1faa48a33963ce2c2e0e2446b4504a05d541bbaf531e1644ad92a2feae5b2eb8851b067e7bd8d7d23d82e63d368983ba44f52901cba7e05cfa35e832ec445a7de50eca670fa90
And use Hashcat to crack it.
$ hashcat -a 0 -m 13100 kebhash /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
hashcat (v6.2.6) starting
* Device #1: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/l/tmptimeout
You can use --force to override this, but do not report related errors.
* Device #2: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/l/tmptimeout
CUDA API (CUDA 12.4)
* Device #1: NVIDIA GeForce RTX 2060 SUPER, 7602/7967 MB, 38MCU
OpenCL API (OpenCL 3.0 CUDA 12.4.131) - Platform #1 [NVIDIA Corporation]
* Device #2: NVIDIA GeForce RTX 2060 SUPER, skipped
OpenCL API (OpenCL 3.0 PoCL 0.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #2 [The pocl project]
* Device #3: cpu-haswell-AMD Ryzen 5 3400G with Radeon Vega Graphics, skipped
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x000fffff mask, 262144 bytes, 5/13 rotates
Rules:
* Zero-Byte
* Not-Iterated
* Single-Hash
* Single-Salt
ATTENTION! Pure (unoptimized) backend kernels selected.
Pure kernels can crack longer passwords, but drastically reduce performance.
If you want to switch to optimized kernels, append -O to your commandline.
See the above message to find out about the exact limits.
Watchdog: Temperature abort trigger set to 90c
Host memory required for this attack: 298 MB
Dictionary cache hit:
* Filename..: /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
* Passwords.: 14344385
* Bytes.....: 139921510
* Keyspace..: 14344385
$krb5tgs$23$sqL-svc$INLANEFREIGHT.LOCAL$msg1/aLnfeirhgt.local:334829a09a5ebf7b29a8e5b579958218abc3af89972d8b0d11f7f25c0f15998012639b37b9cc1b253677bb75cbc569f9e708cd173a5b0e4adc5fc427a80ffcbb1e4
f6de7af81319e2c53bb46ae556a7d5dbe8e40e0a0a89e055e40e469d9aada6257b0295564bc0f9fdf2069edd55dede0c95240a99e2e343ae59b6f2c18a5ba148d3e5d1f9
af6320d867735b64ae280398bf3158340a6215cbbc3e498fd7843e1dfe914ba2f7c3927b88e067d472e1e249d6597f6b4129e54e498af59a5b94bd3535dc12a79e503ea5e4
4bc926bb6b10fdfad7a13b2e4ac293a57112811bff4b173973b1cc668d192dd0c9148b02d863c2e072ab134ae0df0e5b7e719b0f6d9b6b188af9369a791821f660b9e51bd
a874272970e3966fcf7534399e365d59b1ee4cddb7a4168bd7273e89213c91390cfa9e1bd7bda9dbd2d14c288de24ea2486b2a473b7ca5fb7c64c66c3706a1509ce30c158f
1355e1460133268db2a3e37ee06cbe04079e1a9e2dbe62e7ae8970ba91ebd1ba1beac0c6aa58b0cae84503e84bdd279e2b842b7f0d27e763650a2a8a1a32969f0cc156b7b3f
70c41d1ef7e1b33c09f7deae12a404912a4f3e176c49d9e6df213233e9027e208aae8e0099288e6596fdce21f17e7f2208e5b7bbbf03d7929e7aae9968bc0e6f4feae25c5b
957390726d16deade5169bb80e6a3f742e09ec90386c0b6c0ff0252f78631794e229e596f3dbd24b76101b39bda0493be339e9b8d0f5b945dcebd51f119b0e442e471be47df
fea24b8b042d7760b83a025e1959c4ee1342969ff0c6b7adc3f854a31e5e0bdea09d0a7d3ace029dd57fab0e1100e4f24007dcda49526beee89c7e2ee48790ba9f7dbcd119
e50c44a33f1e84a449a22faee5b2be88b51b6e7b7db8d723d8e6e7d368903a4445929c1a7e0c4537de50eca26740e - - - [REDACTED]
What is the cleartext password value for the MS Cache 2 hash?
Copy the hash bellow into a file named hashDDC2.
printf '%s\n' '$DCC2$10240#backup_admin#62dabbde52af53c75f37df260af1008e' > hash
And use Hashcat to crack it.
$ hashcat -m 2100 -a 0 hash.txt /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt --status --status-timer=10
hashcat (v6.2.6) starting
* Device #1: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
* Device #2: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
CUDA API (CUDA 12.4)
* Device #1: NVIDIA GeForce RTX 2060 SUPER, 7586/7967 MB, 34MCU
OpenCL API (OpenCL 3.0 CUDA 12.4.131) - Platform #1 [NVIDIA Corporation]
* Device #2: NVIDIA GeForce RTX 2060 SUPER, skipped
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #2 [The pocl project]
* Device #3: cpu-haswell-AMD Ryzen 5 3400G with Radeon Vega Graphics, skipped
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Rules: 1
Optimizers applied:
* Zero-Byte
* Single-Hash
* Single-Salt
* Slow-Hash-SIMD-LOOP
Watchdog: Temperature abort trigger set to 90c
Host memory required for this attack: 1474 MB
Dictionary cache hit:
* Filename..: /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
* Passwords.: 14344385
* Bytes.....: 139921510
* Keyspace..: 14344385
$DCC2$10240#backup_admin#62dabbd e52af53c75f37df260af1008e:[REDACTED]
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 2100 (Domain Cached Credentials 2 (DCC2), MS Cache 2)
Hash.Target......: $DCC2$10240#backup_admin#62dabbd e52af53c75f37df260af1008e
Time.Started.....: Sun Sep 21 18:05:41 2025 (0 secs)
Time.Estimated...: Sun Sep 21 18:05:41 2025 (0 secs)
Kernel.Feature...: Pure Kernel
Guess.Base.......: File (/usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt)
Guess.Queue......: 1/1 (100.00%)
Speed.#1.........: 349.80 kH/s (9.71ms) @ Accel:32 Loops:256 Thr:128 Vec:1
Recovered........: 1/1 (100.00%) Digests, 1/1 (100.00%) Salts
Progress.........: 139264/14344385 (0.97%)
Rejected.........: 0/139264 (0.00%)
Restore.Point....: 0/14344385 (0.00%)
After cracking the NTLM password hashes contained in the NTDS.dit file, perform an analysis of the results and find out the MOST common password in the INLANEFREIGHT.LOCAL domain.
Download the file and extract it. Next, we need to group the occurrences to determine which one is the most common.
43 db3a9af5e74be03220d213b47ef25b53
16 aebfce03f70c9eaef720f4e1ab6abda23
16 d93d36727cebcb2f9735c08d9cac921a
11 dc265511a1d1a7a3ce6f6d2a3fb6bbe1
7 e13fec8b498d89b3feef27a24d51571d
6 cf3a5525ee9414229e66279263ed5c58
6 54435cc15ac3dc7f043bdf2992c2ae26
3 31ddcfe0d16ae931b73c59d7e0c089c0
2 e97d29ee0107e5fd3d2c0bd47c42c218e
2 c28f9caad8d92092f9fa4e2ad0d2f0c1
2 919c18373c7df8bf61f9f37767d74402
2 624792aacc000631d4e747b9251b9c1b7
2 58a478135a93ac3bf058a5ea0e8fdb71
2 4f09baef15ededfff7fc8039304e4782
2 3218ff2adc0ea3e3ec3aa75b8c9ffb35
2 15d1768caa7a9ee12fc35479c98e672
1 ff8155a21d8ad080fff9593f711c15662
1 ff2248199c684237f35485765efef655
1 ff06b34fbbe8a26680e0ef5ecad16b2a0
1 fefa77275f0559ca01b9fc9dd58ec3897
1 fec6fe44c0bc1d64defe26e80ec6cf26
1 feb8b56b13821cf0b60c1e786f217555
1 fe430b3415c02050ecf0687945254cb4
db3a9af5e74be03220d213b47ef25b53
Insert the hash into a file named hash
echo 'db3a9af5e74be03220d213b47ef25b53' > hash
And crack it using Hashcat.
$ hashcat -a 0 -m 1000 hash /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
hashcat (v6.2.6) starting
* Device #1: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
* Device #2: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
CUDA API (CUDA 12.4)
* Device #1: NVIDIA GeForce RTX 2060 SUPER, 7564/7967 MB, 34MCU
OpenCL API (OpenCL 3.0 CUDA 12.4.131) - Platform #1 [NVIDIA Corporation]
* Device #2: NVIDIA GeForce RTX 2060 SUPER, skipped
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #2 [The pocl project]
* Device #3: cpu-haswell-AMD Ryzen 5 3400G with Radeon Vega Graphics, skipped
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Rules: 1
Optimizers applied:
* Zero-Byte
* Early-Skip
* Not-Salted
* Not-Iterated
* Single-Hash
* Raw-Hash
ATTENTION! Pure (unoptimized) backend kernels selected.
Pure kernels can crack longer passwords, but drastically reduce performance.
If you want to switch to optimized kernels, append -O to your commandline.
See the above message to find out about the exact limits.
Watchdog: Temperature abort trigger set to 90c
Host memory required for this attack: 597 MB
Dictionary cache hit:
* Filename..: /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
* Passwords.: 14344385
* Bytes.....: 139921510
* Keyspace..: 14344385
db3a9af5e74be03220d213b47ef25b53:[REDACTED]
Session..........: hashcat
Status...........: Cracked
