Introduction to Windows
For a penetration tester, it’s essential to have a working knowledge of different technologies. Among the most important are Windows and Linux, since these two operating systems make up the majority of the environments encountered during security assessments, whether they are hosted on-premises or in the cloud. A solid understanding of both platforms not only helps in identifying and exploiting weaknesses but also in defending them and using them as a base for launching further penetration testing activities.
The Windows Operating System
Microsoft officially introduced Windows on November 20, 1985, as a graphical shell that ran on top of MS-DOS. Over the following years, the Windows Desktop line expanded to include tools like File Manager, Program Manager, and Print Manager, which simplified user interaction with the system.
A major milestone came with Windows 95, which marked the first full integration of Windows and DOS. This version included built-in internet connectivity and introduced the Internet Explorer browser. Since then, Microsoft has released more than a dozen Windows versions, including Windows XP, Vista, and Windows 8, leading up to the current desktop edition: Windows 11. Each release has typically come in multiple editions aimed at home users, businesses, and large enterprises.
Windows Server Evolution
Microsoft’s server line began in 1993 with Windows NT 3.1 Advanced Server. Over time, Windows NT was enhanced with features like Internet Information Services (IIS), networking protocol support, and Administrative Wizards to simplify management.
In Windows 2000 Server, Microsoft introduced Active Directory (AD), which revolutionized system administration by enabling centralized management for file sharing, encryption, VPNs, and more. This version also added the Microsoft Management Console (MMC) and support for dynamic disk volumes.
- Windows Server 2003 introduced server roles, a built-in firewall, and the Volume Shadow Copy Service.
- Windows Server 2008 brought failover clustering, Hyper-V virtualization, Server Core, an updated Event Viewer, and major AD improvements.
- Later releases included Server 2012, 2016, and 2019, with the most recent versions incorporating support for Kubernetes, Linux containers, and advanced security enhancements.
Support Lifecycle and Legacy Systems
Like most software, Windows versions follow a support lifecycle. Once new versions are released, older ones are eventually deprecated and stop receiving official updates—unless an organization pays for extended support. For example, Windows Server 2008 and 2012 reached end of life for security updates on January 14, 2020. At present, only Server 2012 R2 and newer are officially supported.
That said, Microsoft occasionally issues out-of-band security patches for older, unsupported versions. A famous case was the emergency fix for the SMBv1 vulnerability (EternalBlue), which affected even legacy systems.
Despite risks, many organizations continue running outdated Windows versions, often to support critical business applications or due to budget and operational constraints. For penetration testers, this reality makes it vital to understand the nuances between Windows versions, the configurations they rely on, and the vulnerabilities they expose.
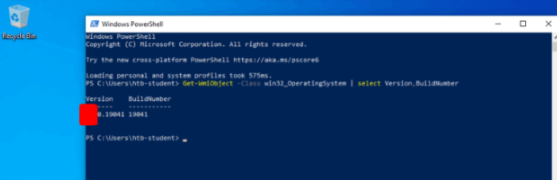
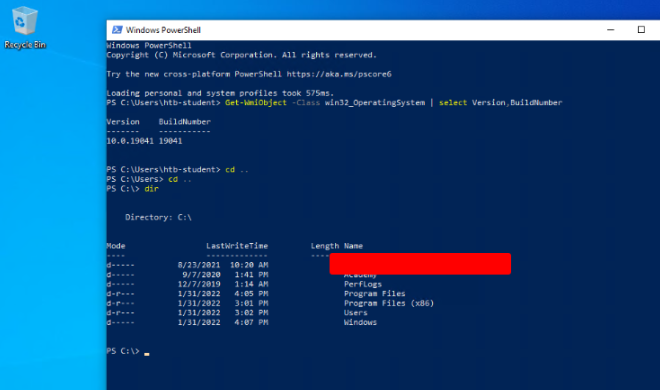
What is the Build Number of the target workstation?
Connect to the windows machine using xfreerdp3
xfreerdp3 /v:127.0.0.1 /u:htd-student /p:Academy_WinFun!

Open PowerShell
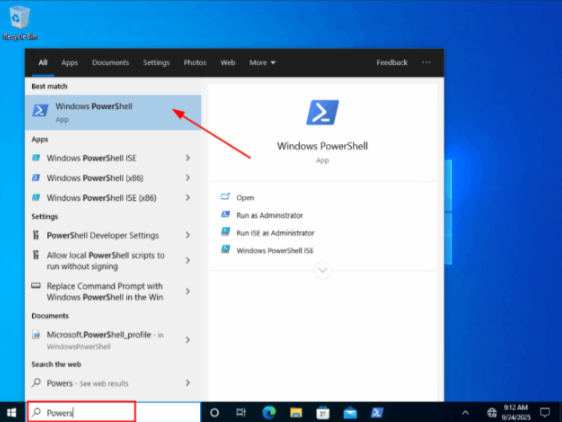
Use the command bellow:
Get-WmiObject -Class win32_OperatingSystem | select Version,BuildNumber
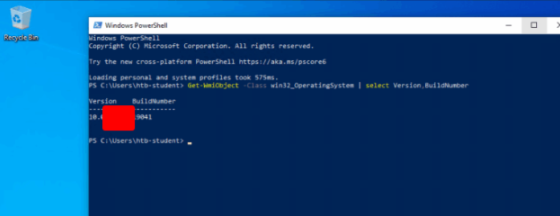
Which Windows NT version is installed on the workstation? (i.e. Windows X – case sensitive)
Operating System Structure
In Windows operating systems, the root directory is represented as <drive_letter>:\ (most commonly the C: drive). This root directory—also called the boot partition—is where the operating system is installed. Additional physical or virtual drives are typically mapped to other letters, such as E: for a separate data partition.
The root of the boot partition follows a well-defined directory structure, with each folder serving a particular role:
| Directory | Purpose |
|---|---|
| Perflogs | Designed to store Windows performance logs. It’s empty by default but can be used during performance monitoring. |
| Program Files | On 32-bit systems, this is where both 16-bit and 32-bit applications are installed. On 64-bit systems, only 64-bit applications are placed here. |
| Program Files (x86) | Available on 64-bit editions of Windows, this folder stores 32-bit and 16-bit applications to keep them separate from native 64-bit programs. |
| ProgramData | A hidden system folder that holds data required for installed programs to function. It’s accessible by applications regardless of the user account currently logged in. |
| Users | Contains a profile folder for each system user. Inside are two special subfolders: Public and Default. |
| Default | Acts as the profile template for all new users. When a new account is created, Windows copies the contents of this folder to form the user’s initial profile. |
| Public | Provides a common space where all users can share files. By default, it’s also shared over the network, though access requires a valid network account. |
| AppData | A hidden per-user folder (e.g., cliff.moore\AppData) containing application data and settings. It includes three subfolders: Roaming (data synchronized across machines, like custom dictionaries), Local (machine-specific data that doesn’t sync), and LocalLow (similar to Local, but with reduced integrity—often used by apps like web browsers in protected mode). |
| Windows | Houses the majority of system files necessary for the operating system to function. |
| System, System32, SysWOW64 | Core directories that store the DLL files required for Windows functionality and its API. When a program requests a DLL without an absolute path, Windows automatically looks here. |
| WinSxS | Known as the Windows Component Store, it maintains copies of all Windows components, updates, and service packs. This ensures system stability and supports features like side-by-side assembly. |
Find the non-standard directory in the C drive. Submit the contents of the flag file saved in this directory.
Go to the root folder
cd ..
cd ..
dir
File System
Windows supports five main file systems: FAT12, FAT16, FAT32, NTFS, and exFAT. The older FAT12 and FAT16 formats are considered obsolete and are no longer used in modern versions of Windows. For this training, we’ll briefly review FAT32 and exFAT, but our primary focus will be on NTFS, the standard file system for Windows today.
FAT32 (File Allocation Table 32)
FAT32 is one of the most widely adopted file systems, commonly found on USB drives, SD cards, and other portable storage media. It can also be used to format traditional hard drives. The “32” in its name indicates that it uses 32-bit addressing to track clusters of data on a storage device.
Advantages of FAT32:
- Broad device compatibility: Works across a wide range of devices, including computers, cameras, gaming consoles, smartphones, and tablets.
- Cross-platform support: Supported by all Windows versions since Windows 95 and also compatible with macOS and Linux.
Limitations of FAT32:
- Maximum file size is limited to 4 GB, which is restrictive for modern use cases like large video files or databases.
- Lacks built-in security or compression features.
- Does not support native file encryption—external tools are required for that.
NTFS (New Technology File System)
Introduced with Windows NT 3.1, NTFS has been the default Windows file system ever since. It not only resolves FAT32’s shortcomings but also provides advanced features designed for security, reliability, and performance.
Advantages of NTFS:
- High reliability: NTFS uses journaling, which logs changes to files (creation, modification, deletion). This helps restore consistency after unexpected shutdowns or power failures.
- Strong security: Allows fine-grained access control through permissions at both the file and folder level.
- Scalability: Supports extremely large partitions and file sizes.
- Metadata support: Enhanced data structuring improves performance and system efficiency.
Limitations of NTFS:
- Not widely supported by mobile devices or lightweight embedded systems.
- Many older media devices (such as certain TVs or digital cameras) cannot read NTFS-formatted storage
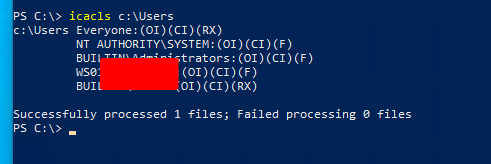
What system user has full control over the c:\users directory?
icacls c:\Users
NTFS vs. Share Permissions
Windows dominates the desktop operating system landscape, holding more than 70% of the global market share. This widespread adoption makes it the prime target for malware authors, who naturally want their efforts to reach as many systems as possible. From a business standpoint, investing resources into developing malware for Windows simply offers the best return on effort, which is why Windows is often perceived as being “less secure” than other platforms.
It is important to understand, however, that no operating system is inherently immune to malware. As long as software can be written for an OS, malicious software can also be created for it. A virus, by definition, is just a program with harmful intent—and this applies equally to Windows, Linux, macOS, and beyond.
Malware Spread in Windows Environments
Windows malware is often capable of spreading across networks, particularly through network shares configured with overly permissive settings. One infamous example of a vulnerability leveraged in such attacks is EternalBlue, a critical flaw in the SMBv1 protocol. Even years after its discovery, many unpatched Windows systems remain exposed, allowing attackers to deliver ransomware and bring entire organizations to a halt.
The Role of SMB
The Server Message Block (SMB) protocol is central to Windows networking. It provides the ability to share resources like files and printers across systems, and is widely used in organizations of all sizes—small businesses, medium enterprises, and large corporations alike. While SMB is essential for collaboration, its misuse or misconfiguration has repeatedly been exploited as a powerful attack vector.
What protocol discussed in this section is used to share resources on the network using Windows? (Format: case sensitive)
When Windows systems need to access shared files, printers, or network devices, they use a protocol designed for resource sharing across a LAN. This protocol is known as SMB, and it enables communication between clients and servers for these shared services. It is fundamental to Windows networking and is widely used in enterprise environments.
What is the name of the utility that can be used to view logs made by a Windows system? (Format: 2 words, 1 space, not case sensitive)
To inspect system, application, and security logs on Windows, administrators open a built-in graphical tool that organizes entries by category. This tool is called Event Viewer, and it helps diagnose issues and monitor system activity. It is essential for troubleshooting errors and investigating suspicious behavior.
What is the full directory path to the Company Data share we created?
C:\Users\htd-student> net share
Share name Resource Remark
-------------------------------------------------------------------------------
C$ C:\ Default share
IPC$ Remote IPC
ADMIN$ C:\WINDOWS Remote Admin
Company Data [REDACTED]
The command completed successfully.
Windows Services & Processes
Services are a fundamental part of the Windows operating system, designed to handle long-running background processes. Unlike regular applications, services can be configured to start automatically during system boot, without requiring any user interaction. Once launched, they continue to run silently in the background—even after a user logs out of the system.
Applications can also be installed as services to ensure persistence and reliability. For instance, a network monitoring tool on a server may be deployed as a service to guarantee that it runs continuously and independently of user sessions.
Functions of Windows Services
Windows services are responsible for a wide range of critical tasks, including:
- Networking operations (e.g., handling communication protocols).
- System diagnostics and monitoring.
- User credential management.
- Automated updates, such as those managed by the Windows Update service.
- Many other core OS functions that require stability and consistency.
Service Management in Windows
Services are controlled through the Service Control Manager (SCM). The most common way to access this is via the services.msc Microsoft Management Console (MMC) snap-in. This graphical tool allows administrators to view and configure service properties, including:
- Name – the identifier of the service.
- Description – details about its role and purpose.
- Status – whether it is currently running, stopped, or paused.
- Startup Type – configuration for how the service launches (Automatic, Manual, or Disabled).
- Log On As – the user account or system account the service runs under.
Command-Line Management
Beyond the GUI, Windows also provides powerful command-line tools for working with services:
- sc.exe – a legacy but robust tool for creating, configuring, and controlling services.
- PowerShell cmdlets – such as
Get-Service,Start-Service, andStop-Service, which give administrators scriptable control over services and integrate well with automation workflows.
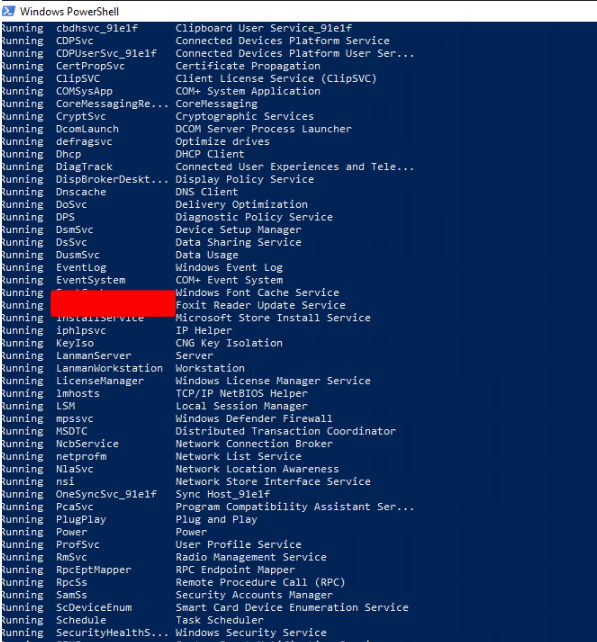
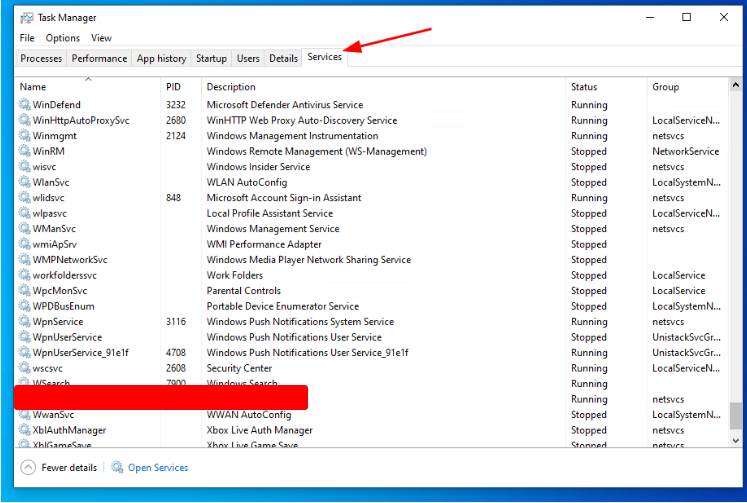
Identify one of the non-standard update services running on the host. Submit the full name of the service executable (not the DisplayName) as your answer.
Get-Service | ? {$_Status -eq "Running"}
Interacting with the Windows Operating System
Graphical User Interface (GUI)
The graphical user interface (GUI) was first developed in the late 1970s at the Xerox Palo Alto Research Center (PARC). It was later adopted by Apple and Microsoft to make computers more user-friendly, particularly for non-technical users who might struggle with the command line.
As its name suggests, a GUI allows users to interact with the operating system and applications through a visual, point-and-click interface, instead of typing commands. This design made computers accessible to a much wider audience, since people no longer needed to memorize commands or learn programming just to operate their machines.
In professional environments, system administrators frequently rely on GUI tools for managing services such as Active Directory, configuring Internet Information Services (IIS), or interacting with databases.
Remote Desktop Protocol (RDP)
Remote Desktop Protocol (RDP) is a proprietary Microsoft technology that enables users to connect to a remote computer over a network connection and access its GUI.
- How it works: An RDP client connects to a system running RDP server software.
- Port usage: By default, RDP communicates over TCP port 3389.
- User experience: Once connected, users see and interact with the remote desktop as if they were sitting in front of the machine locally.
RDP is widely used by system administrators to manage servers and workstations remotely. It is also common for employees to access their office computers while traveling or working from home, often in combination with a VPN for secure connectivity.
Windows Command Line
While GUIs provide ease of use, the command line offers more precise control and flexibility. Command-line interfaces (CLIs) are powerful tools for daily administration, troubleshooting, and especially automation. For example, administrators can write scripts to add multiple users to a domain at once, saving significant time.
Windows provides two main command-line environments:
CMD (Command Prompt)
The Command Prompt (cmd.exe) is a traditional CLI environment for running commands and scripts. Common tasks include:
- Running quick commands like
ipconfigto display IP configuration details. - Creating scheduled tasks.
- Writing batch scripts for automation.
It can be launched in multiple ways:
- From the Start Menu.
- By typing
cmdin the Run dialog (Win + R). - By directly executing the binary located at:
C:\Windows\System32\cmd.exe
PowerShell
In addition to CMD, Windows includes PowerShell, a more advanced CLI and scripting framework that integrates with the .NET framework. PowerShell enables deeper automation and system management than CMD and is a preferred tool for modern Windows administration.
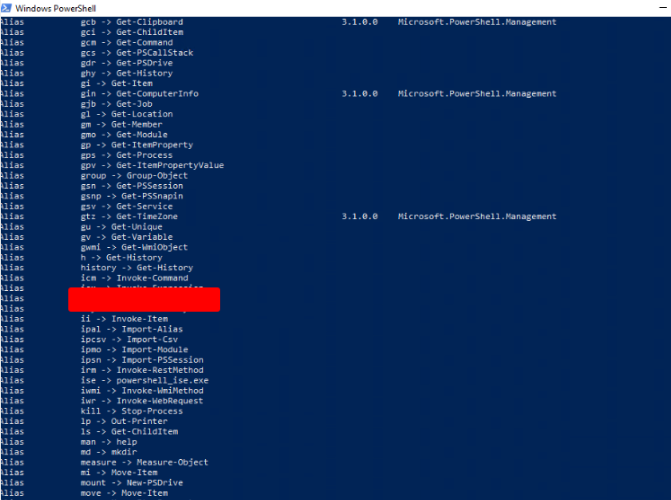
What is the alias set for the ipconfig.exe command?
Get-alias
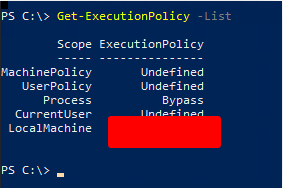
Find the Execution Policy set for the LocalMachine scope.
Get-ExecutionPolicy -List
Windows Management Instrumentation (WMI)
Windows Management Instrumentation (WMI) is a subsystem of PowerShell that gives system administrators robust tools for monitoring and managing systems. Its primary goal is to provide a centralized framework for device and application management across enterprise networks.
Since Windows 2000, WMI has been a core component of the operating system, installed by default and deeply integrated into system operations.
Key Components of WMI
WMI is made up of several components that work together to deliver management and monitoring capabilities:
| Component | Description |
|---|---|
| WMI service | The main process that launches automatically at boot. It acts as a bridge between WMI providers, the WMI repository, and management applications. |
| Managed objects | Any logical or physical element that can be monitored or configured through WMI. |
| WMI providers | Specialized objects responsible for tracking events and data tied to specific managed objects. |
| Classes | Structures used by providers to send data to the WMI service. |
| Methods | Actions attached to classes, enabling tasks such as starting or stopping processes on remote machines. |
| WMI repository | A database that stores static WMI-related information. |
| CIM Object Manager | The system component that retrieves data from WMI providers and delivers it to requesting applications. |
| WMI API | Provides a standardized way for applications to interact with the WMI infrastructure. |
| WMI Consumer | Issues queries to objects through the CIM Object Manager. |
Practical Uses of WMI
System administrators and security professionals commonly rely on WMI for tasks such as:
- Retrieving status information for local or remote systems.
- Configuring security settings on remote computers or applications.
- Managing user and group permissions.
- Setting or modifying system properties.
- Executing code or commands.
- Scheduling recurring processes.
- Enabling detailed logging for troubleshooting or auditing.
Using WMI in Practice
WMI tasks can be executed through PowerShell or the WMI Command-Line Interface (WMIC):
- Launch the interactive WMI shell by typing:
wmic - Run a one-off command, such as retrieving the system hostname:
wmic computersystem get name - Display a full list of available WMIC commands and aliases:
wmic /?
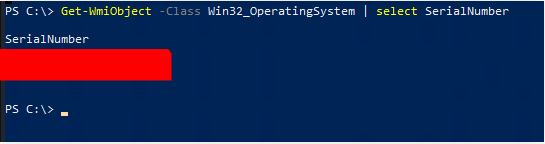
Use WMI to find the serial number of the system.
Get-WmiObject -Class Win32_OperatingSystem | select SerialNumber
Windows Security
Security is one of the most critical aspects of the Windows ecosystem. Because Windows consists of numerous integrated components—applications, services, features, and layers of configuration—it presents a large attack surface. Even fully patched systems may be left vulnerable if administrators misconfigure settings or fail to apply best practices.
Windows also comes with many built-in features that, while useful, can be abused by attackers. Over the years, the platform has suffered from a wide range of serious vulnerabilities that have enabled highly effective remote and local exploits.
Evolving Security Measures
Despite these challenges, Microsoft has consistently improved Windows security. As digital environments grow more interconnected and attackers adopt increasingly advanced techniques, Microsoft has responded by embedding new defensive features. These improvements give system administrators stronger tools to:
- Harden systems against common attack vectors.
- Block malicious activity proactively.
- Detect and respond to intrusion attempts or misuse.
Windows Security Model
Windows enforces a security model built around strict principles of access control and authentication. These principles apply across different system entities, including:
- Users
- Networked computers
- Threads
- Processes
Each of these entities can be authorized to perform only specific actions, limiting the scope of what they can do. The design of this model helps minimize unauthorized access and raises the barrier for attackers or malicious software attempting to exploit the system.
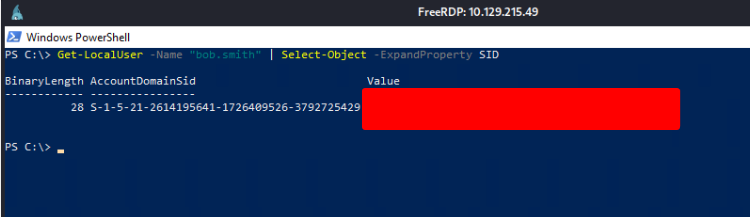
Find the SID of the bob.smith user.
Get-LocalUser -Name "bob.smith" | Select-Object -ExpandProperty SID
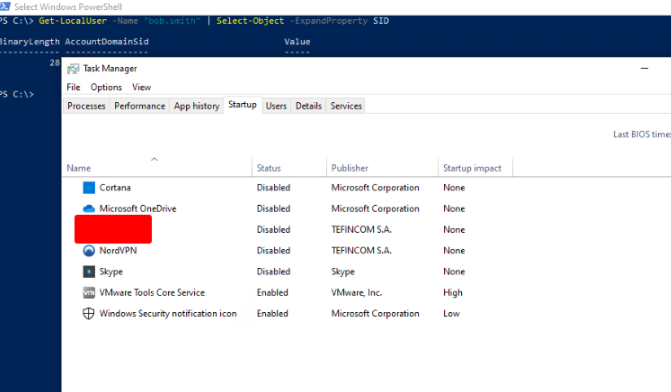
What 3rd party security application is disabled at startup for the current user? (The answer is case sensitive).
Press Ctrl + Alt + Del and choose Task Manager. Go to the Startup tab.
Skills Assessment – Windows Fundamentals
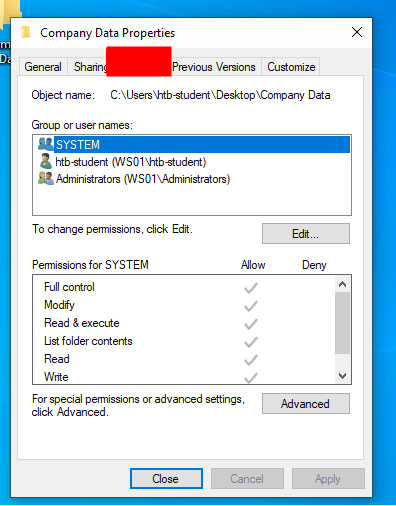
What is the name of the group that is present in the Company Data Share Permissions ACL by default?
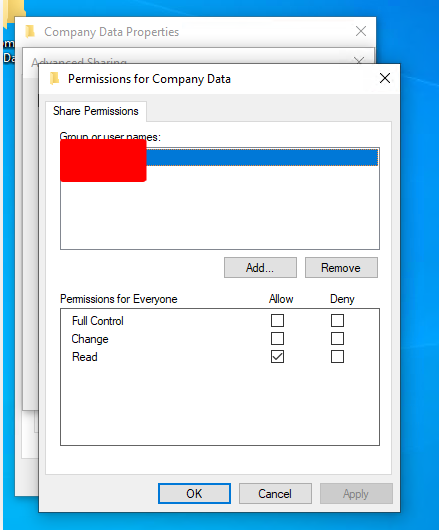
What is the name of the tab that allows you to configure NTFS permissions?
What is the name of the service associated with Windows Update?
List the SID associated with the user account Jim you created.
PS C:\Users\htd-student> Get-CimInstance -ClassName Win32_UserAccount | ForEach-Object {
$Username = $_.Name
$SID = $_.SID
Write-Output "User: $Username, SID: $SID"
}
User: Administrator, SID: S-1-5-21-2614195641-1726409526-3792725429-500
User: bob.smith, SID: S-1-5-21-2614195641-1726409526-3792725429-1003
User: DefaultAccount, SID: S-1-5-21-2614195641-1726409526-3792725429-503
User: defaultuser0, SID: S-1-5-21-2614195641-1726409526-3792725429-1000
User: Guest, SID: S-1-5-21-2614195641-1726409526-3792725429-501
User: htd-student, SID: S-1-5-21-2614195641-1726409526-3792725429-1002
User: Jim, SID: [REDACTED]
User: mrBr3n, SID: S-1-5-21-2614195641-1726409526-3792725429-1001
User: WDAGUtilityAccount, SID: S-1-5-21-2614195641-1726409526-3792725429-504
PS C:\Users\htd-student>
List the SID associated with the HR security group you created.
Get-WmiObject -Class Win32_Group -Filter "Name='HR'" | Select-Object -ExpandProperty SID
PS C:\WINDOWS\system32> Get-WmiObject -Class Win32_Group -Filter "Name='HR'" | Select-Object -ExpandProperty SID
[REDACTED]