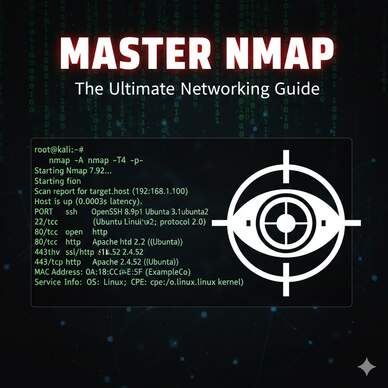
The Swiss Army Knife of Networking: A Comprehensive Guide to Mastering Nmap
If you have ever watched a hacking scene in a movie—from The Matrix Reloaded to Mr. Robot—you have likely seen a black screen with green text scrolling rapidly. While Hollywood often exaggerates cybersecurity, there is one tool they get right almost every time: Nmap. Network Mapper, or Nmap, is the undisputed king of network discovery … Ler mais