Definition:
A vulnerability assessment is a systematic process of identifying, quantifying, and prioritizing security weaknesses in a system, network, or application. Unlike a full penetration test, it focuses on detection and reporting rather than exploitation.
Key Differences: Vulnerability Assessment vs Penetration Test
| Aspect | Vulnerability Assessment | Penetration Test |
|---|---|---|
| Goal | Identify and quantify vulnerabilities | Exploit vulnerabilities to assess risk |
| Depth | Surface-level to moderate | Deep, with exploitation |
| Risk to Systems | Low | Higher, potential system impact |
| Output | List of vulnerabilities with severity | Exploitation proof, attack paths |
| Frequency | Often repeated regularly | Usually periodic or engagement-based |
Steps to Conduct a Vulnerability Assessment
- Define Scope
- Identify the systems, applications, and networks to be assessed.
- Information Gathering
- Collect relevant data about systems, versions, and services.
- Vulnerability Scanning
- Use automated tools and scripts to detect known vulnerabilities.
- Analysis of Findings
- Determine which vulnerabilities are exploitable, assess severity, and identify potential business impact.
- Reporting
- Present the findings in a clear, actionable report with recommendations.
Delivering an Effective Vulnerability Assessment Report
- Executive Summary
- High-level overview for management, including key risks and priorities.
- Technical Findings
- Detailed vulnerabilities, affected systems, risk ratings, and evidence.
- Recommendations
- Actionable steps to remediate or mitigate identified risks.
- Appendices
- Include tool outputs, logs, or screenshots for reference.
Nessus Skills Assessment
The team at Inlanefreight has brought us on board to perform an internal vulnerability assessment on one of their servers. Since their budget doesn’t allow for a full-scale penetration test this year, they requested a high-level review to identify any critical vulnerabilities. The insights we uncover could help their CISO make a strong case to the Board of Directors for funding a more comprehensive security evaluation in the future.
The focus of this assessment is a Windows Server used as a development environment, which makes it a key piece of their internal infrastructure.
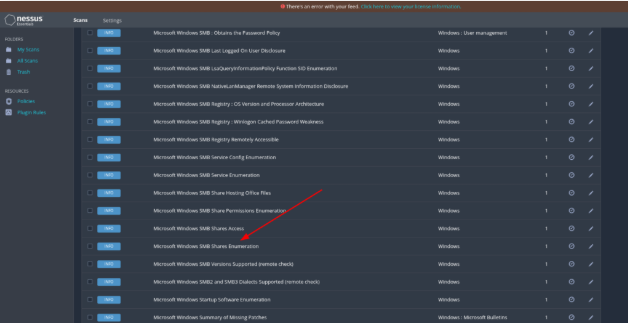
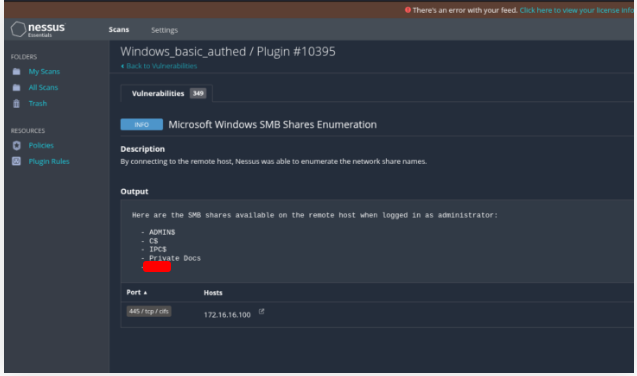
What is the name of one of the accessible SMB shares from the authenticated Windows scan? (One word)
Open the site
Connect to the scan (htd-student:HTD_@password)
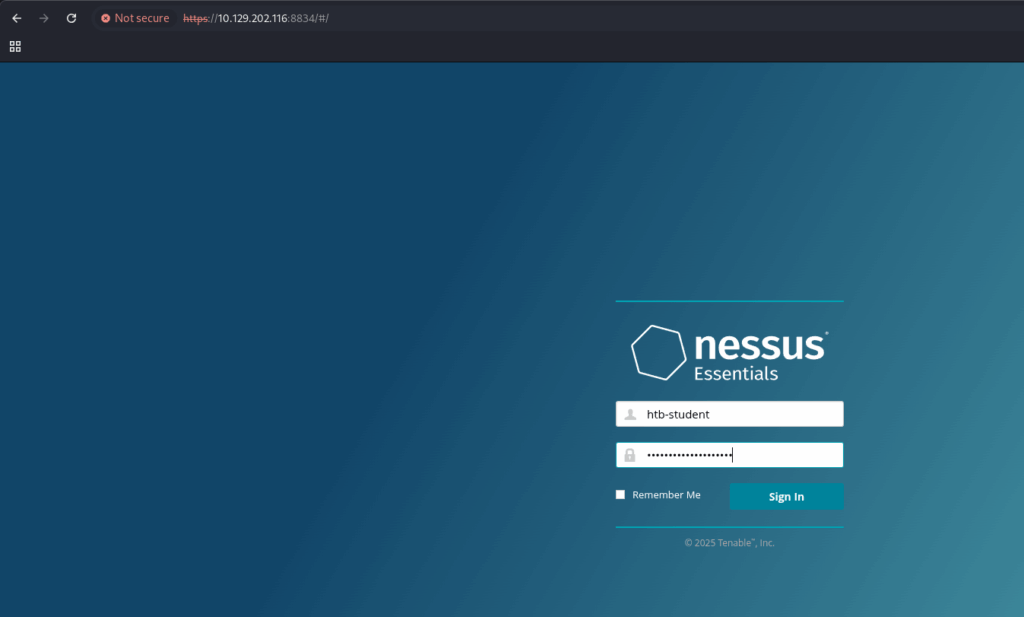
Create a new scan
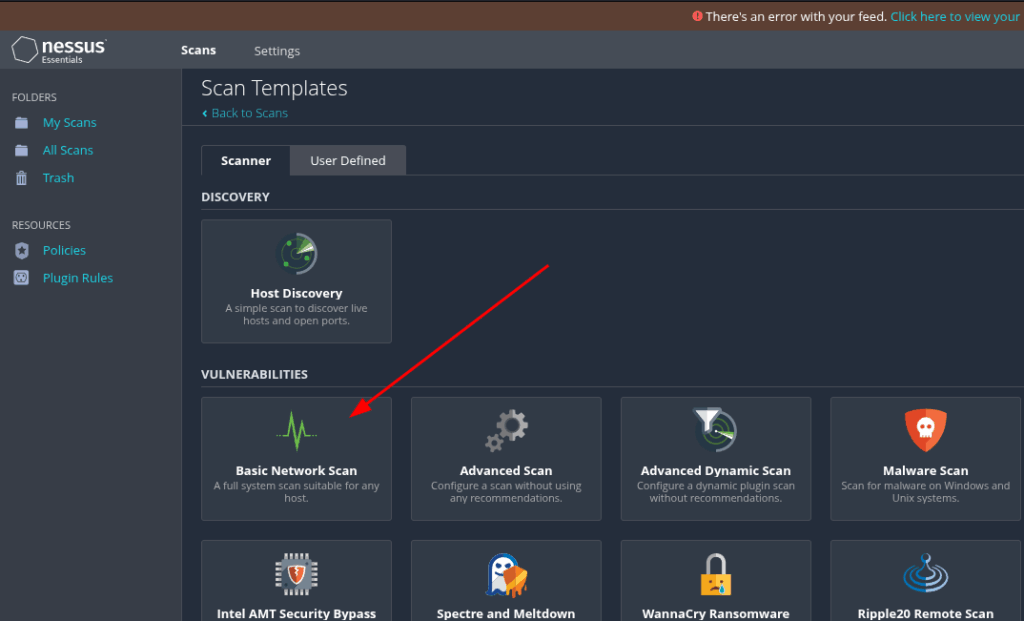
Configure the parameters
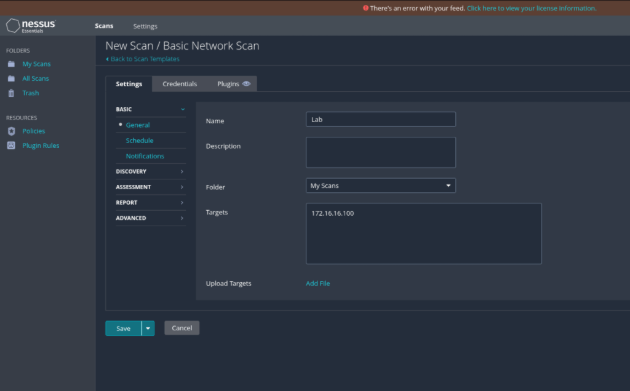
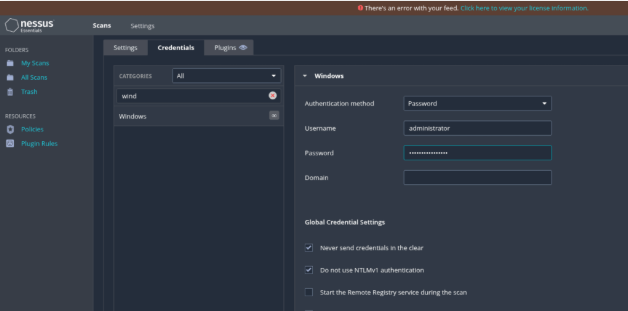
And click in save to start the scanning
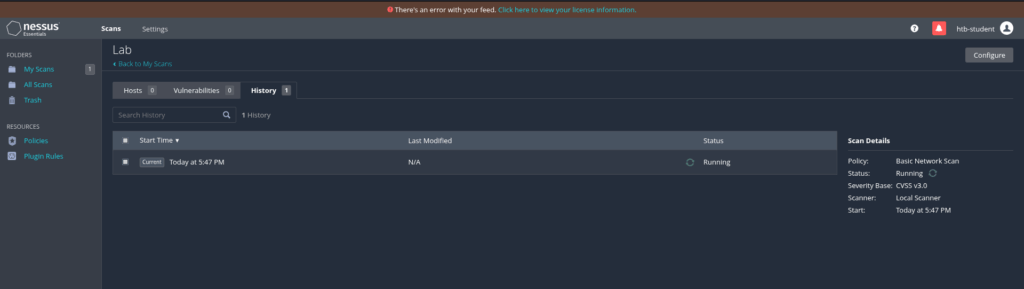
Once that is complete, simply run the scan, it will take about 60 minutes
After finish, you will find the answer
What was the target for the authenticated scan?
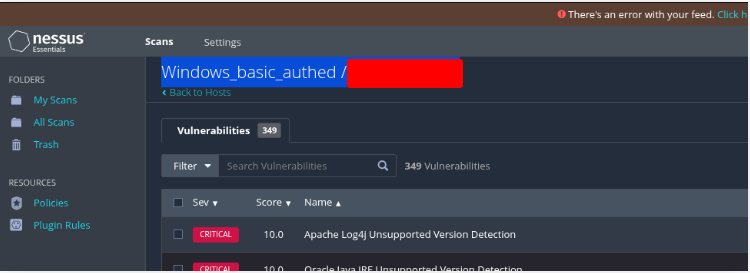
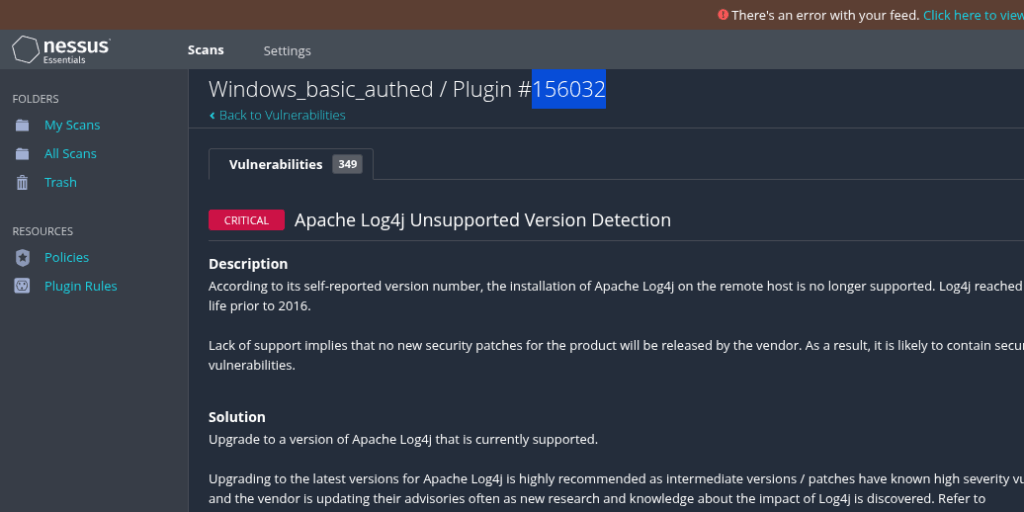
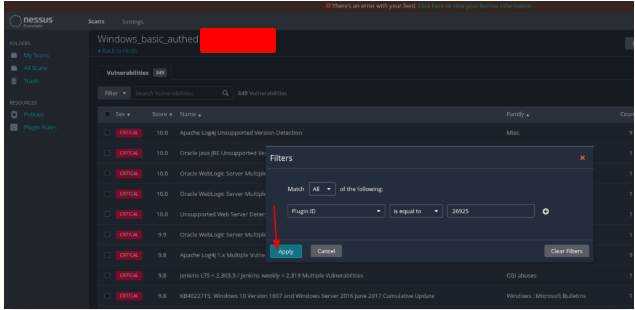
What is the plugin ID of the highest criticality vulnerability for the Windows authenticated scan?
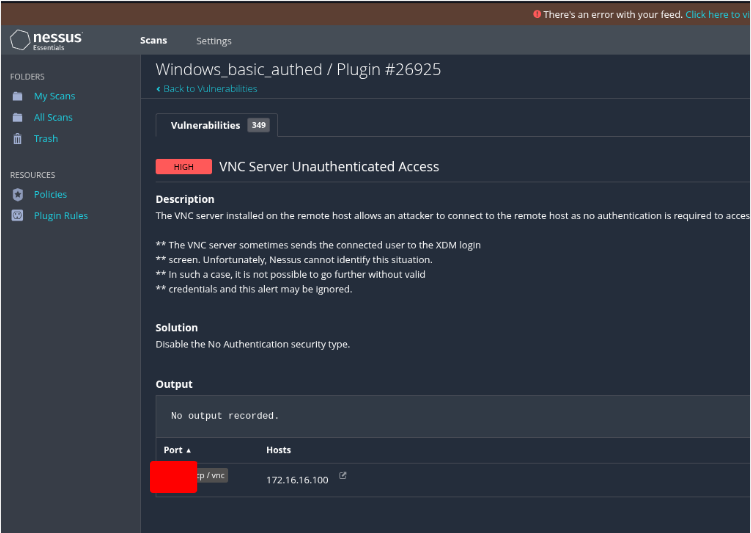
What is the name of the vulnerability with plugin ID 26925 from the Windows authenticated scan? (Case sensitive)
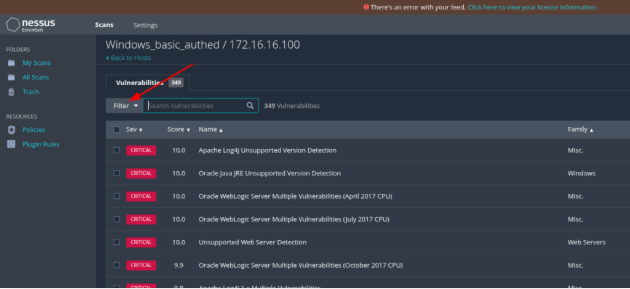
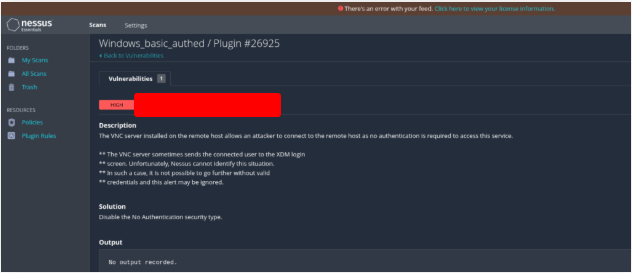
What port is the VNC server running on in the authenticated Windows scan?
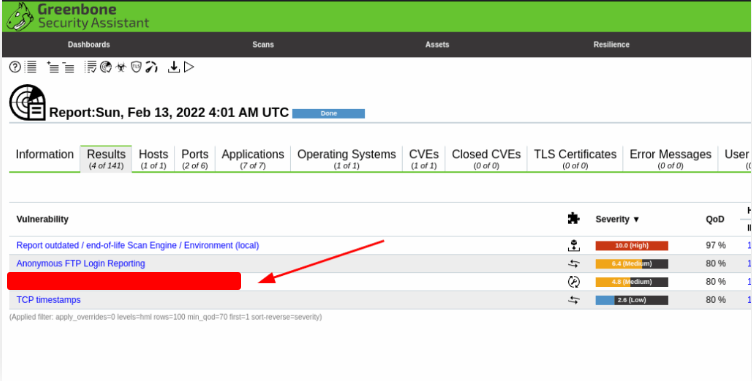
OpenVAS Skills Assessment
Inlanefreight has engaged us to carry out an internal vulnerability assessment on one of their servers. Due to budget constraints, they’ve requested a high-level review to spot any major security issues rather than a full-scale penetration test. The findings from this assessment could give their CISO the data needed to secure additional funding from the Board of Directors for a deeper, more comprehensive security evaluation in the future.
Our focus for this assessment is a Linux server, a critical component of their internal infrastructure.
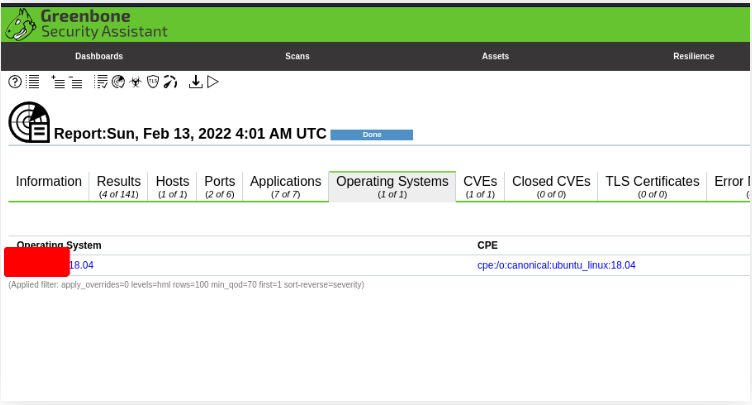
What type of operating system is the Linux host running? (one word)
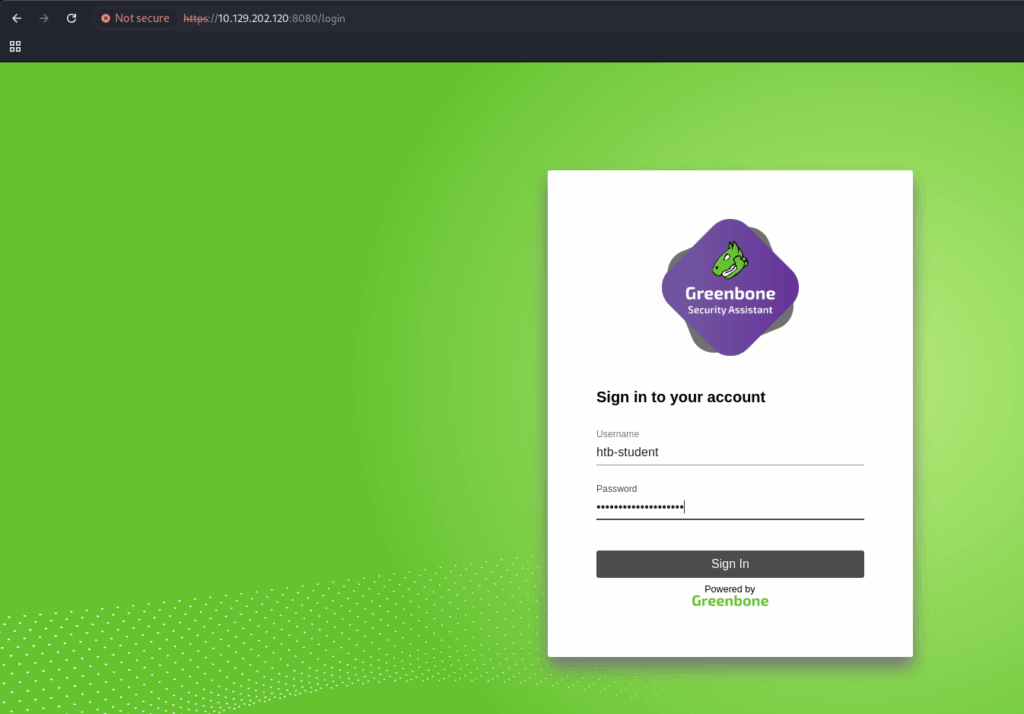
Go to https://127.0.0.1:8080/ and authenticate with htd-student:HTD_@password.
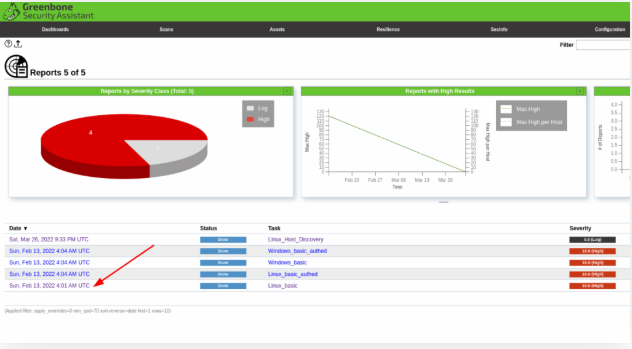
Open the reports choosing Scan -> Reports
What type of FTP vulnerability is on the Linux host? (Case Sensitive, four words)
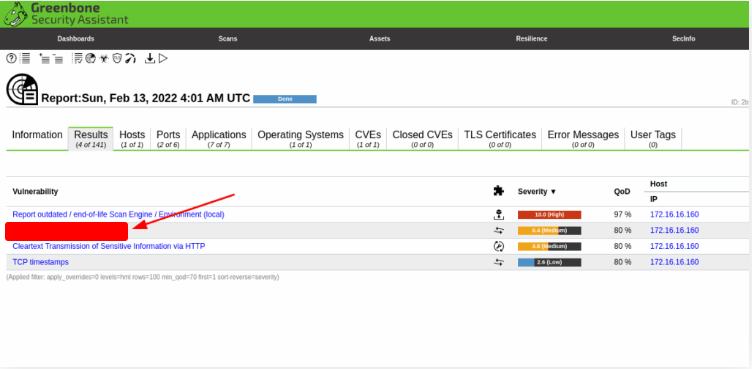
For this one, stay in the reporting section but go to the Results Tab, the answer will straight away be available, which is
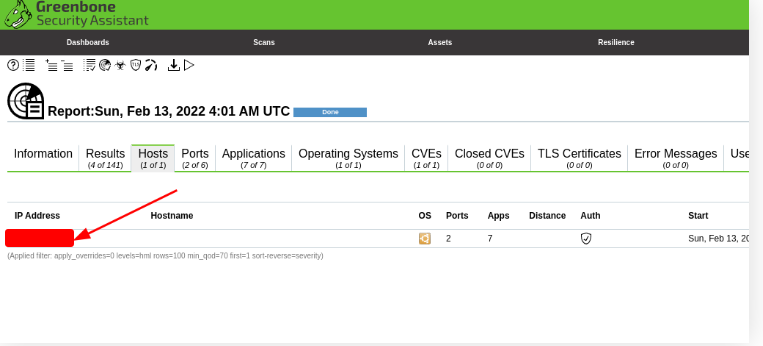
What is the IP of the Linux host targeted for the scan?
For this one, go to the “Hosts” Tab and you will see the IP that the scan was performed against.
What vulnerability is associated with the HTTP server? (Case-sensitive)
Go back to the results section and you will see the HTTP Vulnerability that was identified