If you have ever watched a hacking scene in a movie—from The Matrix Reloaded to Mr. Robot—you have likely seen a black screen with green text scrolling rapidly. While Hollywood often exaggerates cybersecurity, there is one tool they get right almost every time: Nmap.
Network Mapper, or Nmap, is the undisputed king of network discovery and security auditing. Whether you are a seasoned penetration tester, a system administrator troubleshooting connectivity, or a cybersecurity enthusiast, Nmap is likely the first tool you will open in your terminal.
In this comprehensive guide, we will go beyond the basics. We will dissect how Nmap works, explore its most powerful parameters, and dive deep into the Nmap Scripting Engine (NSE) to turn a simple port scanner into a full-fledged vulnerability detector.
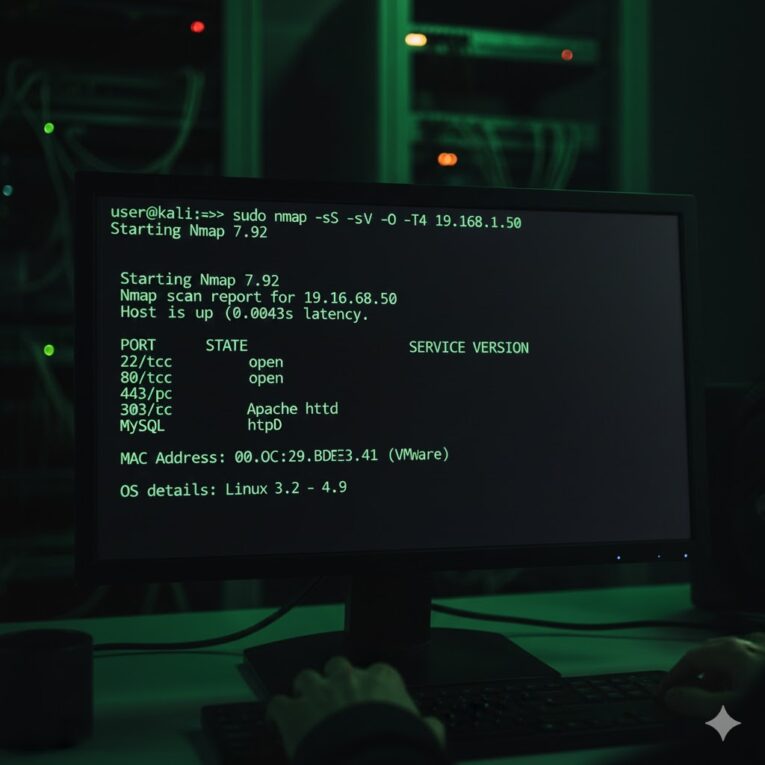
Here is what a typical Nmap scan looks like in action:
Plaintext
user@kali:~$ sudo nmap -sS -sV -O -T4 192.168.1.50
Starting Nmap 7.92 ( https://nmap.org ) at 2023-10-27 10:00 EDT
Nmap scan report for 192.168.1.50
Host is up (0.00043s latency).
Not shown: 996 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
443/tcp open ssl/http Apache httpd 2.4.29 ((Ubuntu))
3306/tcp open mysql MySQL 5.7.33-0ubuntu0.18.04.1
MAC Address: 00:0C:29:BD:E3:A1 (VMware)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 14.32 seconds
What is Nmap and Why Do We Need It?
Created by Gordon Lyon (also known as Fyodor) in 1997, Nmap started as a Linux-only tool but quickly evolved into a cross-platform standard. At its core, Nmap uses raw IP packets in novel ways to determine what hosts are available on the network, what services (application name and version) those hosts are offering, what operating systems (and OS versions) they are running, and what type of packet filters/firewalls are in use.
Why is it indispensable?
- Network Mapping: It creates a map of your network structure.
- Vulnerability Assessment: It identifies open ports that shouldn’t be open.
- Inventory: It helps sysadmins track devices.
- Exploitation: For red teamers, it is the reconnaissance phase foundation.
The Anatomy of a Scan: How Nmap Works
Before throwing flags at the terminal, it is crucial to understand what Nmap is actually doing “under the hood.” Nmap relies heavily on the TCP/IP stack conventions.
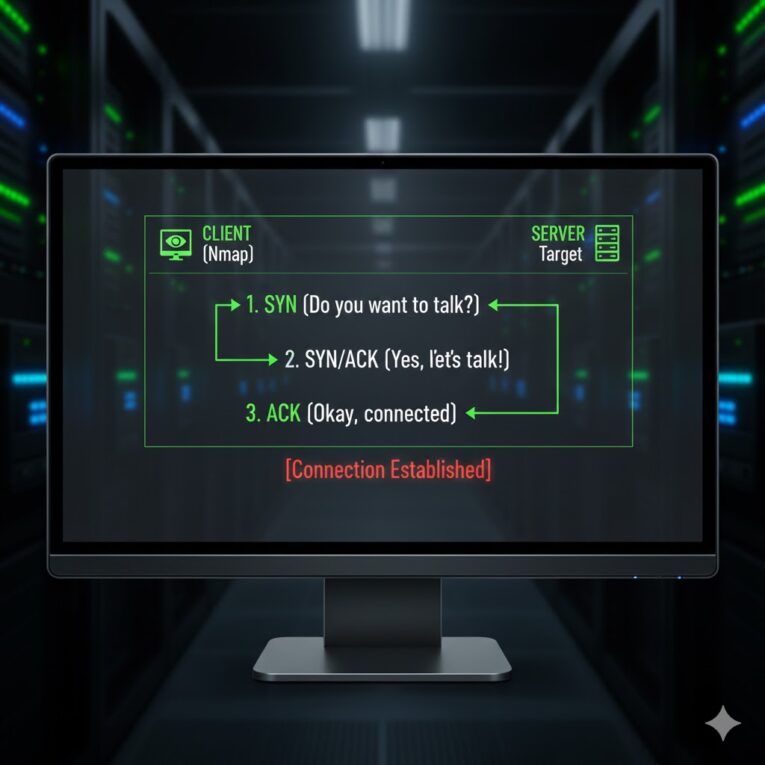
When two computers talk, they usually perform a three-way handshake:
- SYN: The client sends a “synchronize” packet to initiate a connection.
- SYN-ACK: The server acknowledges and sends its own sync request.
- ACK: The client acknowledges the server, and the connection is established.
Nmap manipulates this process to gather intelligence. By sending slightly malformed packets or stopping the handshake halfway, Nmap can determine the state of a port without fully logging a connection on the target machine.1
Plaintext
CLIENT (Nmap) SERVER (Target)
| |
| 1. SYN (Do you want to talk?) |
|------------------------------------>|
| |
| 2. SYN/ACK (Yes, let's talk!) |
|<------------------------------------|
| |
| 3. ACK (Okay, connected!) |
|------------------------------------>|
| |
v [Connection Established] v
The Essentials: Host Discovery and Basic Scanning
The first step in any engagement is finding out who is alive.
Host Discovery (Ping Sweep)
If you want to scan a whole subnet just to see which IPs are active without scanning their ports, use the -sn flag (formerly -sP).
nmap -sn 192.168.1.0/24
This tells Nmap: “Don’t port scan; just tell me who responds to ping.”
The “Big Three” Scan Types
Once you have a target, you need to decide how to scan it. Nmap offers several methods, but these three are the most critical. It helps to visualize how they differ in their approach to the handshake:
Plaintext
TCP CONNECT SCAN (-sT) TCP SYN "STEALTH" SCAN (-sS)
(Noisy, Full Connection) (Quiet, Half-Open)
Nmap Computer Target Port Nmap Computer Target Port
| | | |
|--- SYN ----------->| |--- SYN ----------->|
| | | |
|<-- SYN/ACK --------| |<-- SYN/ACK --------|
| | | |
|--- ACK ----------->| |--- RST (Reset) --->|
| | | |
[Connection Made & Logged] [Connection Dropped before Completion]
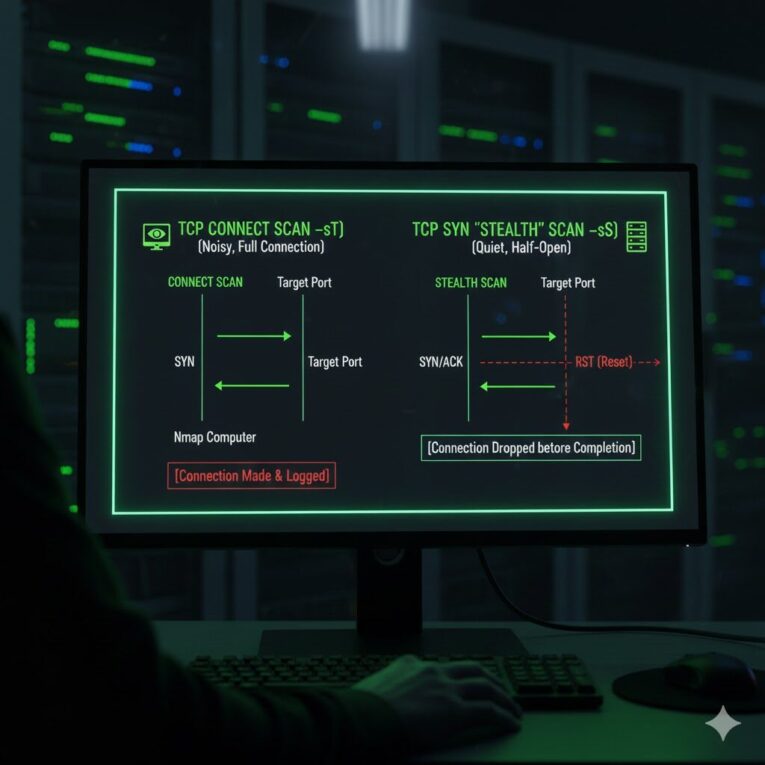
1. TCP SYN Scan (-sS)
This is the default scan for root users and is often called a “Stealth Scan” or “Half-open Scan.”
- How it works: As shown in Figure 3, Nmap sends a SYN packet. If the port is open, the target responds with SYN-ACK. Nmap immediately sends a RST (Reset) packet to tear down the connection before it is fully established.
- Pros: Fast, stealthier (fewer logs on the server), works with almost any TCP stack.
- Cons: Requires root/administrator privileges to craft raw packets.
2. TCP Connect Scan (-sT)
If you don’t have root privileges, Nmap defaults to this.
- How it works: It performs the full 3-way handshake. It asks the operating system to establish a connection with the target port.
- Pros: No root privileges needed.
- Cons: Noisier (appears in application logs), slower.
3. UDP Scan (-sU)
Services like DNS (53), SNMP (161), and DHCP (67/68) run on UDP. A TCP scan will miss these entirely.
- How it works: Nmap sends a UDP packet. If it gets no response, it assumes the port is
Open|Filtered. If it gets an ICMP Port Unreachable error, the port isClosed. - Pros: Finds services TCP misses.
- Cons: Extremely slow. Operating systems limit the rate of ICMP error messages, forcing Nmap to slow down.
Advanced Intelligence: Service Version and OS Detection
Knowing a port is “Open” is good. Knowing what is running on it is better.
Version Detection (-sV)
Standard scanning only looks at the port number. If you run a web server on port 22 (usually SSH), a standard scan will report “SSH”.
Using -sV forces Nmap to interrogate the open port, grabbing banners and analyzing responses to determine the actual service and version.
nmap -sV 192.168.1.10
OS Detection (-O)
Nmap analyzes the TCP/IP stack implementation of the target. Every OS handles packets slightly differently (TCP window size, TTL, etc.). Nmap compares these nuances against its massive database to fingerprint the Operating System.
nmap -O 192.168.1.10
The “Aggressive” Scan (-A)
If you want to throw everything at the target, use -A. This enables:
- OS Detection (
-O) - Version Detection (
-sV) - Script Scanning (
-sC) - Traceroute
Warning: This is very noisy and easy for Intrusion Detection Systems (IDS) to spot.
Port Specification and Timing
By default, Nmap scans the top 1000 most popular ports. In a real pentest, this isn’t enough.
- Scan All Ports:
-p-(Scans ports 1 through 65535). - Specific Ports:
-p 80,443,8080or-p 1-100. - Fast Scan:
-F(Scans top 100 ports).
Timing Templates
Speed matters. Nmap offers timing templates ranging from 0 to 5 (-T0 to -T5).
- -T0 (Paranoid): Extremely slow, used to evade IDS.
- -T3 (Normal): The default.
- -T4 (Aggressive): The industry standard for modern, reliable networks.
- -T5 (Insane): Very fast, but may sacrifice accuracy and miss ports.
Recommendation: Always use -T4 unless you have a specific reason to be slow.
The Powerhouse: Nmap Scripting Engine (NSE)
This is where Nmap transforms from a scanner into a vulnerability assessment framework. The NSE allows users to write (and share) scripts in the Lua programming language to automate a wide variety of networking tasks.
Nmap comes with hundreds of scripts categorized for ease of use. You trigger them using the --script flag. The architecture is simple but powerful:
+------------+
| Nmap Core | (Handles packet sending/receiving)
+------------+
|
v
+------------+
| NSE Engine | (The Lua interpreter)
+------------+
|
| Uses --> [Default Scripts]
| Uses --> [Vuln Scripts]
| Uses --> [Auth Scripts]
|
v
+------------+
| Target Host| (Queries services, checks for bugs)
+------------+
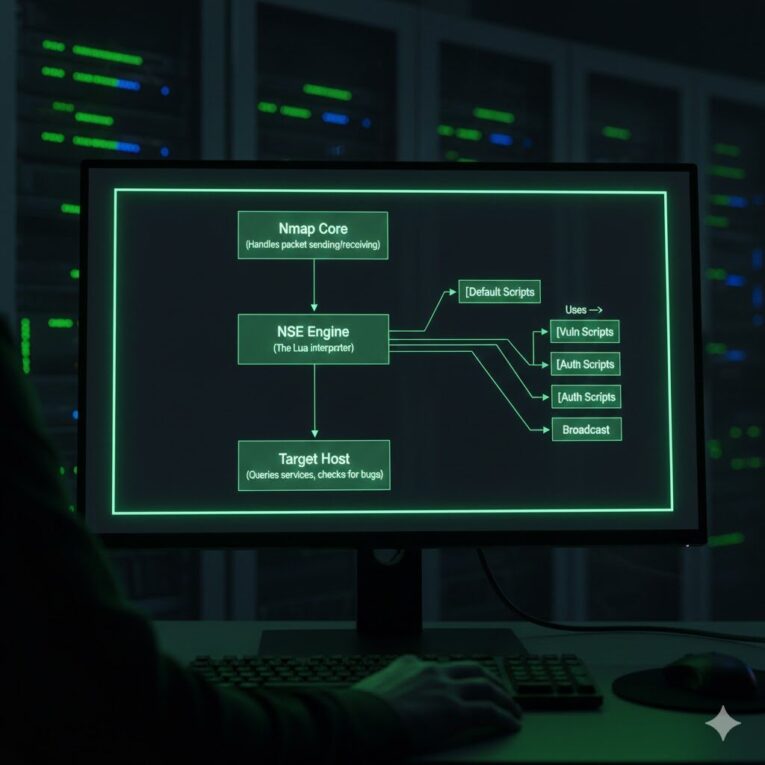
Common Script Categories
- Default (
-sC): A safe set of discovery scripts (equivalent to--script=default). - Vuln: Checks for known specific vulnerabilities (e.g., SMBGhost, Heartbleed).
- Auth: Attempts to find default credentials or bypass authentication.
- Broadcast: Uses broadcast packets to discover hosts not included in the command line.
Essential Script Examples
1. Vulnerability Scanning:
To check a target for common known vulnerabilities:
nmap --script vuln 192.168.1.10
2. HTTP Enumeration:
To discover folders and files on a web server:
nmap --script http-enum 192.168.1.10
3. SMB OS Discovery:
To extract precise Windows versions and computer names:
nmap -p 445 --script smb-os-discovery 192.168.1.10
Advanced Techniques: Evasion and Output
Firewall Evasion
Sometimes, a firewall will block your scan. Nmap has tricks to slip past defenses.
- Fragmentation (
-f): Splits packets into tiny fragments, making it harder for packet filters to analyze the header. - Decoys (
-D): Makes it look like the scan is coming from multiple IP addresses simultaneously, hiding your true IP among the noise.Bashnmap -D RND:10 192.168.1.10(This generates 10 random decoy IPs).
Saving Your Work
Scanning takes time. Never run a scan without saving the output. Nmap offers three formats:
- Normal (
-oN): Human readable text file. - XML (
-oX): For importing into other tools (like Metasploit or Zenmap). - Grepable (
-oG): Easy to parse with command-line tools like grep/awk.
Pro Tip: Use -oA filename to output all three formats at once.
nmap -sS -sV -oA my_scan_results 192.168.1.10
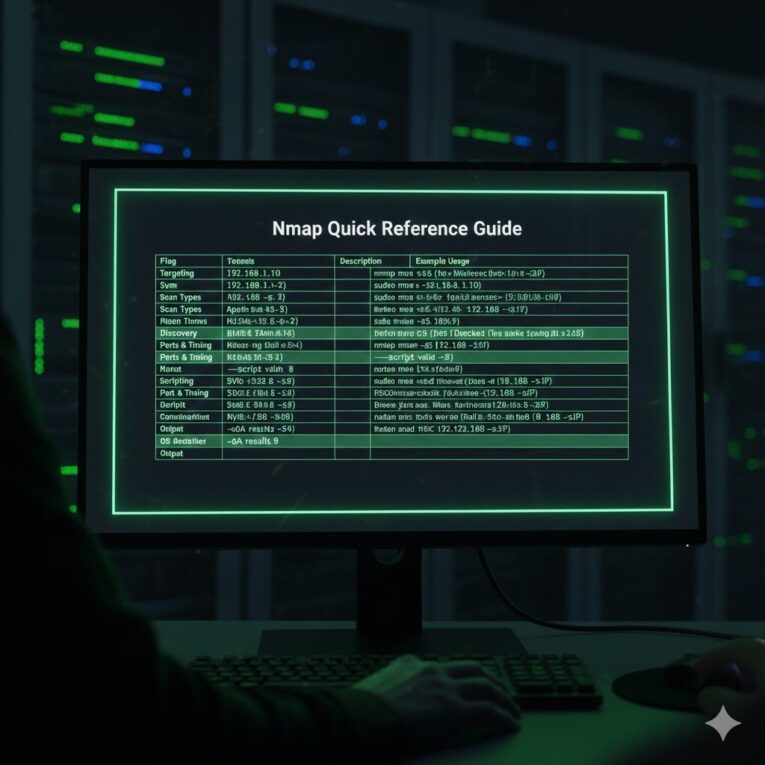
Nmap Quick Reference Guide
For a quick overview of the most common commands and options, refer to the cheat sheet below.
| Flag | Description | Example Usage |
| Targeting | ||
192.168.1.10 | Scan a single IP | nmap 192.168.1.10 |
192.168.1.0/24 | Scan an entire subnet (CIDR) | nmap 192.168.1.0/24 |
| Scan Types | ||
-sn | Ping Sweep (No port scan) | nmap -sn 192.168.1.0/24 |
-sS | TCP SYN Scan (Stealth, needs root) | sudo nmap -sS <IP> |
-sT | TCP Connect Scan (No root needed) | nmap -sT <IP> |
-sU | UDP Scan (Slow) | sudo nmap -sU <IP> |
| Discovery | ||
-sV | Detect Service Versions | nmap -sV <IP> |
-O | Detect Operating System | sudo nmap -O <IP> |
-A | Aggressive (OS, Version, Scripts) | nmap -A <IP> |
| Ports & Timing | ||
-p 22,80 | Scan specific ports | nmap -p 22,80 <IP> |
-p- | Scan all 65535 ports | nmap -p- <IP> |
-T4 | Faster timing template | nmap -T4 <IP> |
| Scripting | ||
-sC | Run default safe scripts | nmap -sC <IP> |
--script vuln | Run vulnerability scripts | nmap --script vuln <IP> |
| Output | ||
-oA <name> | Output in all 3 formats | nmap -oA results <IP> |
Conclusion: The Responsibility of Power
Nmap is a tool of immense power. With a single command, you can map an entire corporate network or identify a critical vulnerability in a server. However, with great power comes great responsibility.
Legal Disclaimer: probing networks that you do not own or have explicit written permission to test is illegal in most jurisdictions. Port scanning can be interpreted as a prelude to an attack. Always ensure you are operating within ethical boundaries and legal frameworks.
Mastering Nmap is a journey. The flags and scripts discussed here are just the tip of the iceberg. As you practice, you will develop your own methodology, combining flags to suit specific environments. Open your terminal, set up a home lab, and start scanning.