Introduction
Windows systems come with two powerful command-line interfaces built in: CMD.exe (Command Prompt) and PowerShell. Both of these tools give users the ability to directly interact with the operating system, automate repetitive tasks, and manage system-level functionality in a way that graphical interfaces cannot. With these tools, administrators can configure services, manipulate files, install or troubleshoot applications, and script complex workflows to save time.
In this module, we focus on how these tools work and how they differ. From a system administration perspective, mastering CMD and PowerShell is essential for effectively managing Windows hosts. From a penetration testing perspective, these same tools can be leveraged to perform reconnaissance, exploitation, persistence, and even data exfiltration inside a Windows environment. As we progress into more advanced topics within The Academy, we will see how understanding these utilities can provide both defensive and offensive advantages.
Command Prompt vs. PowerShell
While both CMD.exe and PowerShell allow direct command-line interaction, they differ significantly in functionality and power. One immediate difference is interoperability: you can execute traditional Command Prompt commands inside a PowerShell console, but if you want to run PowerShell-specific commands inside Command Prompt, you need to prefix them with powershell (for example:
powershell get-alias
Beyond this interoperability, their differences are best summarized in the following table:
| PowerShell | Command Prompt |
|---|---|
| Introduced in 2006 | Introduced in 1981 |
| Runs both batch commands and PowerShell cmdlets | Runs only batch commands |
| Supports command aliases | No alias support |
| Cmdlet output can be piped to other cmdlets | Output cannot be piped between commands |
| Outputs objects | Outputs plain text |
| Executes sequences of cmdlets in scripts | Executes commands sequentially, one after another |
| Includes an Integrated Scripting Environment (ISE) | No ISE available |
| Built on the .NET framework, can access libraries | Cannot access programming libraries |
| Cross-platform: can also run on Linux | Windows-only |
Why the Difference Matters
The Command Prompt is more limited and largely remains a static environment for running basic commands and scripts. It’s useful for simple administrative tasks such as file navigation, batch scripting, and launching executables.
By contrast, PowerShell is a full-fledged scripting language and automation framework. Its integration with the .NET framework allows it to access system libraries and APIs directly, making it capable of handling advanced administrative tasks such as managing Active Directory, querying system logs, or controlling remote systems. It can generate complex scripts, chain cmdlets together using pipelines, and work seamlessly across multiple platforms—including Linux.
For security professionals and penetration testers, PowerShell is particularly valuable. Its flexibility allows for the creation of payloads, system enumeration scripts, and even post-exploitation frameworks. Because of its ubiquity on Windows systems, attackers often rely on PowerShell for “living off the land” techniques—leveraging built-in tools to avoid detection while executing malicious activities.
Command Prompt Basics
Getting started: cmd.exe (Command Prompt)
The first step down the rabbit hole toward developing command-line kung fu is to jump into cmd.exe (the Command Prompt). For your white-belt training, we’ll cover what cmd.exe is, how to open it, and the basic way the shell operates.
What is CMD.exe?
The Command Prompt—commonly called cmd.exe or just CMD—is the classic command-line interpreter built into Windows. It descends from the old DOS COMMAND.COM shell and remains available on virtually every Windows machine. CMD lets you type text commands that the OS interprets and executes directly. Single commands can perform useful administrative tasks, for example:
- Change a user password:
net user alice NewP@ssw0rd - View network configuration:
ipconfig /all - List files in a directory:
dir C:\Users\Public
Because it is text-based, CMD typically uses far fewer system resources than equivalent GUI tools, which can be handy on constrained systems or during remote troubleshooting.
Although PowerShell has largely eclipsed CMD for automation and complex scripting, the Command Prompt still pays dividends: it’s simple, ubiquitous, and often allowed where more powerful tools are blocked.
How to open CMD
You can launch Command Prompt several ways:
- Start menu → type cmd → Enter.
- Press Win + R, type
cmd, press Enter. - Right-click the Start button → Windows Terminal (Admin) or Command Prompt (Admin) to run with elevated privileges.
- From File Explorer: type
cmdinto the address bar and press Enter to open a shell at that folder.
Running as Administrator is often required for tasks such as managing users, editing system files, or changing network settings.
How the shell works — basics you should know
When you open CMD you see a prompt (e.g., C:\Users\alex>). You type commands and press Enter — the shell parses the command, the OS executes it, and output appears in the console. Important basic concepts:
- Commands and arguments:
ping -n 4 8.8.8.8—pingis the command;-n 4and8.8.8.8are arguments. - Batch scripts: Save sequences of commands in a
.bator.cmdfile to automate tasks. Example header:@echo off ipconfig /flushdns netstat -ano - Redirection: Save output to a file:
ipconfig /all > network.txt - Appending:
dir >> listing.txtadds to an existing file instead of overwriting. - Pipes: CMD supports simple piping to pass output between programs:
dir | find "Windows" - Built-in utilities: Many maintenance tools are available (e.g.,
tasklist,taskkill,chkdsk,sfc,netstat,netsh).
CMD’s feature set is smaller than PowerShell’s object-oriented pipeline, but its simplicity is an advantage in constrained environments.
Why CMD still matters for pentesters and admins
Quick story: on several engagements I encountered hosts where PowerShell was tightly locked down via AppLocker or Group Policy. In those cases, Command Prompt was still available and allowed me to continue enumeration and privilege escalation. Legacy and simplified tools like cmd.exe, certutil, bitsadmin, and rundll32 often survive lockdowns and can be used for both defensive troubleshooting and offensive techniques (aka “living off the land”).
Because many production systems still include legacy utilities, admins and assessors should be familiar with them—not only to exploit gaps in testing but to harden systems against misuse.
In what directory can the cmd executable be found? (just the folder name as answer)
Connect to the Windows machine using RDP
xfreerdp3 /v:127.0.0.1 /u:htd-student /p:password
Open Powershell and use the command bellow:
Get-Command cmd.exe | Select-Object Source
PS C:\Users\htd-student> Get-Command cmd.exe | Select-Object Source
Source
------
C:\Windows\[REDACTED]\cmd.exe
Getting Help
In the last section, we learned the basics of the Command Prompt and how to open it. Now, we’re going to build on that knowledge by exploring its built-in help system, looking at example outputs, and reviewing some extra tips and resources.
The Command Prompt comes with a native help feature that gives us detailed explanations about the commands available on our system and instructions on how to use them. In this part, we’ll go over the following topics in more depth:
- How to access and use the help function in Command Prompt
- Why the help function is such an important resource
- Where to find additional external sources of information
- Extra hints and tricks for getting more out of the Command Prompt
Getting Help
When you first open the Command Prompt, the empty screen can feel intimidating. You may find yourself asking questions like:
- Which commands are available to me?
- How do I properly run these commands?
Let’s tackle the first question. To see what’s at your disposal, all you need to do is type help. Running this command without any options or arguments will display a list of built-in commands along with short explanations of how each one is used. Below, we’ll take a closer look at the output it provides.
If I wanted to view the help documentation for ‘ipconfig’, what command and/or modifier would I use? (full command string)
[REDACTED]
What CLI equivalent “Help utility” exists on Linux hosts? (one word)
[REDACTED]
Which CMD hotkey will open an interactive list of the previous commands we have ran?
[REDACTED]
System Navigation
Here’s a rewritten version of your paragraph that keeps the meaning but uses different wording:
So far, we’ve covered the fundamentals to give you a basic sense of how the Command Prompt works. Building on that foundation, our next objective is to use the Command Prompt to navigate the system effectively. In this section we’ll focus on getting comfortable with moving around and inspecting the file structure by:
- Listing the contents of a directory
- Determining our current location in the filesystem
- Changing directories with
cd - Browsing and examining the file system
At the end, we’ll also take a quick look at several Windows folders that may be of interest from an attacker’s point of view. With that roadmap in mind, let’s jump in and start exploring the system together.
Would you like this rewritten as a longer, blog-style section with examples and commands?
What command will give us a listing of all files and folders in a specified path?
[REDACTED]
What command will print my current working directory onto the console?
[REDACTED]
Working with Directories and Files – CMD
Now that you can move around the system from the command line, it’s time to get comfortable working with files and folders. This topic can get deep quickly because Windows offers multiple ways to do the same things; we’ll cover some common approaches but remember there are many alternatives. Let’s jump in.
What is a directory?
A directory is simply a folder within the Windows filesystem — a place that holds files and other folders. You navigate the directory tree using the same commands we practiced earlier (for example, cd and dir).
To reuse our hallway hotel analogy and make directories easier to visualize:
- The drive (for example,
C:) is the whole building — the root of the filesystem, like a hotel. - That hotel has floors — top-level directories such as
Windows,Users, andProgram Files. - Each floor contains hallways, which are folders nested inside those top-level directories. For example, under
C:\Usersyou’ll find a folder for each account on the machine (e.g.,C:\Users\htd) — this is several levels down in the tree. - As more software gets installed or the system is used, new hallways and rooms (more directories and subdirectories) appear.
- Finally, a file is like a room behind a door inside a hallway — when you open the door you “look inside” the file.
What command can display the contents of a file and redirect the contents of the file into another file or to the console?
[REDACTED]
What command can be used to make the ‘apples’ directory? (full command as answer, not the alias)
[REDACTED]
Gathering System Information
Now that you can navigate a Windows host using only the Command Prompt, it’s time to focus on a core skill used by both system administrators and penetration testers: collecting system information.
Also called host enumeration, gathering system details can look intimidating at first, but it’s an essential step for building a reliable picture of the environment. Understanding the host and its context helps both sides of the security equation:
- Red teamers (pen testers, red-team operators, ethical hackers) use enumeration to discover running services, misconfigurations, and potential attack paths.
- Blue teamers (system administrators, SOC analysts, defenders) use the same data to troubleshoot, harden systems, and verify integrity across the network.
No matter which role you’re preparing for, this section will cover:
- The types of information you can collect from a host.
- Why thorough enumeration matters and how it influences next steps.
- How to retrieve this information with Command Prompt and a simple, repeatable approach you can follow.
What command will output verbose system information such as OS configuration, security info, hardware info, and more?
[REDACTED]
Access the target host and run the ‘hostname’ command. What is the hostname?
PS C:\Users\htd-student> hostname
[REDACTED]
PS C:\Users\htd-studen
Finding Files and Directories
Now that you can confidently create, edit, move, and delete files and folders, it’s time to dive into a pivotal skill for both system admins and penetration testers: enumeration. In this expanded section we’ll show how to locate specific files and directories using the Command Prompt, explain why a methodical file-system survey matters for both offensive and defensive work, and provide a compact, prioritized checklist of artifacts and locations you should pay close attention to while enumerating a Windows host. We’ll also touch on practical tips and common command patterns to speed up searches, how to interpret results, and which findings typically deserve immediate follow-up.
What command can be used to search for regular expression strings from command prompt?
[REDACTED]
Using the skills acquired in this and previous sections, access the target host and search for the file named ‘waldo.txt’. Submit the flag found within the file.
Search for the file
where /R c:\ waldo.txt
c:>where /R C:\ waldo.txt
C:\Users\MTanaka\Favorites\waldo.txt
Read the file
c:\>type C:\Users\MTanaka\Favorites\waldo.txt
[REDACTED]
Environment Variables
Now that we’ve built a solid foundation with the Command Prompt, it’s time to turn our attention to one of the most important concepts for understanding how Windows applications and scripts function: Environment Variables. These variables are essentially key-value pairs that define important system information, such as the location of executables, user profiles, or temporary storage paths.
In this section, we’ll break down what environment variables actually are, why they play such a vital role in both everyday administration and penetration testing, and how they influence the way applications interact with the operating system. We’ll also cover practical scenarios where these variables make life easier—like customizing the shell, pointing software to the right directories, or troubleshooting misconfigured paths. Finally, we’ll walk through the different ways you can view, modify, and manage environment variables directly from the Command Prompt, giving you full control over how your system interprets and executes commands.
What variable scope allows for universal access?
[REDACTED]
Managing Services
Monitoring and managing services on a machine is a core responsibility for administrators. From an attacker’s perspective, being able to inspect services, identify reliable attack points, and start or stop services is extremely valuable after gaining access to a host. In this section we’ll focus on the sc service control utility built into Windows — but we’ll approach it through the attacker’s lens. Imagine you’ve just gained a foothold on a victim machine and need to:
- Enumerate which services are running.
- Attempt to disable or evade the antivirus.
- Modify existing services to alter behavior or persistence.
We can walk through practical sc commands, example outputs, and operational trade-offs for each task if you want—either from a defensive hardening standpoint or as part of an authorized penetration test scenario.
What command string will stop a service named ‘red-light’? (full command as the answer)
[REDACTED]
What Windows executable will allow us to create, query, and modify services on a host?
[REDACTED]
Working With Scheduled Tasks
Scheduled tasks provide administrators with a reliable way to run recurring jobs, but they also serve as a favored persistence mechanism for attackers. In this section we’ll cover how to use the schtasks utility to:
- Inspect which scheduled tasks are present on the system.
- Create new scheduled tasks to automate routine actions — or, in an offensive testing scenario, to spawn a shell or establish persistence on the host.
True or False: A scheduled task can be set to run when a user logs onto a host?
[REDACTED]
Access the target host and take some time to practice working with Scheduled Tasks. Type COMPLETE as the answer when you are ready to move on.
[REDACTED]
CMD Vs. PowerShell
So far we’ve worked with the classic Windows command-line interpreter, cmd.exe. Now we’ll switch focus to Windows’ newer and far more capable shell: PowerShell. This section explains what PowerShell is, how it differs from CMD, how to get help inside the shell, and the basics of navigating within it.
What is PowerShell?
PowerShell is a modern command-line shell and scripting language designed to be extensible and highly automatable. Unlike the legacy CMD environment, PowerShell works with structured objects (not just text), integrates tightly with the .NET ecosystem, and can be extended with modules and cmdlets. It’s cross-platform (available on Windows, Linux, and macOS) and can run traditional batch/CMD commands as well as PowerShell-specific commands and aliases.
How PowerShell differs from CMD
Both shells ship with Windows, so you might ask: why use one instead of the other? The table below summarizes the key differences.
PowerShell vs CMD (high-level)
- Language:
- CMD: Batch-style commands and simple built-ins.
- PowerShell: Native cmdlets, scripting constructs, plus support for batch/CMD commands and aliases.
- Command composition:
- CMD: Pipes and redirection operate on plain text; passing structured data between commands is limited.
- PowerShell: Commands return objects, so you can pipe rich, structured data between commands for powerful one-liners.
- Output format:
- CMD: Text only.
- PowerShell: Objects with properties and methods (displayed as formatted text but manipulable programmatically).
- Parallelism:
- CMD: Executes commands sequentially.
- PowerShell: Supports multi-threading and parallel execution patterns (e.g.,
ForEach-Object -Parallelin newer versions).
PowerShell was designed for extensibility and integration. It’s not just another CLI — it’s a full scripting environment that can automate complex administration tasks and interact with many platforms and APIs.
Why PowerShell matters (who uses it and why)
PowerShell is widely adopted across IT and security disciplines because it enables automation and deep system control. Common use cases include:
- Provisioning and configuring servers and roles
- Managing Active Directory users, groups, and permissions
- Creating and enforcing file-share permissions
- Interacting with Azure AD, Azure resources, and Microsoft 365 services
- Automating file and directory operations, backups, and monitoring
- Gathering system inventory and diagnostic data
- Managing Exchange mailboxes (cloud and on-premises)
For system administrators, PowerShell dramatically reduces manual work and supports large-scale automation. For penetration testers, PowerShell is valuable because it brings many built-in capabilities and easy module import, letting tools run inside the environment. But that same power has trade-offs: PowerShell’s advanced logging and history features make it easier for defenders to detect and audit actions, so if stealth is required and PowerShell isn’t necessary, cmd.exe may leave fewer artifacts.
What command string can we use to view the help documentation for the command Get-Location? (full string)
[REDACTED]
What command can we use to show us our current location on the host system?
[REDACTED]
What hotkey can be used to clear our input line completely?
[REDACTED]
All About Cmdlets and Modules
In this section we’ll answer three practical questions:
- What are cmdlets and modules?
- How do we work with them in PowerShell?
- How can we install and load new modules from online sources?
Understanding these concepts is essential whether you’re a systems administrator or a penetration tester. PowerShell’s modular design and extensibility are what make it such a powerful tool—so let’s break down the pieces.
What is a cmdlet?
A cmdlet (pronounced “command-let”) is a lightweight, single-purpose command in PowerShell that operates on objects. Microsoft describes a cmdlet as “a single-feature command that manipulates objects in PowerShell.” Cmdlets typically follow a clear Verb-Noun naming convention (for example, Test-WSMan), which makes their purpose easier to infer: the part before the dash is the action (Verb) and the part after is the target (Noun).
Cmdlets behave much like functions in other languages, but one important difference is implementation: most cmdlets are implemented in compiled languages such as C# (not written in the PowerShell scripting language itself). To discover what commands and utilities are available on a system you can use Get-Command. To inspect what options (parameters) a cmdlet accepts and to read its documentation you can run Get-Help. To explore the properties and methods that a cmdlet’s output exposes (so you can pipe and manipulate the results) use Get-Member.
What is a PowerShell module?
A module is a packaged collection of PowerShell functionality that’s easy to distribute and reuse. A module can contain one or more of the following:
- Cmdlets
- Script files and functions
- Compiled assemblies (DLLs)
- Supporting files such as manifests and help documentation
Modules let authors bundle related functionality together so users can import a single unit and immediately gain access to many commands and helpers.
Example: using PowerView (PowerSploit) as a learning aid
To illustrate modules in the wild, we’ll reference PowerView.ps1, a script/module originally distributed as part of the PowerSploit collection by the PowerShellMafia. PowerSploit is a suite of PowerShell tools that many penetration testers have used for Windows/Active Directory reconnaissance and exploitation. While some of the project repositories may be archived, many of the techniques and scripts remain relevant for learning how modules are structured and how they expose cmdlets and functions.
We won’t perform a full PowerSploit tutorial here; instead we’ll use PowerView as a concrete example to examine how modules are organized and how you interact with the commands they provide. If you later want, I can show how to import a module, list its exported functions, and safely run a few read-only enumeration commands to see their output and available properties.
What cmdlet can help us find modules that are loaded into our session?
[REDACTED]
What module provides us with cmdlets built to manage package installation from the PowerShell Gallery?
[REDACTED]
Take a moment to practice installing and loading modules on the target host. Answer “COMPLETE” when done.
[REDACTED]
User and Group Management
For a system administrator, managing users and groups is one of the most fundamental responsibilities. Users represent the people who need access to systems and data, while groups allow administrators to apply permissions and policies more efficiently across multiple accounts. Since users are often the largest and most unpredictable element of any environment, they also tend to be the primary attack vector for adversaries.
From a penetration tester’s perspective, learning how to enumerate, analyze, and exploit user and group configurations can be one of the quickest ways to gain a foothold or escalate privileges inside a target network. Misconfigured accounts, excessive group memberships, or weak administrative boundaries often open the door for privilege abuse.
In this section, we will:
- Define what users and groups are in the Windows ecosystem.
- Show how to manage and enumerate them using PowerShell cmdlets.
- Provide a short introduction to Active Directory (AD) domains and domain users, where user and group management extends beyond a single machine and into the entire enterprise.
By the end, you’ll understand not only how to create, remove, and query users and groups with PowerShell, but also why this knowledge is equally critical for defenders and attackers alike.
What resource can provide Windows environments with directory services to manage users, computers, and more? (full name not abbreviation)
[REDACTED]
What PowerShell Cmdlet will display all LOCAL users on a host?
[REDACTED]
Connect to the target host and search for a domain user with the given name of Robert. What is this users Surname?
Connect to the server using the user mtanaka
ssh mtanaka@127.0.0.1
# password: password
Import AD module and query the user
Import-Module ActiveDirectory
Execute the command bellow
Get-ADUser -Filter {GivenName -eq "Robert"} -Properties Surname | Select-Object Name,GivenName,Surname,SamAccountName
Get the surname 🙂
PS C:\Users\MTanaka> Import-Module ActiveDirectory
PS C:\Users\MTanaka> Get-ADUser -Filter {GivenName -eq "Robert"} -Properties Surname | Select-Object Name,GivenName,Surname,SamAccountName
Name GivenName Surname SamAccountName
---- --------- ------- --------------
Robert Loxley Robert [REDACTED] RLoxley
Working with Files and Directories – PowerShell
Now that we can move around the host and manage users and groups using only PowerShell, it’s time to focus on files and directories. In this section we’ll practice creating, editing, moving, and deleting files and folders, and we’ll introduce the basics of file permissions and how to enumerate them. By now you should be familiar with common verb patterns like Get, Set, and New; to stay efficient we’ll often combine multiple cmdlets into single, practical command sequences—just like an experienced sysadmin or pentester would.
Working with files and directories
Many PowerShell cmdlets are purpose-built for filesystem tasks, and a single workflow will frequently use several of them together. For example, you might New-Item to create a folder, Get-ChildItem to list its contents, Set-Content to write a file, and Remove-Item to clean up afterward. Combining these operations into compact one-liners or short scripts speeds up repetitive tasks and keeps your session tidy.
Quick concepts to keep in mind
- PowerShell treats items (files, folders, registry keys, etc.) as objects — you can inspect properties and methods and pipe objects between commands.
- Common verbs (
Get,New,Set,Remove,Copy,Rename,Add,Clear) map intuitively to typical file-system actions. - Use
Get-Help <Cmdlet>to view usage examples and parameter descriptions for any cmdlet.
Common cmdlets for file & folder management
Below are commonly used commands when working with file system objects in PowerShell, along with commonly used aliases you’ll see in scripts or legacy shells:
- Get-Item (
gi) — Retrieve a specific object (file, folder, registry key, etc.). - Get-ChildItem (
ls,dir,gci) — List the contents of a directory (or registry hive). Supports wildcards and recursion. - New-Item (
md,mkdir,ni) — Create a new object (file, directory, symbolic link, registry entry, and more). - Set-Item (
si) — Change an object’s property values or replace the item at a path. - Copy-Item (
copy,cp,ci) — Duplicate an item to another path. - Rename-Item (
ren,rni) — Rename a file or directory. - Remove-Item (
rm,del,rmdir) — Delete a file or folder (supports-Recursefor non-empty directories). - Get-Content (
cat,type) — Show the contents of a file (supports streaming and reading line-by-line). - Add-Content (
ac) — Append text to the end of a file without overwriting existing content. - Set-Content (
sc) — Overwrite a file with new contents. - Clear-Content (
clc) — Empty a file’s contents while leaving the file itself intact. - Compare-Object (
diff,compare) — Compare two objects or files and show differences (useful for config diffs).
Example workflows (short)
- Create a directory and a file inside it:
New-Item -Path C:\Temp\Reports -ItemType Directory; New-Item -Path C:\Temp\Reports\notes.txt -ItemType File - View and append to a file:
Get-Content C:\Temp\Reports\notes.txt; Add-Content C:\Temp\Reports\notes.txt -Value "Collected on $(Get-Date)" - Copy and then remove a folder (recursive):
Copy-Item -Path C:\Temp\Reports -Destination D:\Backups\Reports -Recurse; Remove-Item -Path C:\Temp\Reports -Recurse
File permissions and enumeration (brief intro)
Understanding ACLs and permissions is essential: a file’s access control determines who can read, write, execute, or modify it. PowerShell exposes ACLs as objects you can query and modify:
- Retrieve an ACL:
Get-Acl C:\path\to\file.txt - View effective permissions or audit entries by inspecting the returned object (use
Get-Memberto see properties). - Modify permissions with
Set-Aclor helper cmdlets from modules (be cautious — changing ACLs can lock users or services out).
Putting it together
In later examples we’ll combine these cmdlets into compact sessions that demonstrate practical tasks: building a directory structure, seeding files with test data, enumerating permissions, and safely cleaning up. These combined examples will show how an operator (or tester) moves quickly through the filesystem using PowerShell’s object-oriented approach.
What Cmdlet has an alias of “cat” ?
[REDACTED]
What Cmdlet can we use to create new files and folders?
[REDACTED]
Using the skills discussed in this section, practice creating, editing, and removing files and directories on the target host provided. Type COMPLETE as the answer below when you are ready to move on.
[REDACTED]
Finding & Filtering Content
Being able to search, filter, and locate specific content is a core requirement for anyone working in a command-line environment, no matter which shell or operating system is in use. In PowerShell, however, the way this is achieved is a little different compared to Bash or cmd. Instead of treating everything as plain text, PowerShell works with objects. This object-oriented approach gives us much more control when filtering and manipulating output.
In this section, we’ll break down the fundamentals of how PowerShell represents data, explain what objects, classes, properties, and methods are, and then set the stage for working with the PowerShell pipeline to filter and search effectively.
Why Objects Matter in PowerShell
Unlike cmd.exe or Bash, where command outputs are text strings that must be parsed with tools like grep or awk, PowerShell commands return structured objects. This means every piece of information has context and can be accessed directly through its properties and methods. Understanding this difference is the key to unlocking the real power of PowerShell.
Key Concepts
- Object
An object is a single instance of a class in PowerShell. Think of a computer as an object: it exists as a whole entity but is built from many different parts. - Class
A class is the blueprint that defines what an object looks like and what it can do. Continuing our computer analogy, the design specifications (CPU, RAM, storage, software stack, etc.) form the class. Every actual computer we build from that blueprint is an object. - Properties
Properties are the data associated with an object — the details that describe it. For a computer, these would be the individual components like the processor, hard drive, graphics card, and operating system. In PowerShell, properties are what we can query, sort, or filter against. - Methods
Methods are the actions or functions that an object can perform. Using our computer example, tasks such as processing data, connecting to Wi-Fi, or running a program represent methods. In PowerShell, calling a method executes a built-in function tied to the object.
Why This Matters for Searching and Filtering
By recognizing that PowerShell deals with objects rather than raw strings, you gain precise control. Instead of scanning unstructured text, you can filter directly against object properties. For example, when listing processes with Get-Process, you can filter on memory usage, process name, or ID without ever parsing text output.
Next Steps: Filtering and the Pipeline
With this foundation in mind, we’re ready to move on to the PowerShell pipeline — the mechanism that allows us to pass objects from one command to another. We’ll see how to use filtering cmdlets such as Where-Object and Select-Object to isolate exactly the information we want, and how to combine these into efficient one-liners.
What defines the functions our objects have?
[REDACTED]
What Cmdlet can show us the properties and methods of an object?
[REDACTED]
If we wanted to look through a directory and all sub-directories for something, what modifier would we use with the Get-ChildItem Cmdlet?
[REDACTED]
Working with Services
In the last section, we learned how to filter output through the pipeline, looking at services from the perspective of a penetration tester. Now let’s flip the script and approach the same concept from the perspective of an administrator, where the focus is on security, stability, and troubleshooting.
Scenario: A Suspicious Pop-Up
Imagine this situation:
Mr. Tanaka contacts the Helpdesk after noticing a mysterious window flash on his screen earlier in the day. He assumed it was Windows Update, but later he began receiving alerts that Windows Defender had been disabled. On top of that, his computer now feels sluggish.
As administrators, our task is clear:
- Investigate which Defender-related services are disabled.
- Attempt to restart or re-enable them.
- Later, dig into the event logs to trace how and when this happened.
This scenario underscores why service administration is not just about convenience — it’s a critical part of maintaining the security posture of a host.
Why Services Matter
Services in Windows are the backbone of how applications and core OS components run in the background. Unlike standard applications, they don’t require user interaction and rarely have a visible interface. At their core, services are long-running, single instances that manage critical processes.
To clarify:
- A service is a background component running on the host.
- A process is a temporary execution container created when an application or user task is launched. A single service can spin up and manage multiple processes.
Windows organizes services into three broad categories:
- Local Services – operate with limited privileges and no network identity.
- Network Services – run with enough permissions to interact with the network securely.
- System Services – high-privilege services tied closely to the OS itself.
Understanding which category a service belongs to is vital. Shutting down the wrong one could cause system instability, while attackers disabling a protective service (like Defender) could leave the host exposed.
PowerShell and Service Management
PowerShell makes managing services straightforward thanks to the Microsoft.PowerShell.Management module. This module includes several cmdlets for querying, starting, stopping, and configuring services. Some of the most useful ones include:
Get-Service– list services and check their status.Start-Service– start a stopped service.Stop-Service– stop a running service.Restart-Service– stop and then start a service.Set-Service– configure properties like startup type.
For example:
# Find all services related to Windows Defender
Get-Service | Where-Object { $_.DisplayName -like "*Defender*" }
# Start a Defender service if it is stopped
Start-Service -Name WinDefend
And as always, if you’re unsure of what’s available, you can use:
Get-Help Get-Service -Detailed
This will provide examples, parameters, and context on how to use the cmdlet effectively.
Local and Remote Interaction
PowerShell doesn’t just let us interact with services on the local machine — it also allows remote administration. Using PowerShell Remoting (Enter-PSSession, Invoke-Command), administrators can query and control services across multiple hosts. This makes it invaluable in enterprise environments where a single misconfiguration could affect dozens or hundreds of systems.
Wrapping Up
Managing services is one of the most important daily tasks for a Windows administrator, and understanding how attackers might attempt to disable or modify them only increases the urgency. With PowerShell, we gain the tools to investigate, troubleshoot, and enforce correct service configurations — whether locally or remotely.
Think of this as earning the next stripe on your CLI Kung-Fu Belt: you’re now equipped to handle services like a pro, balancing security and stability in the face of both misconfigurations and potential attacks.
What Cmdlet will show us the current services of a host?
[REDACTED]
If we wanted to start the Windows Defender Service, what command would we use?
[REDACTED]
What Cmdlet will allow us to execute a command on a remote host?
[REDACTED]
Working with the Registry
Now that you’re comfortable with the command line, it’s time to level up and tackle one of Windows’ more complex subsystems: the Registry. This section will explain what the Registry is, how to navigate its hierarchical structure, how to read key/value pairs, and how to safely make changes when needed.
What is the Windows Registry?
Think of the Registry as a hierarchical tree-like database that holds configuration data for the operating system and installed applications. The Registry is organized into keys (the branches) and values (the data stored at those branches). These entries contain everything from application settings and file associations to installation paths and system options that control how Windows and software behave.
Because the Registry centrally stores configuration and state, it’s a prime place for both legitimate administration tasks and deeper security work. For administrators and responders it’s invaluable for diagnosing issues and auditing system state. For penetration testers and attackers it’s frequently used for discovery, storing credentials or settings, and—importantly—creating persistence mechanisms. Security frameworks such as MITRE ATT&CK include many examples of how adversaries use the Registry when they gain local or remote access to a host.
What you’ll learn in this section
- How the Registry is structured (hives, keys, and values).
- How to navigate and query the Registry from the CLI (PowerShell and
reg.exe). - How to read, export, and interpret key/value pairs.
- How to make changes safely, and what precautions to take (backups, exports, least-privilege editing).
- Common Registry locations that are useful for troubleshooting, inventory, persistence hunting, and hardening.
A registry entry is made up of two pieces, a ‘Key’ and ‘ ‘ . What is the second piece?
[REDACTED]
What is the abbreviation for ” HKey_Current_User”.
[REDACTED]
Take some time to practice adding and modifying the registry. Use the target host as a testbed and type “COMPLETE” as the answer below when you are done.
[REDACTED]
Working with the Windows Event Log
From the viewpoint of a SOC Analyst or IT Administrator, monitoring, collecting, and categorizing events across the network is one of the most valuable sources of intelligence for defending systems. Logs provide visibility into user behavior, system performance, application stability, and potential malicious activity. For attackers, however, these same logs can be leveraged in very different ways — as reconnaissance tools to understand the target’s defenses, as obstacles to be disabled or tampered with, or as hiding places where evidence of compromise must be erased.
In penetration testing, event logs can sometimes reveal sensitive information such as credentials, misconfigurations, or overlooked details about how systems are monitored. Other times, by enumerating logs, we gain insight into the organization’s logging strategy — whether they are relying solely on defaults or have hardened their environment with granular, detailed monitoring.
In this section, we’ll explore the following:
- What the Windows Event Log is
- What information it records and where that information is stored
- How to interact with it from the command line using
wevtutil - How to interact with it using PowerShell cmdlets
What is the Windows Event Log?
To truly understand event logs, we need to start with the concept of an event. An event is any identifiable action or occurrence recognized by the system, whether generated by hardware, software, or a user. These events can come from many sources:
- User-Generated Events: Input through peripherals like mouse movement, keyboard activity, or user-triggered actions.
- Application-Generated Events: Application installs, updates, crashes, or memory usage spikes.
- System-Generated Events: Operating system processes such as driver loading/unloading, system boot or shutdown, and user logon/logoff events.
Given the sheer number and variety of these events, Windows requires a consistent way to capture, categorize, and make them available for analysis. This leads us to event logging.
Event Logging Defined
Microsoft defines event logging as:
“…provides a standard, centralized way for applications (and the operating system) to record important software and hardware events.”
This definition captures the purpose well: logs give us a standardized, structured way to record and retrieve event data.
Breaking it down further:
- Every event is generated by a source (application, service, or system component).
- Each source formats its own data, but Windows unifies these events under a central logging service.
- This ensures consistency in how information is captured, regardless of its origin.
The Windows Event Log Service
At the heart of this system is the Windows Event Log service. It is a core Windows service that starts automatically during system initialization. While it doesn’t run as a standalone binary, it operates in the context of another host process, ensuring that the logging mechanism is always active and available.
The service does more than just collect system-wide events:
- It provides a framework for applications to create and manage their own dedicated logs.
- It exposes an API for developers to write logs programmatically.
- It allows administrators and security teams to query, filter, export, and analyze logs.
Because of its central role, the Event Log becomes both a defender’s tool and an attacker’s target.
Why This Matters
Before we dive into hands-on querying with wevtutil and PowerShell, it’s crucial to build a mental model of what events look like and how they are structured. This includes:
- Event Types: Information, Warning, Error, Critical, Audit Success, Audit Failure.
- Log Categories: System logs, Application logs, Security logs, and custom application logs.
- Event Elements: Source, Event ID, Level, Message, Timestamp, and associated metadata.
Understanding these fundamentals gives us the context to properly interpret event logs, identify suspicious activity, and spot gaps in monitoring. It also gives penetration testers the knowledge to assess how visible their activities may be to defenders.
Explore the targets provided and practice your Event Log PowerShell Kung-Fu. Type COMPLETE as the answer when finished.
[REDACTED]
Networking Management from The CLI
PowerShell has greatly extended our ability to interact with networking features in Windows. From checking adapter settings and IP configurations to managing DNS, WinRM, and SSH access, administrators now have a far more powerful toolset for both troubleshooting and remote management. In this section, we’ll walk through how to inspect and validate network settings, as well as how to enable and manage remote access on a Windows host.
Scenario:
Mr. Tanaka’s workstation needs a quick checkup to confirm that his host is operating correctly and that IT staff can securely administer it from the office. To do this, we’ll review his machine’s network configuration and ensure remote management is enabled.
What Is Networking Within a Windows Environment?
Networking on Windows systems is built upon the same fundamental protocols as Linux or Unix-based hosts. The TCP/IP stack, wireless standards, and many common services behave almost identically across platforms. If you are already familiar with networking basics, most of this will feel familiar. If not, you may want to explore the Introduction to Networking or the Network Traffic Analysis modules for a deeper dive into packet flows, addressing, and routing.
Where Windows differs is in the way its hosts communicate with one another, with domains, and with Linux machines in mixed environments. Let’s quickly review several protocols you’re likely to encounter when administering or testing Windows hosts:
| Protocol | Description |
|---|---|
| SMB | Server Message Block enables Windows hosts to share resources such as files and printers. It also provides a standard authentication mechanism between hosts. In Linux, the open-source equivalent is SAMBA. |
| NetBIOS | Not a protocol itself but a communication mechanism. Historically used to transport SMB traffic, it is now often leveraged as a fallback name resolution system (NBT-NS) when DNS fails. |
| LDAP | Lightweight Directory Access Protocol is cross-platform and powers authentication and authorization in environments like Active Directory. |
| LLMNR | Link-Local Multicast Name Resolution provides local name resolution when DNS isn’t available. As it only works on local broadcast domains, it’s limited in scope. |
| DNS | Domain Name System is the global naming service, resolving human-readable hostnames to IP addresses (e.g., www.google.com → 8.8.8.8). |
| HTTP/HTTPS | Hypertext Transfer Protocol is the foundation of web communications, with HTTPS adding encryption for security. Widely used for web servers, APIs, and data exchange. |
| Kerberos | A ticket-based authentication protocol, primarily encountered in Active Directory for secure domain authentication and authorization. |
| WinRM | Windows Remote Management, Microsoft’s implementation of WS-Management, is used for remotely managing Windows hardware and software. Powerful for IT administration, but also commonly abused by attackers. |
| RDP | Remote Desktop Protocol provides a full graphical interface for connecting to Windows systems remotely. It allows complete desktop interaction over a network. |
| SSH | Secure Shell provides encrypted communication for remote access and file transfers. While traditionally used in Unix-like systems, Windows now includes support as well. |
This isn’t an exhaustive list, but it highlights the major protocols you’ll work with when managing or testing Windows networks.
Local vs. Remote Access
- Local Access: This refers to working directly at the machine itself — sitting at the keyboard, viewing its display, and using its resources. In this case, you’re not relying on remote protocols except when connecting out to other hosts on the network or Internet.
- Remote Access: This involves connecting to the host from a different machine, often across a network. Tools such as RDP, WinRM, and SSH come into play here, each with their own strengths and security considerations. Remote access allows IT administrators to manage systems without being physically present, but it also introduces potential entry points that attackers may exploit if poorly secured.
What We’ll Do Next
- Use PowerShell cmdlets to check and validate local network settings (IP configuration, adapter details, DNS servers).
- Explore how to enable and configure WinRM for remote administration.
- Review how to set up and use SSH for secure host management.
What common protocol is used to resolve names to IP addresses.
[REDACTED]
What PowerShell cmdlet will show us the IP configurations of the hosts network adapters.
[REDACTED]
What command can enable and configure Windows Remote Management on a host?
[REDACTED]
Skills Assessment
Your team has been given access to a non-critical Windows host as part of an authorized engagement. That host contains multiple user accounts. The goal of this exercise is to enumerate user names and recover passwords where possible so you can document every discovered credential for follow-up analysis.
This exercise is structured as a sequence of individual challenges. Each challenge corresponds to a specific user account and requires you to authenticate as that user to complete the task and retrieve the flag. In most cases the workflow is chained: the flag recovered for one user becomes the SSH password for the next user (for example, the flag for user2 is used as the SSH password to authenticate as user3).
For each challenge you may be asked to:
- Run particular commands or utilities available on the host.
- Locate files, configuration entries, or artifacts that contain or lead to credentials.
- Perform specific actions or gather evidence that demonstrates successful authentication or access.
Feel free to approach each stage creatively: multiple techniques are often valid and comparing methods will deepen your understanding. Make sure to document every approach you try. Capture one-liners, scripts, command outputs, file paths, and concise notes describing the reasoning that led you to each flag. Those records will be essential for reporting and remediation.
Good practice & reporting expectations
- Record the exact commands and arguments you used, plus any output that proves success.
- For each credential discovered, note the location and method used to obtain it (e.g., file path, registry key, process memory, credential cache — keep this high level in reports).
- Rate each finding by impact (Low/Medium/High) and suggest remediation steps (e.g., rotate password, enforce MFA, reduce service permissions, audit logging).
- Keep your working notes clear and reproducible — reviewers should be able to validate your steps.
Important: authorization & safety
This exercise should only be performed within the scope of a signed engagement or an explicitly authorized lab environment. Do not attempt these techniques on systems you do not have permission to test. If you want, I can include a short checklist your team can have signed by stakeholders to confirm authorization before you run any intrusive steps.
The flag will print in the banner upon successful login on the host via SSH.
Connect using ssh and get the flag
ssh user0@127.0.0.1
$ ssh user@127.0.0.1
###########################################
# #
# Alert! #
# #
###########################################
# You are entering into a secured area! Your IP, Login Time,
# Username has been noted and has been sent
# [REDACTED] to the server
# administrator!
#
# This service is restricted to authorized users only. All
# activities on this system are logged.
# Unauthorized access will be fully investigated and reported
# to the appropriate law enforcement agencies.
###########################################
user@127.0.0.1's password:
Access the host as user1 and read the contents of the file “flag.txt” located in the users Desktop.
Access the server using ssh, username user1 and password D0wn_the_rabbit_H0!3. Open the desktop folder and read the flag.txt
Microsoft Windows [Version 10.0.22000.1219]
(c) Microsoft Corporation. All rights reserved.
user1@ACADEMY-ICL11 C:\Users\user1>cd Desktop
user1@ACADEMY-ICL11 C:\Users\user1\Desktop>dir
Volume in drive C has no label.
Volume Serial Number is F684-763E
Directory of C:\Users\user1\Desktop
12/02/2022 08:47 PM <DIR> .
06/29/2022 02:37 PM <DIR> ..
06/29/2022 07:31 AM 14 flag.txt
06/29/2022 02:35 PM 2,354 Microsoft Edge.lnk
2 File(s) 2,368 bytes
2 Dir(s) 10,750,062,592 bytes free
user1@ACADEMY-ICL11 C:\Users\user1\Desktop>type flag.txt
[REDACTED]
user1@ACADEMY-ICL11 C:\Users\user1\Desktop>
If you search and find the name of this host, you will find the flag for user2.
Connect in the machine using username user2 and password “Nice and Easy!”. Use the command hostname
user2@ACADEMY-ICL11 C:\Users\user2\hostname
[REDACTED]
How many hidden files exist on user3’s Desktop?
Connect in the machine using username user3 and password ACADEMY-ICL11. Use the command dir / a to get the flag.
user3@ACADEMY-ICL11 C:\Users\user3>cd Desktop
user3@ACADEMY-ICL11 C:\Users\user3\Desktop>dir
Volume in drive C has no label.
Volume Serial Number is F684-763E
Directory of C:\Users\user3\Desktop
07/18/2022 08:30 AM <DIR> .
06/29/2022 02:42 PM <DIR> ..
0 File(s) 0 bytes
2 Dir(s) 10,763,026,432 bytes free
user3@ACADEMY-ICL11 C:\Users\user3\Desktop>dir /a
Volume in drive C has no label.
Volume Serial Number is F684-763E
Directory of C:\Users\user3\Desktop
07/18/2022 08:30 AM <DIR> .
06/29/2022 02:42 PM <DIR> ..
06/29/2022 02:40 PM 282 desktop.ini
07/18/2022 08:30 AM 0 file-1.txt
07/18/2022 08:30 AM 0 file10.txt
07/18/2022 08:30 AM 0 file11.txt
07/18/2022 08:30 AM 0 file12.txt
07/18/2022 08:30 AM 0 file13.txt
07/18/2022 08:30 AM 0 file14.txt
07/18/2022 08:30 AM 0 file15.txt
07/18/2022 08:30 AM 0 file16.txt
07/18/2022 08:30 AM 0 file17.txt
07/18/2022 08:30 AM 0 file18.txt
07/18/2022 08:30 AM 0 file19.txt
07/18/2022 08:30 AM 0 file2.txt
07/18/2022 08:30 AM 0 file20.txt
07/18/2022 08:30 AM 0 file21.txt
07/18/2022 08:30 AM 0 file22.txt
07/18/2022 08:30 AM 0 file23.txt
07/18/2022 08:30 AM 0 file24.txt
07/18/2022 08:30 AM 0 file25.txt
07/18/2022 08:30 AM 0 file26.txt
07/18/2022 08:30 AM 0 file27.txt
07/18/2022 08:30 AM 0 file28.txt
07/18/2022 08:30 AM 0 file29.txt
07/18/2022 08:30 AM 0 file3.txt
07/18/2022 08:30 AM 0 file30.txt
07/18/2022 08:30 AM 0 file90.txt
07/18/2022 08:30 AM 0 file91.txt
07/18/2022 08:30 AM 0 file92.txt
07/18/2022 08:30 AM 0 file93.txt
07/18/2022 08:30 AM 0 file94.txt
07/18/2022 08:30 AM 0 file95.txt
07/18/2022 08:30 AM 0 file96.txt
07/18/2022 08:30 AM 0 file97.txt
07/18/2022 08:30 AM 0 file98.txt
07/18/2022 08:30 AM 0 file99.txt
06/29/2022 02:41 PM 2,354 Microsoft Edge.lnk
[REDACTED] 2,636 bytes
2 Dir(s) 10,763,026,432 bytes free
User4 has a lot of files and folders in their Documents folder. The flag can be found within one of them.
Connect in the machine using username user4 and password 101. Use the command bellow:
forfiles /S /M flag.txt /C "cmd /c if @fsize NEQ 0 echo @path"
user4@ACADEMY-IC11 C:\Users\user4\Documents>forfiles /S /M flag.txt /C "cmd /c if @fsize NEQ 0 echo @path"
"C:\Users\user4\Documents\3\4\flag.txt"
user4@ACADEMY-IC11 C:\Users\user4\Documents>type C:\Users\user4\Documents\3\4\flag.txt
[REDACTED]
user4@ACADEMY-IC11 C:\Users\user4\Documents>
How many users exist on this host? (Excluding the DefaultAccount and WDAGUtility)
Connect in the machine using username user5 and password “Digging in The nest”. Use the command
net user
user4@ACADEMY-IC11 C:\Users>net user
User accounts for \\ACADEMY-IC11
---------------------------------------------------------
Administrator DefaultAccount Guest
htd-student user0 user1
user100 user2 user3
user4 user5 user66
user77 user88 user99
WDAGUtilityAccount
The command completed successfully.
user4@ACADEMY-IC11 C:\Users>
For this level, you need to find the Registered Owner of the host. The Owner name is the flag.
Connect in the machine using username user6 and password 14. Use the command bellow:
reg query "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion" /v RegisteredOwner
Microsoft Windows [Version 10.0.22000.1219]
(c) Microsoft Corporation. All rights reserved.
greenhorn\user6@ACADEMY-ICL11 C:\Users\user6.GREENHORN>reg query "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion" /v RegisteredOwner
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion
RegisteredOwner REG_SZ [REDACTED]
greenhorn\user6@ACADEMY-ICL11 C:\Users\user6.GREENHORN>
For this level, you must successfully authenticate to the Domain Controller host at 172.16.5.155 via SSH after first authenticating to the target host. This host seems to have several PowerShell modules loaded, and this user’s flag is hidden in one of them.
Log in the machine from the machine of user6, connect on the host 172.16.5.155 using username user7 and password htd-student. Use the command bellow to find all the modules.
powershell Get-Module -ListAvailable
greenhorn\user7@ACADEMY-ICL-DC C:\Users\user7>powershell Get-Module -ListAvailable
Directory: C:\Users\user7\Documents\WindowsPowerShell\Modules
ModuleType Version Name ExportedCommands
---------- ------- ---- ----------------
Script 0.0 Flag-Finder Get-Flag
Directory: C:\Program Files\WindowsPowerShell\Modules
ModuleType Version Name ExportedCommands
---------- ------- ---- ----------------
Script 1.0.1 Microsoft.PowerShell.Operation.Valid {Get-OperationValidation, Invoke-OperationValidation}
Binary 1.0.0.1 PackageManagement {Find-Package, Get-PackageProvider, Get-PackageSource ...}
Script 5.1.0 Pester {Describe, Context, It, Should ...}
Script 1.2 PowerShellGet {Install-Module, Find-Module, Update-Module ...}
Script 1.2.3 PSReadline {Get-PSReadlineKeyHandler, Remove-PSReadlineKeyHandler, Get-PSReadlineOption ...}
Binary 2.8.0.3 PSWindowsUpdate {Add-WUServiceManager, Enable-WURemoting, Get-WindowsUpdate, Get-WUApiVersion ...}
Directory: C:\Windows\system32\WindowsPowerShell\v1.0\Modules
ModuleType Version Name ExportedCommands
---------- ------- ---- ----------------
Manifest 1.0.1.0 ActiveDirectory {Add-ADComputerServiceAccount, Add-ADDomainControllerPasswordReplicationPolicy, Add-ADFineGrainP...
Manifest 1.0.0.0 AADSSDeployment {Add-AADSSDeployment, Install-AADSSDomain, Install-AADSSDomainController ...}
Manifest 3.0.1.0 AppLocker {Get-AppLockerFileInformation, New-AppLockerPolicy, Set-AppLockerPolicy, Test-AppLockerPolicy ...}
Manifest 1.0.1.0 Appx {Add-AppxPackage, Get-AppxPackageManifest, Remove-AppxPackage ...}
Manifest 1.0.1.0 BestPractices {Get-BpaModel, Get-BpaResult}
Manifest 1.0.1.0 BitsTransfer {Add-BitsFile, Complete-BitsTransfer, Get-BitsTransfer ...}
Manifest 2.0.0.0 BranchCache {Add-BCCache, Disable-BC, Disable-BCDowngrading ...}
Manifest 1.0.0.0 CimCmdlets {Get-CimAssociatedInstance, Get-CimClass, Get-CimInstance, Get-CimSession ...}
Manifest 1.0.0.0 ConfigDefender {Add-MpPreference, Get-MpPreference, Remove-MpPreference ...}
Manifest 1.0.0.0 ConfigEnvironmentVariables {Get-EnvironmentVaria
We found the page that contain the modules.
cd C:\Users\user7\Documents\WindowsPowerShell\Modulesvvv
Let’s see it’s content
greenhorn\user7@ACADEMY-ICL-DC C:\Windows\System32\WindowsPowerShell\v1.0\Modules> cd C:\Users\user7\Documents\WindowsPowerShell\Modules
greenhorn\user7@ACADEMY-ICL-DC C:\Users\user7\Documents\WindowsPowerShell\Modules>dir
Directory of C:\Users\user7\Documents\WindowsPowerShell\Modules
11/22/2022 09:07 PM <DIR> .
11/22/2022 09:07 PM <DIR> ..
11/22/2022 09:08 PM <DIR> Flag-Finder
0 File(s) 0 bytes
3 Dir(s) 32,612,028,416 bytes free
greenhorn\user7@ACADEMY-ICL-DC C:\Users\user7\Documents\WindowsPowerShell\Modules>
Open this folder to find the file and get the flag.
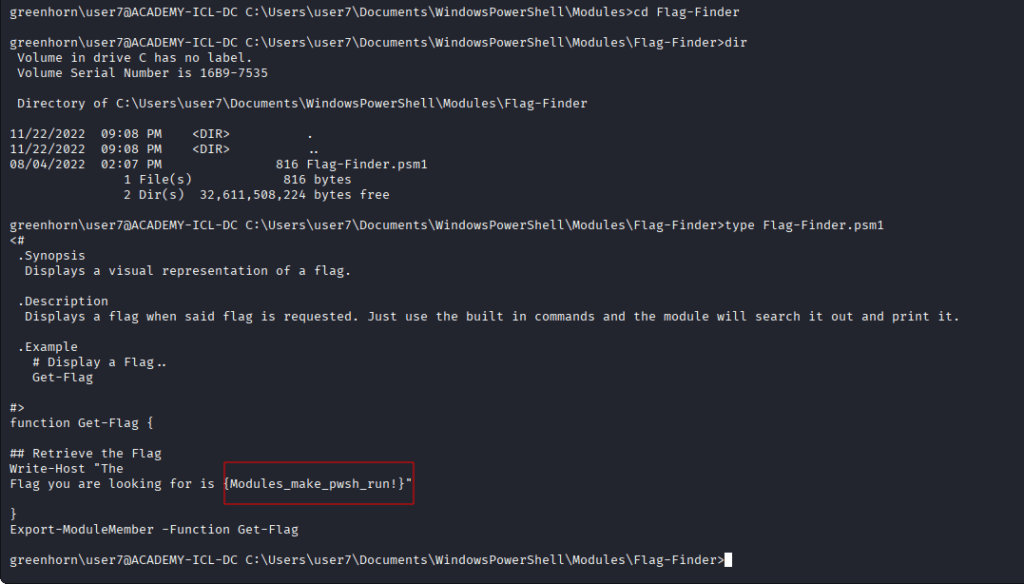
greenhorn\user7@ACADEMY-ICL-DC C:\Users\user7\Documents\WindowsPowerShell\Modules>cd Flag-Finder
greenhorn\user7@ACADEMY-ICL-DC C:\Users\user7\Documents\WindowsPowerShell\Modules\Flag-Finder>dir
Directory of C:\Users\user7\Documents\WindowsPowerShell\Modules\Flag-Finder
11/22/2022 09:08 PM <DIR> .
11/22/2022 09:08 PM <DIR> ..
08/04/2022 02:07 PM 816 Flag-Finder.psm1
1 File(s) 816 bytes
2 Dir(s) 32,611,582,284 bytes free
greenhorn\user7@ACADEMY-ICL-DC C:\Users\user7\Documents\WindowsPowerShell\Modules\Flag-Finder>type Flag-Finder.psm1
.Synopsis
Displays a visual representation of a flag.
.Description
Displays a flag when said flag is requested. Just use the built in commands and the module will search it out and print it.
.Example
# Display a Flag...
Get-Flag
# Retrieve the Flag
function Get-Flag {
Write-Host "The flag you are looking for is [REDACTED]
}
Export-ModuleMember -Function Get-Flag
This flag is the GivenName of a domain user with the Surname “Flag”.
Connect in the machine using username user8 and password “Modules_make_pwsh_run!”. Use the command bellow:
powershell -NoProfile -Command "Import-Module ActiveDirectory; Get-ADUser -LDAPFilter '(sn=Flag)' -Properties GivenName | Select-Object -ExpandProperty GivenName"

Microsoft Windows [Version 10.0.22000.1219]
(c) Microsoft Corporation. All rights reserved.
greenhorn\user8@ACADEMY-ICL11 C:\Users\user8.GREENHORN>powershell -NoProfile -Command "Import-Module ActiveDirectory; Get-ADUser -LDAPFilter '(sn=Flag)' -Properties GivenName | Select-Object -ExpandProperty GivenName"
[REDACTED]
greenhorn\user8@ACADEMY-ICL11 C:\Users\user8.GREENHORN>
Use the tasklist command to print running processes and then sort them in reverse order by name. The name of the process that begins with “vm” is the flag for this user.
Connect in the machine using username user9 and password Rick. User the command bellow:
tasklist | sort /R
Microsoft Windows [Version 10.0.22000.1219]
(c) Microsoft Corporation. All rights reserved.
greenhorn\user9@ACADEMY-ICL11 C:\Users\user9.GREENHORN>tasklist | sort /R
WmiPrvSE.exe 4440 Services 0 20,620 K
winlogon.exe 680 Console 1 16,436 K
wininit.exe 632 Services 0 7,044 K
[REDACTED] 3284 Services 0 22,124 K
vm3dservice.exe 4716 Console 1 6,712 K
vm3dservice.exe 3580 Console 1 6,944 K
vm3dservice.exe 3232 Services 0 6,456 K
VGAuthService.exe 3612 Services 0 11,544 K
tasklist.exe 5220 Services 0 8,804 K
System Idle Process 0 Services 0 136 K
System 4 Services 0 0 K
svchost.exe 5996 Services 0 10,140 K
svchost.exe 5984 Services 0 7,708 K
svchost.exe 5944 Services 0 18,040 K
svchost.exe 5804 Services 0 24,368 K
svchost.exe 5596 Services 0 13,256 K
svchost.exe 5140 Services 0 11,768 K
svchost.exe 4564 Services 0 8,832 K
svchost.exe 4100 Services 0 8,032 K
svchost.exe 3860 Services 0 7,920 K
What user account on the Domain Controller has many Event ID (4625) logon failures generated in rapid succession, which is indicative of a password brute forcing attack? The flag is the name of the user account.
Connect in the machine using username user9 and password vmtoolsd.exe. From this machine connect in the local machine.
ssh user10@172.16.5.155
The password is “vmtoolsd.exe”. From there, use the commands bellow:
powershell
$evts = Get-WinEvent -FilterHashtable @{ LogName='Security'; Id=4625 }
$evts | Format-Table TimeCreated, @{N='User';E={$_.Properties[5].Value}}
$evts.Count
PS C:\Users\user10> # eventos do usuário específico
PS C:\Users\user10> $evts = Get-WinEvent -FilterHashtable @{ LogName='Security'; Id=4625 } |
>> Where-Object { $_.Properties[5].Value -eq 'justalocaladmin' }
PS C:\Users\user10>
PS C:\Users\user10> # lista os registros e depois imprime a contagem
PS C:\Users\user10> $evts | Format-Table TimeCreated, @{N='User';E={$_.Properties[5].Value}}
TimeCreated User
----------- ----
11/29/2022 7:05:04 PM [REDACTED]
