During a penetration test, it is very common to transfer files to and from the target system. Whether you’re moving scripts, payloads, or collected data, knowing how to do this efficiently and safely is essential.
This module covers file transfer techniques using tools that are commonly available on both Windows and Linux systems, ensuring that you can operate in almost any environment without relying on specialized software.
Windows File Transfer Methods
The Windows operating system has evolved, and new versions include a variety of utilities for file transfer and execution. Understanding how file transfer works in Windows is important for both attackers and defenders:
- Attackers use these methods to move and execute malicious payloads while minimizing detection.
- Defenders learn how these operations work to monitor activity, implement security policies, and prevent compromise.
Fileless Threat Example: Astaroth APT
The Astaroth attack demonstrates a fileless approach, meaning the attack does not rely on traditional malware files stored on disk. Instead, it uses legitimate system tools to download and execute code directly in memory.
Attack Chain Overview:
- Spear-phishing email – Victim clicks a malicious link leading to an
.LNKfile. - WMIC Execution – The LNK file runs the WMIC tool with the
/Formatparameter, executing malicious JavaScript. - Payload Download via Bitsadmin – The JavaScript downloads additional payloads.
- Base64 Encoding & Decoding – Downloaded payloads are base64-encoded;
Certutildecodes them into DLL files. - DLL Execution –
regsvr32loads one DLL, which decrypts and loads others. - Final Payload Injection – The Astaroth payload is injected into the
Userinitprocess, fully compromising the system.
Download the file flag.txt from the web root using wget from the Pwnbox. Submit the contents of the file as your answer.
$ wget http://127.0.0.1/flag.txt
--2025-05-09 14:31:06-- http://127.0.0.1/flag.txt
Connecting to 127.0.0.1:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 32 [text/plain]
Saving to: ‘flag.txt’
flag.txt 100%[===================>] 32 --.-KB/s in 0s
2025-05-09 14:31:07 (2.58 MB/s) - ‘flag.txt’ saved [32/32]
$ cat flag.txt
[REDACTED]
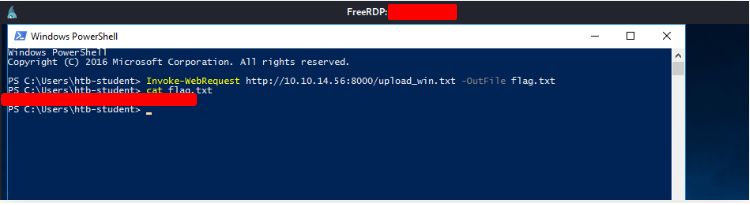
Upload the attached file named upload_win.zip to the target using the method of your choice. Once uploaded, unzip the archive, and run “hasher upload_win.txt” from the command line. Submit the generated hash as your answer.
$ xfreerdp /u:htd-student /p:'HTD' /v:127.0.0.1
In your machine, create a http server in the folder that you copied the file
$ python -m http.server 8000
Serving HTTP on 0.0.0.0 port 8000 (http://0.0.0.0:8000/) ...
Open Powerwhell
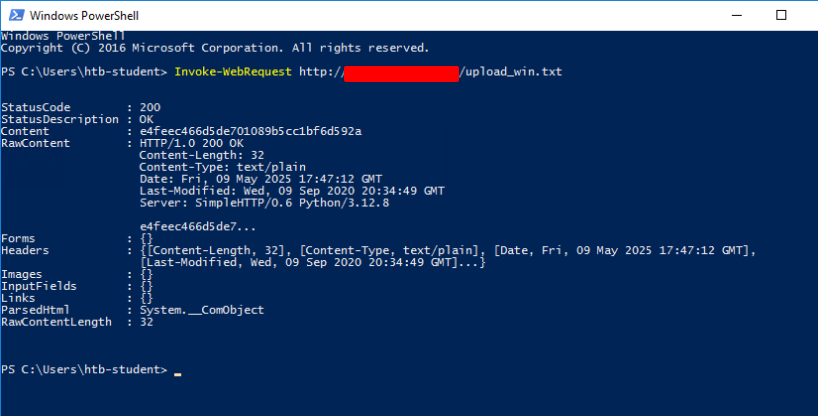
Download the file from your machine and show the content of it
Connect to the target machine via RDP and practice various file transfer operations (upload and download) with your attack host. Type “DONE” when finished.
DONE
Linux File Transfer Methods
Linux is a versatile operating system with numerous built-in tools that can facilitate file transfers. Understanding these methods is important for both attackers and defenders:
- Attackers can move malware or scripts across systems efficiently.
- Defenders can monitor these channels to prevent and detect sophisticated attacks.
Case Study: Linux Incident Response
- Scenario: Incident response was conducted on nine web servers. Six servers were found compromised by threat actors.
- Attack Vector: SQL Injection vulnerability allowed execution of a malicious Bash script.
- Purpose of the Script: To download a second piece of malware that connected to the attacker’s Command & Control (C2) server.
Download Methods Used by the Bash Script
The Bash script attempted three download methods sequentially using HTTP:
- cURL – first choice for HTTP download.
- wget – fallback if cURL failed.
- Python – final fallback using HTTP requests if the other two failed.
Note: Although Linux supports FTP or SMB for file transfers, most malware across OS platforms uses HTTP or HTTPS, making it a universal channel for attackers.
Key Takeaways
This section highlights multiple ways to transfer files on Linux, including:
- HTTP/HTTPS – for universal, stealthy downloads.
- Bash scripts – automation of multi-step download/execution.
- SSH/SCP/SFTP – secure file transfer over encrypted channels.
Understanding these methods equips testers and defenders with the knowledge to perform and defend against sophisticated attacks effectively.
Download the file flag.txt from the web root using Python from the Pwnbox. Submit the contents of the file as your answer.
$ wget -qO- http://127.0.0.1/flag.txt
[REDACTED]
Upload the attached file named upload_nix.zip to the target using the method of your choice. Once uploaded, SSH to the box, extract the file, and run “hasher <extracted file>” from the command line. Submit the generated hash as your answer.
Download the file and create a php server
$ python -m http.server 8000
Serving HTTP on 0.0.0.0 port 8000 (http://0.0.0.0:8000/) ...
127.0.0.1 - - [12/May/2025 12:15:25] "GET / HTTP/1.1" 200 -
127.0.0.1 - - [12/May/2025 12:15:25] code 404, message File not found
127.0.0.1 - - [12/May/2025 12:15:25] "GET /favicon.ico HTTP/1.1" 404 -
127.0.0.1 - - [12/May/2025 12:16:02] "GET /upload_win.txt HTTP/1.1" 200 -
127.0.0.1 - - [12/May/2025 12:16:38] "GET /upload_win.txt HTTP/1.1" 200 -
127.0.0.1 - - [12/May/2025 12:17:57] "GET /upload_win.txt HTTP/1.1" 200 -
127.0.0.1 - - [12/May/2025 12:20:33] "GET /upload_win.txt HTTP/1.1" 200 -
Connect to the server and upload the file
ssh htd-student@127.0.0.1
htd-student@127.0.0.1's password:
Welcome to Ubuntu 20.04 LTS (GNU/Linux 5.4.0-47-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Mon 12 May 2025 02:41:34 PM UTC
System load: 0.0
Usage of /: 36.9% of 15.68GB
Memory usage: 13%
Swap usage: 0%
Processes: 143
Users logged in: 0
IPv4 address for ens192: 127.0.0.1
IPv6 address for ens192: dead:beef::250:56ff:feb0:5fe5
74 updates can be installed immediately.
0 of these updates are security updates.
To see these additional updates run: apt list --upgradable
The list of available updates is more than a week old.
To check for new updates run: sudo apt update
Last login: Sat May 10 17:35:38 2025 from 127.0.0.1
htd-student@password
$ wget http://127.0.0.1:8000/upload_win.txt
--2025-05-12 15:22:26-- http://127.0.0.1:8000/upload_win.txt
Connecting to 127.0.0.1:8000... connected.
HTTP request sent, awaiting response... 200 OK
Length: 32 [text/plain]
Saving to: ‘upload_win.txt’
upload_win.txt 100%[===================>] 32 --.-KB/s in 0s
2025-05-12 15:22:27 (5.07 MB/s) - ‘upload_win.txt’ saved [32/32]
htd-student@password:~$ cat upload_nix.txt
[REDACTED]
htd-student@password:~$ exit
logout
Connection to 127.0.0.1 closed.
Connect to the target machine via SSH and practice various file transfer operations (upload and download) with your attack host (workstation). Type “DONE” when finished.
DONE
Transferring Files with Code
Common Languages on Target Machines
- Linux: Python, PHP, Perl, Ruby (commonly pre-installed)
- Windows: Less common, but can have Python, Ruby, or other languages installed
- Script Execution: Windows has cscript and mshta for executing JavaScript or VBScript. JavaScript can also run on Linux.
Flexibility of Programming Languages
- According to Wikipedia, there are ~700 programming languages.
- Any programming language can be leveraged to:
- Download files from the internet
- Upload files to a server
- Execute instructions on the OS
Practical Application
- Attackers and penetration testers can use these languages to automate tasks, perform post-exploitation activities, or transfer files.
- Choosing the right language depends on:
- Availability on the target system
- Specific functionality required (e.g., HTTP download, file manipulation, process execution)
This section emphasizes examples using common programming languages to perform these tasks, which helps in both offensive and defensive scenarios.
Connect to the target machine via SSH (Username: htd-student | Password:HTD_@password) and practice various file transfer operations (upload and download) with your attack host. Type “DONE” when finished.
DONE
Miscellaneous File Transfer Methods
Beyond the standard methods (HTTP, FTP, SMB, scripting languages), there are several other techniques to transfer files on both Windows and Linux systems:
1. Netcat / Ncat
- Lightweight networking tools that can create TCP or UDP connections.
- Often called the “Swiss army knife” of networking.
- Can be used for:
- Sending files from one machine to another
- Creating reverse shells
- Establishing simple TCP listeners for file transfer
2. RDP (Remote Desktop Protocol)
- Primarily used for remote desktop access to Windows machines.
- Can transfer files by:
- Copy-pasting between local and remote machines
- Mapping local drives on the remote session
3. PowerShell Sessions
- Windows PowerShell can:
- Download files from URLs using
Invoke-WebRequestorInvoke-RestMethod - Upload files via SMB or HTTP
- Execute remote commands and scripts to facilitate file transfers
- Download files from URLs using
These alternative methods are particularly useful when traditional file transfer protocols are restricted or monitored. They are commonly used during penetration tests, post-exploitation, and incident response scenarios.
Use xfreerdp or rdesktop to connect to the target machine via RDP (Username: htd-student | Password:HTD_@password) and mount a Linux directory to practice file transfer operations (upload and download) with your attack host. Type “DONE” when finished.
DONE
Living off The Land
Origin:
- The concept “Living off the land” was introduced by Christopher Campbell (@obscuresec) and Matt Graeber (@mattifestation) at DerbyCon 3.
- It refers to using tools and binaries that are already present on a system to perform actions that may go beyond their original purpose.
LOLBins:
- Short for Living off the Land binaries.
- These are system binaries or scripts that attackers can abuse for tasks such as file transfer, command execution, or privilege escalation.
- The term came from a Twitter discussion about how to classify such binaries.
Resources for LOLBins:
- LOLBAS Project (Windows binaries)
- Aggregates Windows binaries that can be abused.
- GTFOBins (Linux binaries)
- Aggregates Linux binaries that can be abused.
Common functions performed with LOLBins:
- Download – retrieve files from the internet or another host.
- Upload – send files to another host or system.
- Command Execution – run arbitrary commands.
- File Read / Write – access or modify files on the system.
- Bypasses – circumvent security controls like UAC, execution policies, or monitoring.
Focus of This Section:
- How to use LOLBAS (Windows) and GTFOBins (Linux) to perform download and upload operations during penetration testing or post-exploitation.
Connect to the target machine via RDP ((Username: htd-student | Password:HTD_@password)) and use Living Off The Land techniques presented in this section or any other found on the LOLBAS and GTFOBins websites to transfer files between the Pwnbox and the Windows target. Type “DONE” when finished.
DONE
