Module 2 — Reconnaissance & Information Gathering
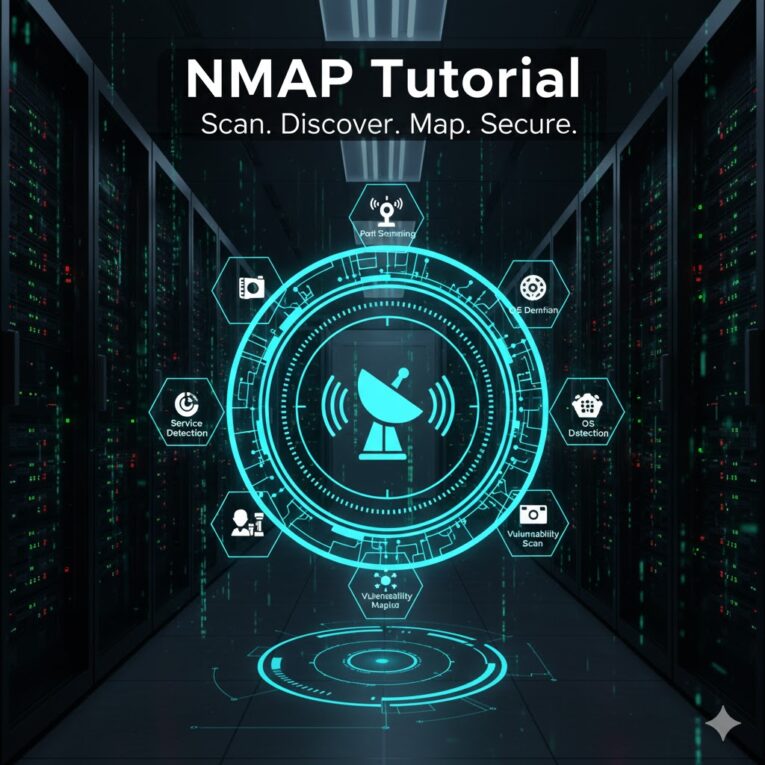
This module takes you from basic reconnaissance to advanced information-gathering techniques specifically for iOS apps and their backends. The goal: build a complete, prioritized map of the attack surface so later static/dynamic analysis and tests are targeted and efficient. Learning objectives By the end of this module you will be able to: Prerequisites Recommended tools … Ler mais